EXECUTIVE SUMMARY
The potential vulnerability of freight transportation information systems to terrorist attacks is a serious concern for homeland security. In this report the groundwork is laid for a study of the cybersecurity of the information systems on which freight transportation depends to facilitate efficient delivery of the goods and materials that drive the economy.
The development of computer security system designs and strategies for the freight transportation industry must be accomplished within a framework that is sensitive to the following important attributes of the industry:
-
It consists of different carrier modes (i.e., truck, rail, sea, air, and pipeline). Its companies cover a wide range of characteristics, including size, economic condition, technical know-how, cargo types, and geographical location. This diversity makes it difficult to develop a uniform security design concept with managed implementation schedules. Instead, evolutionary steps tailored to the different parts of the industry on a case-by-case basis must be developed to address identified vulnerabilities.
-
The existing freight transportation information system is a confederation of company-to-company information system integrations constructed to permit more efficient operation. The design is not uniform, not specified, not documented, not evaluated, not tested, and not under configuration control. These features make security design analysis and evaluation extraordinarily difficult.
-
Many potential cyberattacks on the freight transportation industry would result in consequences to stakeholders other than the industry itself. For example, (a) customers that depend on the freight industry for tightly managed supply delivery schedules can suffer significantly when deliveries are delayed; (b) safety-related attacks, such as an attack on a hazmat freight vehicle, would affect the general public directly; and (c) political attacks, such as threats to import a nuclear weapon into the United States, would affect the
-
government’s policies on imports. Consideration of possible measures to address such scenarios, and their costs, should reflect these facts.
As a result of this situation, a focused, evolutionary process for identifying and prioritizing security enhancements will be required. Development and implementation of such a process are likely to be slower than one might like, so there is a need to focus efforts on the most critical areas. Otherwise, unnecessary expense will be incurred, and, under some conditions, the efforts might even be counterproductive—every change to the system introduces the risk of new vulnerabilities.
TYPES OF THREATS
Cyberattacks on transportation and logistics networks could take several different forms, with varying consequences and probabilities. Reducing vulnerability requires consideration of all plausible types, including those discussed here. The first one is a direct attack on the information systems, while the latter two use information technology (IT) to enable or amplify a physical attack. It should be noted that a physical attack on the IT systems coordinated with a cyberattack could cause far more damage than either type alone. This report, however, is concerned only with cyberattacks, which would not differ much if they were accompanied by physical attacks. The full study should consider all types of threats involving cyberattacks, and their consequences.
Denial of service: Cyberattacks, whether by terrorists or hackers, might bring down information systems with what is known as a “denial-of-service” attack. For example, the perpetrator might gain entry to a large number of unprotected computers on the Internet and program them to access selected websites simultaneously. The computers controlling these websites might then crash. Companies in other industries have been subjected to denial-of-service attacks on their websites and servers, which were probably perpetrated by individual hackers. Such attacks are not the subject of this report, which focuses on large-scale, organized attacks intended to inflict maximum economic damage over a long period of time. No massive, coordinated attacks have yet been launched on any network, but if directed at freight information systems, such attacks could disrupt freight service, causing significant damage to the economy.1 A related concern is delib-
erate disruption of a military mobilization during a national crisis. Although individual freight companies may not be unusually vulnerable to such attacks, the interconnections of the industry’s information systems and the increasing role of the Internet suggest the potential for widespread damage. One individual system whose loss could result in significant economic harm is that of the Bureau of Customs and Border Protection (Customs; formerly the U.S. Customs Service), because it is vital for the orderly flow of imports and exports.2 The full study suggested by this report should also consider how quickly the system could recover from an attack and how well the freight system could operate in the interim. Of the three types of attacks, denial-of-service attacks probably are the easiest to perpetrate but the least damaging.
Hazardous material shipments: More than 800,000 hazmat shipments occur daily in the United States. Some are potential targets for terrorists trying to harm people or seeking materials for making weapons. Terrorists could hack into and misuse information systems to identify and track such shipments in order to attack them at high-consequence locations. Under some conditions, the male-factors might actually cause an accident resulting in the release of hazardous materials purely through a cyberattack, for example by seizing control of railroad switches or signals. Alternatively, terrorists might commandeer the supervisory control and data acquisition (SCADA) system of a pipeline network carrying dangerous material to maximize the damage following a physical attack.
Weapons of mass destruction: Terrorists trying to bring a weapon of mass destruction (chemical, biological, or nuclear) into the United States could disguise it as ordinary freight. They could exploit vulnerabilities in transportation information systems to mask and track their shipments, thus reducing the risk of detection. This approach is likely to become more attractive to terrorists as physical security requirements become more stringent. Terrorists also might use unauthorized access to freight information systems to move weapons around in the United States or export them to other countries. This type of attack could have extremely serious consequences, but it also may be the least likely, and the IT role in the attack may not be central. Information systems could, however, play a role in reducing physical vulnerability to such use of the freight transportation system.
All major industries are vulnerable to cyber- and physical attacks. The freight transportation industry appears to offer unusual potential for both
economic and physical damage from terrorist cyberattacks.3 These concerns may grow because freight transport is increasingly dependent on IT. As long as the threat of terrorism remains, cybersecurity in the freight transport sector will be an important issue, although it is impossible to define the threat exactly orquantify it.
KEY CHARACTERISTICS OF THE FREIGHT TRANSPORTATION INDUSTRY
A cyberattack could come at any time and hit any point of vulnerability in the system. A variety of measures to reduce vulnerability are being implemented or considered. The factors discussed here and in more detail in Chapters 1 and 2 should be taken into account when such measures are considered.
INDUSTRY SCALE AND COMPLEXITY
Freight transportation is handled by a great many individual companies operating different modes of transport (e.g., ship, truck, train, air) in a large and complex global system. The industry uses millions of trucks, rail cars, containers, and so forth and employs millions of people to move billions of tons of freight annually. Some modes (e.g., air, rail, pipelines) are concentrated, with relatively few companies. Others (e.g., trucking, international shipping) include many companies, ranging from large and highly sophisticated organizations to “mom and pop” operations using manual or low-technology systems. The fragmented and changing nature of the industry, the diversity of the modes, and the lack of overall system security coordination can lead to vulnerability. Intense competition keeps profit margins low for companies in all modes, which limits their ability to fund new infrastructure, technology, and procedures if the return on investment is not readily apparent.
PUBLIC–PRIVATE INTERACTIONS
Freight operations in the United States are essentially all in the private sector, but they are intimately connected with the public sector. In addition to using government-owned facilities such as highways, ports, and airports, the freight
transportation industry is affected by many aspects of government regulation—federal, state, local, and regional. Government monitoring (e.g., customs clearance, truck weighing, and even first responder monitoring of hazmat shipments) provides opportunities for unauthorized access to information systems, including the electronic cargo declarations submitted to Customs, because any entry point provides a potential vulnerability for cyberterrorists.
INFORMATION SYSTEMS COMPLEXITY
Freight information systems are a significant factor in the steadily improving efficiency of the industry. These systems also help provide highly reliable delivery, which, among other benefits, permits customers to operate with lower inventories, including “just-in-time” inbound materials strategies. The transport/logistics system functions globally, but it is made up of discrete and varied subsystems among the different modes and even among the companies within a mode. The system is not integrated; instead, the subsystems are only interconnected at many different points and in different ways. Many transport and logistics firms also connect with their customers and government agencies such as Customs. Each interconnection represents a point of potential vulnerability to attack. In addition, the ever-changing mix of carriers, shippers, distributors, and freight forwarders who are or can be connected to the “system” makes it very difficult to identify and authenticate users. The complexity and diversity of these systems are a serious challenge in the development and implementation of a comprehensive cybersecurity strategy for freight transportation information systems.
OVERALL COORDINATION
Coordination of efforts to reduce cybervulnerability is a major challenge. No single government agency, private firm, or association is in a position to consider the whole transportation/logistics continuum as a complex system. Instead, many different organizations have influence over fragments of the system. They act where they can, but that is not necessarily at the point of highest priority.
VULNERABILITIES, SECURITY, AND TECHNOLOGIES
Many factors create potential vulnerabilities to cyberattacks on freight transportation information systems, including the interconnection of systems, the increased reliance on the Internet for communications, and the emergence of
decentralized systems. These potential vulnerabilities and associated technologies are discussed here. A fundamental issue is whether the improvement in security is adequate to justify the cost.
INTERCONNECTIONS
The interconnection of systems across large transportation sectors allows carriers, shippers, and manufacturers alike to increase the efficiency of their operations. As the web of interconnected information systems grows, however, it can become more susceptible to denial-of-service attacks, improper use, and unauthorized access.
Large organizations in the transportation sector have interconnected their own information systems to create systems spanning the enterprise. Smaller companies have interconnected their systems to create “federated” or “cooperative” systems that allow them to compete more effectively with larger organizations. In addition, regulatory forces (some motivated by post–September 11 homeland security concerns) are driving the interconnection of commercial and government systems by requiring carriers, importers, exporters, and manufacturers to submit more information electronically to the government. For example, Customs’ Automated Manifest System represents a vital link in the flow of information about imported goods.
Documents such as bills of lading and letters of credit are essential for the shipments of goods. They are increasingly sent in electronic form, but electronic documents can easily be altered or counterfeited if they are not appropriately protected. Electronic data interchange standards exist for the transportation sector, but the sector has generally not incorporated authentication technologies into its emerging systems and standards to ensure the authenticity of the document author and that the document can be exchanged privately with another party.
INTERNET COMMUNICATIONS
The Internet is used increasingly as the primary communication method among transportation partners or transportation carriers and their customers. Freight transportation has benefited from a revolution in logistics based largely on improved communications through the Internet. In supply chain management and the optimization of logistics, the ability to transmit data across the Internet reliably is critical. Improvements in supply chain efficiency have been an important factor in economic growth, as discussed in Chapter 1. The most critical security concern of the Internet is that attacks can come at any time and from
virtually anywhere in the world. It is inherently difficult to prevent such attacks or to identify the perpetrators afterwards, as noted in Chapter 2.
The Internet itself provides only minimal levels of access control and protection against eavesdropping. Virtual private network technology incorporates encryption and other security mechanisms to provide enhanced security for remote user-to-system and system-to-system communications over the Internet, but only for prearranged situations involving a small number of systems. In general, the lack of a widely accepted encryption infrastructure significantly impedes improved security.
DECENTRALIZED SYSTEMS
Since the introduction of Web-based application techniques in the early 1990s, system architects have been shifting the design of information systems from primarily centralized systems toward decentralized systems (networks that—like the Internet—operate without central control).
The most significant challenge for the use of wide-scale decentralized systems is that of developing the infrastructure needed to authenticate all of the users in the system. In the decentralized model, no central authority can resolve such issues, which makes security control more difficult, though still possible.
OTHER DEVELOPMENTS
Many technologies now being implemented or tested for potential use in the freight transportation industry may have cybersecurity implications.
Embedded processors are, to varying degrees, being used or tested by the transportation sector, primarily for the identification and monitoring of shipments. Radio frequency identification (RFID) tags automatically identify an asset or its declared contents, or both. E-sensorsdetect and document environmental changes to a shipment along its route. E-seals are the electronic version of mechanical seals; they can be placed on shipments or structures to detect an unauthorized entry or deter intrusions because of the fear of detection. These devices are being studied in pilot programs (see Appendix B). They are intended to address aspects of physical security, not cybersecurity, but their links to transportation information systems suggest that they should be part of a study of IT vulnerability. For example, terrorists might hack into e-seals to conceal tampering with a container.
Several enabling technologies may become part of the transportation sector’s IT infrastructure. Wireless communications (i.e., RF, infrared, terrestrial, satellite-based) can transmit information with mobile units. Wireless tracking systems already are used in the trucking industry, often for critical, high-value ship-
ments. Almost all of the embedded devices that may be used in the transportation sector rely on wireless communications. Cryptography is intended to maintain the privacy and integrity of information exchanged between two entities over a network and contributes to the verification of sender authenticity. Smart cards (or smart tokens) and digital certificates help to authenticate users. Biometric devices help to authenticate human beings through a physical attribute such as a fingerprint or voice pattern.
ASSESSING POTENTIAL POLICY OPTIONS
Given the damage potential from cyberattacks on freight transportation IT systems, public and private options for enhancing cybersecurity should be identified and developed. The actual vulnerabilities, risks, and consequences of such attacks have not yet been determined, analytically or otherwise, for the various modes. Furthermore, no mechanism now exists for determining how much security is enough or which steps could be identified as having the highest priorities. Additional study as suggested here is intended to lead to a strategy for these issues.
A strategy to reduce vulnerability must account for the company composition and structure in each mode and the operations the companies perform. It must be based on an analysis of security gaps, the costs and benefits of current and emerging technologies and processes that could be implemented to enhance cybersecurity, and the ability of transport companies to implement them. The analysis that would permit such a strategy to be developed has not yet been conducted.
Some security measures may improve the efficiency of operations and pay for themselves as normal investments. Although they may not necessarily be a company’s investment of choice, such measures would at least be of interest and should be a special focus of the proposed study. Other measures are expensive but may be effective in reducing the likelihood or consequences of a cyberattack. In such cases, the main beneficiary may be the public rather than the company that implements the measure. Since the risk of an attack cannot be specified and factored into the costs and benefits of preventing it, prioritizing potential steps to reduce vulnerability to cyberattacks is important.
The purpose of this report is to determine how such a study should be structured and the issues that it should address. It does not present a plan for implementing cybersecurity measures. As far as possible within the limited scope, the measures that might be considered and how they might apply to the freight transportation system are reviewed. Several concepts for further study are then suggested in order to develop a strategy for possible steps to reduce the sector’s
potential vulnerability to cyberattacks in the least costly and disruptive way. More detail can be found in Chapter 3.
Task 1. Determine the chief vulnerabilities of freight transportation information systems. The first step is to identify and describe the main information systems used in the transportation sector and to understand the role they play in normal operations. These systems should then be analyzed for potential cybervulnerabilities. Much of this analysis would reflect IT vulnerability studies in general, but the specific use of the technologies in the freight industry would have to be reviewed in depth. Detailed information might be obtained with a series of interviews and perhaps a survey (if consistent with current administration requirements). The objective would be to develop a sufficiently detailed system description in a format appropriate for security analyses.
A variety of plausible attack scenarios would then be used to assess the systems as they exist now and as they may evolve, and the consequences should they be attacked successfully. The purpose would be to develop a full understanding of the kinds of vulnerabilities that should be accorded the highest priority. Analyses are then required of the expected costs (including interference with normal operations) in countering these specific types of potential vulnerabilities within each modal setting. Prioritization might be determined by combining the consequences of a successful exploitation of a vulnerability, the likelihood that such an attack could be mounted, the costs of reducing the vulnerability, and the impact on normal operations. While this prioritization could be done subjectively, it might also be possible to develop a methodology to do so more analytically. In either case, it is important that a system-level perspective be used to identify, assess, and compare the security issues at the level of components, subsystems, and the overall system.
Task 2. Review current industry and government practices addressing IT security. Security practices will be difficult to obtain in detail. Most companies will be understandably reluctant to discuss their practices and protective hardware and software because of concerns that any revelations could compromise security. It may be possible, as in Task 1, to obtain the information by interviews conducted under stringent assurances of nondisclosure. Companies and government agencies might be presented with a menu of security options and asked what they use. The effectiveness of these options, however, often lies in the stringency with which they are implemented. That
information will be even more difficult to procure. Interviewers must be well versed in the technology and its use, and they must be prepared to probe for details. The main purpose of this effort is to determine how the vulnerabilities and risks identified in Task 1 are being addressed.
Task 3. Determine the potential for IT-related security enhancements in the sector. This task is, in part, a follow-up to Task 2. Current and emerging technologies and practices should be examined to determine what role, if any, they could play in addressing identified security gaps and deficiencies. Integral to this assessment should be an understanding of the characteristics of the industry and an analysis of how realistic and attractive these technologies and practices would appear to decision makers. A key part of the study should be to research the costs and benefits of security measures as they might be implemented in the freight transportation sector. Other concepts might require government support because the benefits do not outweigh the costs to the company. Because IT costs may decline over time and with increasing scale of deployment, this task should also consider the feasibility of strategies that might make promising security measures more attractive.
Task 4. Analyze policies to reduce cybervulnerability. The U.S. government could play a useful role in disseminating information on new security options and best practices. It also might evaluate the extent to which these options were being implemented. This task could include the development of a set of cybersecurity guidelines and recommendations and consideration of how to promote their use most effectively in the freight transportation industry.4 Part of the task might be to cooperate with companies in performing security audits, perhaps including “red teaming” to test security, and in other joint private–public initiatives. The same tests should be applied to the government’s connections to the private-sector IT systems.
Task 5. Assess the economic impact of cost increases in the freight transportation industry. Some cybersecurity measures may supply economic benefits as well as security, as illustrated in Figure ES-1. For example, the use of digital signatures might reduce costs related to fraud detection and manage-
|
4 |
The Administration released a national cybersecurity plan in February 2003 (see news.com.com/2100-1001-984697.html). |
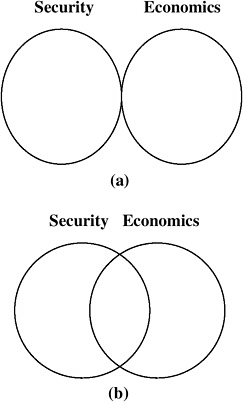
FIGURE ES-1 Relationship between security and economic benefits: (a) little or no economic benefit to security enhancements; (b) significant economic benefit to security enhancements.
ment and increase customer confidence. Other measures might protect against low-likelihood but very high-consequence events—for example, involving weapons of mass destruction. Such measures may have a high public value without significantly benefiting the company that implements them, which could result in economic inefficiency for the industry and the national economy.
This task should deal with but not be limited to the following issues:
-
At what levels and distribution of costs for security does the economic impact become a concern, both for the freight industry itself and its users?
-
On the basis of existing models for relating economic inputs and outputs, what changes in economic outputs might result from varying levels of investment in security?
-
Given the tight profit margins associated with the freight industry, is there a significant possibility of economic damage to the companies that constitute this industry?
-
For investments that may be needed for national security purposes but that provide little or no advantage to the company implementing the measures, what form of government participation (e.g., tax credits) would be most effective?
Results should be quantitative and be developed for a wide set of assumptions in order to permit consideration of a significant range of possible outputs.
REFERENCES
ABBREVIATION
NRC National Research Council
Anderson, P. L., and I. K. Geckil. 2002. Flash Estimate: Impact of West Coast Shutdown. Anderson Economic Consulting Group, Lansing, Mich., Oct. 15.
NRC. 2002. Making the Nation Safer: The Role of Science and Technology in Countering Terrorism. National Academies Press, Washington, D.C.












