4
Emerging and Converging Technologies1
During the century just begun, as our ability to modify fundamental life processes continues its rapid advance, we will be able not only to devise additional ways to destroy life but will also be able to manipulate it—including the processes of cognition, development, reproduction, and inheritance.
—Matthew Meselson2
It is difficult to predict what the global technology landscape will look like in 20, 10, or even 5 years into the future. But it is not difficult to predict that as advances are made, so too will the opportunities for misuse. This chapter summarizes information on emerging technologies that are expected to have significant economic, societal, and dual-use risk impact in the near future. As highlighted during the workshop, prominent among these are advances in knowledge and delivery technology that have increased the dual-use potential and risk of non-lethal bioregulators; and the convergence of nanotechnology and biotechnology in the form of DNA nanotechnology.
|
1 |
This section is based on the workshop presentations of Kathryn Nixdorff and Elliott Kagan. |
|
2 |
Meselson, M. 1999. “The problem of biological weapons.” Presentation given to the 1818th Slated Meeting of the American Academy of Arts and Science, Cambridge, MA, January 13. http://www.pugwash.org/reports/cbw/cbw5.htm. Accessed on October 30, 2004. |
A major theme that emerged from these discussions is the notion that pathogens are not the only potential bioterrorist agents. Some experts argue that bioregulators, which are non-pathogenic organic compounds, may pose a more serious dual-use risk than had been previously perceived, particularly as improved targeted delivery technologies have made the potential dissemination of these compounds much more feasible than in the past. This shift in focus highlights the reality that the materials, equipment, and technology necessary for disseminating and delivering the agents to their intended recipient(s) are equally, if not more, important than the agents themselves in terms of their dual-use risk.
The immune and neuroendocrine systems are particularly vulnerable to bioregulator modification. In fact, the capacity to develop bioweapons that can be aimed at the interaction of the immune and neuroendocrine systems again points to a shift in focus from the agents to, in this case, how a range of agents can be exploited (or created) to affect the human body in targeted, insidious ways.
A controversial issue that arose from these discussions is how all research on immune system evasion could be considered potentially dangerous, thus highlighting the very important need to uphold the norms of the Biological Weapons Convention. The unlikely possibility that reaffirming these norms will have any immediate effects further complicates the problem. Discussion of these issues is reserved for Chapter 5.
Another important theme that emerged from discussions of the material presented here is the notion of time and how the advancing technology landscape has an uncertain future and unpredictable dual-use risk implications. This unpredictability poses a significant challenge for developing and implementing a strategy to manage these risks.
Added to the temporal challenge are difficulties associated with adapting or developing prevention strategies that are effective against the wide range of risks posed by the various types of dual-use agents, materials, and technologies. Comments were made about how the CDC Select Agent Program does not accurately reflect the variable nature of these risks.3
Importantly, the growth and proliferation of dual-use agents, materials, equipment, and technology summarized here does not necessarily imply that the acquisition, creation, or effective use of a biological agent is easy. The Japanese cult Aum Shinrikyo’s nine failed attempts between 1990 and 1994 to disperse biological weapons in Tokyo and nearby areas are a reminder of the difficulty of carrying out an attack, even with category A agents (Bacillus anthracis or botulinum toxin), despite the expenditure of
|
3 |
The interim final rule on the possession, use, and transfer of select agents and toxins can be viewed online at http://www.cdc.gov/od/sap/docs/42cfr73.pdf. |
considerable time, effort, money, and talent. Not only did Aum Shinrikyo obtain a non-lethal vaccine strain of anthrax, it had not mastered the aerosolization technology required to disseminate it.4
BIOREGULATORS AND INNATE IMMUNITY5
Bioregulators are naturally occurring organic compounds that regulate diverse cellular processes in multiple organ systems and are essential for normal homeostatic function. They are structurally diverse and play key roles in many critically important bodily functions, such as maintaining bronchial smooth muscle tone, blood pressure, heart rate, body temperature, mood and consciousness, and innate and adaptive immune responses. Most bioregulators operate by targeting specific cell receptors and signal transduction pathways, ultimately impacting mRNA synthesis (see Figure 4-1 A and B ). Several different types of bioregulators are considered potential threat agents: cytokines (pro-inflammatory agents, such as IL-1; chemokines; and growth factors); hormones (catecholamines, insulin); neurotransmitters (neuropeptides, biogenic amines, amino acids); eicosanoids (e.g., prostaglandins, leukotrienes); enyzmes (e.g., kallikreins, tissue factor); and nucleic acids (i.e., DNA, RNA).
In the past, the dual-use risk of bioregulators was considered minimal because of their lack of suitability for aerosolization unless microencapsulated; their limited shelf life after atmospheric release; the fact that proteins denature at very high temperatures and lose activity at low temperatures; and high purchase costs. However, new knowledge and advancing technologies, particularly delivery technologies, have raised concerns about the dual-use risk of bioregulators. Potential delivery platforms include the use of bacterial plasmids or viral vectors for cloning the genes that encode bioregulators; the use of transgenic insects (i.e., to secrete and inoculate the bioregulators); nano-scale delivery systems (e.g., engineered proteins either within or bound to nanotubes); and microencapsulated delivery systems (i.e., incorporating vectors or the proteins themselves into biodegradable microspheres or liposomes for controlled release).6
|
4 |
Leitenberg, M. 2000. “An assessment of the biological weapons threat to the United States.” A White Paper prepared for the Conference on Emerging Threats Assessment: Biological Terrorism, at the Institute for Security Technology Studies, Dartmouth College, July 7-9, Journal of Homeland Security, http://www.homelandsecurity.org/journal/Articles/Leitenberg.htm. Accessed on October 30, 2004. |
|
5 |
This section is based on the workshop presentations of Kathryn Nixdorff and Elliott Kagan. |
|
6 |
Wang, D. et al. 1999. “Encapsulation of plasmid DNA in biodegradable poly(D,L-lacticco-glycolic acid) microspheres as a novel approach for immunogene delivery.” Journal of Controlled Release 57:9-18. |
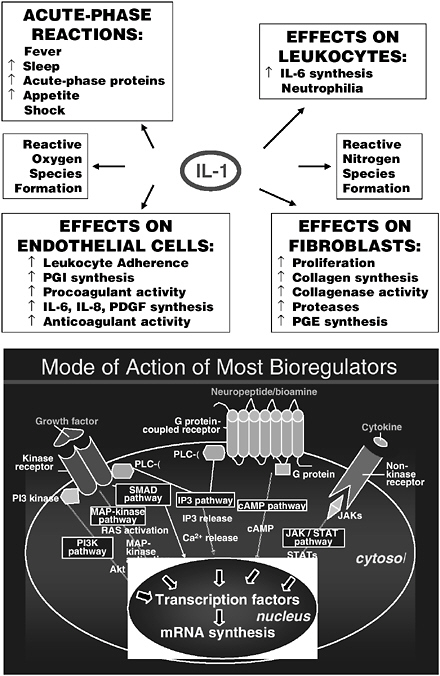
FIGURE 4-1 A and B The multiple ways that bioregulators impact mRNA synthesis. Because of the key role that bioregulators play in so many cellular and physiological processes, their dual-use risk increases as delivery technologies advance.
NOTE: Adapted from Elliott Kagan’s PowerPoint presentation, September 22, 2004.
Given that anything less than 3 microns in diameter is respirable across what amounts to a 75 square meter absorptive surface, the miniaturization of respiratory delivery systems comes with considerable dual-use risk. Moreover, transgenic plants could be put to dual-use as bioregulator-production factories.
In many ways, bioregulators pose serious dual-use risks:
-
Their onset of action is rapid, occurring within minutes to hours.
-
They can potentially cause injury or death with no obvious evidence of attack (i.e., stealth factor).
-
Their clinical effects are non-specific (i.e., very low index of clinical suspicion).
-
Casualties may manifest as multiple occurrences of unexplained symptoms.
-
They target critical human biochemical pathways.
-
They may target multiple organ systems (e.g., central nervous system, lungs, immune system, gastrointestinal system, cardiovascular system, etc.).
-
Potential long-term consequences include pulmonary fibrosis, cancer, sterility, autoimmunity, etc.
-
There are no vaccines available.
-
Most bioregulators are not on standard military threat lists, meaning there is no provision for appropriate antidote stockpiling.
-
The effects of bioregulators may synergize with those of traditional BT/BW agents.
-
They can be engineered to target specific human biological systems at the molecular level.
-
Future potential as threat agents will parallel advances in biotechnology.
Bioregulators have been used in prior state-sponsored bioweapons programs, including South Africa’s Project Coast, which included a peptide synthesis program aimed at enhancing the effects of certain bioregulators (see Chapter 3). Also, according to congressional testimony by Soviet defectors, the former Soviet Union reportedly synthesized recombinant bioweapon peptides that could induce autoimmunity.7
The Vulnerability of the Immune System8
The immune system plays a crucial role in protection against infectious disease. The immune system is particularly vulnerable to the numerous evasion strategies that microorganisms utilize; as the development of a lethal form of the mousepox virus by Australian scientists in 2001 demonstrated, the manipulation of microorganisms can lead to the creation of mechanisms to evade the immune system in devastating ways.9 The immune system is also vulnerable to modulation by bioregulators.
There are two components of immunity, innate and adaptive. The innate immune system has a relatively low specificity for microorganisms; the immune cells recognize what are known as pathogen associated molecular patterns (PAMPs). In contrast, the adaptive immune system has a very high specificity and recognizes specific antigens on single microorganisms. Innate immune system actors are ready to work immediately, sometimes within minutes, and do not require much induction or activation. Adaptive immune cells must be activated by interaction with specific antigens; in fact, adaptive immune cells must go through three phases—activation, proliferation, and differentiation—before they can exert their effector functions, a process that takes days and sometimes weeks. Another key difference is that the innate system has no memory, whereas adaptive immunity does. Although adaptive immunity may not afford much initial protection, its long-term protective power is better. On the other hand, if the innate immune system, which represents the first line of defense, is destroyed, the battle is lost from the start.
In light of the vulnerability of both components of the immune system to immune evasion strategies, it was suggested that any research that would enhance the ability of an organism to evade the immune system should be considered potentially very dangerous and that there should be a closer interaction and information exchange between security professionals and funding agencies. For example, NIH has issued grants to compile an encyclopedia of the innate immune system; one could imagine using such an encyclopedia as a blueprint for ways to maliciously manipulate the innate immune system. It was also pointed out that a number of pharmaceutical companies are examining the use of toll-like receptors (TLRs) to induce the innate immune response.10 In fact, drugs that target
TLRs are already commercially available. For example, imiquimod is an immune response modifier typically prescribed for genital warts and some skin cancers; it stimulates TLR7, a key antiviral TLR. Other participants expressed concern that such a restrictive stance on immune system research would hinder valid and beneficial scientific and technological progress.
The immune system is doubly vulnerable to either natural or deliberate attack by virtue of its interaction with the neuroendocrine system. The dual-use risk of bioregulators is particularly relevant within this context. Both the immune and the neuroendocrine systems produce cytokines, peptide hormones, and neurotransmitters and regularly communicate with each other via shared receptor circuitry.11
For example, when an immune system cell is activated, the signal is transduced and a cascade of reactions initiated, ultimately ending in activation of genes encoding various protein products. These cells include the pro-inflammatory cytokines, particularly macrophages, T-lymphocytes, and interleukin-4 (IL-4). (Considerable research efforts are being directed toward manipulating these cellular reactions to either increase or suppress the production of these various bioregulators. Increased bioregulator production, particularly of the pro-inflammatory cytokines, can cause misguided auto-immune reactions, and suppression runs the danger of compromising protection against infection.) These pro-inflammatory cytokines have a profound effect on the neuroendocrine system by inducing the over-production of hormones in the hypothalamus, thereby damaging neurons and producing sickness behavior (i.e., a lethargic, sleepy, sick feeling). They can also induce the hypothalamus to make corticotropin-releasing hormone (CRH) which, if produced in large enough quantity, can cause neuronal damage; experiments have shown that inhibition of CRH production can lessen neuronal damage after a stroke. By inducing the pituitary production of adrenocorticotropic hormone which activates the adrenal glands to produce cortisol, excessive cytokine production can have a profound effect on immune suppression.12
Normally, these various interactive reactions are kept in balance, but modulating one system could have profound effects on the other. The greater, systemic damage that could be done by targeting single components of these interacting physiological systems leave both systems doubly open to assault and represent a necessary shift in focus (in terms of what
constitutes the greatest dual-use risk) from the bioagents themselves to interacting physiological systems as the targets of malign intent.
In light of the increasing bioterrorist threat posed by bioregulators, due to greater knowledge about their systemic damage and advances in delivery technology, it was emphasized that it will be critically important to uphold the BWC norm against the hostile use of science and technology generally (and specifically with regards to bioregulators); and to strengthen future biodefense surveillance by developing next-generation biosensors for the detection of human bioregulators.
DNA NANOTECHNOLOGY13
In just five years, nanotechnology has catapulted from being a specialty of a relative handful of physicists and chemists to a worldwide scientific and industrial enterprise.14 The U.S. government estimates that the nanotech economy will be worth $1 trillion by 2012. Compare that to the current $4 billion pharmaceutical market (see Chapter 3).
In the popular literature, definitions of nanotechnology range from “the science involving matter that is smaller than 100 nanometers”15 to anything dealing with “human-built structures measuring 100 nanometers or less.”16 At the workshop, three definitions were provided: “arranging molecules (atoms) as precisely as possible so as to perform a designated function,” “doing with real molecules what computer graphics does with molecular models,” and “putting what you want where you want it and having it do what you want it to do.”
Semantics aside, an intriguing feature of the nanoscale is that it is the scale upon which biological systems build their structural components, like microtubules, microfilaments, and chromatin.17 In other words, biochemistry is a nanoscale phenomenon. Even more intriguingly, a key property of these biological structural components is self-assembly. The most successful biological self-assembler is, of course, the DNA double helix. In their quest to emulate these biological phenomena, scientists have
|
13 |
This section is based on the workshop presentation of Nadrian Seeman. |
|
14 |
Service, R. F. 2004. “Nanotechnology grows up.” Science 304:1732-1734, 18 June. |
|
15 |
Blumenstyk, G. 2004. “Big Bucks for Tiny Technology.” The Chronicle of Higher Education 51:A26. http://chronicle.com/weekly/v51/i03/03a02601.htm. |
|
16 |
Monastersky, R. 2004. “The dark side of small.” The Chronicle of Higher Education 51(3): A12. http://chronicle.com/free/v51/i03/03a01201.htm. |
|
17 |
Seeman, N. C. and A. M. Belcher. 2002. “Emulating biology: building nanostructures from the bottom up.” PNAS 99:6451-6455. |
created the field of DNA nanotechnology,18 as well as the closely related field of DNA-based computation by algorithmic self-assembly.19
DNA nanotechnology is the design and development of objects, lattices, and devices made of synthetic DNA. Since the DNA helix is naturally linear (i.e., unbranched), the assembly of structures or devices built with synthetic DNA requires constructing branched molecules that can then be connected to form structural networks or motifs. The DNA motifs are combined by means of sticky-end cohesion, a high specificity DNA reaction.
There are two types of DNA nanotechnology: high structural resolution DNA nanotech, which involves using DNA as both brick and mortar in the construction of various kinds of nano-objects; and compositional DNA nanotech, which involves using a DNA mortar to join non-DNA particles. The latter, which was not discussed in detail at the workshop, can be used in many ways to organize large complexes; multiple labs worldwide are involved in this technology. The focus of the workshop presentation was on high structural resolution DNA nanotech, which only about a dozen labs worldwide are researching.
The potential applications of high structural resolution DNA nanotechnology are many and varied:
-
Architectural control and scaffolding
-
Improving macromolecular crystallization protocol (which is how the field began)
-
Nanoelectronics organization
-
DNA-based computation
-
Constructing and controlling polymers
-
-
Nanomechanical devices
-
Nanorobotics
-
Nanofabrication
-
Sensors and detectors
-
Computational devices
-
-
Self-replicating nano-systems
The primary difference between nanomechanical devices and self-replicating systems is that the former are “clocked” devices, meaning that someone (a person or robot, as the case may be) has to do something in order for the nano-device to operate. Self-replicating systems, on the other hand, are autonomous devices that do not need direction intervention in order to work. Purdue University researcher Chengde Mao is credited with having made one of the first autonomous nano-devices, in this case a DNAzyme, which can bind and cleave RNA molecules one by one.20 The creation of this device exemplifies the extraordinary progress that the DNA nanotech field has achieved just over the course of the past two years. Autonomous devices were unimaginable two years ago.
The future trajectory of the technology is unclear, although it will almost certainly have multiple medical applications, including therapeutic delivery by nanoparticles. One could imagine, for example, synthetic, enzyme-carrying DNA devices interfering with amyloid fibrils by binding to them and unloading a load of peptidase or protease. It is also conceivable that devices could be engineered to conduct nano-searches of what is present or what is needed (e.g., in terms of pharmaceutical intervention or even environmental detection). Another possibility might be the development of implants made of new, bio-compatible materials that are stronger and better than ever before.
Similar technology may someday enable people to inject or attach removable devices for the monitoring of metabolic parameters and controlled release of drugs, insulin, or other compounds. In October 2004, scientists from the Institute of Bioengineering and Nanotechnology, Singapore, invented a contact lens capable of releasing precise amounts of medication to treat glaucoma and other eye diseases.21
While nanotechnology (and all other emerging, converging technologies) promise radical changes in science and society, future progress in the field will require overcoming many scientific challenges.
As far as the nature of the dual-risk posed by this field, since the technology is expected to make for relatively inexpensive, small scale science, the dual-use risks will be similar to those of more conventional biotechnology in terms of ease of access and difficulty of detection. On the other hand, one participant noted that the “intellectual footprint” left by bringing two or more technologies together to create a bioweapon (e.g., nanotechnology and synthetic biology) might make bioweapons activity more noticeable and easier to detect.
|
20 |
Chen, Y. and C. Mao. 2004. “Putting a break on an autonomous DNA nanometer.” Journal of Am. Chem. Soc. 126 (28):8626-8627. |
|
21 |
http://www.ibn.a-star.edu.sg/news_interface_article.php?articleid=54. Accessed on October 30, 2004. |
CONVERGING TECHNOLOGIES22
Some experts consider the convergence of bio-, nano-, and information technologies, along with the neuro- and cognitive sciences, will enable humans to do things never dreamt of until now (see Figure 4-2). Some experts consider the convergence of these so-called enabling technologies a transformation that will prove as powerful as the industrial revolution.
Enabling technologies are those that interact with each other to create novel products that would otherwise be impossible to achieve. Nanotechnology enables by providing a common hardware for molecular engineering and allowing for the realization of desirable architectures. Nanotechnology enables biotechnology by developing new imaging techniques, probes and sensors; and it contributes to the miniaturization demands of information technology. Biotechnology enables other technologies by identifying chemical and physical processes and algorithmic structures in living systems that have a genetically-based material organization. It enables nanotechnology by providing a paradigm that nanotechnologists use in developing systems; much of the work in nanotechnology involves mimicking biotechnological processes while simultaneously redesigning them to fit particular purposes. Biotechnology enables information technology by providing new systems of computing, some of which may be based on DNA. Information technology enables through its ability to represent physical states as information and model processes. It provides the computing power that is essential to all research; it enables nanotechnology through precision control of patterning and intervention; and it enables biotechnology by providing the means to model complex processes and thereby solve difficult research problems.
The transformative potential of the convergence of these enabling technologies is attributed to four shared features:
-
Embeddedness: Converging technologies (CTs) will form an invisible technical infrastructure for human action. CTs will produce incredibly intrusive devices, like devices in a refrigerator that not only “decide” when certain items need to be restocked but send a message to the supermarket. Marks and Spencers, a clothing retail store in England, is reportedly collaborating with a Japanese manufacturer to create microchips that will be embedded in every single item of clothing; the microchips will transmit information back to the store headquarters, such as when the item was purchased, if and when it was returned, how much it cost, how it’s selling generally, and whether it needs to be restocked.
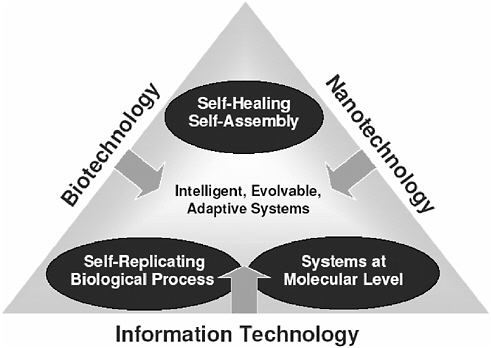
FIGURE 4-2 Converging Technologies (CTs). Biotechnology, nanotechnology, and information technology are converging in ways that will enable humans to do things never dreamt of until now.
NOTE: Adapted from Michael Morgan’s PowerPoint presentation, September 22, 2004.
-
Unlimited reach: As the convergence continues to draw in new technologies and technology-enabling sciences, it would appear that nothing can escape the reach of CTs and that the mind, social interactions, communication, and emotional states can all be engineered.
-
Engineering the mind and body: The reality of CTs has led to the notion that it may be possible to “improve” humankind with greater molecular or physical powers, for example by using electronic implants.
-
Specificity: The convergence of enabling technologies and knowledge systems can be geared to address very specific tasks, such as the targeted delivery of designer pharmaceuticals tailored to an individual’s genome to effect a cure without side effects.
Most applications of CTs are perceived as positive opportunities for economic growth. However, there are potential negative consequences. It is not difficult to imagine the problems that might occur if brain implants,
for example, were finally commercially available. The implants might give the user access to encyclopedias and dictionaries, maps, etc., or they could be customized to include databases of expert knowledge. But after the first two years of marketing, troubling statistics might emerge. In, say, 5 percent of the cases, the implants might not appear to work at all (i.e., the user somehow never learns to access them), and another 5 percent of the users might lose access to the implant with the first few months of use. Among the remaining 90 percent, although some people might be able to access the implant on the fly while performing other mental operations, others might only be able to access them with their eyes closed or while otherwise taking time out from other activities to concentrate. Finally, a small percentage of users might suffer irreversible brain damage. Consequently, the implants would fail as a consumer product.
The economic risk associated with this type of technological application is only one of many challenges that CTs face. More importantly, there are serious ethical issues associated with invasions of privacy and enhancing human capabilities and possibly changing the very notion of humanity. Moreover, CTs may have a socially destabilizing effect. In stark contrast to the potential benefits of biotechnology with respect to addressing human security concerns and closing the health, economic, and development gap between the North and South, the specificity afforded by CTs threatens to do the opposite. CTs may produce greater unemployment (e.g., as robots replace humans), and they may exacerbate the divide between the rich and poor and between technologically advanced and traditional countries. Other potential problems include adverse health effects associated with the use of novel materials and devices.
Particularly troubling and potentially internationally destabilizing are CTs exploited for “domination on the battlefield.” Proposed military applications exploit the most dangerous potential of CTs. These applications include surveillance, the physical enhancement of soldiers’ bodies, remote manipulation of soldiers’ minds, and the creation of autonomous killing machines. Founded by a $50 million contract from the U.S. Army, MIT’s Institute for Soldier Nanotechnologies (ISN) is designing “the soldier system of the future,” one that will make soldiers less vulnerable to enemy and environmental threats.23 Some experts question the feasibility of such endeavors. Nonetheless, the intent exists.
The very uncertainty about these capabilities may lead to a new, highly unstructured and non-negotiable arms race. This raises issues about transparency, as secrecy would likely accelerate the race. A question was raised about whether nanotechnology, like blinding laser weaponry,
|
23 |
http://web.mit.edu/isn/. Accessed on October 28, 2004. |
might ever reach a point where it would simply be unacceptable as a form of warfare. It was suggested that issues of arms regulation associated with emerging and converging technologies be addressed in an international forum, with an insistence on unambiguous adherence to international agreements.
However, looking to the bright side, some experts expect that, like current biotechnologies, CTs will be market-driven and/or driven by health or human security needs. If so, military applications may not be as worrisome as futuristic scenarios anticipate. In fact, the more important question may be, to what extent will health-related CTs be sustainable by governments? Will society be able to afford CTs, or will the price of CT medical devices drive the cost of health care up even further? Several groups are grappling with these sorts of issues. As it is difficult to imagine any third-party payer covering the costs of health-related CTs, a comment was made that the entire system of third-party payers will likely need to be completely overhauled in order to benefit health-wise from these technologies.
In order to manage the risks created by converging technologies—not just the dual-use risks created by potential military applications but the tremendous risk to human security by civilian CT use—the European High Level Expert Group (HLEG) on “Foresighting the New Technology Wave,” as called upon by the European Commission and Member States, suggested the development of a “societal observatory” with the following goals:24
-
to monitor in real-time and assess international CT research;
-
to study social drivers, economic and social opportunities and effects, and ethics and human right dimensions;
-
to serve as a clearing-house and platform for public debate;
-
to deal with questions regarding the applicability of patents, the definition of the commons, and the allocation of intellectual property in multidisciplinary collaborations; and
-
to monitor roadmaps, benchmarks, and public response.
It is unclear to what extent the working groups of this observatory would be comprised of scientists, as opposed to philosophers, historians, social scientists, and other experts. This touches upon the more general issue of the role of the individual scientist in managing the dual-use risk
of advancing technologies (see Chapter 5 for summary of workshop discussion on this topic).
It was suggested that the idea of a societal observatory could arguably be a piece of the “web of prevention” that some workshop participants said will be necessary for managing the dual-use risk of advancing technologies, as described in Chapter 5. Unfortunately, at the time the above-mentioned EU workshop was held, the notion of an observatory was more visionary than planned, and there had not yet been any discussion regarding its detailed development and implementation. The report in which this suggestion was made (along with 15 other recommendations) was only the first of what are expected to be many more steps in exploring the breadth, potential, and risks of CTs, particularly within the European Union and in relation to the Lisbon Declaration.
A question was raised about the reality of implementing potential CT applications. Some CTs, like brain implant technology, will not likely become a reality until far into the future, although there are devices currently being built that interact directly with the brain.
















