4
Clandestine Stocks and Production of Nuclear Weapons and Nuclear-Explosive Materials
We concluded in Chapters 2 and 3 that procedures and technology are available to verify with high confidence declarations of stockpiles of nuclear weapons and nuclear-explosive materials (NEM) at declared sites. But undeclared nuclear weapons and NEM could exist as a consequence of retention of undeclared existing nuclear weapons and NEM or could come into existence by the clandestine production of nuclear weapons from existing NEM. In addition, undeclared NEM for weapons might be produced clandestinely or diverted covertly from peaceful nuclear power programs. Current non-nuclear weapon states and possibly terrorist groups might also acquire nuclear weapons or NEM. The potential for clandestine activities in these categories poses the largest challenges to efforts to strengthen transparency and monitoring for nuclear weapons, components, and materials on a comprehensive basis.
This chapter addresses those challenges, asking how and to what degree other states could gain confidence that undeclared nuclear weapons and stocks of NEM do not exist and are not being produced at clandestine facilities. Accordingly, we describe tools and techniques that could be used for two interrelated tasks: (1) to detect undeclared stocks and production activities that might exist and (2) to narrow the uncertainties in declarations that could mask such clandestine activities.
Table 4-1 highlights the key routes by which a state might retain or acquire undeclared nuclear weapons. The most straightforward of these is the retention of existing nuclear weapons at clandestine sites. A state wishing to cheat would simply move some number of weapons to a secret facility and provide a false declaration indicating that these weapons had never been produced or that they had long ago been dismantled. Alternatively, new nuclear weapons could be assembled at a clandestine facility. In this case,
the required NEM could be supplied from existing undeclared stocks or could be newly produced at undeclared production facilities. We first discuss tools and techniques for detecting clandestine stocks of nuclear weapons or NEM, if they exist, and then turn to the problem of detecting clandestine production of weapons and NEM. In both cases, we attempt to estimate very roughly the maximum size of an undeclared stockpile or production activity that might go undetected.
TABLE 4-1 Routes to Undeclared Nuclear Weapons
|
Route to undeclared nuclear weapons |
Source of NEM |
|
|
None Required |
|
|
|
|
|
|
These highlighted routes to undeclared weapons are the principal focus of this chapter. Covert diversion of NEM from declared stocks or production facilities was considered in Chapter 3, where we concluded that the application of safeguards like those used by the International Atomic Energy Agency (IAEA) should be able to detect any significant diversion. We also do not consider here the problem of overt breakout—that is, the open diversion of NEM from declared stocks or production facilities—because this would provide timely warning that the state may be producing undeclared nuclear weapons, which is the purpose of the monitoring system. Nor do we discuss the possibility of theft or transfer of nuclear weapons or NEM from other states. We assume that any significant theft would be detected, and the transfer of weapons or NEM would only shift the problem of detecting a false declaration from one state to another (provided that all such states were subject to equivalent monitoring and safeguards arrangements).
DETECTING UNDECLARED STOCKS OF WEAPONS AND NEM
In order to gain confidence that declarations are complete and that no undeclared stocks of nuclear weapons or NEM exist, states or an inspection agency must have an ability to collect direct or circumstantial evidence of undeclared stocks if they do exist. Direct evidence would be the actual discovery of undeclared weapons or NEM. Circumstantial evidence would include audits of records and physical evidence from which one could infer that it is likely that undeclared nuclear weapons or stocks of NEM exist at some unidentified location.
If a state agreed to declare all of its nuclear weapons and all stocks of NEM, then the discovery of a single weapon or container of NEM not listed in the declaration would ipso facto be a violation of the agreement, unless promptly and satisfactorily explained. As noted in previous chapters, an agreement to tag all declared nuclear weapons and containers of NEM would greatly facilitate monitoring, because the discovery of a single weapon or container without a valid tag would be direct evidence of a violation. If tags are not used, the state might claim that the discovered weapons or containers of NEM were not properly listed in the declaration because they had been moved recently and the declaration had not been updated accordingly, or some other excuse that would be difficult to refute incontrovertibly.
National Technical Means
The main problem with discovering undeclared stocks is knowing where to look. Existing storage facilities for nuclear weapons and NEM, such as the bunkers shown in Figure 2-3, are distinctive and easily detected and identified using National Technical Means (NTM), in particular high-resolution satellite photography.1 Any such facilities that were omitted from the declaration would be high priorities for challenge on-site inspections. But a state wishing
to cheat could be expected to select a building that would give few indications of its contents, such as a warehouse in an industrial complex, with few outward signs of high security or other activities usually associated with the storage of nuclear weapons or NEM. Nuclear weapons and containers of NEM are small—even a house-size building could hold hundreds of weapons (or enough NEM for hundreds of weapons). The number of personnel and traffic to the clandestine facility could be kept to a minimum and given a plausible cover story. NEM components or containers of bulk material need little or no maintenance. Nuclear weapons require periodic inspections and the replacement of limited-life components, such as batteries or tritium, but this could be accomplished without attracting attention. If necessary, weapons and materials could be moved between clandestine facilities using commercial vans or trucks, with no security escort.
Nuclear weapons and NEM give few clues about their existence within a facility. NEM emits neutrons and gamma rays, but these radiations are easily shielded and are detectable only at relatively short range (on the order of 100 meters or less) even without shielding. Barring a severe accident, such as the detonation of the high explosive in a weapon, the likelihood that a clandestine storage facility would be detected using NTM probably would be low. One might intercept communications indicating suspicious activities that may be related to nuclear weapons or NEM, but such opportunities would be limited given the relatively low level of activity and small numbers of people required to maintain clandestine stocks.
Human Sources
The surest way to locate a clandestine storage facility for undeclared nuclear weapons or NEM is through human intelligence—for example, the leak of information by someone who has knowledge of the hidden stocks. Governments have varied in their ability to maintain secrecy. The case of Mordechai Vanunu, a nuclear technician who claimed to have personal knowledge of Israel’s undeclared nuclear weapon activities, was widely publicized. Even oppressive and secretive governments such as Iraq and North Korea have experienced high-level defectors. While in the United States the secrecy of some major programs was apparently well kept, the general outlines of the Manhattan Project, as well as many sensitive technical details, were known to the Soviet Union through individuals associated with the U.S. nuclear weapons pro-
gram. Over the years, there have been many serious leaks from highly sensitive U.S. and Soviet programs, motivated by ideology or greed. The extent to which a covert program may have been compromised by individuals within the program or by knowledgeable outsiders can never be known with certainty by a state undertaking the secret program.
One may be able to increase the probability that individuals would report activities that contravene international agreements to international authorities. If the individuals most likely to have knowledge of undeclared activities can be identified, inspectors can request confidential interviews with these people. Such interviews have been used by the IAEA to resolve uncertainties and investigate possible violations of safeguards agreements. Individuals also could be encouraged to come forward on their own, by requiring that states pass domestic laws making it illegal for individuals to participate in activities that contravene an international agreement, requiring that individuals report violations to a designated international commission, and guaranteeing immunity for the “whistle blowers.” This concept, which is sometimes called “societal verification,”2 received a favorable review by former Under Secretary General for Disarmament Affairs of the United Nations, Jayantha Dhanapala.3 Societal verification might serve as an additional deterrent to governments contemplating whether to establish a clandestine stockpile of weapons or NEM. A government wishing to cheat would attempt to screen participants to eliminate potential whistle-blowers, but it could never be absolutely and forever certain of their loyalty to the regime.
|
2 |
Joseph Rotblat, “Societal Verification,” in Joseph Rotblat, Jack Steinberger, and Bhalchandra Udgaonkar, eds., A Nuclear-Weapon-Free World: Desirable? Feasible? (Boulder, CO: Westview Press, 1993), pp. 103-118. Joseph Rotblat, “Citizen Verification,” Bulletin of the Atomic Scientists 48 (May 1992), pp. 18-20 and Richard L. Garwin, Appendix H “Theater Missile Defense, National ABM Systems, and the Future of Deterrence,” in Naval Studies Board, National Research Council Post-Cold War Conflict Deterrence (Washington, DC: National Academies Press, 1997), pp. 182-200. Available as of January 2005, at: http://bob.nap.edu/html/pcw/Dt-h.htm. |
|
3 |
Jayantha Dhanapala, “Civil Society and the Verification of Disarmament,” workshop on “Societal Verification” at the Hague Appeal for Peace conference, May 13, 1999. Available as of January 2005, at: http://www.un.org/Depts/dda/speach/13May1999.htm. |
Audits of Records
The probability that clandestine stocks would be discovered and directly observed cannot be assumed to be high. Fortunately, there are ways that an inspection agency or other states might gather circumstantial evidence of the existence of undeclared nuclear weapons and stocks of NEM. One can examine the original records for the assembly and disassembly of nuclear weapons and the production and use of NEM, for example, to check their authenticity, internal consistency, and consistency with the declaration and with intelligence information. An examination of operating records is similar to a financial audit, in which a company’s records are examined to verify the legitimacy and accuracy of transactions, and that balances accurately reflect receipts and disbursements. It is reasonable to assume that the assembly and disassembly of every nuclear weapon was documented in the operating records of each assembly facility. The declared inventory of each weapon type should equal the total recorded number assembled minus the number disassembled. In order to hide existing nuclear weapons, the records would have to be falsified to indicate either that the hidden weapons had never been assembled, or that they had been disassembled or explosively tested at an earlier date.
The authenticity of original paper records, if they still exist, could be verified using standard forensic techniques, which should be able to detect any recent alterations. The records also could be examined for any unusual patterns—for example, periods of low assembly or high disassembly rates or of highly uniform assembly or disassembly rates—that might indicate attempts to falsify the records to hide the existence of undeclared weapons. Finally, archived national intelligence information could be checked for consistency with the operating records provided. Imagery taken by photoreconnaissance satellites might show activity at variance with the records—for example, movements of large numbers of weapons out of or into the plant during periods when the operating records showed little or no activity.
Operating records for NEM production facilities also could provide evidence about the existence of undeclared weapons, or undeclared stocks of NEM that could be used to assemble them. The declared inventories of highly enriched uranium (HEU) and plutonium should be consistent with original records for the production and use of these materials, and the records should be internally consistent. In the case of a uranium enrichment plant, for ex-
ample, the recorded receipts of uranium entering the plant as feed should be consistent with recorded shipments of HEU and discharges of depleted uranium. Over a given period, the mass of uranium and U-235 in the feed should equal the masses of uranium and U-235 in the HEU and the depleted uranium combined, with some margin of error due to measurement uncertainties. In addition, records of the separative work performed could be compared with the capacity of the plant, which can be verified through design documents and on-site inspections.
The material balance will depend on the design and operation of the plant, but for illustration, consider a plant that produces HEU and depleted uranium with U-235 concentrations of 90 percent and 0.35 percent, respectively. For every 1,000 kilograms of natural uranium entering the plant, 4 kilograms of HEU and 996 kilograms of depleted uranium are produced. The feed contains 7.1 kilograms of U-235, of which 3.6 kilograms goes into the HEU and 3.5 kilograms goes into the depleted uranium.
Similar methods could be applied to verifying declarations of plutonium production. This would involve examining records of the fabrication of uranium fuel and target rods for production reactors; the design of the fuel and the reactors, typical fuel loadings in the core, and dates of fuel loading and discharge; monthly production of thermal energy; shipments of spent fuel; the design of the reprocessing plants; monthly production of plutonium product; and the volume, isotopic composition, and disposition of the various waste streams.
As with weapons, archived intelligence information might be checked for consistency with the records; for example, imagery of a plutonium production reactor or a gaseous diffusion enrichment plant could indicate whether the plant is operating and, at least roughly, the level of production. Production records for NEM could also be checked for consistency with records for weapon assembly. In the case of gaseous diffusion plants, records of enrichment work performed might also be checked against records of electrical consumption.
This method of verifying production declarations would depend on the accuracy, completeness, and authenticity of the records that were provided. As noted above, the authenticity of paper records can be verified, but the original records might have been lost or destroyed, and electronic records may be impossible to authenticate. Moreover, even authentic records may be unintentionally inaccurate or incomplete. Record keeping was not exemplary
in the early days of most nuclear weapon programs, when the emphasis was on producing material and weapons as quickly as possible. Although record keeping presumably was good for weapons, plutonium, and HEU, it is less likely that accurate records were kept for less valuable materials, such as natural or depleted uranium or reprocessing wastes, which are important for accounting purposes.
Physical Evidence
A variety of methods exist for gathering physical evidence that could be used to confirm NEM production records and resolve uncertainties or apparent discrepancies in them. These methods are sometimes referred to as “nuclear archaeology.” In the case of graphite-moderated plutonium production reactors, for example, isotope ratios of impurities in the graphite can provide an accurate estimate of the total integrated neutron flux that was available to produce plutonium during the life of a reactor.4 Isotopes of various common impurities capture neutrons and produce heavier isotopes of the same element. The ratios of the resulting stable isotopes can be accurately measured by mass spectrometry. By comparing these isotopic ratios with those occurring naturally, the integrated neutron flux at the point of capture can be determined. This method is particularly attractive in that it does not depend on the original concentration of the impurity in the tested items, but only on the ratios of remaining isotopes. A model of the neutron flux with the reactor, however, is essential to relate such measurements accurately to the plutonium produced during the life of the reactor.
Titanium has been identified as a particularly attractive impurity for this purpose. A number of other elements that exist as impurities in graphite would allow independent checks. Measurements of titanium isotope ratios in graphite core samples reportedly can give error margins as low as 2 percent on total plutonium production, assuming that the relevant neutron capture cross sections will be measured more accurately.5 For a relatively small cost, the plutonium production from all of the 13 former graphite-moderated Soviet production reactors, which produced essentially all the Russian Federation’s plutonium, could be esti-
mated in this way. The Russian Federation has made plans to entomb the closed-down production reactors under radiation barriers, after which it will be much more difficult and expensive to carry out nuclear archaeology. As of early 2005, however, these plans had not moved forward, so the opportunity remains. Although there have been discussions of a joint U.S.-Russian experiment on one of the reactors and some proposals have been developed, it had not been funded as of early 2005.
The United States has used both graphite- and heavy-water-moderated reactors to produce plutonium. The nine graphite-moderated reactors at Hanford reportedly produced 76.4 tons of plutonium; with an accuracy of 2 percent this implies an uncertainty of about 1.5 tons. The five heavy-water-moderated reactors at Savannah River produced 36.1 tons of plutonium. A comparable technique has not yet been developed for heavy-water reactors, and the fractional uncertainty would most likely be larger.
In principle, the cumulative production of HEU could be calculated by determining the total amount of U-235 stripped from the stocks of depleted uranium produced by the enrichment facility. In practice, however, a comprehensive inventory of depleted uranium stocks of U.S. and Russian would be very difficult and costly, and the resulting estimate of HEU production probably would not be sufficiently accurate to be useful. As an indication of the magnitude of the problem, the U.S. Department of Energy stores about 500,000 tons of depleted uranium, mostly in the form of uranium hexafluoride in some 60,000 steel cylinders at three U.S. enrichment plants. This depleted uranium resulted from the production of HEU at various enrichment levels for nuclear weapons and fuel for naval, research, and test reactors, as well as LEU at various enrichment levels for civilian reactor fuel. Moreover, the isotopic composition of the feed varied significantly, including partially depleted and slightly enriched uranium recovered from irradiated reactor fuels in addition to natural uranium. Finally, a small fraction of the depleted uranium discharged from U.S. enrichment plants has been used for various defense and commercial purposes, such as tank armor, armor-piecing munitions, ballast, and radiation shielding. Russian stockpiles of depleted uranium are likely comparable in size and in the complexity of their production history.
Information from depleted uranium might be useful in cross-checking production records, however. It would be possible, for example, to date accurately the contents of the individual cylinders of uranium hexafluoride using the decay products of the uranium
isotopes, and to determine by the ratios of U-234 to U-235 whether these particular tails resulted from the production of HEU or low enriched uranium (LEU).6 If the depleted uranium cylinders are numbered and if these numbers are documented in the operating records, measurements on a random sample of cylinders could be used to confirm the accuracy of the records.
South Africa: Verifying the Completeness of Declarations
South Africa presents an important case study in verifying the completeness of declarations. Having built six gun-type nuclear weapons during the 1980s, South Africa decided to dismantle its weapons and join the Nuclear Non-Proliferation Treaty (NPT) as a non-nuclear weapon state. Beginning in July 1990, South Africa dismantled all its weapons, decommissioned its production and assembly facilities, and recast the HEU weapon components into standard shapes for storage and international inspection.
In March 1993 President de Klerk announced that South Africa had built and dismantled six nuclear weapons. The IAEA was given a full history of the nuclear weapon program, along with a list of the people involved in it. The agency was granted permission to conduct inspections at any relevant location and to interview former managers and workers about the program. A special team of inspectors easily confirmed that the declared amount of HEU had been placed in storage and that weapon-related activities had ceased at various declared facilities. Verifying that the declaration was complete—that South Africa had dismantled all of its weapons and placed all of its HEU under safeguards—was considerably more difficult, however.
The IAEA requested the historical production records from South Africa’s uranium enrichment plant. Inspectors used these records, along with other technical and design documents, to recalculate the plant’s daily production over the entire period and to produce an overall material and isotopic balance. On the basis of these studies, together with examination of the facilities and interviews of facility personnel, the IAEA concluded that the amount of HEU that could have been produced was consistent with the amount in South Africa’s initial declaration within an acceptable margin of uncertainty—less than 25 kilograms, or roughly 5 percent of the declared inventory of HEU. The IAEA therefore con-
cluded that there was no evidence that South Africa’s declaration was incomplete; that is, there was no evidence of the existence of undeclared weapons or significant amounts of undeclared HEU.7
A comprehensive assay of the 370 tons of depleted uranium tails, which are stored on-site in some 600 cylinders, would have reduced somewhat the uncertainty in the material balance, but the IAEA decided that the increased confidence provided by such measurements would not justify the considerable expense. Measurements of certain samples were performed, however, which confirmed IAEA calculations (based on the original production records) indicating that substantially more U-235 was contained in the depleted uranium than had been recorded in the official accounting records. These measurements were an important piece of evidence that allowed the IAEA to conclude that there was no evidence of any missing HEU.
The IAEA experience in South Africa illustrates that high confidence in the completeness of declarations can be achieved with a high level of cooperation and transparency. But it also demonstrates that uncertainties will exist and may be difficult to resolve. Verifying South Africa’s HEU declaration was complicated by the fact that uranium had also been enriched for nonweapons purposes, and poor records were kept of wastes and materials not valuable for the weapons program. According to then-Director General Hans Blix, “There is inherent difficulty in verifying the completeness of an original inventory in a country in which a substantial nuclear program has been going on for a long time.”8 The irony is that South Africa’s nuclear program, which produced a total of six weapons, may prove to be the smallest and shortest lived of all programs that produced a nuclear weapon. We believe that the difficulties experienced by the IAEA in verifying South Africa’s declaration are likely to be much more difficult for the de jure nuclear weapon states, making it much more difficult to conclude that their declarations are complete.
|
7 |
Adolf von Baeckmann, Gary Dillon, and Demetrius Perricos, “Nuclear Verification in South Africa,” IAEA Bulletin, 37 (March 1995). Available as of January 2005, at: http://f40.iaea.org/worldatom/Periodicals/Bulletin/Bull371/baeckmann.html. |
|
8 |
Hans Blix, Statement to the 36th Session of the General Conference of the IAEA, Sept. 21, 1992. |
Uncertainties in Weapon and NEM Stockpiles
As noted above, if a country retained undeclared stocks of weapons or NEM, there would be some chance that these would be detected and directly observed as a result of intelligence collection or information provided by individuals with knowledge of the stocks. If original operating records had been falsified to hide the existence of undeclared stocks, detection of such falsifications would be seen as convincing evidence of an attempt to cheat. Otherwise, the only evidence of hidden stockpiles would be an imbalance of NEM calculated or inferred from an examination of the operating records and physical inventories. Here we consider the likelihood that the existence of undeclared stocks of NEM could be inferred based solely on these statistical methods. The actual likelihood of detecting undeclared stocks of a given size would be greater than given here, however, because of the other possible sources of information listed above.
Even the most exhaustive examination of operating records and the most thorough physical inventory is likely to result in NEM estimates with a margin of error of at least a few percent. As discussed in Chapter 3, the official U.S. estimate of the total amount of plutonium produced or otherwise acquired by the United States is 2.8 tons greater than the measured amount of plutonium in current stockpiles plus the estimated amounts removed from the inventory in nuclear tests, wastes, reactor burnup, and other transfers. This “inventory difference,” which amounts to 2.5 percent of total plutonium production, is the combined result of errors in measurement and record keeping, overestimates of the amount produced in reactors, and underestimates of the amount of plutonium in wastes. Inventory differences for HEU production are likely to be even larger.
All things considered, the accounting uncertainties in plutonium and HEU stocks are likely to be no smaller than 2 and 4 percent, respectively.9 To put this in perspective, Table 4-2 expresses the estimated uncertainties in total plutonium and HEU inventories of the de jure and de facto nuclear weapon states in terms of an approximate number of “Significant Quantities” as defined by the
IAEA.10 The amount of material that could be diverted, however, with low probability of arousing suspicion by statistical means alone is much smaller—roughly five times smaller than these accounting uncertainties (see Box 4-1). Based on this, as well as the fact that nuclear weapon states could produce more than one nuclear weapon per significant quantity (see below), we judge that Russia and the United States probably could confidently conceal from statistical detection undeclared NEM stocks equivalent to several hundred nuclear weapons; the United Kingdom, France, and China could conceal undeclared stockpiles equivalent to one or two dozen weapons; and Pakistan, Israel, and India may be able to conceal enough NEM for at most one or two weapons.
TABLE 4-2 Uncertainties in Plutonium and HEU Inventories (Number of Significant Quantities)
|
|
2% of Estimated Pu Inventory |
4% of Estimated HEU Inventory |
Total SQ |
|
Russia |
400 |
1700 |
2000 |
|
United States |
250 |
1100 |
1400 |
|
France |
10 |
50 |
60 |
|
United Kingdom |
20 |
40 |
50 |
|
China |
10 |
30 |
40 |
|
Pakistan |
|
2 |
2 |
|
Israel |
1 |
|
1 |
|
India |
1 |
|
1 |
|
North Korea |
<1 |
|
<1 |
|
One Significant Quantity is defined by the IAEA as 8 kilograms of plutonium or 25 kilograms of HEU. The sum of the Pu and the HEU may not add up to the total due to rounding. Adapted from: David Albright, Global Fissile Material Inventories, June 2004. Available as of January 2005, at: http://www.isis-online.org/global_stocks/tableofcontents.html. |
|||
|
10 |
As noted in Chapter 3, a Significant Quantity is the amount of NEM the IAEA considers sufficient to manufacture a first nuclear weapon; it is defined as 8 kilograms of plutonium or 25 kilograms of HEU. |
|
BOX 4-1 A common misperception is that a party could divert material up to the accounting uncertainty without fear of detection. To see that this is incorrect, assume that the inspected party’s total stock of NEM is 100 tons and that the uncertainty in the inspecting party’s estimate of this stock is ±2 tons. The figure below gives the probability that an undeclared stock of a given size would escape statistical detection (i.e., that the declared stock would fall below the 95% confidence interval estimated by the inspecting party). For example, if the inspected party failed to declare 0.4 tons (one-fifth of the accounting uncertainty), the probability that this undeclared stock would escape detection is 94%. Note that the probability of escaping detection drops sharply as the size of the undeclared stock increases beyond this point. Thus, the inspected party could not be highly confident that undeclared stocks much larger than one-fifth of the accounting uncertainty would escape statistical detection by the inspecting party. 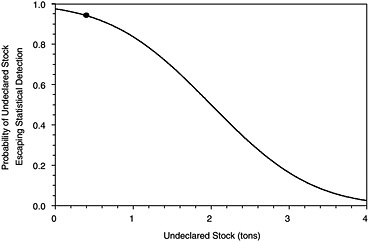 The actual situation would be more complex for a number of reasons. First, the above example assumes that the inspecting party’s estimate of the actual stock is unbiased, but bias of some type is inevitable and is difficult to evaluate quantitatively. Second, the uncertainty in the inspecting party’s estimate (and any bias that |
|
may exist) would depend on the inspection process itself (e.g., examination of records, physical measurements, etc.) and would not be known in advance, complicating assessments of the size of the undeclared stock that would confidently escape detection. Third, the inspecting party’s interpretation of the results would depend on its prior estimate of the probability that the inspected party is cheating (see Footnote 18 in chapter 2). If the inspecting party’s prior probability of cheating is high (because of other suspicious behavior or evidence), then declarations that lie below the estimated confidence interval would greatly strengthen the case that the inspected party was cheating. |
These uncertainties are associated with the stock of NEM. This was the only major uncertainty in South Africa’s declaration, because in this case the entire declared stock of HEU was available for inspection. But if a state also maintains substantial declared stocks of nuclear weapons or weapon components, the inspecting party would also have to consider uncertainties in its knowledge about the amount of NEM in these weapons and components. Suppose, for example, that a state declared a total stockpile of 500 kilograms of plutonium, contained entirely in 100 weapons. Even if the inspecting party was absolutely confident that the state had produced no more than 500 kilograms of plutonium, it could not be sure that there were no undeclared weapons unless it could also confirm the amount of plutonium in the declared weapons. If the declared weapons each contained 4 kilograms of plutonium, then there might be a hidden stockpile of 25 undeclared weapons.11
For this reason, we believe it would be very helpful if declarations specified the amount of NEM in each type of weapon. These amounts, which the nuclear weapon states currently consider highly classified information, might vary by a factor of two or more between different weapon designs. Although existing techniques and procedures could be adapted to permit verification of declared amounts of NEM in randomly selected weapons without revealing other sensitive weapon design information, this degree of transparency probably is not acceptable to the nuclear weapon
states under current conditions. As explained in Chapter 2, such sensitive information could initially be exchanged in encrypted or digest form, to be decoded only by mutual agreement to resolve questions in connection with verifying declarations in the event that arsenals were reduced to low levels where high accuracy of accounting would take on added significance.
If substantial numbers of nuclear weapons were disassembled and their NEM components converted into bulk materials while declarations and associated transparency measures are in place, the inspecting party would over time develop increasing confidence in the declared amounts of NEM in the remaining weapons and components. For instance, if in the above example the state dismantled 50 weapons of a given type and in the process turned over 250 kilograms of plutonium, then one could be reasonably confident that the remaining 250 kilograms was contained in the 50 weapons remaining in the declared stockpile.
DETECTING UNDECLARED PRODUCTION OF WEAPONS AND NEM
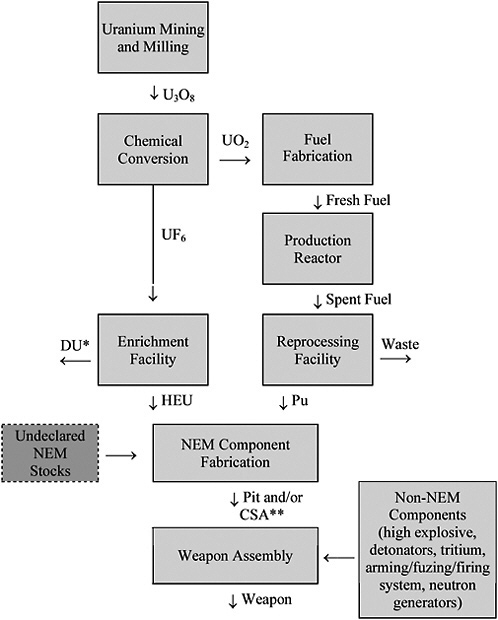
The other main route to the acquisition of undeclared nuclear weapons is to produce new weapons in undeclared production and assembly facilities. The key elements of such a program are shown in Figure 4-1. We assume that most or all of these activities would occur in clandestine facilities, because the monitoring and inspection procedures discussed in Chapters 2 and 3 would be designed to prevent the undetected use of civil or other declared facilities for significant undeclared activities.
A complete program to produce nuclear weapons is a substantial undertaking, even for a highly experienced and technologically advanced state. Many of the activities shown in Figure 4-1 would be difficult to conceal in a cooperative environment in which a country is required to declare all of its nuclear facilities and is subject to routine inspection of these facilities and challenge inspections of any suspicious activities. In general, the construction and operation of facilities for the production of NEM are the most easily detected activities. Detection would be more difficult if the weapon program were embedded in a large civil nuclear program, and more difficult still if NEM were obtained from existing clandestine stocks or from an external source, obviating the need for telltale production facilities.
There are a number of powerful tools available to the United States and the international community, including national technical means, human intelligence, and environmental monitoring, that are able to gather evidence of any clandestine nuclear activities that may exist. These tools would be most effective in conjunction with the right to obtain confirmation by on-site inspections of suspicious activities that have been identified.
National Technical Means
The principal means of uncovering evidence of clandestine production of NEM or nuclear weapons would be provided by NTM; for example, mining and milling operations can easily be identified using photoreconnaissance satellites. A clandestine program to produce 10 Significant Quantities of HEU or plutonium per year would require 40 to 80 tons of natural uranium per year,12 as well as chemical facilities to convert it into forms appropriate for enrichment or fuel fabrication. Extending declarations to include the location of uranium mines would make undeclared uranium mining and milling activities more vulnerable to detection. Inspectors could visit a random sample of mines in districts where it is believed that uranium ores are present in order to confirm the absence of undeclared uranium mining and milling operations. Extending safeguards to include yellowcake production would make it difficult to divert uranium from safeguarded mills to clandestine chemical conversion facilities. NTM (e.g., signals intelligence) could also detect attempts to secretly import uranium from other countries.
Existing plutonium and HEU production facilities are quite distinctive and are easily detected and identified using photoreconnaissance satellites. A state wishing to cheat would, of course, attempt to hide or disguise the construction and operation of undeclared facilities, but this is practically impossible for plutonium production. Although a clandestine reprocessing facility might conceivably be hidden underground, it would require an undeclared source of spent fuel. A plutonium production reactor is
necessarily a large facility with special features and equipment. Even if the reactor itself could be hidden (which seems unlikely), the unavoidable discharge of waste heat into the environment would be detectable by infrared sensors on satellites. A reactor capable of producing 10 Significant Quantities of plutonium per year would have a thermal power of about 250 megawatts—equal to the heat output of a small city.
The gaseous diffusion enrichment plants built by several of the nuclear weapon states are easy to detect by virtue of their enormous size, electrical power requirements, and heat output. A small gas centrifuge enrichment plant, on the other hand, would be much easier to conceal or disguise. A plant capable of producing 10 Significant Quantities of HEU per year would require on the order of 10,000 centrifuges, with a floor area of roughly 10,000 square meters and a power consumption of about 300 kilowatts, which is comparable to many large commercial and industrial buildings.13
The final steps are the fabrication of weapon components and assembly of the weapon. Although in the past these activities typically have been conducted in distinctive facilities, this need not be the case, particularly if a state is willing to accept lower levels of safety and security. Among the most distinguishing features of the U.S. Pantex weapon assembly facility, for example, are the assembly cells, which are designed to withstand the accidental detonation of high explosives and prevent dispersal of plutonium. If a state were willing to accept higher risks of theft and dispersal of NEM and higher risks to worker health and safety, component fabrication and weapon assembly could take place in almost any large building.
The physical appearance of facilities can give important clues about their function and possible relationship to a clandestine weapon program, but this is only one piece of the intelligence puzzle. The flow of special materials, equipment, and components—particularly items imported from other countries—and particularly the intercept of communications between certain individuals also can provide valuable information about the existence and location of undeclared activities, which can then be used to focus attention on particular facilities.
Human Sources
NTM is supplemented by information from various human sources, including reports in the open literature, travelers, defectors, and individuals within the program itself. As noted above, the likelihood that individuals with knowledge of illegal activities would report these violations to international authorities can be enhanced in a number of ways. Human sources are likely to be much more valuable in detecting the undeclared production of nuclear weapons or NEM, compared with the detection of undeclared stocks, simply because of the far greater number of individuals that would be involved in building and operating production facilities. The secret South African weapons program, for example, which produced six nuclear bombs, reportedly employed a total of 1,000 people (but no more than 300 at any one time);14 thousands more were likely employed in nonsecret uranium mining and milling, chemical conversion, and uranium enrichment operations. Although a completely clandestine program conducted by a state experienced in nuclear weapons technology could be smaller, at least several hundred people would be required. A state wishing to cheat could compartmentalize knowledge and attempt to deceive workers about the true nature of the program, but this would be difficult in an environment where it is widely known that all nuclear activities must be declared and are subject to inspection by international authorities. A leak or defection by only one of the hundreds of people involved could be enough to expose the program and trigger requests for on-site inspections of undeclared production facilities.
Environmental Sampling and Monitoring
The processing and enrichment of uranium, the operation of a nuclear reactor, and the reprocessing of spent reactor fuel inevitably release materials into the environment that are uniquely characteristic of these activities. These effluents can be in the form of gases, liquids, and fine particles released during normal facility operations or during accidents. Traces of these effluents can be detected in environmental samples collected during on-site inspections at facilities or monitoring stations as a component of an agreement or NTM.
Environmental sampling is most powerful in detecting undeclared activities at declared or suspect facilities. Small particles may be deposited throughout and around a facility, both within and outside of areas where NEM and related materials are handled. These particles can be collected with “swipe samples” during on-site inspections (e.g., by wiping a piece of filter paper on a wall or the inside of a process tank). Recent examples include the collection by IAEA inspectors of plutonium particles in the North Korean reprocessing facility, and HEU particles in the Iranian centrifuge enrichment facility. The particles are analyzed using mass spectrometry to determine their elemental and isotopic composition. In this way, inspections can indicate whether uranium has been enriched or whether any reprocessing has occurred at the facility. Isotope ratios can also be used to establish whether uranium has been enriched above a given level, and the burnup of the fuel that was reprocessed and the date that reprocessing or other purification processes occurred. It is highly likely that any significant, undeclared enrichment or reprocessing operations could be detected by environmental sampling at the suspect facility.
Effluents can also be carried many kilometers downwind or downstream from the facility, where they may be detected by sampling air, soil, vegetation, water, and sediments. The Comprehensive Nuclear Test Ban Treaty (CTBT) provides for a network of 80 air-sampling stations to detect radioisotopes released from clandestine nuclear tests. Similar “wide-area” environmental sampling networks have sometimes been proposed to detect clandestine production of NEM. The ability of wide-area environmental sampling to detect such activities depends primarily on the amount of effluent released, which in turn depends on plant design as well as the diligence and experience of plant operators. Also important are meteorological conditions and the existence of background signatures produced by nearby civil nuclear facilities, fallout from atmospheric nuclear testing in the 1950s and early 1960s, and from the 1986 Chernobyl reactor accident. The sensitivity and specificity of environmental sampling are generally dependent on variables that neither the monitor nor the proliferator can reliably predict.
Many long-lived radioisotopes are produced in the fuel elements of a nuclear reactor during its operation. Some of these radioisotopes are volatile and can be released into the environment if fuel elements rupture inside a reactor, or when the spent fuel is dissolved in a reprocessing plant. The long-lived radioisotope krypton-85 is an especially valuable signature of reprocessing activity,
because it is very difficult to prevent the release of noble gases. Only extreme measures, such as cryogenically trapping all effluents, can trap noble gases. The technology to detect radioactive xenon from nuclear tests is highly developed,15 and similar techniques could be applied to the detection of radioactive krypton. Other radioisotopes, in particular cesium-137, strontium-90, plutonium-239, and plutonium-240, could be released in amounts detectable at long ranges as a result of accidents at reprocessing facilities.
Releases from uranium conversion and enrichment facilities generally are less detectable than releases from reactors and reprocessing facilities, depending on the technology used and the likelihood of accidents. Because the uranium compounds used in enrichment (e.g., uranium hexafluoride) are quickly oxidized to naturally occurring uranium compounds, only particles containing enriched (or depleted) uranium are usually detectable and would be uniquely indicative of the existence of a uranium enrichment facility. Centrifuge enrichment facilities can have extremely low routine release rates, although a large pipe break or the failure of a number of centrifuges might release significant amounts of enriched uranium into the environment. Gaseous diffusion and electromagnetic separation facilities have much larger routine release rates, but it is highly unlikely that a state wishing to clandestinely produce HEU would use these older, much less efficient, and far more detectable technologies, unless they were unable to develop or otherwise acquire centrifuge technology.
A 1999 report by an IAEA group representing 26 member states provides useful information on the sensitivity of environmental monitoring required to detect clandestine facilities producing Significant Quantities of NEM (i.e., 8 kilograms of plutonium or 25 kilograms of weapons-grade uranium annually).16 The report
relied primarily on data on historical releases from existing facilities as a reference. Releases from a clandestine facility might be considerably higher or lower, depending on the operator’s level of technical expertise and the care taken to minimize releases. In general, a technically advanced state operating with a substantial budget and without undue pressure to meet tight deadlines could be expected to build and operate a clandestine facility with very low emissions, while an inexperienced state with limited resources or an experienced state engaged in a crash program might be much less successful in controlling releases. The study concluded that air sampling was the most promising technique. In general, soil and vegetation sampling are less sensitive methods of detecting atmospheric releases, and water and sediment sampling are unlikely to be effective unless effluents are discharged directly into waterways.
The IAEA study used the known emissions from the Sellafield plant in the United Kingdom to estimate the emissions of a hypothetical smaller, clandestine reprocessing plant. The IAEA study estimated that the krypton-85 released from a small reprocessing facility could be detected by a continuous gas sampler at distances of over 100 kilometers downwind under stable atmospheric conditions, with high detection probability and low false alarm rate. The study concluded that a network of 26 sampling stations would have a high probability of detecting the operation of a clandestine reprocessing facility within the portion of a million square kilometer area of the Middle East most capable of supporting a clandestine facility.17 In addition, particulate sampling may be useful for detecting accidents at reprocessing plants. Because of the relatively short detection range and high capital and operating cost of air sampling stations, wide-area environmental sampling would be most suitable for detecting undeclared reprocessing activities over limited areas, such as the Middle East.
The IAEA study estimated releases of a mere 0.01 to 1 gram per year of HEU for a centrifuge enrichment facility producing 25 kilograms of HEU per year, based on data from existing commercial facilities. Even at the upper limit of 1 gram per year, the study concluded that a network of 26 stations could detect with high probability releases from a clandestine centrifuge enrichment facility over only a tiny fraction of a million square kilometer area of the Middle East (even after excluding the areas considered too far from roads, electricity, and people to support such a facility).18 Releases from gaseous diffusion and electromagnetic isotope enrichment plants would be much larger and more detectable. Unless substantial progress is made in reducing the cost or increasing the sensitivity of analyzing uranium particulate samples, wide-area environmental sampling would be a practical method of detecting undeclared uranium enrichment activities only over small areas, such as the Korean peninsula.
In summary, we judge that environmental samples taken during on-site inspections can be highly effective in detecting significant undeclared enrichment or reprocessing activities at declared or suspect facilities. Environmental sampling is less able to detect such activities at unidentified facilities, or to provide assurance that no significant, undeclared enrichment or reprocessing activities have occurred in a particular state. Although reliable detection of clandestine reprocessing appears possible at reasonable cost for at least limited regions (assuming that facility operators do not cryogenically trap krypton emissions), reliable detection of clandestine centrifuge enrichment over large areas currently is not possible at reasonable cost.
On-site Inspections
As discussed in Chapters 2 and 3, routine on-site inspections are vital for confirming declarations of inventories and activities at declared sites. While possibly subject to numerical quotas, such inspections at declared sites should not be subject to refusal by the party being inspected. The inspectors should be guaranteed protection and prompt unimpeded access with any equipment agreed to be necessary for inspection purposes, but agreed limitations on the
extent of access relating to the protection of sensitive weapons information could be acceptable.
If evidence of suspect activities at undeclared sites has been discovered by some combination of NTM, human intelligence, wide-area environmental sampling, or information developed in the process of routine inspections and audits of declared activities, challenge inspections would provide a mechanism for clarifying the situation. The right to conduct on-site inspections of suspect sites is provided for in the Additional Protocol to the IAEA safeguards agreements, as well as various other multilateral and bilateral arms control treaties.
The modalities of how a challenge inspection would be initiated and conducted would depend on whether an agreement was bilateral or multilateral. An existing example of the mechanism for dealing with such issues is the Joint Compliance and Inspection Commission (JCIC) established by the START I Treaty to resolve questions of compliance. The JCIC and other similar commissions have successfully resolved many issues over the past three decades. In the case of multilateral treaties various procedures have been adopted. In the CTBT, any party can request an on-site inspection for cause but at least 30 of the 51 members of the Executive Committee would have to approve the inspection; in the Chemical Weapons Convention, an inspection would proceed automatically unless it was opposed by a given number of parties. Under the Additional Protocol the IAEA must give notice of inspection at least 24 hours in advance, and give the reasons for the inspection. The rights of inspection are broad, including environmental sampling, radiation surveys, examination of shipping records, visual surveys, and so forth. Protection of “proliferation sensitive information” is provided but this protection must not prevent the agency from collecting credible assurance of the absence of undeclared NEM or of the completeness of the specified declarations.
Two questions are frequently asked about challenge inspections. First, would the United States be willing to call for a challenge inspection when the evidence for the “probable cause” could jeopardize sensitive intelligence sources and methods? Even if the source of the original stimulus for suspicion might in fact be very sensitive, we believe corroborative evidence could be made available and locations could be established using commercial satellite photography, which now has good resolution. Second, would a multilateral Executive Committee be willing to authorize an in-
spection that could have serious political or military repercussions? Once the United States requested approval from a multinational committee, we believe it should be possible to obtain the necessary support for an inspection when a convincing case could be presented. When necessary, the request could be backed up by sharing relevant classified information privately with other states or publicly as has been done in the past. In practice, the number of challenge inspections for an agreement related to nuclear weapons or NEM should be relatively few. Unless wide-area environmental sampling is used there are no natural events to trigger the system, as is the case with earthquakes in the CTBT.
Finally, there is the question of whether any state would permit an on-site inspection that would prove it was in violation of the agreement. Although the challenged country would probably attempt to block or delay the inspection by various means, the international community would undoubtedly see rejection of a challenge inspection, when a serious case for cause had been presented, as an admission of guilt. If the challenged country were indeed innocent of the charges, the inspection would provide an opportunity to clear itself and possibly shift international criticism to the party calling for the inspection in the first place.
Detection of Nuclear Weapon Programs by U.S. Intelligence
The historical record of U.S. intelligence in identifying foreign nuclear weapon programs is a valuable reference point for evaluating the likelihood that clandestine weapons programs would be detected in the future. At present the record and even some underlying capabilities of U.S. intelligence relating to recent events are the subject of intense controversy. On the specific question of how early the United States became aware of efforts to acquire nuclear weapons, however, the record is good. In every known case, U.S. intelligence became aware of efforts by other countries to develop nuclear weapons relatively early in these programs and well in advance of the actual achievement of a nuclear device. Although there have often been inaccuracies in detailed estimates, such as the date of the initial fabrication of a nuclear device and the total number of weapons assembled as of a given date, the United States has identified key production facilities before a significant amount of NEM or a nuclear weapon was produced. The following is a very brief summary of the U.S. experience:
-
Soviet Union. Despite extreme secrecy, the existence of the Soviet nuclear weapons program became known
-
soon after World War II, and the facilities that eventually produced the first NEM were identified by 1948. Knowledge of the Soviet program emerged from analysis of many unrelated sources ranging from very sensitive NTM to the open literature, which taken together pointed unambiguously to a high-priority project to develop nuclear weapons as rapidly as possible.19 The Soviet Union conducted its first nuclear test sooner than most analysts anticipated, but the purpose and general nature of the program were clear well before the first Soviet test in late August 1949.20
-
China. U.S. intelligence identified all of China’s major NEM production facilities prior to their operation.21 Limited to the use of satellite and aerial photoreconnaissance by the strict secrecy of Maoist China, U.S. intelligence had difficulty in determining the operational status and capacity of these facilities. Although U.S. intelligence correctly identified the uranium enrichment facility at Lanzhou two years before China tested its first weapon (which used HEU produced by this facility), for example, it underestimated the capacity of the plant and judged that the facility would not be operational for three more years.22
|
19 |
Nuclear History Program, Berlin Crisis History Session #8, Interview with Spurgeon M. Keeny, Jr., October 30, 1992, Transcript. Center for International Security Studies at the School of Public Affairs, University of Maryland, pp. 320-321 and Henry S. Lowenhaupt, “On the Soviet Nuclear Scent,” Studies in Intelligence, Central Intelligence Agency, Fall 1967, pp.13-29. Secret document, declassified and approved for release. |
|
20 |
Roscoe H. Hillenkoetter, “Estimate of the Status of the Russian Atomic Energy Project,” Director of Central Intelligence Memorandum to the President, July 6, 1948, p. 1, and David Holloway, Stalin and the Bomb: The Soviet Union and Atomic Energy (New Haven, CT: Yale University Press, 1994), p. 220. |
|
21 |
National Intelligence Estimate [NIE] 13-2-60, “The Chinese Communist Atomic Energy Program,” December 13, 1960; National Intelligence Estimate [NIE] 13-2-62, “Chinese Communist Advanced Weapons Capabilities,” April 25, 1962; Special National Intelligence Estimate [SNIE] 13-2-63, “Communist China’s Advanced Weapons Program,” July 24, 1963; Special National Intelligence Estimate [SNIE] 13-4-64, “The Chances of an Imminent Chinese Communist Nuclear Explosion,” August 26, 1964; and National Intelligence Estimate [NIE] 13-2-65, “Communist China’s Advanced Weapons Program,” January 27, 1965. All partially declassified, approved for release and available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
22 |
National Intelligence Estimate [NIE] 13-2-62, “We believe that the Chinese would at some point in their program endeavor to produce U-235, but we have no evidence of U-235 production at present. Latest evidence indicates that a facility at Lanchou [Lanzhou] suspected of being a gaseous diffusion plant has not been completed. If this plant is in fact intended to be a gaseous diffusion facility, it probably could not produce weapon grade U-235 before 1965. The Chinese could probably test an all U-235 or composite device within a year after the activation of a production facility,” p. 4. |
-
Israel. The United States photographed what was to become the Dimona nuclear facility under construction in the late 1950s,23 and the existence of a plutonium production reactor at the site was clearly established in the early 1960s.24 Any doubts about the purpose of the program25 were removed when Israel refused to allow the United States to carry out meaningful bilaterally agreed inspections of Dimona.26
-
India. India’s nuclear test in 1974 came as a surprise,27 but the suspicious nature of the secretive Indian nuclear program was recognized a number of years earlier and the facilities supporting the development of the device had been identified.28
|
23 |
Avner Cohen, Israel and the Bomb (New York, NY: Columbia University Press, 1998), p. 83. |
|
24 |
Dean Rusk to John F. Kennedy, “Israel’s Atomic Energy Activities,” Department of State Memorandum, January 30, 1961, p. 1. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
25 |
William N. Dale to Department of State, “Current Status of the Dimona Reactor,” Department of State Airgram A-742, April 9, 1965, p. 5. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
26 |
From 1961 until 1969, U. S. scientists conducted regular (roughly annual) inspections of Dimona. From the start, the Israelis denied access to most of the key areas in the facility. After the July 12, 1969, inspection, the U.S. and Israeli governments reached an agreement to discontinue the procedure. See Avner Cohen, Israel and the Bomb (New York, NY: Columbia University Press, 1998), pp. 329-338 and Memorandum of Conversation, “1969 Dimona Visit,” Department of State, August 13, 1969, p. 2. Secret document, declassified and approved for release. Available as of January 2005, at: http://www2.gwu.edu/~nsarchiv/israel/documents/visit/01-01.htm. |
|
27 |
The U.S. intelligence community did not detect the preparation for the May 18, 1974, “peaceful nuclear explosion” at the Thar Desert test site near the city of Pokhran prior to the test but were well aware that India possessed a capability to test at any time. See National Security Study Memorandum [NSSM] 156, “Indian Nuclear Developments,” September 11, 1972, p. 1. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
28 |
George McGhee to Dean Rusk, “Anticipatory Action Pending Chinese Communist Demonstration of Nuclear Capability,” Department of State, September 13, 1961. Available as of January 2005, at: http://nsarchive.chadwyck.com. “India’s atomic program is sufficiently advanced so that it could, not many months hence, have accumulated enough fissionable material to produce a nuclear explosion,” p. 2 and George Perkovich, India's Nuclear Bomb: The Impact on Global Proliferation (Berkeley, CA: University of California Press, 1999), p. 52. |
-
Pakistan. The fact that Pakistan was engaged in a major effort to develop nuclear weapons was apparent in the mid-1970s, early in the program.29 The location and nature of the facilities supporting the effort were also identified early, including the secret uranium enrichment facility at Kahuta. In response to Pakistan’s covert theft of Urenco centrifuge enrichment technology,30 the United States terminated economic and military aid to Pakistan in 1977 and again in 1979, many years before Pakistan was able to produce significant amounts of HEU and assemble its first weapon.31
-
South Africa. The goals of the South African nuclear program were long suspect, particularly when in the 1970s South Africa developed the Helikon enrichment process capable of producing HEU.32 The United States cut off nuclear cooperation in 1976 due to South Africa’s refusal to sign the NPT. These suspicions were confirmed in 1977 when the United States was informed by the Soviet Union that one of its satellites had discovered an apparent nuclear test site in the Kalahari Desert.33
|
29 |
National Security Study Memorandum [NSSM] 202, “U.S. Non-proliferation Policy,” May 23, 1974, p. V-9. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com and Swarts to Hartman, “Demarche to Pakistan on Nuclear Fuel Reprocessing,” Department of State, January 30, 1976, p. 1. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
30 |
State Department Briefing Paper, “The Pakistani Nuclear Program,” June 23, 1983, p. 4. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://nsarchive.chadwyck.com. |
|
31 |
Tracking Nuclear Proliferation, 1998: Pakistan, “Glenn-Symington Amendment” (Washington, DC: Carnegie Endowment for International Peace, 1998). Available as of January 2005, at: http://www.ceip.org/files/Publications/TrackingPakistan.asp. |
|
32 |
Directorate of Intelligence, “Prospects for Further Proliferation of Nuclear Weapons,” October 2, 1974, p. 5. Classified memorandum partially declassified and approved for release. Available as of January 2005, at http://nsarchive.chadwyck.com and Directorate of Intelligence, “New Information on South Africa's Nuclear Program and South African-Israeli Nuclear and Military Cooperation,” March 30, 1983, p. 1. Secret document, partially declassified and approved for release. Available as of January 2005, at: http://www.foia.ucia.gov. |
|
33 |
David Albright, “South Africa’s Secret Nuclear Weapons,” ISIS Report (Washington, DC: Institute for Science and International Security, May 1994). Available as of January 2005, at: http://www.isis-online.org/publications/southafrica/ir0594.html and Mitchell Reiss, “South Africa: Castles in the Air,” in Bridled Ambition: Why Countries Constrain Their Nuclear Capabilities (Washington, DC: Woodrow Wilson Center, 1995), p. 10. |
-
Iraq. Iraq’s nuclear program became the object of suspicion beginning in the late 1970s. Israel was sufficiently concerned about the ultimate purpose of the Osiraq research reactor that in 1981 it destroyed the reactor in a controversial bombing raid. There was considerable evidence of the buildup of the Iraqi nuclear program during the 1980s, and key facilities were identified and destroyed during the 1991 Gulf War.34 Subsequent inspections determined that the nuclear program, while more extensive than previously believed, had not produced a weapon or significant amounts of NEM.
-
North Korea. North Korea became the subject of suspicion when it began construction in the early 1980s of a small graphite-moderated reactor capable of producing significant quantities of plutonium.35 Although North Korea signed the NPT in 1985, this suspicion grew when it delayed signing the required IAEA inspection protocol until 1992. During this period North Korea initiated construction of much larger graphite-moderated nuclear reactors, as well as a building identified by U.S. intelligence as a suspected reprocessing facility,36 and a suspected site where associated reproc-
|
34 |
Iraq had three operating reactors including the Osiraq reactor. Two small research reactors, IRT 5000 rated at 5,000 kilowatts and Tammuz 2, rated at 500 kilowatts, were both damaged by Coalition air strikes in March 1991. See Iraq Profile, “Iraqi Nuclear Facilities: Research Reactors,” The Nuclear Threat Initiative, Available as of January 2005, at: http://www.nti.org/e_research/profiles/Iraq/Nuclear/2117_3362.html. |
|
35 |
Gary Samore, ed. North Korea's Weapons Programmes: A Net Assessment, An IISS Strategic Dossier (Basingstoke, UK and New York, NY: International Institute for Strategic Studies and Palgrave Macmillan, 2004). “Through satellite reconnaissance, the US detected the construction of the 5MW(e) reactor at an early stage, and was able to confirm initial operation of the reactor in 1986 by noting the emission of steam plumes from its cooling tower, which indicated the reactor was venting excess heat,” p. 35. See also Michael J. Mazarr, North Korea and the Bomb: A Case Study in Nonproliferation (New York, NY: St. Martin’s Press, 1995), p. 40. |
|
36 |
Gary Samore, ed. North Korea's Weapons Programmes: A Net Assessment, An IISS Strategic Dossier (Basingstoke, UK and New York, NY: International Institute for Strategic Studies and Palgrave Macmillan, 2004), p. 36. In July 1989, the U.S. media described a U.S. and South Korea meeting on the suspected North Korean reprocessing facility at Yongbyon, corroborating earlier South Korean media reports. See, for example, John J. Fialka, “North Korea May Be Developing Ability to Build Nuclear Weapons,” The Wall Street Journal, July 19, 1989, p. A16, and Don Oberdorfer, “North Koreans Pursue Nuclear Arms: U.S. Team Briefs South Korea on New Satellite Intelligence,” The Washington Post, July 29, 1989, p. A9. |
-
essing wastes were hidden. The first IAEA inspections of the facility in 1992 and 1993 confirmed U.S. suspicions that plutonium had been separated from irradiated reactor fuel.37
-
Iran. Iran received significant assistance from China for its civilian nuclear program beginning in the mid-1980s, and in 1995 Iran contracted with Russia to complete one of the two partially constructed reactors at Bushehr, which were begun with German assistance in the late 1970s but were severely damaged during the 1980-1988 Iran-Iraq War. The United States pressed China and Russia throughout the 1990s to curtail their nuclear cooperation with Iran, citing intelligence information indicating that Iran intended to develop nuclear weapons. Evidence of a secret centrifuge enrichment program began to emerge publicly as early as 1995, and in August 2002 the existence of a secret nuclear facility at Natanz was revealed by an Iranian opposition group.38 Perhaps in response to these leaks, in 2003 Iran opened what it claimed to be all of its facilities to IAEA inspection, including a pilot centrifuge enrichment plant under construction near Natanz.39 The controversy over Iran’s nuclear program continues, but the relevant point here is that the existence of the NEM production program was discovered well before weapons or significant amounts of HEU were produced.
|
37 |
Michael J. Mazarr, North Korea and the Bomb: A Case Study in Nonproliferation (New York, NY: St. Martin’s Press, 1995), p. 84. For additional details see: Samore, North Korea’s Weapons Programmes, “The 1992 Plutonium Mystery,” pp. 36-38. |
|
38 |
News Bulletin, “Mullahs’ Top Secret Nuclear Sites and Weapons of Mass Destruction Projects,” Iran Liberation, The National Council of Resistance of Iran, August 19, 2004, p. 2. Available as of January 2005, at: http://www.globalsecurity.org/wmd/library/news/iran/2002/iran-020819-ncri_news.pdf. |
|
39 |
Mohamed ElBaradei, “Implementation of the NPT Safeguards Agreement in the Islamic Republic of Iran,” Report by the Director General, November 10, 2003 (Derestricted November 26, 2004). Available as of January 2005, at: http://www.iaea.or.at/Publications/Documents/Board/2003/gov2003-75.pdf. |
-
Libya. Libya was long believed to have been laying the groundwork for a nuclear weapons program. Under pressure from the United States and the United Kingdom, Libya disclosed details of this effort at the beginning of 2004, took steps to terminate it, and agreed to accede to the Additional Protocol to the IAEA safeguards agreement.40 Although it had received substantial assistance, the Libyan program had not progressed to the point of producing NEM.
-
Other Programs. In the past a number of other states, including Argentina, Brazil, South Korea, Taiwan, Switzerland, and Sweden, initiated programs directed at developing a nuclear weapon capability. All of these programs were subsequently abandoned when the political leadership recognized that the programs would not be in the overall best interests of those states. In each of these cases, the United States had early indications of the evolving plans, which allowed high-level diplomacy to influence political leaders, who in some cases may not have been fully aware of the actions of secret organizations within their own military and scientific communities.
Looking ahead, the technical collection capabilities of U.S. intelligence will continue to increase, as they have over the last half century, particularly with the advent of advanced space-based sensor technology. Although substantial uncertainties have and will continue to surround intelligence estimates, it is important to remember that in the context of an international agreement in which all nuclear facilities were declared, these uncertainties could be resolved by requesting an on-site inspection of the suspect facility. As noted in the previous section on environmental monitoring, an on-site inspection would be highly likely to detect any significant undeclared activities, such as the enrichment of uranium or the separation of plutonium. Based on the historical evidence, and with these additional capabilities, we judge that a clandestine nuclear weapons program very likely would not escape early detection.
|
40 |
Mohamed ElBaradei, “Implementation of the NPT Safeguards Agreement of the Socialist People’s Libyan Arab Jamahiriya,” Report by the Director General. May 28, 2004. Available as of January 2005, at: http://www.fas.org/nuke/guide/libya/iaea0504.pdf. |
CONCLUSIONS
As discussed in Chapters 2 and 3, procedures and technology are available to verify with high confidence the declarations of stockpiles of nuclear weapons and NEM at declared sites. Independent knowledge of the actual total size of the Russian stockpiles of nuclear weapons and NEM, however, is sufficiently uncertain that verified declarations alone cannot preclude the possibility that undeclared stockpiles might exist at undeclared locations. Although there is a good chance that the possible existence of undeclared stockpiles would be revealed by a combination of National Technical Means, human intelligence, audits of records, and physical inventories, the theoretical possibility that significant numbers of undeclared weapons had been retained at hidden sites would remain for many years, and perhaps several decades.
Undeclared nuclear weapons also could come into existence by the clandestine production of NEM. Past experience indicates a high probability that this would be detected over time. Though not perfect, NTM, human sources, and environmental monitoring form a fairly tight net with which to catch evidence of the large programs and facilities required to produce NEM. Given the extensive knowledge of existing nuclear programs, the massive amounts of additional information that would result from the process of verifying declarations, the new inspection capabilities provided by the IAEA Additional Protocol, and the demonstrated capabilities of NTM, it is very unlikely that any state, including Russia, participating in a cooperative fashion involving detailed declarations could develop a complete, stand-alone covert nuclear weapon production program that would not be discovered over time. If, however, undeclared stocks of NEM exist or can be diverted without detection from civilian stocks or production facilities, it is much more likely that the assembly of new weapons could escape detection.
The synergistic effect of the approaches discussed in Chapters 2, 3, and 4 in a cooperative environment, coupled with robust NTM capabilities, would substantially reduce current uncertainties in U.S. assessments of foreign nuclear weapon and NEM stockpiles over time. Nevertheless, in view of the sheer size and age of the Russian stockpile (where current uncertainties amount to the equivalent of several thousand weapons), Russia probably could conceal undeclared stocks equivalent to several hundred weapons. In the case of other countries with much smaller programs, abso-
lute uncertainties would be much less, leading to the possibility that these countries could conceal undeclared stocks equivalent to one or two dozen weapons in the case of China, and at most one or two weapons in the case Israel, India, and Pakistan. Confidence that declarations were accurate and complete, and that covert stockpiles or production facilities did not exist, would be increased by the successful operation of a monitoring program over a period of years in an environment of increased transparency and cooperation.