SCENARIO 1: DENIED ACCESS TO SPACE—
AN INTELLIGENCE-INFERRED SURPRISE
It has been widely reported that several key U.S. space capabilities would be vulnerable to loss or disruption in an antiaccess/access denial (A2/AD) situation. The primary capabilities lost are (1) access to timing and position via GPS, (2) access to communications via commercial or military communications satellites, and (3) reception of ISR signals and imagery. Although our naval forces could surely inflict similar disruptions on an adversary’s space systems, the impact of potential loss of significant access by friendly forces, including those of the United States, is not diminished. The following sections describe the potential attack modes.
Electronic Attack
The most common and likely threat is electronic attack. The proliferation of military and commercial radio frequency (RF) transmitters makes the ability to interfere with satellite receivers a matter of geometry, transmitted power level, and selection of effective waveforms and operating bands. If provided with sufficient jamming power and appropriate waveform selection, then space-based communications, ISR, and GPS systems could be affected if within line of sight of an adversary.
It has long been known that GPS receivers are relatively vulnerable to interference. A number of U.S. weapon systems programs have anticipated potential GPS vulnerabilities in their designs. Accordingly, they may provide backup navigation and timing capabilities or antijam design features to afford additional
antijam margin. On the other hand, some systems do not yet have such features. Further, to the best of the committee’s knowledge, the combined impact of substantial GPS jamming from multiple sources against naval forces has not been well characterized but is expected to be significant.
Electronic jamming of communications satellites by interfering with received communications signals at either the relaying satellites or at the airborne or surface vehicles themselves can also be highly effective, depending on the antijam protection level of the communications networks. It would be expected that the lower frequency systems with less antenna directivity would be more vulnerable because there would be greater geometric opportunity to enter the receive antenna beams. Commercial systems, often used by the military, are typically not built to operate against overt electronic jamming and would therefore be expected to be relatively vulnerable to a determined electronic attack. The present diversity of available communications satellite networks can substantially complicate an adversary’s electronic warfare (EW) attack plan. On the other hand, attempting to adapt to changing network availabilities during an electronic attack can complicate friendly force operations, especially with the lines of communications being interrupted. In particular, interoperability is highly volatile in such cases because some units may be without access to some networks while others are without a different set of networks depending on jammer-victim geometries. Thus an attack on only a subset of network terminals could significantly impact the entire network by limiting the commonality of a unit’s situation awareness. As far as the committee knows, this integrated effect and identification of countermeasures to facilitate adaptation have not yet been examined.
The ability to induce interference, loss of sensitivity, and perhaps deceptive signal inputs to ISR sensors has also been discussed for many years. The diversity of sensors and their locations can complicate planning and operations by adversaries to jam communications networks. However, the ability to not only impact ISR asset availability but also degrade the credibility of their sensor data by means of deceptive waveforms can result in unreliable, untrustworthy information.
Kinetic Attack
It is well known that countries such as China and Russia possess antisatellite capabilities. Other countries are seeking such capability as well. Even if a country initially only possesses the ability to destroy satellites in low Earth orbit (LEO), the ability will probably extend to higher orbits in just a matter of years. It is further recognized that a mutually assured destruction standoff could occur in which both sides—the United States and an adversary—are capable of attack. However, the adversary may determine that attacking U.S. assets could have a greater negative effect on its units deployed far from U.S. territory than loss of
overhead access at the country denying entry, which can use land- and air-based alternatives more effectively for geographic advantage.
Cyberattack
A cyberattack can have multiple entry points and can affect far more than just space assets. But it may be especially advantageous for an adversary to impact naval command and control via communications, GPS, and ISR early in an operational escalation in order to deny us knowledge of our adversary’s movements, or, conversely, to deny them knowledge of our movements.
Sequence of Events
This scenario is illustrated in Chapter 8, in the section “Examples of the Proposed Framework for the Three Scenarios” (the figure is shown here again as Figure A-1).
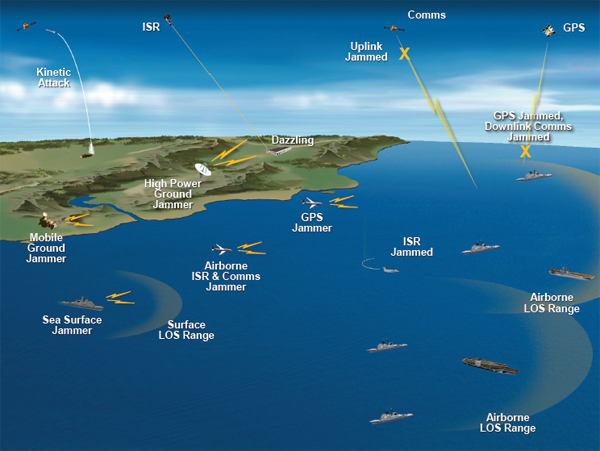
FIGURE A-1 Space access scenario.
1. As a provocation occurs and U.S. forces converge toward a denied area, the adversary country initiates a series of coordinated electromagnetic attacks on our communications, GPS, and ISR using land-based and airborne jammers. First, the attacks are intermittent, as if to serve as warnings. They become more frequent and sustained as the adversary learns how to operate and observes U.S. reactions.
2. Those U.S. assets most vulnerable and/or closest to the jamming sources are disabled immediately, and our naval forces have only limited access to situation awareness data from the front. Further, reception of command direction from the Missions Operations Center is denied except for those forces with priority antijam circuits and systems.
3. U.S. forces then begin to attack the adversary’s space systems. However, because the theater of operation is near the adversary’s borders and the adversary has other land-based and short-range communications alternatives, the impact of the U.S. attack is contained.
4. As part of the escalation the adversary opens up the attack to include cyber operations on military nodes and capital units.
5. An effort is made to limit the traffic on priority networks to the capital units with the expectation that local tactical networks such as Link 16 can be used to transmit information to and from the noncapital units via tactical links for those units for which link jammers are beyond their horizons. Whereas some weapon systems and platforms are operable in GPS jamming because they have alternative capabilities or antijam margins, other units and weapons without such features are limited in their ability to deliver precision strikes.
6. U.S. forces must respond and coordinate their activities in an ad hoc manner without having the communications connectivity or confidence in situational awareness data to ensure appropriate counteractions and access to transmitted orders. This deficit results in degradation of coordinated strategic and tactical actions.
SCENARIO 2: CROWDSOURCING VIA SOCIAL
MEDIA—A DISRUPTIVE SURPRISE
This scenario is illustrated in Chapter 8, in the section “Examples of the Proposed Framework for the Three Scenarios” and includes the following components:
• Incorporate USN, USMC, USCG,
• Determine overseas location,
• Exploit media for world opinion, create doubt, and rally discontent aimed at the United States, and
• Use social media to interfere with the execution of naval missions.
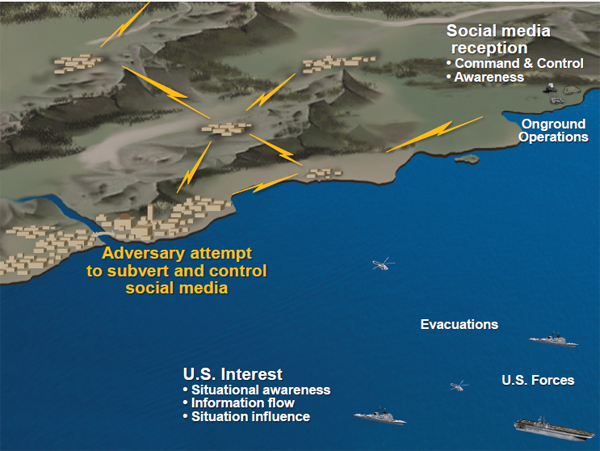
FIGURE A-2 Social media manipulation.
To explore the topic of social media in this context, the committee posited a scenario taking place in a country called Provencia. Tensions were high in Provencia. The Freedom for Provencia (FFP) (shadow organization for the international drug cartel) was making great progress in unseating the legitimate government of the country. With its comparatively large disposable incomes, generous bribes, ruthless actions, false promises, and cunning nature, FFP initiated the final stages of its campaign, to replace the country’s government and to expel all foreign law enforcement and military personnel.
The FFP’s main job was to clear the area and keep the USCG Gallatin (WHEC 721) away from it, for she had interdicted their last two drug shipments. An opportunity presented itself when the Gallatin became entangled with some abandoned fishing nets during a night mission. The action was captured on film and spliced in with film of a local fishing boat collision. This modified film clip showed a collision in which both fishing boats were lost along with several crew lives. The doctored film was sensationalized and released on YouTube and several other social networks. Industry and local populations were outraged. Media activists were recruited to magnify the problem and create additional “documented” transgressions. The following week another staged night accident involving the Gallatin occurred. Again, the media activists exploited the “arrogant” actions of the United States. The issue was introduced to the U.N. Fisheries Panel. Pressure
was mounting for the Gallatin to leave the area and to conduct only daylight operations to lessen the chance of continued “accidents.”
Ashore in the jungles of Provencia similar actions were planned for discrediting the U.S. presence in the country. The intentional night spraying of a village with noxious herbicide by helicopters caused havoc and several deaths among villagers. As the Americans from the USS New York (LPD-21) were thought to have the only helicopters, the United States was blamed and local activists provided stories and pictures to all the media outlets. A medical team dispatched from the USS New York was ambushed en route to the village and forced over a cliff and into a gorge with the loss of U.S. lives. A dam at the bottom of the gorge near the accident site was destroyed by the cartel, resulting in a flood downstream with more loss of lives and property. Explicit raw footage of the area was played on social networks and identified by the world media as the work of U.S. agents.
Village personnel traveling to an NGO medical center were attacked by personnel wearing U.S. military uniforms who spoke English. The NGOs at the medical center, representatives from several countries, took statements from the wounded villagers and filed stories with their media sources. Two American citizens visiting Provencia’s waterfront capital were beaten and robbed, and several other attacks on Americans occurred that evening in the night life part of town. The Marine security guardhouse located near the American counsel was firebombed. Marines rushing to their burning house became involved in an auto accident. All these incidents were planned, executed, and filmed by FFP operatives. Then, not only the social networks but also radio and television networks carried and expanded the stories, generating huge controversy about the U.S. presence in Provencia. A bomb went off in the market square, and personnel in American military uniforms were seen leaving the area. An American employee at the U.S. consulate and his family were attacked while attending a school soccer game, and a bonded U.S. warehouse was broken into, looted, and set afire. Crowds formed around the U.S. facility and demanded that the Americans leave their country.
The government and local law enforcement were incapable of controlling the protestors, and riots were orchestrated by the FFP. The U.S. consul general ordered the evacuation of all nonessential personnel and requested additional security forces. As evacuees gathered at embarkation points, the FFP, using the social media, called on flash mobs to inundate the embarkation sites and block all movement. The USS New York flew in a platoon of Marines to protect the consul; however, all planned landing zones were blocked by flash mobs. The USS New York dispatched landing craft toward the harbor entrance to initiate a surface evacuation option, but the entrance and channel were blocked by numerous anchored vessels.
U.S. forces finally reached the U.S. consul early the next morning after a clandestine night raid by the SEALs from the USS New York cut the anchor lines to several of the blocking vessels. The circling surface craft flowed through the breach, landed on the beach, and discharged troops, who made their way rapidly
to the consulate. Shortly thereafter a landing zone was secured and follow-on forces arrived to restore order and security at the consulate and complete the mission. See Figure A-2 for an illustration of this scenario.
SCENARIO 3: NATURAL DISASTER—A DISRUPTIVE SCENARIO
This scenario is based on a recent disaster, the Japanese earthquake and tsunami on March 11, 2011, and the resultant major nuclear accident at the Fukushima Daiichi nuclear power plant. The following events came into play:
• Largest earthquake to ever hit Japan,
• Among the five most powerful earthquakes ever recorded,
• Resulting tsunami wave reached a height of 40 meters, with a 14- to 15-m wave height in the vicinity of the Fukushima Daiichi power plant,
• More than 22,000 people died or went missing,
• Major accident was set off at the Fukushima Daiichi nuclear power plant,
• Earthquake was “surprising” because it had not been anticipated by many seismologists,1 and
• U.S. DOD involvement, known as Operation Tomodachi, was major.
The Fukushima Daiichi power plant suffered damage to nuclear fuel, the reactor pressure vessels, and the primary containment vessels of multiple reactors. There was also a large release of radioactivity, about one-sixth of that associated with Chernobyl.2 For reference, the Fukushima Daiichi power plant was designed to withstand an 8.2 earthquake and a 5.7 meter tsunami.3
The report of independent assessment of the events associated with the Fukushima Daiichi power plant accident is now public.4 The key finding from this independent report is that the accident was “a profoundly manmade disaster—
_____________
1According to James Mori of the Disaster Prevention Research Institute, Kyoto University, at the 2012 Annual Meeting of the American Association for the Advancement of Science, Vancouver, British Columbia. See Clara Moskowitz, 2012, “What We Learned from Japan’s Deadly Earthquake: One Year Later,” OurAmazingPlanet, online, February 21. Available at http://www.ouramazingplanet.com/2479-japan-tohoku-earthquake-lessons-learned.xhtml. Accessed February 13, 2013.
2Fukushima Nuclear Accident Independent Investigation Commission. 2012. The Official Report of the Fukushima Nuclear Accident Independent Investigation Commission, Executive Summary, The National Diet of Japan, Tokyo. Available at http://warp.da.ndl.go.jp/info:ndljp/pid/3856371/naiic.go.jp/en. Accessed February 13, 2013.
3J. Buongiorno, R. Ballinger, M. Driscoll, et al. 2011. Technical Lessons Learned from the Fukushima Daiichi Accident and Possible Corrective Actions for the Nuclear Industry: An Initial Evaluation, MIT-NSP-TR-025 Rev. 1, Center for Advanced Nuclear Energy Systems, Massachusetts Institute of Technology, Cambridge, Mass., July 26. Available at http://web.mit.edu/nse/pdf/news/2011/fukushima-lessons-learned-mit-nsp-025_rev1.pdf. Accessed February 28, 2013.
4Fukushima Accident Commission. 2012. Official Report, Executive Summary, The National Diet of Japan, Tokyo. Available at http://warp.da.ndl.go.jp/info:ndljp/pid/3856371/naiic.go.jp/en. Accessed February 13, 2013.
that could and should have been foreseen and prevented.”5 The report further concludes that the plant had insufficient training and that the accident “was the result of collusion between the [Japanese] government, the regulators and TEPCO [Tokyo Electric Power Company].”6 Clearly, a combination of conflicts of interest and inattention to contingency planning and safety procedures significantly contributed to the incident. Although heroism and public cooperation were much extolled at the time, the lack of material, contingencies, and C2 capability were later identified as contributing to the scale of the disaster—in particular, to the nuclear meltdown.7
Several key lessons learned from the Fukushima Daiichi nuclear power plant accident include the following:
• TEPCO was too quick to cite the tsunami as the cause of the nuclear accident and to deny that the earthquake had caused any damage.
• The power plant situation continued to deteriorate because the crisis management systems of the Kantei (Prime Minister’s Office), the regulators, and other responsible agencies did not function properly.
• Residents’ confusion over the evacuation stemmed from the regulator’s negligence and failure over the years to implement adequate measures against nuclear disaster.
• Planning to prepare for unanticipated risks was lacking.
• The supply of power for emergency use at the power plant needs to be enhanced, and the vulnerabilities of the power supply system need to be remediated.8
_____________
5Ibid, p. 9.
6Ibid, p. 16.
7Ibid.
8Ibid.








