1
The Electric Transmission and Distribution System as a Terrorist Target
Terrorists could destroy key elements of the electricity generation and delivery system, causing blackouts that are unprecedented in this country in duration and extent. The U.S. economy depends on a reliable supply of electricity, and widespread disruptions of long duration could cause enormous economic damage and suffering. Under some circumstances (e.g. a heat wave) such blackouts could also lead to significant loss of life. On the other hand, attacks on the U.S. power system would not immediately kill large numbers of people or cause massive destruction of familiar structures or facilities, and therefore probably would not be as dramatic as the September 11, 2001, attacks.
There is considerable debate over just how serious a threat terrorists pose to U.S. infrastructure such as the electric transmission and distribution system (NRC, 2002; Meade and Molander, 2006; Mueller, 2006). Electricity is ubiquitous, reliable, and taken for granted ... until the lights go out. Occasional large accidental outages caused by “cascading failures” in the high voltage transmission system (such as the Northeast blackout of August 2003) have briefly raised public concern about potential vulnerabilities, but to date such concerns have rapidly disappeared once power is restored. Power outages caused by damage to the distribution system, the lower voltage lines that carry power to customers, are far more common. Recent examples include the destruction after hurricanes in Florida and the Gulf Coast, as well as the July 2006 outage in New York City’s borough of Queens.
While the inconvenience and cost of these accidental disruptions of the nation’s transmission and distribution system have been large, they pale in comparison with the impacts that might result from a large, well planned, terrorist attack. Even if the probability of such an intentional attack were assessed to be quite low, the consequences are large enough that the nation needs to protect this essential service.
This chapter briefly reviews the electric power system and its vulnerabilities, identifies the types and motivations of potential attackers, explores the potential costs associated with the loss of power, and reviews a few of the actions that have been taken to date to reduce vulnerability.
THE ELECTRIC POWER SYSTEM AND ITS VULNERABILITY
Today in the United States, and in most of the rest of the industrialized world, power flows from large generating plants to customers through a complex, dynamic system whose structure is the result of gradual evolution over more than a century. Early power systems had small generating stations close to local distribution systems that fed power to streetlights and homes at relatively low voltage. As systems became larger and power had to be carried over longer distances, power lines were operated at ever higher voltage in order to minimize losses. Efficient high-voltage transmission lines also made it possible to locate ever larger generators in remote areas rather than close to towns and cities. By the middle of the 20th century, system operators began to connect individual high-voltage systems together so that power could be moved from region to region, both to promote economic efficiency and to increase reliability by making it possible to move power into regions suffering from temporary shortages.
Once electric power has been generated, the voltage is stepped up1 and power moves over long distances through the high-voltage transmission system, a complex network of lines, most of which are carried aboveground on tall towers. At key points throughout this system are substations that contain transformers to increase and decrease the voltage, switching gear that connects the system in desired configura-
_____________________
1The voltage of AC power can be easily increased or decreased using transformers. High voltage is used to move power long distances in order to minimize losses that result from the current heating the line. The power carried by a line is the product of the current and the voltage. However, for a given line, losses from heating go up as the square of the current. In moving a given amount of power, using a higher voltage reduces the current, and thus reduces the loss due to heating.
tions, and circuit breakers that open and close connections while also acting as giant fuses to protect expensive equipment from damage, as well as a variety of other devices. Most substations sit out in the open protected only by a simple chain-link fence. All but a few high voltage lines are also in the open. Thus, both substations and the lines that connect them are vulnerable to damage from storms and to terrorist attack.
When power reaches an area where it will be used, the voltage is reduced and power is distributed to customers over lower-voltage distribution lines. Unlike the transmission system, which is a large interconnected network, many distribution systems branch out radially to deliver power to customers, although some older, dense urban areas, such as New York City, use network configurations for distribution. All the elements of the transmission system, and increasingly those of the distribution system, are monitored and controlled by information and communication systems.
Although problems in any part of the system can disrupt the supply of electric power, this report focuses on the transmission and distribution (T&D) system, substations, and other associated parts, discussing generation only as it relates to issues involving transmission and distribution. Details on how the T&D system is controlled, operated, managed, and regulated are given in Chapter 2.
Non-malicious Threats to the Electricity Delivery System
By its very nature, the T&D system is not perfectly reliable. Even without terrorist activity, the power sometimes goes out, usually for just a few seconds, minutes, or hours, but sometimes for a few days. On very rare occasions, and in limited locations, outages may stretch on for weeks. As the duration and geographic extent of an outage increase, people become seriously inconvenienced, and economic and other costs rise, but people generally do not experience “terror.”
Keeping power flowing to customers is a continuous process of control, recovery, and repair. Most outages are local, brief in duration, and caused by problems at the level of the distribution system—such as lightning strikes, wind storms and tree falls, short circuits caused by wild animals such as squirrels, vehicles that crash into power poles, and similar events. Line crews can usually fix these outages in a matter of hours. Distribution systems that incorporate automation can often isolate a problem and restore service for many affected customers in a matter of seconds or minutes.
Outages caused by disruptions in the high-voltage transmission system are less common. When they do occur, because of faulty equipment, weather, or for other reasons, many such outages are never noticed by customers, because automatic controls and system operators can limit their impact and maintain the supply of power to the distribution system. But, of course, the transmission system does occasionally experience problems that result in loss of service to customers. Weather events, such as hurricanes and ice storms, earthquakes, and similar natural events, can bring down many transmission lines, and, less frequently, can damage transformers, circuit breakers, and other equipment such as the terminal facilities for direct-current (DC) lines. Inadequate attention to maintenance can also contribute to blackouts—as in the recent case of an improperly sized circuit breaker in London, or several instances of arcing to vegetation that have resulted from inadequate tree trimming in the United States.
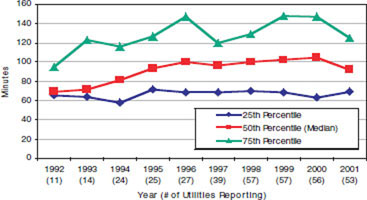
FIGURE 1.1a System Average Interruption Duration Index (SAIDI) indicators for U.S. utilities for the period 1992 to 2001 (excluding major events). SOURCE: EPRI (2003).
As explained in greater detail in Chapter 2, the transmission system is much more stressed, and thus more vulnerable, than it was a few decades ago, principally as a result of two factors: (1) years of underinvestment in system upgrades stemming from ambiguities and altered incentives that resulted from electric power restructuring and associated changes in the regulatory environment and (2) demands on the system to move power between sellers and buyers in new competitive power markets in greater volume and in ways in which the system was not designed to operate.2
Figures 1.1a and 1.1b show the trend in two common measures of power supply disruption in the United States over the decade from 1992 to—2001 the System Average Interruption Duration Index (SAIDI), which indicates the average time that customers are without power during the period analyzed (Figure 1.1a), and the System Average Interruption Frequency Index (SAIFI), which indicates the average number of interruptions per customer served per year (Figure 1.1b). Both reflect principally the effects of distribution system disturbances and exclude outages caused by major events. Figures 1.2a and 1.2b show SAIDI and SAIFI measures of reliability internationally. Reliability in the United States appears to be poorer, on average, than that experienced by customers for electric power in some other
_____________________
2Much of the transmission system was originally designed to serve the needs of vertically integrated regulated utilities. Following deregulation of the power industry and the introduction of competition among generators, the transmission system is now being expected to move power in ways that have resulted in patterns of power flow that did not exist previously under regulation.
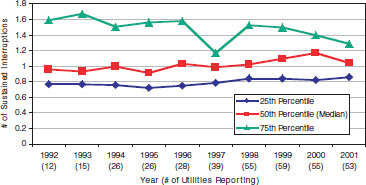
FIGURE 1.1b System Average Interruption Frequency Index (SAIFI) indicators for U.S. utilities for the period 1992 to 2001 (excluding major events). SOURCE: EPRI (2003).
developed countries, although much of this difference is due to major differences in population density and power system configurations.
As indicated in Figure 1.3, large outages in the United States between 1984 and 2000 were more frequent than might have been anticipated on the basis of a simple exponential distribution. Although in recent years in the United States there has been no significant change in the frequency of outages (Figure 1.4), there has been a very significant increase in the frequency of transmission loading relief events (Figure 1.5).3
Most problems occurring in the transmission of electric power can easily be corrected by automatic controls and actions taken by system operators. However, occasionally these actions are not sufficient to keep power flowing. Problems or failures originating in one part of the system may give rise to problems (such as overloads) in other parts of the system, which in turn cause additional problems that may ultimately result in a cascading power failure. The fact that the power system uses alternating current (AC) means that the system’s behavior is sometimes further complicated by oscillatory or other complex dynamic behavior, as illustrated in Figure 1.6. Although they are rare, such events sometimes cause a loss of power to many customers (Table 1.1 and Figure 1.3).
Potential Attacks on the Electric Power System
Because electricity is so essential to modern industrialized societies, the power system has frequently been identified as a potential terrorist target. For example, more than 15 years ago, in a report titled Physical Vulnerability of the Electric System to Natural Disasters and Sabotage (OTA, 1990. p. 14), the Office of Technology Assessment concluded:
Some terrorist groups hostile to the United States clearly have the capability of causing massive damage—the loss of so many generating or transmission facilities that major metropolitan areas or even multi-state regions suffer severe, long-term, power shortages. The absence of such attacks has as much to do with how terrorists view their opportunities as with their ability. U.S. electric power systems are only one target out of many ways of striking at America, and not necessarily the most attractive.
More recently, the National Research Council report Making the Nation Safer (NRC, 2002. p. 178) noted that:
[a]nalysis of possible targets, weapons, and delivery systems and of direct and indirect consequences reveals several very dangerous scenarios. The scenarios of greatest concern involve the electrical system. When service is lost, there are immediate consequences to every person, home, and business. An extended outage of electricity would have profound consequences.
The same report emphasized (p. 180):
[t]he impact of a prolonged interruption in the electric power supply to any region of the country would be much larger than the economic loss to the energy sector alone.… The nation’s electric power systems must clearly be made more resilient to terrorist attack.
Potential attackers, as shown in Figure 1.7, include the following.
Terrorists
Most problematic are terrorist groups with significant technical capabilities and resources who want to kill large numbers of people or cause widespread societal or economic damage. Although not very likely, as noted above, such terrorists might view the power system as a primary target. As discussed later in this chapter, a sophisticated attack could cause a lengthy blackout over an extensive region. An attack during a period of extreme weather, such as a heat wave, might lead to the deaths of many people, albeit in a far less spectacular way than in a large explosion or a chemical or biological attack. However, the drawn-out agony produced by such an attack would clearly create great public anxiety and outrage, especially if government and private responses were seen as inadequate, and perhaps, too, if the first attack were followed by other similar attacks. Public confidence could also be eroded, and anger heightened, if terrorists were able to hold the grid hostage by mounting limited demonstration attacks with promises of worse to come if demands were not met.
Although international terrorist groups such as al-Qaeda have been more interested in killing people that in causing economic damage, different groups with different motivations could emerge. An attack that brought a power system
_____________________
3A transmission loading relief event occurs when congestion on the transmission system prevents the transmission of electricity for which a transaction has been contracted.
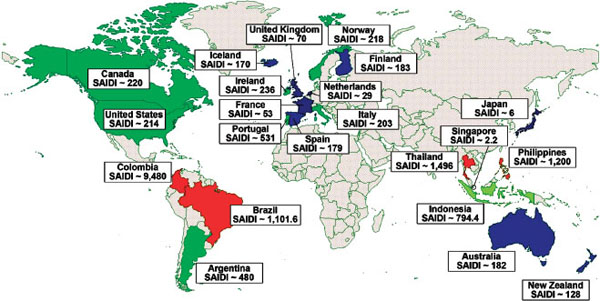
FIGURE 1.2a System Average Interruption Duration Index (SAIDI) indicators internationally for the period 1992 to 2001 (excluding only interruptions caused by major storms and hurricanes). SOURCE: EPRI (2003).
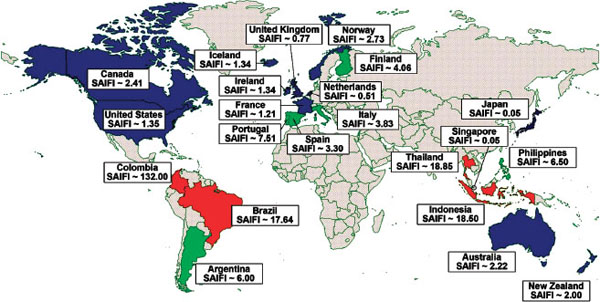
FIGURE 1.2b System Average Interruption Frequency Index (SAIFI) indicators internationally for the period 1992 to 2001 (excluding only interruptions caused by major storms and hurricanes). SOURCE: EPRI (2003).
down for an extended period could cause enormous economic damage, as discussed below.
Terrorists could, under some circumstances, view the transmission and distribution system as an important secondary target.
Terrorist attacks probably would involve physical destruction of key system facilities. However, a combined cyber attack and physical attack could be especially serious, particularly if mounted by someone with detailed knowledge of the electric power system, its physical characteristics, and its vulnerabilities.
Hackers and Other Nonterrorist Individuals and Groups
Terrorist attacks are the main focus of this report, but other types of attackers are also relevant. Not only are lower-level
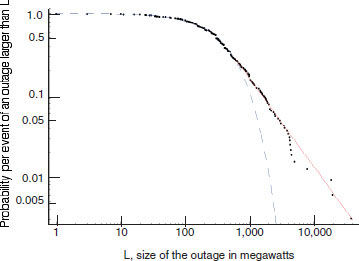
FIGURE 1.3 Relative frequency of electrical outages in the United States between 1984 and 2000. Of the 533 transmission or generation events shown, 324 involved a power loss of 1 MW (average of once every 19 days), and 46 involved a power loss of 1,000 MW (average of 3 per year). Dots indicate actual outage events. The dashed line is an exponential (Weibull) distribution fit to the failures below 800 MW loss. The solid line is a power law fit to the NERC data over 500 MW loss. SOURCE: Data compiled by NERC DAWG, plotted by Jay Apt, Carnegie Mellon University, 2006.
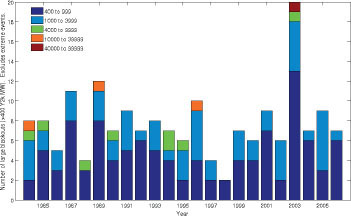
FIGURE 1.4 Frequency of electrical outages in the United States over time. Note that while there is significant year-to-year variability, there is no long-term trend. SOURCE: Data compiled by NERC DAWG, plotted by Paul Hines, Carnegie Mellon University, 2006.
attacks more likely, but many of the steps that should be taken to strengthen the system against terrorists will help against these attacks also. This section briefly describes the types of attacks that may be encountered.
Individuals or small low-tech groups with limited resources who want to kill people or cause widespread societal damage could pose a serious threat, but the amount of harm that one or a few such people could do to the electric system is probably limited. Individuals or groups that want to harm the power system but not kill a lot of people or cause widespread societal damage or harm might include people angry at the power company, bored hunters taking pot shots at insulator strings, or individuals who view the power company as an important symbol of something they oppose. For example, the Earth Liberation Front has reportedly been involved in a plot to bring down high-voltage power lines.4 Any such attack could be serious, especially if undertaken by a current or former employee with detailed insider knowledge. Between 1984 and 2000, approximately 3 percent of major disturbances in the United States were attributed to sabotage.5 The authors of Making the Nation Safer note that sabotage of individual components has “posed a nuisance, but the impacts have generally been manageable” (NRC, 2002, p. 177). Pernicious hackers are people whose primary motivation is not to kill people or cause specific damage, but rather to test limits and perhaps gain recognition within a subculture by demonstrating technical prowess by disrupting the operation of an important and highly visible societal system. Their motivation would be similar to that of computer hackers who release computer viruses and worms, or disrupt corporate and government computer sites. It is likely that such attacks would come from lone individuals or small groups.
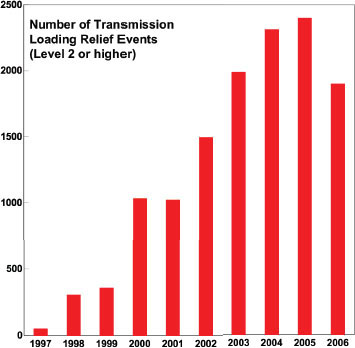
FIGURE 1.5 Annual number of transmission loading relief events since 1997. The substantial increase indicates that over the past decade the level of stress on the system has grown considerably. SOURCE: NERC data plotted by Jay Apt, Carnegie Mellon University, 2006.
Finally, harmful activity could be motivated by commercial benefit. A power company seeking a competitive
_____________________
4See “11 Indicted in Eco-terror Arsons,” available at http://abcnews.go.com/US/Terrorism/story?id=1526225.
5Based on NERC Disturbance Analysis Working Group (DAWG) data available at http://www.nerc.com/~dawg/.
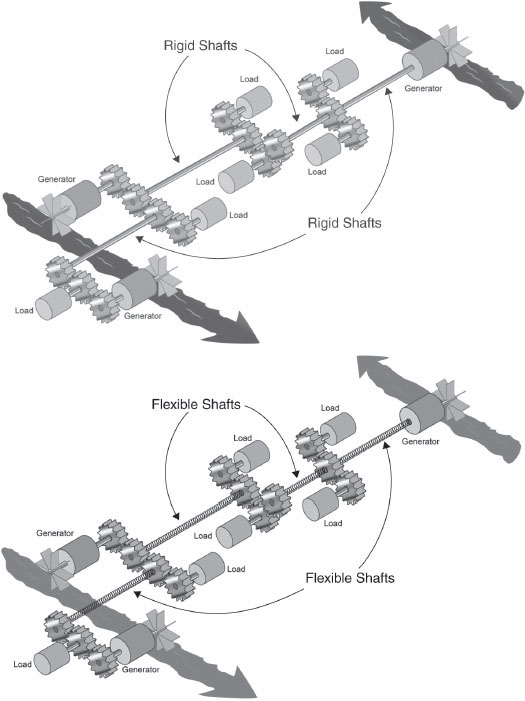
FIGURE 1.6 Illustrative analogy of electric transmission and distribution. Unlike a set of rigid drive shafts (above) that move power from generators to loads, AC power transmission and distribution systems are more accurately thought of in terms of a series of coil springs of varying stiffness through which power is transmitted by twisting (below). Since these links are not rigid, under some circumstances they can exhibit complex oscillatory behavior, or even become so tangled that they can no longer transmit power.
advantage might sabotage its competitor’s equipment, and in the process compromise the integrity of the system. Until the pernicious actions of Enron traders were revealed, few would have given such a possibility a second thought. With tighter oversight and greater awareness within the industry, plus FERC’s increased emphasis on market monitoring, such activity is probably unlikely, but the potential for it should not be ignored. The possibilities include, for example, (1) generators in one independent system operator (ISO) capturing transfer rights on tie-lines between control areas in order individual parts cannot be selected to increase congestion at those facilities and thereby maintain local market power, or (2) large buyers creating transient disturbances on the system in an effort to reduce the number of other buyers, thereby lowering system load and price. A simplified model illustrates how two or more small, physically separated generators acting together might have their supply frequencies altered and produce resonant phenomena that might cause protective devices on other large competi-
|
|
||
| Date | Location | Notable Consequences |
|
|
||
| November 9, 1965 | Northeastern United States (10 states), Ontario | Power to 30 million customers (20,000 MW) interrupted (USFPC, 1965) |
| June 5, 1967 | Middle Atlantic Region | 4 million people affected |
| May 1977 | Miami, Florida | Power to 1 million customers over 15,000 square miles interrupted |
| July 13, 1977 | New York City | Power to 9 million customers (6,000 MW) interrupted for as long as 24 hours; widespread looting, chaos; police made about 3,000 arrests (DOE/FKRC, 1978) |
| December 1978 | France | Power in part of France interrupted due to voltage collapse |
| January 1981 | Idaho, Utah, and Wyoming | Power to 1 million customers interrupted for 7 hours |
| March 1982 | Oregon | Power to more than 900,000 customers interrupted for 1.5 hours |
| 1987 | Tokyo | Power to 2.8 million customers interrupted |
| 1989 | Quebec | Power to 9 million customers interrupted; geomagnetically induced currents from solar storm |
| 1990 | Egypt | Power for entire country affected by sandstorms |
| December 1994 | Western United States | Power to 2 million customers interrupted from Arizona to Washington state |
| 1996 | Malaysia | Power to 20 million customers interrupted |
| 1996 | Philippines | Half of country affected by power plant outages |
| July 2, 19% | Western United States | Power to 2 million customers (11,850 MW) interrupted in 14 states for approximately 6 hours (WSCC, 1996) |
| July 3, 1996 | Western United States | Recurrence of July 2 disturbance; operators interrupted power supply to most of Boise, Idaho, vastly reducing the extent of the event (WSCC, 1996) |
| August 1996 | Indonesia | Power to 100 million customers interrupted |
| August 10, 1996 | Western United States | Power to 7.5 million customers (28,000 MW) interrupted; economic damage estimated at $1 billion to $3 billion (WSCC, 1996) |
| 1998 | North central United States/central Canada | Power to 152,000 customers interrupted by lightning |
| January 1998 | Québec, Northeastern United States | Power to 2.3 million customers interrupted due to ice storms |
| February 1998 | Auckland, New Zealand | Power cables failed, central business district was without power for about 5 weeks, affecting as many as 60,000 of the 74,000 people who worked there |
| June 25, 1998 | Midwestern United States, central Canada | Power to 152,000 customers (950 MW) interrupted |
| November 1988 to June 2003 | Western India | 29 large cascading failures over 15 years—1.9 per year; power to millions of customers interrupted in most cases (Roy and Pentayya, 2004) |
| 1998 to 2001 | Western and midwestern United States | Rotating blackouts in several markets because of summer prices |
| December 1998 | San Francisco | Power to 0.5 million affected |
| 1999 | Brazil | 24.5 GW of load lost short-circuit 440 KV Busbar |
| 1999 | Denmark | Power to 100,000 customers interrupted by a hurricane |
| 1999 | France | Power to 3.6 million customers interrupted by storms |
| 1999 | Taiwan | Entire country affected by transmission tower collapse due to earthquake |
| July 1999 | New York City | Power to 300,000 customers interrupted for 19 hours |
| 2000 | Portugal | Power to 5 million customers interrupted by failure of protection system |
| 2001 | Nigeria | Power to 20 million to 50 million customers affected |
| 2002 | Argentina | Power to 2 million customers interrupted by damaged cables |
| 2002 | Colombia | One-third of country affected by rebel attacks |
|
|
||
| Date | Location | Notable Consequences |
|
|
||
| 2002 | Philippines | Half of country affected by power plant outages |
| 2003 | Algeria | Entire country affected by power plant breakdown |
| 2003 | Denmark | Power to 5 million customers interrupted by a transmission line fault |
| 2003 | Georgia, Eastern Europe | Entire country affected by transmission tower collapse |
| 2003 | North Carolina, Virginia | Power to 2,200,200 customers interrupted by Hurricane Isabel |
| August 14, 2003 | Midwestern and northeastern United States, southeastern Canada | Power to 50 million customers interrupted; estimated social costs from $4 billion to $10 billion; massive traffic jams in New York City (U.S.-Canada, 2004) |
| August 30, 2003 | London | Power to 410,000 customers interrupted by incorrect relay operation |
| September 18, 2003 | Tidewater region, United States | Power to 4 million customers interrupted |
| September 23, 2003 | Denmark and Sweden | Power to 4 million customers interrupted |
| August 24, 1992 | Florida | Power to 1 million customers interrupted |
| September 27, 2003 | Italy | Power to 57 million customers interrupted; at least 5 people died; 30,000 passengers stranded in trains for hours (BBC, 2003; CNN, 2003) |
| 2004 | Florida, Alabama | Power to 5 million customers interrupted by Hurricanes Charley, Frances, Ivan, and Jeanne over a 6-week period |
| 2004 | Kyushu, Japan | Power to 1 million customers interrupted by typhoon |
| July 12,2004 | Southern Greece | Voltage instability as a result of high power transfers into Greece; operator-initiated load shedding unable to prevent voltage collapse; blackout a cause of additional concern due to proximity to 2004 Olympic games |
| 2005 | Alabama, Honda, Louisiana, and Mississippi | Power to 2.2 million customers interrupted by Hurricane Katrina |
| 2005 | Moscow | Power to 1.5 million to 2 million customers interrupted by explosion and fire at substation |
| May 24, 2005 | Moscow | Power to 4 million customers (2,500 MW) interrupted |
| September 12, 2005 | Los Angeles | Large portion of city lost power because error in substation tripped several circuit breakers |
|
|
||
tive generators to trip off the system, or perhaps even cause physical damage. With the instrumentation now deployed on power systems, it could be very difficult to detect and identify the initiator of these events. In the now unlikely event that they were to occur, competitively induced congestion, dynamic instabilities, or equipment disruptions could disrupt the system and perhaps also render it more vulnerable to compounding terrorist assault (DeMarco, 1998).
Precedents for Attacks on Power Systems
Although to date attacks on the U.S. power transmission and distribution system have been limited to small-scale vandalism by a few individuals or small groups with limited technical sophistication, elsewhere in the world the electric power system in general, and particularly the transmission and distribution system, have been a focus of considerable terrorist activity.
In a few cases, such as in Baghdad, successful attacks have been mounted against generation plants. More often, as in Colombia, efforts to attack generation have been prevented by the high levels of security that can be provided for such large concentrated targets. As a consequence, most of the attacks that have occurred have been against transmission and distribution systems. These systems make more attractive targets because they are physically widely dispersed and hence very vulnerable. Often facilities are located in remote places, making them difficult if not impossible to defend against explosions or bullets or other projectiles fired from a distance.
While there is a growing internationalization of some terrorist activity, most attacks in the past have been mounted by indigenous groups bent on damaging or destabilizing established ruling power structures. For example, in the past the Irish Republican Army mounted bomb attacks on power substations in the United Kingdom. More recently
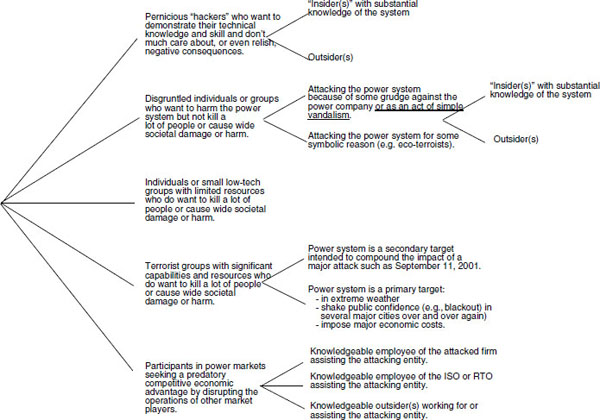
FIGURE 1.7 Simple classification of potential power system attackers.
in Columbia, FARC (Fuerzas Armadas Revolucionarias de Colombia) has mounted hundreds of attacks on a monthly basis against transmission and distribution systems with the objective of diminishing the power and standing of the central government authority and strengthening FARC’s hand in any possible future political settlement. Twenty years previously, Sendero Luminoso mounted similar attacks in Peru. With the capture and imprisonment of almost all of the senior leadership of that organization, such attacks have now largely ceased.
There have been frequent attacks on transmission and distribution facilities in Iraq by insurgent groups intent on contributing to general social disruption, embarrassing central authorities, and preventing the normalization of daily life.
Many such attacks have occurred across Asia. For example, terrorist groups in Thailand have recently increased the size and numbers of their attacks against electric power facilities as part of a broader campaign to bring down the central government in Bangkok. Many parts of Africa have also witnessed such attacks.
Although in the United States attacking the power system may not be as attractive to serious terrorist groups as bombings, or radiological, chemical, or biological attacks, there are enough examples of attacks elsewhere around the world, and enough plausible circumstance under which an attack might occur in the United States, to warrant serious attention and careful planning and preparedness.
The Department of Homeland Security (DHS) has developed a range of worst-case terrorist attack scenarios for use in gaming, in consequence assessment and management, and in supporting the development of detailed plans and response strategies (Lipton, 2005). Most of these scenarios deal with weapons of mass destruction which would not be particularly appropriate for attacks on the power systems, and in particular on the transmission and distribution system.
Nevertheless, the power industry itself has conducted scenario-based tabletop exercises to examine possible attack scenarios and their consequences. These have included a variety of exercises involving attacks against the transmission and distribution system. Individual power companies, as well as reliability organizations and trade and research organizations, have also conducted detailed power system attack simulation studies and threat assessments in order to identify vulnerable assets and to develop protective actions as well as response and recovery strategies.
IMPACTS OF WIDESPREAD, LONG-LASTING BLACKOUTS
Electricity is essential to the U.S. economy and to this country’s way of life. Annual sales in 2006 were $326 billion, approximately the same size as telecommunications (DOE/EIA, 2007). Moreover, the value of electricity is far greater than the price that consumers pay multiplied by the amount they consume. Economists refer to this extra value as “consumer surplus.”
Estimating the economic cost of large-scale or long-duration blackouts is difficult. The Wall Street Journal reported that the economic costs of the massive blackout that struck the Midwest, the Northeast, and parts of Canada in August 2003 could have been as high as $4 billion to $6 billion (Hilsenrath, 2003). North American Reliability Council data indicate that the amount of power not delivered during that blackout was approximately 920,000 megawatt-hours (MWh). Together, these two numbers suggest that the economic cost of the 2003 blackout came to approximately $5 per forgone kilowatt-hour,6 a figure that is roughly 50 times greater than the average retail cost of a kilowatt-hour in the United States. However, many of the affected industries appear to have made up for much of the lost output once power was restored. In a disruption of longer duration and greater geographic extent, a post-blackout rebound could be much more modest.
Lecomte et al. (1998) estimated that the 1998 ice storm that disrupted power to 1,673,000 customers, of whom 1,393,000 were in Quebec, resulted in economic losses of $1.6 billion in Canada and $1 billion in repair costs to the Hydro-Quebec and Ontario Hydro systems. A significant fraction of the 28 deaths in Canada and 17 deaths in the United States also resulted from the lack of power.
Large-scale disruption caused by damage to the high-voltage transmission system garners wide attention, but widespread damage in the distribution system, such as that caused by recent Florida and Gulf Coast hurricanes, can be more expensive. Schuler (2005) notes that Florida Power and Light incurred repair costs of $890 million from damage done by hurricanes in August and September of 2004, largely to distribution systems, and estimates that “the societal costs were probably even greater than those incurred in the 2003 Northeast blackout.”
Loss of power can have profound impacts on other critical infrastructures, as illustrated in an analysis by Chang et al. (2005) of a January 20, 1993, windstorm in the Pacific Northwest with documented impacts on emergency services, transportation, health care, building support, the food supply, and government. Losses included 2.5 million customer-hours of power outages disruptions for up to 3.5 days in some areas.
In the past, the pumping stations on natural gas pipelines were powered by the gas they were transporting. However, as gas prices have risen, often more rapidly than the price of electricity (half of which is generated from coal), many gas pipelines have begun to convert their compressor stations from gas to electricity—thus creating a coupled vulnerability— between what were once two independent energy supply systems. Similar coupling vulnerabilities can occur with oil delivery systems, communication systems, railways, and other critical infrastructure.
Power disruptions also put people out of work. For example, Statistics Canada reported that “an estimated 2.4 million workers in Ontario and Gatineau, Quebec, lost 26.4 million hours of work time in the second half of August because of the [2003] Ontario-U.S. power outage and subsequent conservation period.”7
Several models have been used to estimate the economic impacts of hypothetical local and regional blackouts. Greenberg et al. (2007) used a regional econometric model to examine the economic impacts of a variety of outage scenarios involving blackouts of one New Jersey utility (Public Service Electric and Gas, PSE&G, which serves about half the state) and estimated statewide impacts. The most severe scenario studied involved the loss of 95 percent of power during the first day with 10 percent of power not restored until the end of the second month. Assuming the attack occurred in the summer of 2005, the worst case resulted in a loss of 3.4 percent of the gross state product during that year ($389 billion year in 2000 dollars) followed by a positive rebound of 2 percent the following year. Since the simulated event is assumed to be localized, one of the more interesting issues explored is the extent to which businesses would choose to move to other regions thought to be less at risk of future attack.
Despite the difficulty of producing precise numbers, it is clear that blackouts of large scale or long duration can easily result in economic costs of many billions of dollars. Other infrastructure and services are also lost or are seriously degraded, further disrupting the lives of people who find themselves in dangerous situations, without work, and without conventional services such as operating bank machines and gas stations.
A systematically designed and executed terrorist attack could cause disruptions considerably more widespread and of much longer duration than the largest power system disruptions experienced to date. Since those disruptions have entailed economic impacts approaching 10 billion dollars, it appears possible that terrorist attacks could lead to costs of hundreds of billions of dollars—that is, perhaps as much as a few percent of the U.S. gross domestic product, which is currently about $12.5 trillion. If large, extended outages were to occur during times of extreme weather, they could also result in hundreds or even thousands of deaths due to heat stress or extended exposure to extreme cold.
_____________________
6OTA (1990) estimated in 1990 that disruptions of similar duration would impose costs of $1 to $5 per kilowatt-hour.
7As cited at http://www.ontariotenants.ca/electricity/articles/2003/cp-03j31.phtml.
Even without intentional attacks, power systems are always undergoing damage and recovery. While system owners and operators should do all that they reasonably can to ensure that their systems are able to withstand anticipated assaults from natural and human sources, there are practical limits to how much such systems can be hardened” because of its highly distributed nature. The complete elimination of all possible modes of failure is simply not a feasible objective. Thus, even in the absence of threats from terrorists, an important design objective should be resilience, i.e., the ability to rapidly restore the power system after a problem occurs and the ability to sustain critical social services while the problem persists.
ACTIONS TAKEN SO FAR TO REDUCE VULNERABILITY
The need to reduce the vulnerability of the U.S. electric power system is well recognized in the government and industry. Although related action has been somewhat slow and limited, many improvements made behind the scenes are rarely reported in detail to the media. Reducing the vulnerability of electric power systems is becoming a top priority of utility management. In addition, the Energy Policy Act of 2005 (EPAct) includes provisions to strengthen the system and make temporary improvements permanent. Under authorization provided by EPAct, the North American Electric Reliability Council (NERC) is now moving to improve U.S. electric power system performance through the creation of the national Electric Reliability Organization (ERO), which has the authority to develop mandatory reliability standards. EPAct also provides incentives for both expanding the transmission system and removing barriers to siting transmission lines, and it addresses the problem of relieving areas of critical congestion on the transmission system. Improving the resilience of the transmission system to relatively routine failures will also reduce vulnerability to deliberately caused failures.
Actions by the Utility Industry
Actions by the utility industry to deal with terrorism focus on prevention, detection, and restoration. Prevention measures that the industry has implemented include:
• Self-determination of the proper alert level for physical and cybersecurity in conjunction with the advice of the DHS,
• Security improvements such as physical barriers and an increased security workforce for protecting physical facilities, and
• More stringent security requirements for facility entry.
In the area of detection, several activities are ongoing, such as:
• Training system operators to consider sabotage and terrorism as a possible explanation for disturbances,
• Implementing a real-time data collection process for reporting indicators of potential physical and cyber-events to DHS (such as the presence of strange vehicles and aircraft near critical facilities),
• Holding conferences sponsored by industry and government, conducting dialogs, holding scheduled conference calls, and exchanging security-related alerts, brochures, and newsletters.
Restoration activities include:
• Preparing contingency plans for restoring service,
• Stocking equipment needed for service restoration,
• Cataloging and agreeing to share spare transformers following an attack.
The most relevant provision of EPAct is establishment of the Electric Reliability Organization to develop and enforce reliability standards for the bulk transmission system. Before it was designated as the ERO in July 2006, NERC could only recommend upgrades as needed to maintain reliability. Now, those standards will be mandatory, but they must also be approved by FERC. NERC will base its standards in part on existing data and experience with past operating incidents. According to Section 236 of the ERO certification order:
NERC states that the purpose of a Reliability Standard, or its reliability objective, should derive from one or more of the following eight general objectives: (1) the Bulk-Power System should be planned and operated to perform reliably under normal and abnormal conditions; (2) the frequency and voltage of the Bulk-Power System should be controlled within defined limits by balancing real and reactive power supply and demand; (3) information necessary for the planning and operation of the Bulk-Power System should be made available to those who need it; (4) emergency operations plans should be developed and implemented; (5) facilities for communication, monitoring, and control should be provided, used and maintained; (6) personnel must be trained, qualified and must have the authority to implement actions; (7) the reliability of the Bulk-Power System should be monitored on a wide-area basis; and (8) the Bulk-Power System must be protected from malicious physical or cyber attacks. (FERC, 2006)
Only the last general objective directly addresses the potential for terrorist attacks. Basing NERC standards on past experience will make it difficult to ensure that they protect against effects of terrorism, as there are no data on the
nature or results of terrorist attacks on electric power systems in this country. Furthermore, NERC’s intention to consider costs as well as benefits may work against protection against extreme but unlikely risks that cannot be quantified, including terrorist attacks. Overall, however, establishment of an ERO with real authority is a significant step forward. In addition, EPAct includes measures that should encourage the construction of new transmission lines and the development of new technologies to improve the efficiency and reliability of the power grid, steps that should also provide increased resistance to terrorist attacks. DOE’s report On the Road to Energy Security describes how it is carrying out its responsibilities under EPAct (DOE, 2006).
DHS’s National Infrastructure Protection Plan (NIPP) provides an overall approach to protecting critical infrastructure, including electric power systems (DHS, 2006a). DHS’s analysis of terrorist capabilities and motivations suggests that infrastructure could be a prime target, especially as protection is enhanced at other targets. The plan calls for (1) strong public-private partnerships to foster relationships and facilitate coordination within and across critical infrastructure and key resource sectors; (2) robust multidirectional information sharing that will enhance the ability to assess risks, make prudent security investments, and take protective action; and (3) a risk management framework establishing processes for combining consequence, vulnerability, and threat information to produce a comprehensive, systematic, and rational assessment of national or sector risk. Not addressed in the NIPP, however, is the issue of how private entities can be expected to assume the large costs required to make the system more robust against low-probability events.
DHS revised National Response Plan, a broad, comprehensive plan for preparing for a wide range of emergencies, also addresses critical infrastructure, including electric power systems (DHS, 2006b).
• By their very nature, electric power transmission and distribution systems are not perfectly reliable. Keeping power flowing to customers is a continuous process of control, recovery, and repair. Most outages involve only the distribution system. However, occasionally storms, accidents, or other events cause disruption of the high-voltage transmission system. Power systems are designed and operated to cope with such disturbances and to restore service as rapidly as possible.
• Well-planned attacks on the power system, undertaken by informed terrorists, could result in power outages with extents and durations that are much larger than those produced by all but the largest natural events. Damage to critical, difficult-to-replace system components could be extensive, making restoration of power slow and extremely difficult.
• Although major terrorist organizations have not attacked the U.S. power delivery system, such terrorist attacks have occurred elsewhere in the world. Simply turning off the power typically does not terrorize people. However, the United States should not ignore the possibility of an attack that turns off the power before staging a large conventional terrorist event, thus amplifying the latter’s consequences. Nor should the possibility of a series of attacks designed to do major damage to the economy and to the public’s sense of security and well-being be ignored.
• Economic costs from a carefully designed terrorist attack on the U.S. power delivery system could be as high as hundreds of billions of dollars (i.e., perhaps as much as a few percent of U.S. gross domestic product).
• Both industry and government have begun to address the risks of terrorism to the power delivery system, but there is much more that can and should be done.
BBC. 2003. “Italy Launches Blackout Inquiry.” BBC news online. September 30, 2003. Available at http://news.bbc.co.uk/2/hi/europe/3150788.stm. Accessed August 2007.
Chang, S.E., T.L. McDaniels, and D. Reed. 2005. “Mitigation of Extreme Event Risks: Electric Power Outage and Infrastructure Failure Interactions.” Pp. 70–90 in The Economic Impacts of Terrorist Attacks, H.W. Richardson, P. Gordon, and J.E. Morre II, eds. Northampton, Mass.: Edward Elgar Publishing.
CNN. 2003. “Italy Recovering from Big Blackout.” CNN. Sept. 28, 2003. Available at http://www.cnn.com/2003/WORLD/europe/09/28/italy.blackout/index.html. Accessed August 2007.
DeMarco, C.L. 1998. “Design of Predatory Generation Control in Electric Power Systems.” Pp. 32–38 in Thirty-First Annual Hawaii International Conference on System Sciences, Vol. 3. New York: IEEE.
DHS (Department of Homeland Security). 2006a. National Infrastructure Protection Plan. Available at http://www.dhs.gov/dhspublic/interapp/editorial/editorial_0827.xml. Accessed September 2006.
DHS. 2006b. National Response Plan. Available at http://www.dhs.gov/xprepresp/committees/editorial_0566.shtm. Accessed October 2006.
DOE (U.S. Department of Energy). 2006. On the Road to Energy Security: Implementing a Comprehensive Energy Strategy: A Status Report. Available at http://www.energy.gov/media/FINAL_8-14_DOE_booklet_copy_sep.pdf. Accessed September 2006.
DOE/EIA (Energy Information Administration). 2007. Revenue from Retail Sales of Electricity to Ultimate Customers by Sector, by Provider. Available at http://www.eia.doe.gov/cneaf/electricity/epa/epat7p3.html. Accessed October 2007.
DOE/FERC (Federal Energy Regulatory Commission). 1978. The Con Edison Power Failure of July 13 and 14, 1977. Washington, D.C.: U.S. Government Printing Office.
EPRI (Electric Power Research Institute). 2003. Distribution Reliability Indices Tracking Within the United States. Report No. 1008459. Palo Alto, Calif.: EPRI.
FERC. 2006. Order Certifying North American Electric Reliability Corporation as the Electric Reliability Organization and Ordering Compliance Filing. Available at ftp://www.nerc.com/pub/sys/all_updl/docs/ferc/20060720_ERO_certification.pdf. Accessed September 2006.
Greenberg, M., N. Mantell, M. Lahr, N. Felder, and R. Zimmerman. 2007. “Short and Intermediate Economic Impacts of a Terrorist Initiated Loss of Electric Power: Case Study of New Jersey.” Energy Policy 35(1): 722—733.
Hilsenrath, J. 2003. “The 2003 Blackout: Economy Won’t Likely Be Derailed—Cost Could Hit $6 Billion as Major Sectors Are Hurt; a Few Reaped Benefits.” Wall Street Journal, August 18.
Lecomte, E.L., with A.W. Pang and J.W. Russell. 1998. Ice Storm ’98, ICLR Research Paper Series No. 1. Institute for Catastrophic Loss Reduction, Toronto, Canada. Available at www.iclr.org/pdf/icestorm98_english.pdf. Accessed August 2007.
Lipton, E. 2005. “U.S. Report Lists Possibilities for Terrorist Attacks and Likely Toll.” New York Times, March 16.
Meade, C., and R.C. Molander. 2006. “Considering the Effects of a Catastrophic Terrorist Attack.” RAND Technical Report. Available at www.rand.org/pubs/technical_reports/TR391/. Accessed August 2007.
Mueller, J. 2006. “Is There Still a Terrorist Threat?” Foreign Affairs 85(5): 2–8.
NRC (National Research Council). 2002. Making the Nation Safer: The Role of Science and Technology in Countering Terrorism. Washington, D.C.: The National Academies Press.
OTA (Office of Technology Assessment). 1990. Physical Vulnerability of Electric System to Natural Disasters and Sabotage. OTA-E-453. Washington, D.C.: U.S. Government Printing Office.
Rose, A., and S-Y Liao. 2005. “Modeling Regional Economic Resilience to Disasters: A Computable General Equilibrium Analysis of Water Service Disruptions.” Journal of Regional Science 45(1): 75–112.
Rose, A., S-Y Liao, and G. Oladosu. 2005. “Regional Economic Impacts of Terrorist Attacks on the Electric Power System of Los Angeles: A Computable General Disequilibrium Analysis.” Paper presented at the Second Annual Symposium of the DHS Center for Risk and Economic Analysis of Terrorism Events, University of Southern California, Los Angeles, Calif., August 20.
Roy, A., and P. Pentayya. 2004. “Experience of Blackouts and Restoration Practices in the Western Region of India.” Slides presented at the IEEE Power Engineering Society General Meeting, Denver, Colo., July.
Schuler, R.E. 2005. “Float Together/Sink Together? The Effect of Connectivity on Power Systems.” Pp. 91–118 in The Economic Impacts of Terrorist Attacks, H.W. Richardson, P. Gordon, and J.E. Morre II, eds. Northampton, Mass.: Edward Elgar Publishing.
U.S.-Canada (U.S.-Canada Power System Outage Task Force). 2004. Final Report on the August 14, 2003 Blackout in the United States and Canada: Causes and Recommendations. Available at http://www.www2.nrcan.gc.ca/es/erb/erb/english/View.asp?x=690&oid=1221. Accessed August 2007.
USFPC (U.S. Federal Power Commission). 1965. Northeast Power Failure: November 9 and 10, 1965. Washington, D.C.: U.S. Government Printing Office.
WSCC (Western Systems Coordination Council) Operations Committee. 1996. Western Systems Coordinating Council Disturbance Report. Butte, Mont.: WSCC.













