1
Introduction
The U.S. air transportation system is an attractive target for terrorists because of the potential that attacks on it will cause immediate harm and anxiety to large numbers of people, as well as cause massive economic disruption to the United States and the world. The system is vulnerable owing to its mission to provide service to people with a minimum of intrusion on privacy and with minimal disruption of access. The detection and mitigation of attacks on air transportation are made more difficult by the transient nature of the passengers’ movement through airports and the fact that it is common for passengers to be carrying several bags, making it relatively easy to conceal threat mater-
ials. The use of commercial airliners as weapons in the September 11, 2001, attacks on the Pentagon and the World Trade Center has also broadened concepts of what constitutes a threat to U.S. assets in general and to the air transportation system in particular.
Based on terrorist attacks to date involving the hijacking and bombing of aircraft, current threat-detection measures concentrate on detecting weapons or explosives. In the future, such attacks could also involve the use of toxic chemicals, chemical and biological warfare agents, or even radiological and nuclear materials.1
The government agency charged with responsibility for the implementation of technology for countering such threats is the Transportation Security Administration (TSA). The TSA, and the Federal Aviation Administration before it, have invested extensively in the development and deployment of technological and procedural systems designed to protect the traveling public. In support of this mission, the TSA has tasked the National Research Council (NRC) with assessing a variety of technological opportunities for protecting the U.S. transportation system, with a focus on the air transportation system.
STATEMENT OF TASK
In order to perform the assessment requested by the TSA, the NRC created the Committee on Assessment of Security Technologies for Transportation, under the National Materials Advisory Board. The committee’s statement of task is as follows:
This study will explore opportunities for technology to address national needs for transportation security. While the primary role of the committee is to respond to the government’s request for assessments in particular applications, the committee may offer advice on specific matters as required. The committee will: (1) identify potential applications for technology in transportation security with a focus on likely threats; (2) evaluate technology approaches to threat detection, effect mitigation, and consequence management; and (3) assess the need for research, development, and deployment to enable implementation of new security technologies. These tasks will be done in the context of current, near-term, and long-term requirements.
The committee will perform the following specific tasks:
-
Identify potential applications for technology in transportation security with a focus on likely threats derived from threat analyses that drive security system requirements. Review security system developments structured to meet the changing threat environment. Assess government and commercial industry plans designed to address these threats.
-
Evaluate technology approaches to threat detection, effect mitigation, and consequence management. Delineate the benefits of the insertion of new technologies into existing security systems. Evaluate the trade-offs
|
1 |
The President’s Homeland Security Department Proposal, available at http://www.whitehouse.gov/deptofhomeland/bill/index.html, accessed April 22, 2007; National Research Council. 2002. Making the Nation Safer: The Role of Science and Technology in Countering Terrorism, National Academy Press, Washington, D.C. |
-
between effectiveness and cost, including the cost of changing the security system architectures.
-
Assess the need for research, development, and deployment to enable implementation of new security technologies. Review and assess the potential benefit of existing and advanced detection technologies, including scanning technologies, sensing technologies, and the use of computer modeling and databases. Review and assess emerging approaches to effect mitigation and consequence management.
COMMITTEE APPROACH
An overarching goal of this committee has been to provide timely reports that meet the TSA’s priorities for defeating terrorist threats. The committee judged that this could best be done by issuing a series of short reports on chosen technology applications. In consultation with the TSA, the committee selected four topics for study and produced four reports (all published by the National Academies Press, Washington, D.C.), of which this report is the fourth:
-
Opportunities to Improve Airport Passenger Screening with Mass Spectrometry (2004),
-
Defending the U.S. Air Transportation System Against Chemical and Biological Threats (2006),
-
Assessment of Millimeter-Wave and Terahertz Technology for Detection and Identification of Concealed Explosives and Weapons (2007), and
-
Fusion of Security System Data to Improve Airport Security (2007).
Taken together, the four reports will satisfy the first part of the statement of task—an identification of applications for technology in transportation security. Independently, each report addresses a particular technology focus and identifies additional research needs.
By mutual agreement between the committee and the sponsor, the broad focus on “transportation security” in the statement of task was narrowed to the “threat of attacks on the air transportation system.” While the defensive measures and technologies discussed here may not have application to all transportation modes (e.g., containerized ships, bridges, highway tunnels, subways, and others), the committee believes that the air transportation security arena provides a relatively well controlled testbed for gaining experience with defensive strategies that could be adapted to other, more-complex, less-controlled transportation spaces—for example, bus terminals, train stations, cruise ships, and cargo terminals—with appropriate modifications.
BACKGROUND
The security of the U.S. commercial aviation system has been a concern since the 1970s when hijacking became a serious problem. A number of aviation security programs have been implemented. However, weaknesses continue to exist. These weaknesses were observed and exploited by terrorists on September 11, 2001, enabling them to hijack four commercial aircraft, with tragic results. Terrorists and persons of like mind can be expected to continue to examine the nation’s transportation security operations, both overtly and covertly, to find weaknesses to exploit.2
While all modes of transportation are security concerns, aviation security remains a priority. With hundreds of commercial airports, thousands of commercial aircraft, tens of thousands of daily flights, and millions of passengers using the system daily, providing security to the nation’s commercial aviation system is a daunting task. Figure 1-1 illustrates some of the threat vectors that may exist in the nation’s largest airports.
As can be seen in Figure 1-1, there are multiple points of vulnerability in and around an airport. Protection of each of these points generates a large body of data. Integrating the data collected in a manner that allows a better picture of potential threats could substantially strengthen airport security.
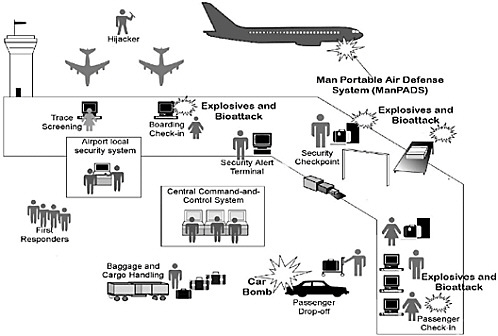
FIGURE 1-1 Generic airport diagram showing various airport spaces and some likely sites for attacks. Data fusion would allow for the coordination of input data from each of these potential threat vectors.
|
2 |
Al Qaeda Training Manual. Available at http://www.usdoj.gov/ag/trainingmanual.htm. Accessed April 22, 2007. |
On November 19, 2001, President George W. Bush signed into law the Aviation and Transportation Security Act (ATSA) (Public Law 107-71), which mandated the federalization of passenger and baggage screening at more than 438 commercial airports in the United States by November 19, 2002, and the screening of all checked baggage using explosive detection systems (EDSs). On March 1, 2003, the TSA was transferred from the Department of Transportation to the newly created Department of Homeland Security, as required by the Homeland Security Act of 2002 (Public Law 107-296).
Virtually all of the nation’s aviation security responsibilities are with the TSA. They include the conducting of passenger and baggage screening and the overseeing of security measures for airports, commercial aircraft, air cargo, and general aviation. These programs of the TSA are intended to form a layered system that maximizes the security of passengers, aircraft, and other elements of the aviation infrastructure.
The TSA has undertaken several programs to measure and improve the performance of checkpoint and checked-baggage operators in detecting threat objects. In July 2003, the TSA completed a study of the performance of its passenger and carry-on luggage-screening system, which identified numerous performance deficiencies, such as inadequate staffing, poor training of screeners, and poor supervision of operators. These deficiencies were the result of a lack of skills and knowledge, low motivation, an ineffective work environment, and wrong or missing incentives. The TSA is taking steps to remedy these deficiencies. Although it is making progress in its checked-baggage screening operations, it continues to face operational and funding challenges in screening all checked and carry-on baggage using EDSs, as mandated by the ATSA.3
SHORTCOMINGS OF EXISTING SYSTEMS
The United States has 438 airports that service commercial aviation and has deployed more than 1,100 bulk EDSs and 6,000 explosive trace detection systems manufactured by a number of different companies. The overarching requirements to deploy these systems universally and rapidly have understandably led to little coordination and interface compatibility among the different systems and the system manufacturers. As a result, the present situation is that detection systems operate largely as stand-alone systems, and only operator interaction enables coordination among these systems. Many of these multiple stand-alone detection systems operate with undesirably high false-alarm rates, slow throughput, and excessive demands on individual operators.
Deterring many likely attack scenarios will require the coordinated operation of the detection systems within the airports to prevent attempted attacks from succeeding. Consider, for example, a team of terrorists whose objective is to place an explosive device on an airplane. By separating out elements of the device, each member of the team may be able to get through security screening individually. Once through, they can assemble their device. An effective data fusion system might prevent this scenario by merging data from multiple systems to indicate an overall alert condition, thereby turning data into information.
|
3 |
Government Accountability Office. 2004. Aviation Security: Improvement Still Needed in Federal Aviation Security Efforts. GAO-04-592T. General Accounting Office, Washington, D.C., March 30. Available at http://www.gao.gov/cgi-bin/getrpt?GAO-04-592T. Accessed April 22, 2007. |
Data fusion also provides the most effective approach to reducing false alarms while simultaneously maintaining or improving the probability of detection. This improvement is possible because data fusion should enable the combination of different security system modalities to discriminate explosives from ordinary passenger items.
Data fusion is also essential for facility security. In the area of access control, data fusion is considered critical to the deployment of biometric systems. At the airport level, there is a major need to integrate and fuse data from multiple, facility-monitoring security systems. Without this fusion, the airports are vulnerable to a variety of attack vectors. For example, some airports have security systems in their heating, ventilation, and air conditioning systems to detect the presence of chemical or biological agents; however, these security systems are not linked to video, motion, or radar security systems to provide situational awareness in the presence of an attack. It is thus difficult for airport security personnel there to direct an effective response to such an attack.
SCOPE OF THE REPORT
The scope of this report was derived from the expressed needs of the TSA. During briefings to the committee, the Transportation Security Laboratory identified the following three reasons for pursuing data fusion and integration in transportation security: (1) to improve or maintain detection accuracy while decreasing false alarms, (2) to reduce the footprint at airports from new in-line systems, and (3) to reduce staffing requirements by automating information processes.
The current approach to most threat detection consists of multiple stand-alone detection systems, some with unacceptably high rates of false alarms and slow throughput. These individual systems also impose high demands on individual operators. Any integration or fusion of data takes place at the initiative of individual operators and security personnel. As is illustrated in Chapter 2, standardized data integration and automated fusion systems should remove the dependency of these systems on individual initiative and reduce the load on operators. Operators could then focus their efforts on resolving higher-probability alarms.
The current security technologies include x-ray radiography and computed tomography (CT), trace detectors, and metal detectors. Human observations are also made but are not formally incorporated into or used by any of these security methods. Further, all decisions by current security schemes are binary, and there is no method for the fusion of partial results that, taken together, would suggest a threat.
For example, a CT operator scanning a passenger’s bag may not signal an alarm but may be close to the alarm threshold; at the same time, a TSA security agent may notice suspicious behavior by the owner of the bag. There is currently no way to put these two partial pieces of evidence together to suggest the advisability of a more complete search. As another example, the x-ray radiography image of passenger X’s carry-on bags may indicate a threat, but the physical search reveals nothing in the carry-on bags; a checked bag belonging to passenger X may also alarm, but the fact that two alarms have been raised for the same traveler will not be known.
New technologies proposed for introduction at airports include biometrics, mass spectrometry, x-ray diffraction, x-ray backscatter, millimeter-wave (MMW) and terahertz
(THz) imaging,4 nuclear quadrapole resonance, and Secure Flight (a program to rapidly identify passengers who are unlikely to present a threat). In addition, the committee anticipates further improvements to existing technologies. However, at this point, little effort (other than biometrics) has been focused on integrating either existing or future technologies. At the time of this writing the committee is not aware of any attempts to develop standards for data integration of existing or new technologies.
For the nation to make progress in improving the security of all transportation systems, the TSA will need to make more effective use of its security systems and its security system data-processing mechanisms. This report focuses on exactly this area—how the TSA and airport security personnel can better utilize existing security systems (humans and machines contributing to the security information flow) through the fusion of data—and it provides the foundation for the more effective use of existing and future security systems that will enable significant improvements in the transportation security environment.
In order to provide the most timely and easily implemented recommendations to the TSA, the scope of this report is limited to near-term objectives and does not address a number of important ancillary questions. In particular, it does not address the integration and sharing of data above the airport level. That is, it does not address regional or national data integration or fusion among airports and among different security organizations. These important questions will require additional study. As any regional or national approach to integration or fusion will require the implementation of the recommendations in this report at the airport level, the approach recommended here is a necessary first step for later regional and national integration and fusion initiatives.
STRUCTURE OF THE REPORT
The committee met several times with the study’s sponsor, the TSA, and with input from the TSA, it developed the following objectives for this report:
-
Describe the air transportation data fusion problem from the elemental system level to the airport level,
-
Discuss current projects to address data fusion, and
-
Provide recommendations for improving security and data utilization through data fusion.
The report is structured to follow these objectives, with Chapter 2 serving as a foundation on issues related to data fusion in an airport security model and providing an overview of current projects in this realm (projects of the Department of Defense and private industry). Chapter 3 contains the majority of the committee’s scientific analysis, with a summary of the TSA data fusion projects. Recommendations for moving forward are presented in Chapter 4.








