6
Communications
Effective communications are a fundamental requirement for the Navy. The establishment of FORCEnet as the enabler of the pillars of Sea Power 21—Sea Strike, Sea Shield, and Sea Basing—emphasizes this requirement. Effective communications are also a key element of achieving the composable and adaptable command, control, communications, computers, intelligence, surveillance, and reconnaissance (C4ISR) systems called for in earlier chapters.
6.1 CURRENT NAVAL COMMUNICATIONS
Navy operations require connectivity among a diverse set of platforms, including submarines, surface ships, aircraft, and shore sites. The links among these platforms support a wide range of applications, including command and control, battle management, the dissemination of common operational and tactical pictures, sensor-data dissemination, the tracking and engagement of time-sensitive and other targets, and many other C4ISR functions. Each of these platform types and applications presents unique challenges. For example, the submarine community operates in a very constrained physical communications environment, yet requires global connectivity. Shore sites have less-stringent physical constraints, but they are only available at a limited set of global sites that generally are quite distant from a theater of operations.
The Navy uses a variety of communications links for different applications. Figure 6.1 identifies major current and planned satellite data links and terrestrial line-of-sight (LOS) and beyond-line-of-sight (BLOS) data links. Additionally, there are underwater, surface, and subsurface communications technologies based
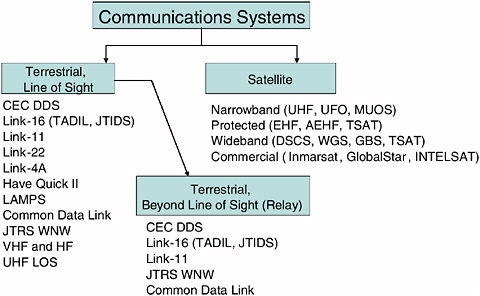
FIGURE 6.1 Some key Navy communications systems. NOTE: CEC DDS, Cooperative Engagement Capability Data Distribution System; TADIL, Tactical Digital Information Link; JTIDS, Joint Tactical Information Distribution System; LAMPS, Light Airborne Multipurpose System; JTRS WNW, Joint Tactical Radio System Wideband Network Waveform; VHF, very high frequency; HF, high frequency; UHF LOS, ultrahigh frequency line of sight; UFO, Ultra High Frequency Follow-On (Navy satellite program); MUOS, Mobile User Objective System; EHF, extremely high frequency; AEHF, advanced extremely high frequency; TSAT, Transformation Satellite; DSCS, Defense Satellite Communications System; WGS, Wideband Gapfiller System; GBS, Global Broadcasting System; Inmarsat, International Maritime Satellite; INTELSAT, Intelligence Satellite. SOURCE: Courtesy of Johns Hopkins University/Applied Physics Laboratory. Copyright © 2005 The Johns Hopkins University/Applied Physics Laboratory. All rights reserved.
on very low frequency (VLF) electromagnetic waves and on acoustics. These technologies have very low data rates but can support strategic covert, underwater-communications applications. The use of optical technologies in the form of both wired devices (e.g., a tethered buoy using optical fiber) and laser beams are also being explored for specialized applications.
Until recently, most of these communications links were platform- and application-specific (i.e., stovepipes) and had limited networking capability. Newer platforms and systems are being designed to provide a significant improvement in communications connectivity and capability while still interfacing with legacy equipment. As an example, the destroyer, experimental (next-generation, multimission destroyer) (DDX) and the Joint Strike Fighter (JSF) will support many more links and higher data rates than any other ship or aircraft will. But in
addition, the Navy can leverage technology advancements from the other Department of Defense (DOD) Services. The Joint Battle Management Command and Control (JBMC2) roadmap identifies key platforms that will facilitate interoperability among multiple platforms operated by the joint Services. For instance, the cooperative engagement capability (CEC) integrates sensors, decision makers, and shooters for cooperative BLOS weapons engagement. Another example is the Joint Tactical Radio System (JTRS) Wideband Network Waveform (WNW) software radio. This radio will support multiple links and wave-forms, providing connectivity among many different systems, and can operate as a Mobile Ad Hoc Network (MANET).
As described in Chapter 1, until quite recently naval forces have had to operate with severe constraints on communications bandwidth. Even in Operation Iraqi Freedom, smaller, unit-level ships were limited to shared access to 56 kbps International Maritime Satellite (Inmarsat) channels. Thus, there is huge gap between current capabilities and the “infinite” bandwidth promised by the Transformational Communications Architecture (TCA) described in Chapter 3.
Communications satellite systems currently in development (Figure 6.2) will provide substantial increases in communications capacity to begin to fill this gap. Wideband communications are provided at X and Ka bands. X-band communications capacity provided by the Defense Satellite Communications System (DSCS) has already doubled under the DSCS-Service Life Extension Program (SLEP) and will see more than an order-of-magnitude increase with the deployment of the Wideband Gapfiller System (WGS). The current Ka-band Global Broadcast System (GBS), hosted on the UHF Follow-On (UFO) satellites, will be replaced by a two-way Ka-band system hosted on the WGS. Extremely high frequency (EHF) coverage currently provided by Military Strategic, Tactical, and Relay (MILSTAR) will be provided by the Advanced EHF (AEHF) system, again greatly increasing available capacity. Owing to their antijam and low-probability-of-interception characteristics, MILSTAR and AEHF are referred to as protected systems.
In addition to the protected and wideband systems being developed by the Air Force, the Navy is responsible for the development of narrowband systems operating at ultrahigh frequency (UHF). Although there is less bandwidth available at UHF, these frequencies penetrate foliage and urban structures and are important for mobile users with small terminals. The Mobile User Objective System (MUOS) will replace the UFO system, providing significantly more capacity to the warfighter.
To augment the available military satellite communications, the Navy relies heavily on commercial satellite communications. Under the Commercial Wideband Satellite Program (CWSP), the Navy leases C-band transponders from Intelsat and SES AMERICOM. The 56 kbps L-band Inmarsat channels mentioned above are leased from Intelsat. During Operation Iraqi Freedom, commercial satellites provided about 70 percent of the Navy’s long-haul communications
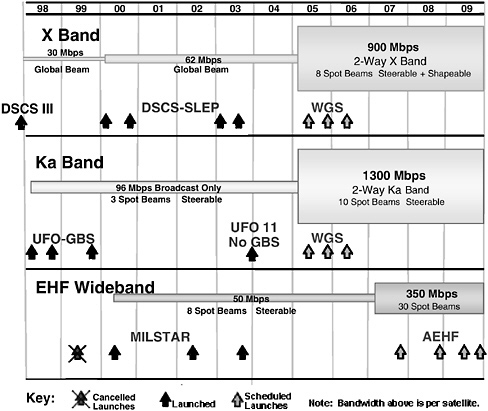
FIGURE 6.2 Communications satellite systems currently in development. Programmed systems have potential to increase available data rates. SOURCE: RDML Thomas J. Elliott, USN (Ret.).
capacity: CWSP provided 30.2 Mbps and Inmarsat provided 3.7 Mbps, while DSCS provided 16.2 Mbps. The possibility that the Navy’s access to commercial satellite communications could be denied by an adversary employing a variety of information warfare techniques is a serious problem.
Although the communications satellite systems coming online in the near future will provide additional bandwidth for joint forces, potentially including naval forces, a number of cautionary notes are necessary. First, the increased bandwidth will be available to the Navy only to the extent that the Navy makes the investments in the terminals and other infrastructure needed to use these systems. Second, DOD military satellite programs have a history of budget and schedule problems.1 Third, at least some authorities believe that even if the
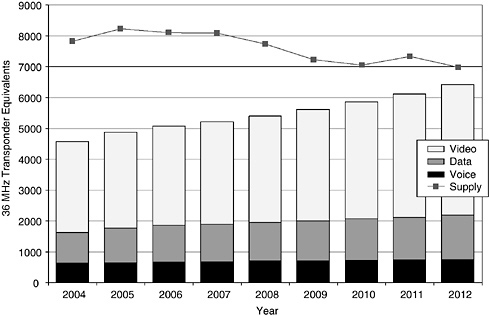
FIGURE 6.3 Excess commercial satellite capacity is forecast to shrink between 2004 and 2012. SOURCE: Adapted from FUTRON Corporation, “FUTRON 2003 GEO Commercial Satellite Demand,” October 2003, <http://www.futron.com/spaceandtelecom/src/satservices.htm>. Accessed January 26, 2006.
promised bandwidth materializes, it will be insufficient for future operations.2 Fourth, the great majority of the additional bandwidth is being provided by spot beams; ships outside the spot beams will not benefit from this bandwidth. Fifth, if military satellite communications programs do not provide the needed bandwidth, there may not be commercial bandwidth available to make up the shortfall (Figure 6.3). Thus, at least in the near future, efforts will be needed to manage the use of bandwidth and to use it efficiently.
6.2 FUTURE NAVAL COMMUNICATIONS
FORCEnet and the enabling Global Information Grid (GIG) architecture hold out the prospect of a transformational change in joint Service communications capabilities whereby bandwidth is no longer a constraint. As described in Chapter 3, the FORCEnet architecture must support a wide variety of joint Service applications and services, each with varied qualities of service, ubiquitous networking capability, open architecture, commercial standards, compatibility with core networking capabilities and applications being developed, and scalability.
The transformational infrastructure for the GIG includes three physical-layer components:
-
A high-speed terrestrial backbone, enabled by the GIG-Bandwidth Expansion (GIG-BE) program;
-
The extension of this backbone into space, using both Free Space Optical (FSO) and radio-frequency (RF) communications, under the Transformational Satellite (TSAT) program; and
-
The extension of the GIG to mobile users, employing the Joint Tactical Radio System (JTRS).
Networking services (e.g., Network Centric Enterprise Services [NCES]) will be supported on the GIG infrastructure through standardized multilayer protocols and interfaces. This architecture is schematically shown in Figure 3.5 in Chapter 3.
Different systems and interfaces needed in the GIG architecture are at various levels of maturity. For example, the GIG-BE program and Teleport (GIG-BE gateways for satellite communications connectivity) are already offering some operational capabilities in their phased deployment. But other systems, particularly TSAT, are many years away from doing so.3 In addition, JTRS is a key enabler for the FORCEnet vision, but the JTRS program has experienced significant cost overruns, schedule delays, and performance issues. Because of these problems, the 2006 House defense authorization bill has language that would result in the elimination of the current JTRS waiver process, allowing the Services to purchase tactical radio communications to fulfill their immediate requirements.4
6.3 MAJOR ISSUES
6.3.1 Transition
The Navy faces a difficult challenge with respect to the transition from the current environment of limited communications bandwidth5 across legacy and commercial communications links, to the environment foreseen in the TCA vi-
sion of unlimited bandwidth across uniformly Internet Protocol (IP)-enabled networks. Limitations in current protocols and their continuing evolution do not make the task any easier.
The committee fully subscribes to the vision of eliminating bandwidth as a constraint and urges the Navy to aggressively pursue opportunities to provide additional bandwidth to its platforms; nevertheless, it recognizes that during the transition period, which is likely to last a decade or more, bandwidth will continue to be limited. The committee therefore recommends that the Navy establish (time-phased) bandwidth allocations by platform and that it ensure that the C4ISR applications which it develops and deploys are consistent with these allocations. Further, the committee recommends that the Navy aggressively pursue efforts such as those demonstrated recently in Trident Warrior 03 exercise using the Automated Digital Networking System (ADNS) to use bandwidth more efficiently.
In carrying out this recommendation, the Navy should learn from ongoing efforts conducted by commercial firms (e.g., Connexion by Boeing) and the other Services. For example, under its Information For Global Research (IFGR) program,6 the Air Force Research Laboratory has developed a capability to make multiple disparate communications channels appear as a single channel (i.e., inverse multiplexing across multiple data radios) to provide transparent air-to-ground IP connectivity to multiple IP hosts onboard aircraft. In October 2003, the IFGR system was integrated and successfully tested onboard an E-8C Joint Surveillance Target Attack Radar System (JSTARS) platform. In December 2003, IFGR underwent a series of successful field evaluations with the Air Mobility Command. As a result of these tests and evaluations, IFGR was selected in February 2004 for deployment on JSTARS as a fast and inexpensive means for the network-enablement of Air Force command and control, intelligence, surveillance, and reconnaissance (C2ISR) weapons systems.
6.3.2 Architecture Development
The Naval Network Warfare Command (NETWARCOM) is currently describing the Navy’s operational communications architecture in some detail,7 but for the future an architecture is required that will ensure that the Navy can continue to execute its missions effectively. The tasking for the present study
called for developing “an architecture,” and the committee has advanced its general views concerning such an architecture (see, in particular, Figures 3.1 and 3.5 in Chapter 3). There are, however, many policy, budgetary, and other related issues that impact the development of a communications architecture, and these matters are beyond the scope of this study.
The committee does recommend the establishment of a communications architecture group tasked with creating a realizable architecture. This architectural group should address the policy, budgetary, and technical issues that are required to achieve the architecture. It should develop plans for tests required to determine latencies and to project future bandwidth needs. This group would develop a fully realized architecture to be implemented in the 2015 time frame as well as a series of transitional architectures to bridge current and future capabilities.
For these architectures to be meaningful, they must ensure that the naval objectives of the future can be met. To accomplish this requires a broad effort that starts with doctrine, develops structure and user-based performance metrics, and addresses issues of security and robustness. The current naval communications capability has performed well in recent operations, but it may be found lacking in a high-stress environment with an adversary waging aggressive information warfare (IW). For example, at least some of the current Navy communications capabilities are easy to deny—most particularly, commercial communications systems such as Inmarsat.
Architecture development requires detailed study and analysis. Given the critical role envisioned for network-centric operations in future naval operations, this task should not be underresourced. Further, the architecture development team should be empowered by the most-senior naval leaders to have access to all of the required information. The product—a 2015 network-centric fully realized architecture and transitional architectures, with performance metrics and a detailed roadmap to execute the development—should be broad enough that the Chief of Naval Operations (CNO) can use it to address Navy-wide issues and provide guidance for programmatic directions. This product also needs to include the details for the policy, technology, and other elements, such that they can be developed and worked as part of an integrated approach.
The most important attributes of the communications architecture to be developed are the flexibility, scalability, interoperability, and robustness that will permit adapting to the many uncertain situations of the future. However, it is also necessary to develop user-oriented performance metrics for the design and quantification of the future communications architecture to ensure that adequate bandwidth is provided to support critical warfighting requirements. This is in contrast to today’s approach, which seems to accept very limited bandwidths and doles out communications capacity in small increments, with limited understanding of the impact on overall mission execution.
To help ensure that effective communications are available, user-oriented analyses of the architecture should start with the assumption of an aggressive
adversary attacking the “network-centric heart” of projected naval and joint military operations: the communications systems. This means that the issues of robustness and of communications systems monitoring, redundancy, and management, as well as provision of the performance required to ensure successful operation, need to be addressed as part of the core architecture. Strategies and policies supporting operations, together with the associated performance metrics, need to be developed in coordination with the appropriate organizations. These strategies and policies need to include the following, among others:
-
Support for all of the elements of Sea Power 21 and the C4ISR needs discussed in this and the other chapters of this report.
-
Reach-back and trace-back capabilities that can scale to reach naval and other analysts who might support surge operations. These capabilities should also include multiple communications paths to distributed data and computing resources for rapid data access and for the generation of actionable information. These should all be scaled to support a greatly increased operations tempo.
-
The conduct of network-centric operations across the Services and combatant commands (COCOMs) and with the various coalition partners. Particularly important issues for network-centric operations include Information Assurance (IA), data insertion and access policies, and the maintenance of data integrity and currency.
-
Support to the DOD doctrine of tasking, posting, processing, and using (TPPU). For example, will data collected from high-volume data producers such as the F-18 aircraft’s shared reconnaissance pod (SHARP) be stored (if so, where?) for TPPU access by all of the other Services and joint task force members, and what communications capacity will be available to support these actions?
-
The development of a robust infrastructure with alternative communications paths and distributed and synchronized data storage and computing. Further, it is important to include the network-monitoring and -management capabilities for an understanding of the state of the network and to enable fighting and recovering from network attacks.
Questions that need to be addressed with regard to strategies and policies include the following: What organization will establish the access and IA policies? Where will the distributed storage and network-management functions be located to ensure a scalable robustness? How will data integrity, currency, and synchronization be maintained? Will the archives of naval information be integrated with others, such as those of the National Geospatial-Intelligence Agency (NGA)?
Other factors that will influence the architecture include the number of units that might be involved in operations concurrently and the degree of reach-back and trace-back, and how these efforts are to be apportioned among local, theater,
and continental United States (CONUS) support nodes for scenarios that are stressful. Further scaling issues will come from new capabilities in ISR, such as the NGA’s migration to the high-definition television (HDTV) standard for unmanned aerial vehicles (UAVs) and the significant increase in the number of UAVs and other collection capabilities. Migration to the HDTV standard will greatly improve the quality of video collected, improving target recognition and resolution, but it will require increased communications bandwidths. The increase in collection capabilities will significantly increase the areas that can be covered in a given amount of time, which will improve the overall strike response capability.
6.3.3 Internet Protocol Maturity and Security Issues
Network-centric capabilities build on the use of the IP and, in particular, on the DOD-mandated Internet Protocol, version 6 (IPv6).8 As described in Chapter 3, the use of the IP facilitates interoperability and provides for improved bandwidth utilization over current frequency-division multiplexing approaches. However, IPv6 is not yet widely deployed commercially, and the Internet Engineering Task Force (IETF) continues its efforts on value-added features for IPv6. These features include such important areas as transition mechanisms (from IPv4 to IPv6), security, routing, and quality of service (QoS).9 In particular, the security issues associated with the transition to IP are of serious concern to the committee (see Appendix C, “Information Assurance,” in this report).
6.3.4 Force Establishment While Under Way
To support the requirement for an adaptive and composable C4ISR architecture, ships need to be able to establish communications rapidly, while under way, with whatever platforms are necessary. The ability to do this requires automated spectrum- and key-management capabilities:
-
Spectrum management.10 A robust spectrum-management capability is needed to establish communications rapidly for a naval strike group. Further,
-
against an aggressive enemy, real-time spectrum management is needed to respond to jamming attacks as well as to adapt to U.S. forces’ own jamming and other communications needs. To make this possible, a distributed spectrum-monitoring capability must be available on the strike group platforms. The capability must also include the needs of coalition forces and must comply with international laws on spectrum usage for both peace and war. Further, the models and algorithms that are used to develop the spectrum-management plans need to be distributed so that the loss of any particular subset of platforms does not result in the loss of the capability to manage the spectrum.
-
Communications security and key management.11 Having a rapidly configurable communications-security and key-management capability across the strike group network’s security devices and the legacy and network-centric wave-forms is also critical to rapid force establishment. Within policy guidelines, this ability must include coalition as well as joint force elements. It must be end to end, including reach-back to CONUS, as well as extending horizontally across a diverse force. This ability must also be distributed, so that loss of access to key nodes will not hamper operations. Further, there must not be reliance on preplaced keys that restrict options for rapidly configuring diverse force elements and are a potential vulnerability if a unit is captured before the encryption units can be destroyed.
The establishment of network-centric operations (NCO) capabilities while ships are under way should be smoothly scalable in size, from a few platforms to multiple battle groups with other participating elements and extensive reach-back to theaters of operation and CONUS. The architecture must have options to deal with lost communications links or platforms and/or nodes.
In addition, it is necessary to develop metrics for underway force establishment and to test deployed systems to ensure that goals for these metrics are achieved. For example, a three-ship strike action group (SAG) in transit might establish the communications required for self defense against a set of possible attacks and concurrently initiate communications for horizontally expanding the force envelope with six new ships and eight new aircraft, as well as adding the reach-back to six nodes for support and for developing strike targets. Concurrently, backup communications plans against jamming would need to be put into a ready mode for very rapid reconfiguration if needed. A metric might be to be able to integrate each platform or node fully in less than 2 minutes and to have the total force and reach-back fully functional in less than 10 minutes. The time to respond to jamming and other attacks should be on the order of a few seconds.
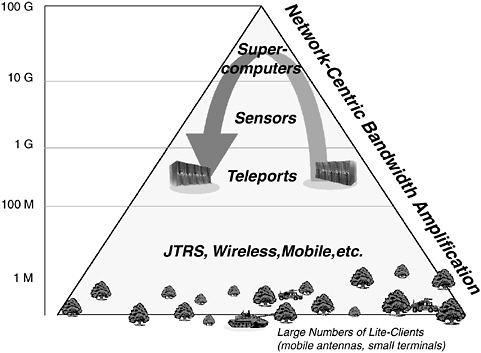
FIGURE 6.4 Bandwidths for network-centric operations, for constant response times, and large numbers of users. Simple queries trigger extensive bandwidth utilization. NOTE: G, gigabyte; M, megabyte. SOURCE: Courtesy of Henry Dardy and Basil Decina, Naval Research Laboratory, Washington, D.C.
6.3.5 Bandwidth Requirements
Figure 6.4 shows how network-centric operations stress the “core” bandwidth as the number of users grows and their support increases, if response times for information exchange are to remain the same as they are now. Network-centric operations and TPPU increase the number of users and the amount of data that users can access. Further, online value-adding functions may require moving information to different locations in order to extract actionable information. These needs all drive an increased demand for bandwidth if response times are to remain the same (or shorten, as future doctrine requires). The apex of the pyramid in the figure represents high-end technology work, and just below that are high-end exchanges across distributed supercomputers and large-scale distributed data-storage capabilities that search complex data sets quickly to provide high-quality targeting information to naval forces. The middle-level exchanges move large intelligence, surveillance, and reconnaissance (ISR) collections, such as those generated by the SHARP pod for the F/A-18 E/F Super Hornet and other collec-
tion data sets, to storage locations where they can be quickly accessed under the TPPU model.12
If the numbers on Figure 6.4 seem too high to be reasonable, it should be pointed out that in 2004 the Chinese announced that they had a 40 Gbps capability operating in a test environment with applications. The Navy needs to develop an aggressive, longer-term plan that provides for significant increases in bandwidth. Speed of access to ever-larger amounts of information by large numbers of users will be one of the key advantages of network-centric warfare. However, as discussed in Section 6.3.1, during the transition to high-bandwidth communications, it will be necessary for the Navy to allocate bandwidth and to ensure that applications take into account bandwidth limitations.
6.3.6 Validating the Architectures by Testing
It is difficult to simulate wartime communications. Simulations do not have the resolution today to capture the interactive effects of complex, network-centric communications systems that support the many functions involved in large-scale conflict.
Because it is so important to have the communications architectures and their scaling correct, large-scale tests will be required to provide insights into communications needs. Since the capabilities included in the architectures will not yet be developed, this testing will be challenging. Techniques that may be helpful include the use of commercial wideband communications and/or the preloading of data on ships to simulate high-capacity military communications.
Ensuring that the testing provides the intended information will require careful preparations, controlled execution, and extensive monitoring. The tests will need to be subdivided into manageable parts. For all of the activities, extensive monitoring of information movement and shortfalls will be required. It is important that the system be set up to capture information end to end and across the multiple platforms so as to obtain a good understanding of the communications performance for the force.
|
12 |
The SHARP pod, which supports large-area collections for multiple strike and other missions, can collect data at over 1.5 Gbps (compressed). Moving the data in a timely manner from multiple missions to support multiple strike and other missions is a significant challenge. Today, only subsets of the data are transferred on the Common Data Link (CDL) communications system with a peak 274 Mbps rate. Other data can be stored and off-loaded later, adding to latency. Also, see Appendix D, Section D.1.4. The NCO challenge of “posting” these data for “all” to access is not solved, but for timely operations it must be solved. See, in Chapter 7 in this report: Figure 7.2, on Distributed Common Ground Station levels of integration, for how these data should be integrated in a timely manner, and Figure 7.6 for more-general information on data rates. This challenge will become even more difficult as sensors advance. |
Examples of metrics that need to be captured during these tests include the following: the time required to bring the various elements into full network-centric operation, the time required to move information, the number (and importance) of missions that are delayed because of lack of communications, and the number of personnel and the time required to recover from various attacks. To help ensure understanding of the communications functions, technical experts who can interpret the results should be deployed in most key network locations on the battlefield.
6.3.7 Developmental and Operational Testing
In addition to the tests described above to help quantify capacity needs and to validate other aspects of the naval communications architectures, there is a need for ongoing stress testing of the communications systems.13 This testing is needed to ensure that network-centric capabilities are available under the stress of combat and attack. In order to identify hidden weaknesses, tests should have data loading and other stresses increased to the point that communications systems fail. Weaknesses can then be eliminated or planned for and avoided. To ensure that real tests and not demonstrations are conducted, the testers must be given the opportunity to disrupt operations, if necessary.
The GIG (with its IP over asynchronous transfer mode [ATM]) that successfully supported Operation Iraqi Freedom and Operation Enduring Freedom came from this type of large-scale testing. Early development testing was used to attain insight into the issues of operational value, technical limitations, and information security associated with large-scale network-centric operations. The testing was conducted in the early and mid-1990s. An example was the August 1994 test conducted with the U.S. Atlantic Command (USACOM) (precursor of the Joint Forces Command), using the USS George Washington battle group located in the Mediterranean; the USS Mount Whitney as the command ship in the Caribbean; Army units operating in Ft. Hood, Texas; and air strikes (simulated as from the carrier) on the Fallon, Nevada, range. Further, National Command Authority was involved, and imagery and other products for strike were available from national sources.
Information for this 1994 test was shared across the networks, including all of the information for strike planning, which was done in a collaborative manner, and video of the targets used for battle damage assessment. The information was posted in the Imagery Repository and Dissemination System so that any user could access it. The USACOM summary message (USACOM 222136Z August) credited this testing with five firsts in the areas of sharing across multiple areas of responsibility (AORs) and with the National Command Authority, and so on. Prototype ATM encryptors were employed to let users understand encryptor impacts
and to help refine IA issues so that these issues could be resolved. From the technical and network-capacity sizing perspective, extensive information was gained that was used in designing the switches and routers, security devices, and architectures that became the core networks supporting Operation Enduring Freedom and Operation Iraqi Freedom. In a presentation on lessons learned from Operation Iraqi Freedom, Brigadier General Robert W. Cone, USA, credited those improvements for a “42 times increase in capacity over Operation Desert Storm.”14
The committee suggests tests of the communication systems that could include the following:
-
Early technology and development testing. Specific testing categories include these: (1) identifying potential candidates among emerging technologies to improve capabilities, (2) evaluating proposed IA concepts using mock-up security devices to lead to an understanding of the potential impacts, (3) determining the ability of new systems to scale to support naval operations, (4) determining the effects of jamming and disruptions of service, (5) determining the ability to recover from attacks and surges, and (6) evaluating joint interoperability by using the GIG Evaluation Facility (see Figure 6.5).
Developing an understanding of the IA issues should motivate the naval elements to very active participation in this testing so that accurate insights can be developed for providing the feedback that Patrick M. Kern’s memorandum of January 24, 2005 (see Appendix C) requested from the Navy in 2005 and 2006. Another important aspect of testing can be the introduction of competition by different approaches to achieve common user performance metrics. This competitive process was used in the initial GIG developments. The GIG process started with the DOD having hundreds of unique communications encryptors and systems (“a tower of babble”) and ended up with secure, interoperable, and scalable communications based on commercially derived protocols. This major change across the DOD was not a major program and it had minimal congressional funding; it was accomplished by using a competitive process across many DOD organizations.
-
Tests to demonstrate the recovery capabilities of operational networks.15 This type of test requires the periodic shutting down and restarting of all of the naval networks to ensure that, if they go down under attack, there are tested
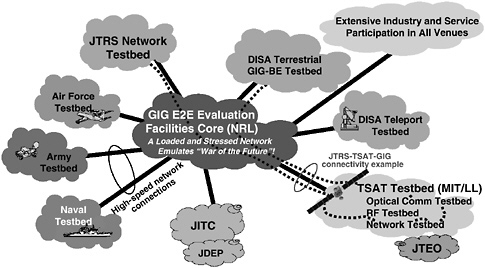
FIGURE 6.5 Global Information Grid-Evaluation Facilities (GIG-EF) end-to-end vision: a place to test early and test often. NOTE: JTRS, Joint Tactical Radio System; DISA, Defense Information Systems Agency; GIG-BE, Global Information Grid-Bandwidth Expansion; GIG E2E, Global Information Grid End to End; NRL, Naval Research Laboratory; JITC, Joint Interoperability Test Command; JDEP, Joint Distributed Engineering Plant; TSAT, Transformational Satellite; MIT/LL, Massachusetts Institute of Technology/Lincoln Laboratory; RF, radio frequency; JTEO, Joint Terminal Engineering Office. SOURCE: Courtesy of Henry Dardy and Basil Decina, Naval Research Laboratory, Washington, D.C.
-
methods for recovery and personnel trained to execute those methods. Metrics for recovery include time, the numbers of people required, and the ability to recover from distributed locations. This class of testing should be done at least once every quarter year for all elements of networks that the naval forces use, including the Navy/Marine Corps Intranet (NMCI). As recovery capabilities improve and the time to recover is reduced, tests should be done without warning and in the middle of major exercises.
-
Surge of forces testing. This testing should be conducted to simulate the communications surges of the emerging adaptability and composability doctrine described earlier. The initial tests should be planned in order to capture data, to understand areas in which training is required, and to develop new tools for assisting in the surge setup. Subject experts should be involved across the battle group and the supporting locations to help interpret the tests. Later tests should be called with little warning, in order to exercise the doctrine using capabilities available without special preparation, often termed “come as you are.”
-
Layer-specific testing. These tests should test the open systems interconnection (OSI) layers; for example, the physical layer should be engaged in jam-
-
ming and other electronic warfare (EW) measures, while the higher layers should be attacked by various denial-of-service and virus techniques. These tests should scale up to attacks that take out the primary network-management and -control nodes and should force the reconfiguration of the supporting management and control functions to backup nodes. In addition, access to reach-back nodes should be forced to go to backup paths.
6.3.8 Potential Technology Advances and Needs
Many technology developments are emerging that will enhance naval NCO. Following are some of these:
-
The Advanced Multi-function Radio Frequency Concept (AMRFC). The AMRFC has the objective of integrating radar, electronic warfare, and communications into a common set of apertures, signal and data processing, signal generation, and display hardware. This type of approach will reduce the number of antennas on ships, which in turn will reduce their radar cross section, permit an easier introduction of new capabilities, help reduce electromagnetic interference, and enable improved spectrum management.
-
The Secure Mobile Environment (SME). The SME, which is being developed by industry for the National Security Agency (NSA), provides a converged cellular telephone, personal digital assistant (PDA), and video and data capability. It will provide both Future Narrow Band Digital Terminal (FNBDT)16 and High Assurance Internet Protocol Encryption (HAIPE) security and will permit Type I and non-Type I encryption17 and have RF interfaces to support a wide range of uses.
-
A 70 to 90 gigahertz satellite communications technology. This new technology will potentially reduce the size of shipboard antennas while significantly increasing bandwidth to the platforms. In addition, there would be a reduced likelihood of the detection and jamming of communications between ships and satellites because of the water vapor absorption of signals that otherwise might be intercepted by enemy planes or ships. A satellite employing this technology could keep a dish antenna trained on a battle group to provide high-speed over-the-horizon connectivity. However, there would be a potential loss of communications during rain.
-
The Large Data Advanced Concept Technology Demonstration (ACTD).
-
This ACTD is sponsored by NGA and is being developed by the Naval Research Laboratory (NRL). It will potentially enable very large amounts of information to be posted, processed, and used as part of NCO under the TPPU model. This capability will scale to exabytes of storage, will be distributed across multiple organizations for redundancy, and will be self-synchronizing to maintain data currency. It will enable data capture and exchange at numerous locations at speeds starting at 10 Gbps and migrating to 40 Gbps and 160 Gbps. It will support IP, legacy systems, and the new low-cost, high-speed InfiniBand, discussed below. It will enable connections with almost all legacy protocols, as well as accommodate future protocols, by using the new protocol-neutral technology being developed by NRL, other government organizations, and industry. Automatic data synchronization will be done on data being processed and extracted—as, for example, in the development of a joint strike package. This synchronization leads to a new concept, building on videoconferencing, called data conferencing, that can be conducted across multiple physical sites using data in real time as they are being received. This new capability will reduce the time needed for the Navy to develop complex strike packages and other materials.
-
InfiniBand is an emerging, high-performance protocol developed by industry.18 It has the important feature of lower costs for high performance. For example, the costs for a 10 Gbps InfiniBand connection are already approaching 15 percent of a 10 Gbps Ethernet connection. Further, InfiniBand offers high QoS. It can be directly connected into servers or computers, saving costs of high-speed routers. An important feature of InfiniBand is that it will interoperate with both the GIG-BE with IP/Multi-Protocol Label Switching (MPLS)19 as well as the Defense Information Support Network (DISN) ATM System (DATMS)20 with IP/ATM and other protocols. The lower cost makes it a good candidate for ship and base architectures, enabling a low-cost migration to the upper levels of the pyramid for naval capabilities. NRL is doing work to demonstrate InfiniBand’s effectiveness over wide areas, including the exchange of multiple 10 Gbps streams between the 2004 Super Computer Conference in Pittsburgh, Pennsylvania; Lincoln Laboratory in Lexington, Massachusetts; and NRL in Washington, D.C. This effectiveness was also demonstrated between the Optical Fiber Conference in Anaheim, California, and NRL in Washington, D.C.
-
Wireless networking.21 Wireless networking is an area of high importance and high activity at this time. The Navy should be engaged through its technology base and IA inputs to ensure that its interests are met in the final configurations. Some of the highlights are as follows. At the Internet Engineering Task Force, the important wireless efforts are known as MANETs. The routing is a challenge for this development. To provide options at the present time, four routing protocols are being advanced by the IETF.22 The Defense Advanced Research Projects Agency (DARPA) is a significant source for sponsoring work on MANET under its Connectionless Network Program. Another DARPA effort that relates to wireless networking is called Defense against Cyber Attacks on Mobile Ad-hoc Network Systems (DCAMANET). In addition to these areas, the Institute of Electrical and Electronics Engineers (IEEE) is moving to improve wideband wireless with the IEEE 802.16 standard for base station data rates up to 280 Mbps and a range of 30 miles, and the ultrawideband (UWB) standards with rates over 400 Mbps over short ranges.
-
Autonomic network defense. As discussed in this chapter, the potential threat of nation-state information warfare attacks on naval communications networks is of serious concern to the committee. Computer network defense is currently based on a human-in-the-loop approach, which is too slow for large-scale, fast-acting threats such as computer-based worms. DARPA has been addressing the development of autonomic network defense technology in a series of programs, the most recent of which is its Dynamic Quarantine of Worms program. This program will develop the capability to detect and respond to worm-based attacks against military networks automatically, provide advanced warning to other DOD enterprise networks, study and determine the worm’s propagation and epidemiology, and provide off-line rapid-response forensic analysis of malicious code to identify its capabilities, modalities, and future behavior. Technical approaches include the automatic and dynamic quarantine response and forensics analysis of malicious code that will employ static and dynamic code analysis for program understanding.
-
Transmission Control Protocol (TCP) scale-back mitigation. In the future, IPv6 with flow control and multicast should provide a TCP scale-back solution. There is still work to do in refining the protocols and in adapting the HAIPE encryption to find the final solution. In the near term for relatively narrowband tactical communications, video multicast capability has been dem-
|
21 |
The discussion of wireless networking has excerpts from NSA’s “The Next Wave,” Vol. 13, November 3, 2004; and the IETF, DARPA, and MIT Media Laboratory Web sites at < www.ietf.org>, <www.darpa.mil>, and <www.media.mit.edu>, respectively. Accessed January 26, 2006. |
|
22 |
These routing protocols are as follows: Ad-hoc On-demand Distant Vector (AODV) routing, Topology Broadcast Reverse Path Forwarding (TBRPF), Dynamic Source Routing (DSR), and Optimized Link Status Routing (OLSR). |
-
onstrated using the Negative Acknowledgement (NACK)-Oriented Reliable Multicast (NORM) Protocol (IETF RFC 3940) as part of a NACK Oriented Reliable Multicast Video Streaming System (NOVISS) effort. This demonstration used a near-term substitute for JTRS with the Wideband Network Waveform (JTRS WNW), the AN/VCR-99(A), and demonstrated the feasibility of this approach for video. The NOVISS approach, while more efficient than TCP, is not a final solution, as delays are introduced that would impact videoteleconferencing, for example. The use of protocols with end-to-end QoS (such as ATM) to carry TCP/IP reduces the TCP scale-back in many cases, and for high-speed networks InfiniBand can be used. Performance-enhancing proxies (PEPs) could potentially improve degraded TCP performance caused by the characteristics of specific link environments but are incompatible with end-to-end encryption.23 DARPA has a research project, Situation-Aware Protocols In Edge Network Technologies (SAPIENT),24 that seeks to move beyond static proxy implementations to a new generation of cognitive protocol architectures.
-
Universal Communication Interface Module (UCIM). UCIM provides a standardized, scalable C4ISR network-centric interface that simplifies and reduces costs of managing both local and distributed assets. UCIM has an IP adapter capability for legacy radios and enables seamless migration to JTRS radios. It manages the cross banding of communications as well as encryption configurations and co-site interference. It can scale across many platforms and hundreds of users. Early testing by the Marine Corps found UCIM to be quite effective.25
-
Needed technical advances. These include improved spectrum-management tools and IA capabilities, including key-management technologies as well as object-level and multilevel encryption; more efficient and wider-bandwidth communications links to improve communications; faster, lower-cost, real-time data compression techniques for sensors such as SHARP and HDTV video; and improved undersea communications, data exfiltration, and relay capabilities. All of these needed advances reinforce the requirement for an aggressive communications science and technology program.
6.3.9 Training
To execute NCO successfully, the future naval force will need to require that almost all naval personnel be trained for communications operations. Architecture concepts, rapid force establishment, network attack and recovery, and IA, to name a few areas, need to be taught to all officers and enlisted personnel. NSA should provide the IA course, which should include classified materials, so that the naval force is prepared for the threats that might be used against it. Since network-centric operations impact almost everyone, versions of this training should be required not just of those directly involved in communications but of almost all officers and enlisted personnel whose use of or decisions on network-centric capabilities could impact mission execution.
6.4 FINDINGS AND RECOMMENDATIONS
The findings and recommendations of this chapter are presented below.
Finding: The Navy faces a difficult challenge with respect to the transition from the current environment of limited communications bandwidth across legacy and commercial communications links, to the environment foreseen in the Transformational Communications Architecture (TCA) vision of unlimited bandwidth across uniformly IP-enabled networks.
The committee fully subscribes to the vision of eliminating bandwidth as a constraint and urges the Navy to aggressively pursue opportunities to provide additional bandwidth to its platforms; nevertheless, the committee recognizes that during the transition period, which is likely to last a decade or more, bandwidth will continue to be limited. The challenge is to organize and conduct phase-development efforts to best cope with current and interim constraints while simultaneously migrating toward the long-term vision.
Recommendation: The Navy Chief Engineer and his or her Marine Corps counterpart should establish (time-phased) bandwidth allocations by platform that are consistent with the development schedules of communications satellite programs and ensure that the C4ISR applications that are developed and deployed are consistent with these allocations. To increase the efficiency of bandwidth utilization and ease the transition to the TCA, the Navy should aggressively pursue efforts, using available technology, to accommodate IP on legacy communications channels to ships.
Examples of such technology include the dynamic bandwidth allocation and quality-of-service management software demonstrated by the Navy in Trident Warrior 03 and the inverse multiplexing and mobile IP software developed by the
Air Force Research Laboratory under the Information For Global Reach Program. The latter software has been selected by the Air Force for operational implementation on the JSTARS aircraft.
Finding: To take advantage of the enormous benefits offered by network-centric capabilities, a global network-centric naval communications and processing network architecture is needed—an architecture driven by the doctrine and overarching information architecture for rapid force application, without special preparation (i.e., “come as you are”).
The communications architecture requires the following capabilities:
-
Rapid configuration of “come as you are” force networks. This capability should provide real-time spectrum management, real-time encryption key management, and network management, including the development of primary and backup network monitoring and control, with a core of preconfigured responses to EW and IW attacks.
-
Surge communications capacity to acquire information required for full-range, rapid force application missions, including information for protecting the force. To develop the communications capacities required, both detailed analysis and large-scale sizing tests need to be conducted with projected new capabilities, such as improved ISR imaging and videoteleconferencing. The Navy should give priority to acquisition of the increased bandwidth capacity required to execute the doctrine.
-
Information assurance capabilities to protect the force. These capabilities need to cover the full range of attacks across the multiple layers of network-centric communications, ranging from antijamming of physical links, to prevention of denial-of-service attacks across the network, to false manipulation of applications.
-
The equipping of all platforms to be able to receive satellite broadband broadcasts (Global Broadcasting System and others) in order to enable operations under electromagnetic emission control (EMCON) conditions. The entire force also needs to be equipped with low-probability-of-interception satellite communications as well as other modes of communications.
Recommendation: The Navy Chief Engineer and his or her Marine Corps counterpart should establish a naval architecture task force to resolve the policy, budgetary, performance, and technical issues that need to be addressed to enable the development of objective and transitional communications architectures. The Chief of Naval Operations (CNO) and the Commandant of the Marine Corps (CMC), should support the task force in its efforts to address and resolve the many issues involved with developing a meaningful architecture.
For these architectures to be meaningful, they must ensure that the naval objectives of the future can be met. To accomplish this requires a broad effort that starts with doctrine, develops structure and user-based performance metrics, and addresses issues of security and robustness. The current naval communications capability has performed well in recent operations, but it may be found lacking in a high-stress environment with an adversary waging aggressive information warfare (IW). For example, at least some of the current Navy communications capabilities are easy to deny—most particularly, commercial communications systems such as Inmarsat.
Architecture development requires detailed study and analysis. Given the critical role envisioned for network-centric operations in future naval operations, this task should not be underresourced. Further, the architecture development team should be empowered by the most-senior naval leaders to have access to all of the required information. The product—a network-centric fully realized architecture to be implemented in 2015 and transitional architectures, with performance metrics and a detailed roadmap to execute the development—should be broad enough that the CNO can use it to address Navy-wide issues and provide guidance for programmatic directions. This product also needs to include the details for the policy, technology, and other elements, such that they can be developed and worked as part of an integrated approach.
Finding: Successful network-centric operations are fundamental to the future Navy. There are many complex facets to modern communications networks that need to function together to ensure that the networks will work properly under the stresses of combat.
Recommendation: The Assistant Secretary of the Navy for Research, Development, and Acquisition (ASN[RDA]) and the Naval Network Warfare Command (NETWARCOM) should establish an aggressive network-testing program to ensure that the systems will have the capabilities needed under the stresses of combat. This testing program should start with the development level, build on testing at the GIG-BE, and have regular operational tests. The operational tests should include the regular shutting down and reactivating of the large naval networks, including the NMCI. Further, these tests should include data overloading, jamming, and denial of communications paths so as to ensure that there is a continually updated understanding of the limits of the current configurations and to ensure the backup capabilities. Interaction with red teams would help ensure that the command-and-control (C2) systems are robust.
Finding: The naval forces are severely limited in communications capacity (bandwidth) to support network-centric operations and to enable the introduction of new capabilities such as videoteleconferencing and new ISR capabilities. Many of the naval units are forced to make either/or trade-offs that could potentially
impact operations. For example, to conduct videoteleconferencing, an emerging important function, up to half of a ship’s other communications must be halted. Further, many units depend on the commercial Inmarsat, which is vulnerable to several classes of disruption.
Recommendation: The ASN(RDA) and NETWARCOM should immediately assign a high priority to increasing the bandwidths to every platform. Options include the following: (1) increasing the rate of GBS deployments and increasing the number of ships to which GBS is deployed; (2) investigating use of the High Frequency Automatic Link Establishment (HF ALE) to request large data transfers over the GBS satellites and for other communications coordination activities; (3) as a near-term-only capability, increasing commercial Inmarsat bandwidth to communications-disadvantaged ships to enable them to be meaningful participants in developing future network-centric operations concepts.
























