4
Innovative Counterfeit-Deterrent Features
This chapter summarizes the most outstanding proposed counterfeit-deterrent features that the committee estimates can be developed for implementation in future series of Federal Reserve notes (FRNs) within what is considered to be an intermediate development time of less than 7 years. The chapter also discusses the process used by the committee to assess the value of proposed features and to rank a subset of them for inclusion in this report. The next chapter summarizes the longer-term, disruptive feature platforms.
FEATURE ASSESSMENT
The committee was tasked to “identify features, materials, and technologies to deter counterfeiting of FRNs, and assess their relative effectiveness” against both current and emerging threats. In particular, the committee was asked to consider novel, noncommercial, and potentially unique features that could be incorporated in notes in the longer term and, furthermore, to consider features that would be aesthetically pleasing and amenable to visual authentication. As a secondary task, the committee was asked to evaluate features for use by the blind, for law enforcement (forensic features), and in machine authentication. In order to decide what features might meet these demands, the committee devised an assessment and evaluation process. In developing this process, the committee concluded that the ideal anticounterfeiting feature has two overarching characteristics: it deters (or prevents) reproduction and it facilitates authentication. These two concepts are at the core of the assessment approach used here. The committee also concluded that
a feature differs in deterrence value for each class of counterfeiter, depending on the technology that each employs, as summarized in Table 4-1.
Likewise, a feature’s detectability depends on the detection method employed, the nature of the currency transaction, and the education, training, and cognitive capabilities of the recipient of the note. While many transactions take place in a venue in which unassisted human authentication is the preferred (or only) option—such as in a store, restaurant, or taxi—an increasing number of transactions involve alternative assisted methods. These assisted methods might deploy a portable, low-cost, nonproprietary basic device that is generally available and easy to use, or a dedicated machine reader such as an automatic currency acceptor that does not involve a human cash handler. Examples of existing simple devices, of varying effectiveness and popularity, include starch pens, magnifying glasses, and ultraviolet penlights. Given the increasing incidence of human, device-assisted authentication abroad and in the United States, an evaluation of potential new features must include their authentication by simple devices and machines as well as by unassisted humans. Table 4-2 summarizes the leading authentication concepts by type of cash handler—that is, by currency user.
Evaluation Scheme
New feature concepts can span a wide range of technological readiness, from ultralow technology to highly innovative possibilities. Of the many potential feature concepts that emerged from the committee’s brainstorming during the course of the study, a subset was ranked for presentation in the report by the feature-assessment process described below. The features evaluated were subsequently
TABLE 4-1 Summary of the Committee’s Analysis of the Feature Requirements for the Deterrence of Counterfeiting, by Class of Counterfeiter
|
Class of Counterfeiter |
Technology Used in Counterfeiting |
Deterrence Concepts |
|
Opportunist |
Commercial home/office digital image technology |
Move beyond the reflected image: transmitted light, active features, new materials and devices |
|
Petty criminal |
Commercial digital technology, special materials and processes |
Require expertise: features that challenge digital reproduction, active features, non-print-based features, novel substrate |
|
Professional criminal |
Printing technology, special materials and processes |
Raise the stakes: features that require substantial investment to reproduce |
|
State-sponsored |
Advanced and capital-intensive technology, forensic features |
Use irreversible engineering: proprietary technologies, forensic features that cannot be reverse-engineered |
TABLE 4-2 Summary of the Committee’s Analysis of Feature Requirements for the Authentication of Currency, by Type of Cash Handler
|
Cash Handler |
Authentication Concepts |
|
General public, unassisted |
Ambient examination: visual, tactile, or audible feature that is obvious in various environments. Careful inspection is culturally acceptable. |
|
General public, assisted |
The basic device (a “gadget”): obvious signal from a device that is cheap, portable, and easy to obtain—preferably a multiuse item such as a penlight or cellular telephone. |
|
Point-of-sale cashier, unassisted |
Low-profile examination: visual, tactile, or audible feature that is obvious in a quick and inconspicuous examination. The appearance of suspicion is not culturally acceptable. |
|
Point-of-sale cashier, assisted |
The dedicated device: obvious signal from an inexpensive, single-use device. The acceptable device may vary among retailers, from cheap (starch pen) to moderate (electronic note authenticator). |
|
Bank teller, unassisted |
Education and experience: visual, tactile, or audible feature that is obvious to the educated and experienced user. Distinctive “look and feel” is important. Careful inspection is acceptable, but lengthy inspection is time-prohibitive. |
|
Bank teller, assisted |
Authenticating device: a dedicated authenticator of moderate to expensive cost. Device must not deface note (that is, no starch pen). |
|
Blind person, unassisted |
Beyond the visual: tactile or audible feature with a strong signal. |
|
Blind person, assisted |
Portable and reliable device: audible or tactile signal from an inexpensive, portable, dedicated device. |
|
Retail machine reader |
Short end first: strong signal from a point sensor in short-end-first feed direction. Handling speed is not critical. |
|
Commercial bank machine reader |
Wide end first: strong signal from a point sensor in wide-end-first feed direction, independent of orientation or face. Handling speed is critical. |
|
Central bank machine reader |
Beyond authentication: features that provide added information as notes recirculate through the Federal Reserve Banks. |
|
Law enforcement, forensic |
Unique and traceable: features that present counterfeiters with many different options regarding simulation or reproduction. These duplicated features can be examined with laboratory equipment to provide a unique “fingerprint” to a particular counterfeiter’s work, allowing classification of counterfeiters and traceability of methods and materials. |
grouped into intermediate term (less than a 7-year development time anticipated before incorporation into a banknote) and long term (longer than a 7-year development time). The long-term features are described in Chapter 5.
In developing an assessment system, the committee turned to the flow model described in Chapter 2 and recognized that the two most important parameters for assessing the effectiveness of a feature are these: (1) how well the feature deters simulation (decreases ρ) for each class of counterfeiter, and (2) how well it aids in currency authentication (decreases s)—for each class of human cash handler,
including the blind, with and without a simple device; for machine readers; and for law enforcement.
Armed with this insight, the committee developed an evaluation matrix that scored the efficacy of each feature for its deterrence and authentication value, by counterfeiter and user, respectively (see Table 4-3). Deterrence value is evaluated for four counterfeiter classes: the opportunist, petty criminal, professional criminal, and state-sponsored counterfeiter. The impact of the primitive counterfeiter is low enough that deterrence is not important for that class.
Validation efficacy is scored for 12 user classes. The general public, cashiers, and tellers are called on to verify currency in ambient conditions, without assistance; thus, unassisted authentication remains important. In addition, these user classes are increasingly employing simple devices to authenticate banknotes in cash transactions. As requested of the committee, the user classes also include the blind (unassisted and assisted by a simple device), machine readers (including automated cashier machines and commercial-and central-bank authenticators), and law enforcement.
When the committee attempted to assign numerical scores to various feature attributes and derive an additive overall score for each feature, it found this scheme inadequate for two important reasons. First, because every selected feature was
TABLE 4-3 Demonstration of the Committee’s Evaluation Process for Proposed Innovative Features for Banknotes
good at something and none was good at everything, the combined score was nearly the same for every feature despite various weighting schemes; consequently, there was little differentiation among features. Second, the flow model outlined in Chapter 2 shows that additive scores are not necessarily relevant to a feature’s effectiveness at decreasing the amount of counterfeit currency in circulation. As a result, ranking the features by a numerical score was not a useful exercise. So instead, to score the efficacy values of proposed features, the committee assigned the following symbols: “■” indicates features excellent in deterring simulation, “![]() ” indicates features good in deterring simulation, “
” indicates features good in deterring simulation, “![]() ” indicates features that would be easy to validate, and “s” indicates features that would be somewhat easy to validate. “Blank” in the matrix indicates that the committee saw the feature as having no value for deterring counterfeiting by the class in question or no value for validation by the user in question.
” indicates features that would be easy to validate, and “s” indicates features that would be somewhat easy to validate. “Blank” in the matrix indicates that the committee saw the feature as having no value for deterring counterfeiting by the class in question or no value for validation by the user in question.
Demonstration of the Evaluation Scheme
Table 4-3 shows an evaluation for two fictional proposed features. Features 1 and 2 are both “excellent” for deterring counterfeiting by opportunist and petty criminal counterfeiters, and Feature 1 is also somewhat effective (“good”) for deterring the professional counterfeiter. Table 4-3 shows that Feature 1 is “easy to validate”—that is, very effective for currency-authentication purposes—for seven classes of user. In the case of the general public assisted by a simple device, the device in question would be something like a generic light-emitting diode (LED) penlight or some other sort of simple, filtered, single-wavelength (color) light source. Feature 1 is also “somewhat effective” for blind users—assuming that a device is available to the blind user that would provide an audible or vibratory response to some feature characteristic or the intrinsic tactile nature of the feature would be of use to the blind user unassisted. Feature 2, while effective for fewer users, may be a better choice, as it provides deterrence value to the opportunist and petty criminal counterfeiter while providing unassisted authentication value to the general public, the cashier, and the bank teller—that is, the first line of defense against the passing of counterfeits.
As mentioned above, the committee devised the evaluation scheme to assist in choosing which feature ideas to develop further. For a feature to remain in consideration, it was required to provide excellent deterrence against simulation by at least one type of counterfeiter and to provide excellent authentication assistance by being easy to validate by at least one type of cash handler. Features that did not meet this criterion were eliminated from further consideration. Features were ranked in the matrix exemplified in Table 4-3 on a continuing basis, and as feature ideas evolved, some features dropped off the list and some new features were added. The evaluation scheme, therefore, became a valuable tool for the
committee’s idea-generation process, as it allows ready identification of features that excel in each category. Furthermore, when used for a variety or combination of features, the evaluation process provides a rationale for selecting features that will offer a broad spectrum of deterrence. While this system does not provide a numerical ranking of any particular feature against another feature, the flow model for counterfeiting discussed in Chapter 2, properly extended and validated, would provide a foundation for a quantitative assessment and comparison of features for a new banknote design.
SUMMARY DESCRIPTION OF NOVEL IMAGE FEATURES
The features summarized in the sections that follow emerged from the committee’s generation of ideas and the assessment process described here. A short description of each feature and of the rationale for why it scored high in the evaluation process is supplemented by further details contained in Appendix C, entitled “Intermediate-Term Feature Descriptions.” The structure of the appendix is outlined in Box 4-1. The information in Appendix C relating to development risks and issues and to the feature development plan is used as the basis for the discussion in Chapter 6, “A Path Forward.”
Looking ahead at this chapter, the results of the committee’s evaluation of the deterrence capabilities of the individual features are summarized in Tables 4-4, 4-5, and 4-6. The results of the evaluation on production, discussed in detail in Appendix C for each feature and including a cost assessment, are summarized in Table 4-7. Table 4-8 evaluates the feature concepts against the emerging digital counterfeit technologies that were discussed in Chapter 3. Box 4-2 groups the features by manufacturing technology (printed, substrate, composite additions); Box 4-3 groups the features by primary application (general public unassisted, blind users unassisted, general public assisted with simple device, and machine readers or dedicated device); and Box 4-4 groups features by expected implementation schedule in the near term, within 3 to 4 years, and in the intermediate term, in less than 7 years. The information in Appendix C was used as the basis for the evaluations and descriptions contained in the tables and the boxes.
Overall, these features have considerable potential to deter opportunist and petty criminal counterfeiters. Some features will also have deterrence value for those professional criminal counterfeiters who do not have the resources to adopt the next level of technology. State-sponsored counterfeiters, however, will likely not be deterred by these features because this class of counterfeiter has ready access to technology, including advanced printing and manufacturing processes. Chapter 5 describes disruptive technologies that might be implemented in the longer term—these are currency features that would pose daunting challenges to counterfeiters who rely on conventional manufacturing technology.
|
BOX 4-1 The Structure of Appendix C, “Intermediate-Term Feature Descriptions” In-depth descriptions of the innovative banknote features that could be implemented in a time frame of fewer than 7 years are presented in Appendix C of this report and may be referenced for important feature details. Each feature description in Appendix C, “Intermediate-Term Feature Descriptions,” includes subheadings dealing with various aspects of the feature:
|
The features summarized in this chapter are grouped below in three manufacturing categories:1 printed features, modified substrate features, and features employing composite additions to the existing substrate. In the first category,
|
1 |
Note that in Appendix C, the features are presented in alphabetical order. |
printed features (Table 4-4) are created using conventional printing processes and are intended to be viewed in reflected and/or transmitted light. In the second category, modified substrate features (Table 4-5) alter the existing cotton-linen substrate or replace it altogether. The third category, composite additions to the substrate (Table 4-6), includes the addition of plastic devices having unique optical and/or tactile properties. These categories were selected because the committee thinks that future anticounterfeiting trends will move away from printed features toward
TABLE 4-4 Committee’s Evaluation of Innovative Printed Features for Banknotes
TABLE 4-5 Committee’s Evaluation of Innovative Modified Substrate Features for Banknotes
more manipulation of the three-dimensional substrate and the incorporation of composite materials.
The features described in this chapter are expected to be used differently by different cash handlers, including the general public, the blind, cashiers, bank tellers, and machine readers. Some features are intended for unassisted use by cash handlers using direct human perception—that is, the feature is visible in ambient light or is tactilely identifiable. Some features are intended for “assisted use” by cash handlers, meaning that the feature’s counterfeit deterrence is enabled by the use of a device—that is, a widely available nonproprietary tool that operates on a feature to produce a human-perceptible signal. Examples of simple devices intended for use by the public include a penlight or a polarizing sheet. Cashiers may use dedicated
TABLE 4-6 Committee’s Evaluation of Innovative Features Based on Composite Additions to the Substrate
devices designed and sold for the sole purpose of banknote authentication but that are still inexpensive and easy to use; examples include electronic devices that read a portion of the banknote and indicate its authenticity and denomination. These electronic devices would also be of use by the blind. Features that are effective for automated retail purposes and for commercial banks would be expressly designed for machine readers. The committee made a preliminary assessment of which features would be readily detected by devices and sophisticated machine readers; as various features are further explored during a research and development program, a key task could further explore the best methods of assisted detection. Finally, features effective for forensics would provide law enforcement with additional capability for associating particular counterfeiting methods with certain counterfeiters.
Printed Features
Color Image Saturation
The color image saturation feature embeds information in the FRN by varying the intensity, or “saturation,” of colors in a printed image in a prescribed way. The printed variations in color intensity can be subtle, so as to prevent notice by the unaided eye. Digital scanners are unable to capture the variations of the feature because they quantize the recorded intensity. However, these genuine variations in color intensity can be readily detected by a dedicated optoelectronic device that can determine whether or not a banknote is authentic. Digital scanners may be used for the analysis of this feature. However, most digital scanners record red, green, and blue channels of information, and luminance is not a signal channel in most scanners, although the red, green, and blue data can be processed to produce a luminance signal using known colorimetric methods. Depending on the subtlety of the embedded luminance signal, 8-bit signals may or may not be sufficient.
Grazing-Incidence Optical Patterns
The grazing-incidence optical pattern feature uses deformations in the surface of a note to generate diffraction patterns that are clearly visible when illuminated and/or viewed at high angles of incidence; that is, the illuminating light is incident on the currency surface at angles greater than 80 degrees. The deformations required for this feature could be added by the intaglio process, exploiting the capability of the high-pressure intaglio presses. This process cannot be easily duplicated by the digital printing processes discussed in Chapter 3. This feature could be observed directly, or with the aid of a simple device such as a penlight.
High-Complexity Spatial Patterns
The high-complexity spatial patterns feature relies on a highly dense and specially designed printed pattern that exploits weaknesses in electronic printer capabilities that are not shared with the conventional analog printing methods currently used for currency production. Thus, for properly designed patterns, the commonly available electronic printers such as ink-jet and other printers will not be able to reproduce defect-free images. The counterfeit images would be readily apparent to the unaided eye.
A representative high-complexity spatial pattern is depicted in Figure 4-1. In this figure, the center of the pattern is indistinct because of the printing process used to create this report. On an authentic banknote, the radial lines would continue to the extreme center of the pattern, providing a much crisper image. The
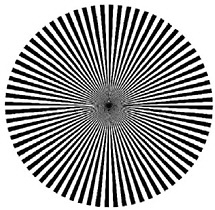
FIGURE 4-1 A starburst pattern is an example of the kind of high-complexity spatial pattern that electronic printers could not reproduce.
committee is not suggesting that this particular pattern be used. However, the gradually decreasing spacing, whether radial or lineal, in patterned images such as this will at some point cause the addressability limits of an electronic printer to place two lines together without a space, or two spaces together without a line, producing a clearly inferior image. With proper design and adequate intaglio printing quality, the analog system should be consistently able to frustrate a digital system’s ability to duplicate the image.
Metameric Ink Patterns
Metamerism results when two colors appear to be the same when they are viewed using one wavelength (or color) of light, but appear to be different when viewed under another wavelength. In commercial printing, in which special inks are often used, care is taken to avoid metameric effects. In this instance, printer specialists become frustrated when two nearby colors appear to be the same color under one light source—say a fluorescent lamp—and then appear as different colors under a conventional tungsten lamp. However, this printing “problem” can be exploited as a feature, possibly coupled as a further enhancement with nanocrystal inks, to generate patterns that can be observed under the special illumination conditions of two different light colors or with a simple filter. Furthermore, a sophisticated authentication test using a dedicated optoelectronic device can be easily developed to measure the reflectance spectrum or “fingerprint” of the metameric inks. Special filters coupled with controlled illuminants may also be used for readily
viewing the patterns in the metameric inks. By using special inks for the printing of features on banknotes, such as those enabled by nanocrystal technology (see the discussion below), counterfeiters would not be able to produce the same effect with good quality when using other “normal” inks. Miniature instrumentation could be readily built that would clearly discriminate between the “real” nanocrystal inks and the simulated attempts.
Nanocrystal Pigments
Dispersions of semiconductor or metallic nanocrystals have the potential to provide unique color and spectral characteristics in an ink format that could be used to form images on currency or, as embedded in a plastic matrix, to create colored features in a security strip. By synthesizing nanocrystals for specific ink formulations, complex color characteristics can be achieved with a degree of control and durability that would be difficult to duplicate using other approaches. These inks could also be used for novel metameric applications, as described above. This feature would require a dedicated optoelectronic device for measuring the color spectrum of the printed feature.
Nanoprint
Microprinting, currently printed on the FRN’s paper substrate, can be viewed with a very sharp eye or modest optical aids. Nanoprint involves printed text, images, or regular arrays of patterns with critical dimensions in the submicron range, formed on smooth surfaces of components of the currency, such as the security strip. Lithography research has produced several methods that can “print” structures and patterns with dimensions in the deep submicron and nanometer regime. Nanoprint rated highly in the committee’s evaluation process because it provides the combination of an extremely high level of security with the potential for low cost. Nanoprint can be viewed directly using a very high magnification electron microscope, but these are only available in specialized laboratories. For use by cash handlers, nanoprinted features would be designed to generate diffraction, moiré, or other patterns. These features would be observed indirectly by exploiting visible and/or machine-readable collective effects such as diffractive or moiré effects.
See-Through Registration
The see-through registration feature involves placing on one side of the currency substrate a printed image that works in tandem with an additional element printed on the opposite side of the currency. When the two images are well aligned and the note is held up to the light, the complete (fully aligned) feature is visible
through the substrate. The two images on either side of the note can also combine to create a transmitted color different than either of the printed images’ colors. This feature is robust and is easily visible. It is currently used in several types of currency, and appears to be effective. It can be implemented in the near term. In the longer term, advances in reprographic technology may make this feature easier to duplicate.
Thermoresponsive Optically Variable Devices
Thermoresponsive optically variable devices use printed inks or other materials that change in appearance with temperature. For example, the inks used to print such a feature might appear blue when cool and red when hot. Figure 4-2 illustrates the response of such a thermally sensitive material to heat from the human hand. This effect is reversible, meaning that after becoming hot and hence red, the color of the feature can return to being blue when cool. A counterfeiter would have to obtain and color-match the appropriate liquid-crystal ink to replicate this feature.
Modified Substrate Features
Fiber-Infused Substrate
The fiber-infused substrate feature embeds small-diameter optical-fiber segments, such as optical plastic, in the currency substrate. These fibers scatter light in a unique way, providing a kind of fingerprint for the currency substrate that is difficult to reproduce. The effect could be detected in transmitted light or induced
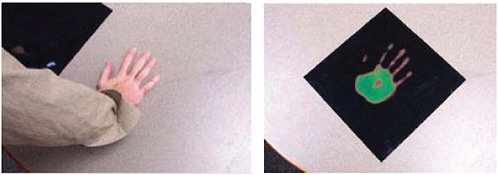
FIGURE 4-2 Images showing the thermal response of a cholesteric liquid crystal. At room temperature, the device is black (upper left in the left frame). Heating by a hand causes changes in the observed color (right frame). SOURCE: Adapted from the University of Wisconsin-Madison IPSE Liquid Crystal Activity Guide; <http://mrsec.wisc.edu/Edetc/supplies/ActivityGuides/LC_Activity_Guide_Expo.pdf>.
using a small penlight. This feature would not be reproducible using electronic printing and scanning techniques. It can be considered an upgrade to the red and blue fibers currently used in U.S. banknotes. When viewed by an instrument that illuminates the fibers and collects the returned optical signal, the unique fiber-absorption characteristics and other optical signatures would be extremely difficult to replicate and hence would provide for excellent authentication.
Microperforated Substrate
The microperforated substrate feature employs very small holes punched into the currency substrate to form symbols or denomination indications that would be easily detected in transmitted light. A simple penlight could be used to make this feature more apparent. Specialized perforating machinery is required to make these small holes without tearing or otherwise damaging the currency substrate. Depending on the cost and performance requirements, the perforations might also be generated by short-pulse laser systems such as femtosecond lasers, which can produce very small holes in many materials ranging from steel to plastic, glass, and even diamonds. Furthermore, the high pulse rate of such laser systems could permit fast generation of the notes.
Plastic Substrate
Although plastic has been historically examined as a matrix for banknote production, it has only become a viable alternative medium during the past decade. In 1996, Australia became the first country to convert fully to polymer-based banknotes, after having experimented with synthetic polymers notes since 1988. One of the more frequently employed synthetic polymers used for these types of banknotes is biaxially oriented polypropylene.
Proponents of these relatively new banknote materials have pointed out performance benefits that include cleanliness, durability, processability, recyclability, security, and compatibility with existing printing equipment and inks. Other experts have indicated that plastic banknotes are more costly to produce. As of 2006, plastic substrates are used by a number of countries, including Bangladesh, Brazil, Brunei, Chile, China, Indonesia, Kuwait, Malaysia, Mexico, Nepal, New Zealand, Northern Ireland, Papua New Guinea, Romania, Singapore, Solomon Islands, Sri Lanka, Taiwan, Thailand, Vietnam, Western Samoa, and Zambia.
The largest drawback with the use of an alternate substrate in U.S. banknotes is that the plastic substrate would have a tactile feel much different than the traditional Federal Reserve note. If the committee heard one common theme from counterfeit security experts, it was that the distinctive tactile feel of U.S. banknotes is the foremost feature used by most people to judge the authenticity of U.S. cur-
rency. This is true according to anecdotal stories (for example, the first person to detect a $100 supernote was a cash handler who thought the bill “didn’t feel right”), focus-group studies, and controlled scientific studies.2 The committee believes that the best security features are those that are easiest to detect. Therefore, there must be an indisputably compelling reason to make a change in the tactile feel of the substrate that arguably is the easiest and most recognized FRN feature. Also, a significant public education program would be necessary to introduce such a change, and during the interim period before the alternate substrate became widely known and accepted, it is feared that counterfeiting would flourish owing to confusion about the genuine substrate. Unlike many other countries, the United States never recalls old banknotes, so confusion regarding the substrate could persist for some time. Given that the committee was unable to construct a compelling case for the counterfeit-deterrence value of a wholesale change to an alternate substrate, the plastic substrate is not included on the list of candidate technologies.
However, the committee considered another possibility that would involve a partial change. The plastic substrate could be used for low-denomination notes. This would provide a significantly different tactile feel for use in denominating by the blind, and it would complicate the practice of bleaching low-denomination notes to produce a quality substrate for higher-denomination counterfeits. The improved durability of the plastic substrate would also provide a cost benefit, since low-denomination banknotes suffer the most user wear and have shorter lifetimes in the marketplace owing to higher usage rates in cash transactions.
It has been reported that the lifetime of plastic banknotes can be as great as four times that of paper.3 The life span of U.S. currency was examined in a comprehensive 2002 Federal Reserve Board (FRB) study that addressed the applicability of alternative substrates.4 The report highlighted the fact that the life of the $1 note was more than 20 months in 2001, which is a longer duration than the life span of comparable denominations in several other countries for which the data are available. These data indicate that a plastic substrate would provide about a twofold lifetime increase for U.S. currency. The conversion of the paper $1 notes to a plastic substrate would require a large investment to accommodate, estimated
|
2 |
H. Treinen. 2004. Banknote recognition: Public reception of double sided intaglio printed banknotes compared with single sided intaglio and offset counterfeited banknotes. Currency Conference, Rome, 2004. Personal communication. |
|
3 |
For additional information, see the paper by L. Coventry, 2001, Polymer notes and the meaning of life, presented at 2001 Reserve Bank of Australia, Currency Conference, Barcelona, Spain, April 2001. Available at <http://www.rba.gov.au/CurrencyNotes/ConferencePapers/cu_coventry_0401.pdf>. Accessed February 2007. |
|
4 |
Michael Lambert, Marsha Reidhill, Genie Foster, and Doug Rodriguez. 2002. Lifespan of U.S. currency and analysis of an alternate substrate, unpublished paper presented at the 2002 Currency Conference and 2002 CEMLA Conference. |
by the authors of the FRB report to be on the order of $100 million. The results of a Monte Carlo simulation of plastic substituted for the paper substrate indicated that the lifetime of the plastic substrate would have to be greater than 36 months for the replacement to be cost-effective. The available lifetime data for a plastic substrate is approximately at this level.
Future reassessment of the cost-effectiveness of a plastic substrate could be done after additional lifetime data become available. Any future study that evaluates the replacement of low-denomination paper-based banknotes (that is, the $1, $2, and $5 FRN) with plastic should also assess the counterfeiting-protection benefit acquired from converting to plastic, including the public confusion in handling two substrates that “feel” different.
If the conversion to a plastic substrate is eventually made for low-denomination notes, that experience will provide useful information for the further assessment of converting all FRNs to the alternate substrate at some later time.
In this chapter, the committee identifies some features that would be added to the current substrate to produce a hybrid substrate, such as the Fresnel lens and window. And Chapter 5 discusses the anomalous currency space that would serve as a localized region within the current paper substrate for inserting plastic, substrate-based features that would be selected on the basis of providing maximum counterfeiting deterrence. This approach would locally change the tactile feel of the banknote.
Tactile Variant Substrate
Tactile variance features create changes in the local “feel” of a banknote across the surface of the currency. This variance can be introduced in a number of ways, such as by incorporating a variety of security threads with different embossing and/or at different locations on different denominations. This feature would deter the bleaching of FRNs in order to use the substrate to make other banknotes of higher denominations. Providing a tactile feel that varies by denomination provides a means for the visually impaired to denominate U.S. banknotes.
Composite Additions to the Substrate
Fresnel Lens for Microprinting Self-Authentication
The Fresnel lens for microprinting self-authentication feature provides an on-the-banknote optical aid for reading the fine features printed on the substrate. The lens would be an authenticating feature used by bending the note to inspect fine detail of microprinted features through it. The feature consists of a thin plastic lens that is incorporated into the substrate. The plastic lens could also impart a distinct
tactile feel to the note and thus serve as a tactile denominating feature for a blind person if the lens placement were denomination-specific. This feature would be difficult to simulate with high quality because of challenges presented by fabricating a sufficiently thin device and integrating it into the substrate.
Hybrid Diffractive Optically Variable Devices
Conventional diffractive optically variable devices, such as holograms, are in widespread use, as are nondiffractive components, such as optically variable inks. The proposed hybrid diffractive optically variable device combines diffractive and nondiffractive effects into one single device. For instance, polarization-dependent effects and encrypted images can be combined with holograms and interference structures to provide a visibly striking image in a single feature. Also, the optical phase and other information in the images produced by the devices can be encoded and retrieved using specialized equipment that is very difficult for even sophisticated replicas to replicate.
Refractive Microoptic Arrays
The refractive microoptic array feature class employs microoptic element arrays of tiny lenses that are integrated into the substrate to create obvious interactive visual effects. As the user moves or tilts the currency, the image being observed changes. The visual effect is striking and easily seen. This feature has a tactile component that might help the blind authenticate an FRN without device assistance. Even professional counterfeiters would have significant difficulty reproducing the optical effects because of challenges presented by fabricating a sufficiently thin device and integrating it into the substrate. For example, a hot-stamped holographic strip might yield an optically variable feature, but it would lack the physical integration of the optical material with the substrate.
Subwavelength Optical Elements
A wide range of optical characteristics can be obtained from a single material by structuring it on length scales shorter than the wavelength of light—that is, substantially less than a few hundred nanometers. For example, parallel arrays of thick, subwavelength metal lines on a transparent substrate are completely transparent to light polarized along the length but are highly opaque to light with the orthogonal polarization. Figure 4-3 shows one example. Features based on subwavelength optical elements could provide visible images that produce distinctive colors, polarization contrast, and other optical effects. They can be used to provide a high level of control over the appearance of an image. While some of the effects
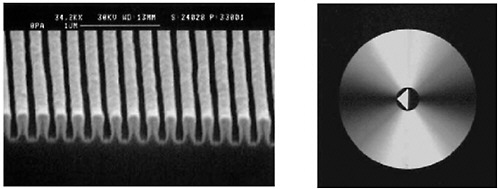
FIGURE 4-3 Scanning electron micrograph (left) of a subwavelength optical device, which in this case consists of an array of metal lines. This structure forms a polarizer, whose implementation as a circular polarizing element is illustrated on the right. SOURCE: Reprinted, by permission, from B. Schnabel, E.-B. Kley, and F. Wyrowski, 1999, Study on polarizing visible light by subwavelength-period metal-stripe gratings, Optical Engineering 38(2): 220-226.
would be visual in unaided examination, the effects would be more dramatic when examined using a polarizing film.
Window
Windows can be integrated into the substrate using a different shape and location for each denomination. For example, if the windows were progressively smaller with each denomination, they would complicate the bleaching of low-denomination notes for use in high-denomination counterfeits. Different denominations could also have different window shapes and positions. Their tactile properties also could be used by the blind for determining denominations. Note that substrate integration technology similar to that required to implement windows is also needed for the Fresnel lens, the hybrid diffractive, the microoptic array, and the subwavelength optical element features. It is envisioned that in the future a window could also be used as a platform for a wide variety of sophisticated features, as described in the section entitled “Anomalous Currency Space” in Chapter 5 and Appendix D.
ASSESSMENT OF FEATURE PRODUCTION COST
The committee made a preliminary estimate of each innovative feature’s manufacturing cost on the basis of a preliminary understanding of the feature technology and limited knowledge of the Bureau of Engraving and Printing’s (BEP’s) produc-
tion capability. Table 4-7 summarizes the committee’s production cost assessments, described in Appendix C.
The committee’s cost assessment does not explicitly take into account the new equipment that feature suppliers would have to acquire, nor that of the substrate supplier for those features that would be integrated within the substrate. It is assumed that these costs would be built into the feature cost and thus are captured as the incremental cost of producing the new feature, compared with the cost of
TABLE 4-7 Production Cost Assessments of Innovative Features for Banknotes
|
Innovative Feature Concepta |
Requires Additional Bureau of Engraving and Printing (BEP) Operational Stepsb |
Incremental Cost Relative to the Security Threadc |
Requires New Capital Equipment at BEPd |
|
Color image saturation |
|
o |
|
|
Fiber-infused substrate |
|
+ |
? |
|
Frensel lens for microprinting self-authentication |
|
+ |
|
|
Grazing-incidence optical patterns |
? |
o |
? |
|
High-complexity spatial patterns |
|
o |
|
|
Hybrid diffractive optically variable devices |
? |
+ |
? |
|
Metameric ink patterns |
|
o |
|
|
Microperforated substrate |
● |
o |
● |
|
Nanocrystal pigments |
|
o |
|
|
Nanoprint |
|
+ |
|
|
Refractive microoptic arrays |
|
+ |
? |
|
See-through registration |
|
o |
|
|
Subwavelength optical elements |
|
+ |
|
|
Tactile variant substrate |
|
o |
|
|
Thermoresponsive optically variable devices |
? |
+ |
● |
|
Window |
? |
o |
? |
|
aCan be implemented in less than 7 years. b“●,” step required; “?,” possible new step required, depending on implementation. c“o,” roughly equivalent to current costs; “+,” more costly. d“●,” new equipment required; “?,” possible new equipment required, depending on implementation. |
|||
producing the current security thread. The cost of developing devices for detecting machine-readable features also is not included in these estimates.
On the basis of this preliminary assessment, all of the intermediate-term features that the committee has described appear to be viable candidates for further consideration, with the possible exception of the plastic substrate for the $1 FRN owing to the Federal Reserve’s estimate of $100 million required for infrastructure changes.5 As discussed earlier in this chapter, the cost of implementing a plastic substrate may not be adequately offset by the added durability advantage and counterfeit-deterrence benefit provided by eliminating a counterfeiter’s option of bleaching and printing a larger-denomination banknote on the lower-denomination substrate.
PRIORITIZATION OF INNOVATIVE FEATURES
The features described in this chapter incorporate a wide range of potentially effective technologies. The committee’s intention is to suggest a number of feature ideas that, once developed, will provide the banknote designer with a portfolio of innovative counterfeiter-deterrent features. Since not every feature idea will be developed, the prioritization of features for entry into a development program would take many factors into account. Those factors would include, for example, the estimated deterrent effectiveness against the projected information technology capability, a balanced mix of printed image and substrate features, a high degree of recognizability by the different types of cash handlers using sensory perception or assisted by some type of equipment, and the expected development time line. These considerations, matched against the BEP’s internal assessment of critical security-feature needs and metrics, would highlight those features for top development priority. The features can be combined in different ways to provide a layered defense against the various classes of counterfeiter. Ultimately, then, the prioritization of the features would be accomplished by the banknote designers.
Effectiveness against evolving counterfeiting threats is a prime consideration when prioritizing potential features for development. Table 4-8 summarizes the committee’s evaluation of the deterrence value of the innovative security features with respect to various digital image technologies that could be used in counterfeiting. This analysis is based on the committee’s estimation of the difficulty in applying these advanced digital copying and reprographic technologies to simulate the proposed features. A comparison with Table 3-1, which evaluates the deterrence value of current FRN features against the current digital threat, indicates a
TABLE 4-8 Committee’s Evaluation of Innovative Security Features in Deterring Digital Age Counterfeiting
|
Features |
Counterfeit-Deterrence Characteristic |
Advanced Digital Printer |
Advanced Color Copier |
Scanners and Digital Cameras |
Imaging Software |
Potential for Attack Through Internet Information Exchange |
|
Printed Features |
|
|
|
|
|
|
|
Color image saturation |
Digital signature embedded in currency |
● |
● |
● |
● |
× |
|
Grazing-incidence optical patterns |
Exploitation of three-dimensional nature of intaglio printing to emboss an optical feature |
● |
● |
|
|
× |
|
High-complexity spatial patterns |
Challenge to all digitally addressable printing |
● |
● |
● |
● |
|
|
Metameric ink patterns |
Specialized printing dye mixtures yield indistinguishable visual color, yet easily differentiated with simple instrumentation |
● |
● |
● |
● |
× |
|
Nanocrystal pigments |
Nanocrystals and dyes with brightness andunique colors and fluorescence |
● |
● |
● |
● |
× |
|
Nanoprint |
Print smaller than any commercial printing methods |
● |
● |
● |
● |
|
|
See-through registration |
Taking advantage of dual-side printing at BEP |
● |
● |
● |
|
× |
|
Thermoresponsive optically variable devices |
Colors that change with temperature |
● |
● |
● |
|
× |
|
Modified Substrate Features |
|
|
|
|
|
|
|
Fiber-infused substrate |
Transmitted effect |
● |
● |
● |
|
|
|
Microperforated substrate |
Transmitted effect |
● |
● |
● |
● |
|
|
Tactile variant substrate |
Patterned change in the feel of the surface |
● |
● |
● |
● |
|
marked improvement in effectiveness for all of the innovative features, with the caveat that these new features must be further developed to fulfill the expectation. The resistance of the features to duplication would be measured during the development program. Table 4-8 also indicates which features may be vulnerable to information exchange via the Internet—in this case, the threat would consist of information sharing of details helpful to counterfeiters, such as a “how to” guide on simulating a feature, specific sources through which critical materials are available, a graphical representation of a feature or portion of a banknote that can be downloaded, and so on.
Box 4-2 groups the features by manufacturing technology as printed, substrate, and substrate composite additions features. Five features incorporate the use of additional materials onto the banknote to produce a composite structure. The committee forecasts that the improvements in digital printing technology will require less reliance on printed images for counterfeit deterrence and more reliance on composite features embedded in the substrate. These composite features would
|
BOX 4-2 Groupings of Innovative Banknote Security Features by Manufacturing Technology
|
employ special materials and advanced manufacturing processes in order to deter counterfeiters effectively.
Box 4-3 groups the features by application, according to the class of cash handler that the feature is targeting. Readily identifiable features relying entirely on sensory perception are highly desired and were a significant focus of the commit-
BOX 4-3 Groupings of Innovative Banknote Security Features by Application
NOTE: Some features have multiple applications. |
tee. However, as counterfeiting technology continues to improve, the committee foresees an increased interest by cash handlers in using simple devices to aid in the authentication of banknotes. This trend could also capture the interest of the public, so that simple, readily accessible devices could be commonly used to validate a banknote. The grouping includes the following, among other features:
-
General public, unassisted: Fresnel lens for microprinting self-authentication embedded in the paper substrate, high-complexity spatial patterns, refractive microoptic arrays, microperforated substrate, see-through registration feature, tactile variant substrate, and thermoresponsive optically variable devices.
-
General public, assisted with simple device: Fiber-infused substrate, grazing-incidence optical patterns, metameric ink patterns, nanocrystal pigments, nanoprint, and subwavelength optical elements.
-
Blind users unassisted (features that provide tactile information to aid in denomination): Fresnel lens for microprinting self-authentication embedded in the paper substrate, refractive microoptic arrays, tactile variant substrate, and window.
-
Machine readers or dedicated devices: Metameric ink patterns and color-image saturation.
Box 4-4 lists those features that the committee estimates can be ready for implementation in the near term, within 3 to 4 years, and those that could require an intermediate term, up to 7 years of development. Of the features described in this chapter that are image-based printed features employing conventional inks, the committee considers that three could likely be implementable in the near term:
-
Grazing-incidence optical patterns,
-
High-complexity spatial patterns, and
-
A see-through registration feature.
Four features are printed using specialty inks; one of those could be implemented in the near term:
-
Metameric ink patterns.
Three features modify the substrate itself; one of those could be fully developed in the near term:
-
The microperforated substrate.
|
BOX 4-4 Groupings of Innovative Banknote Security Features by Expected Implementation Schedule
|
With the exception of the all-plastic substrate, it is assumed that for the features described in this chapter the substrate will continue to be the current cotton-linen blend for U.S. banknotes. The committee believes that the legacy substrate contributes substantially to current authentication—“feel” is the foremost feature used by most people to judge the authenticity of U.S. currency, and controlled access to this substrate is an effective deterrent to opportunist counterfeiters.6 Although the current paper substrate is distinctive, durable, and effective for authentication, chemical bleaching and/or the de-inking of lower-denomination genuine notes provides the counterfeiter an excellent substrate with which to manufacture higher-denomination notes. Several new features could directly address this threat: those with a composite addition to the substrate, such as a window, and low-denomination plastic notes. The key to the value of the composite additions is that
the feature must be progressively different on increasing denominations. Similarly, low-denomination notes made from plastic could not be recycled as $20 or $50 notes, since the plastic substrate has a markedly different look and feel from the cotton-linen substrate. However, changing the substrate material may not provide an overall increase in counterfeit deterrence, as discussed earlier.
CONCLUSIONS
-
A feature’s deterrence value varies with the class of counterfeiter. A feature’s authentication requirements differ with the type of cash handler.
-
An additive numerical model for feature evaluation is not optimal, as it lacks the ability to distinguish feature strengths adequately and cannot be extended to estimate the resulting reduction of counterfeit currency in circulation.
-
A nonlinear evaluation method—such as one based on a model that incorporates consideration of excellence in (1) deterring particular classes of counterfeiters and (2) aiding authentication for specific types of users—can provide a useful tool for prioritizing features.
-
The optimal set of features included on a banknote would address all counterfeiter and user classes.
-
Seventeen features for U.S. banknote applications were identified by the committee as deterrents to anticipated counterfeiting threats. Five of these features (metameric ink patterns, see-through registration features, microperforated substrates, plastic substrates, and windows) have been employed already in currency applications in other countries and thus could be implemented more quickly than the other novel features. Each new feature has the potential to serve as an excellent deterrent for at least one class of counterfeiter, although none is expected to deter state-sponsored counterfeiters completely.
-
Some of the proposed features are readily human-perceptible, while others require the use of readily available devices. In the future, the committee foresees that the use of devices will be common.
-
In general, the committee concludes that the trend is away from reliance on the two-dimensional image, a trend that the Bureau of Engraving and Printing has already begun with the use of a security thread, watermarks, and optically variable ink.
-
The committee suggests the need for an increased use of composite additions to the substrate to thwart the threats posed by advanced reproduction devices.




























