To illustrate the complexity of the electric power delivery system, Granger Morgan, CMU, showed a diagram of a heavily interconnected system (Figure 2-1). Maintaining reliability of such a network requires significant coordination of resources. Such careful balance naturally introduces four vulnerabilities:
• Large, centralized power generation sources are often highlighted as potential targets for terrorists since the loss of a large generator would reduce electrical capacity by hundreds of gigawatts. However, as Dr. Morgan pointed out, these sources are heavily secured against all but very large terrorist attacks. Natural disasters are more likely threats, and most generators are susceptible to fuel disruptions.
• Transmission lines are easy targets for terrorists, but they are also easily replaced. However, natural disasters such as hurricanes and ice storms can also do serious damage to transmission lines.
• Substations, especially those with high-voltage transformers, are probably the most vulnerable to terrorist attack because they are essential components of the transmission system and would take a long time to replace.
• Control centers coordinate the operation of the grid to maintain reliability of the system. The loss of a control center, which is the brains of the system, can have a substantial impact on the operations of the electric grid. Much of the vulnerability of the control center is related to cybersecurity threats, which will be discussed in Chapter 3.
David Owens, Edison Electric Institute, noted that while much of the discussion is focused on the bulk power system, the most common challenges are at the distribution level, which can then end up affecting the bulk power system. He reiterated that substations and substation transformers are potential points of vulnerability in the system. According to John Kassakian, Massachusetts Institute of Technology (MIT), substation attacks are a problem that can cause tremendous disruption, particularly if key lines are affected as in the case of a switching station. Sarah Mahmood, DHS, noted that the manufacturing lead time for a single, large transformer can be up to 18 months plus another 2-3 months to get it installed and operational. Reducing this downtime is the motivation for DHS’s Recovery Transformer Program (RecX), which is discussed in great detail in Box 2-1. Joseph McClelland, Federal Energy Regulatory Commission (FERC), noted that additional complications can arise from the specialization of transformers such as changes in energy efficiency, which can impact interchangeability and thereby reduce the number of spare units for a particular location.
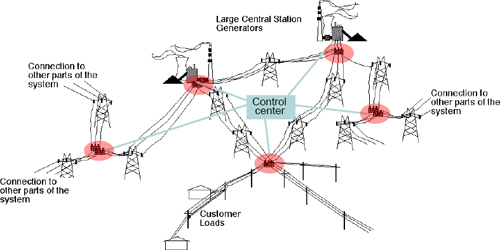
FIGURE 2-1 Illustration of the electric power delivery system. Substations are denoted by red ellipses. SOURCE: Adapted from graphic of Granger Morgan, Carnegie Mellon University, workshop presentation, February 27, 2013.
Ultimately, any of these vulnerabilities could lead to significant outages. Daniel Bienstock, Columbia University, detailed the ways in which one part of the network can have devastating impacts on the rest of the system, stressing segments that may not even be in proximity to each other. By studying the way in which small components affect the greater whole, Dr. Bienstock hopes to develop real-time control algorithms that can analyze a cascading blackout and, while perhaps not mitigating it fully, at least identify the measures to make it less disruptive. Using publicly available data for the Eastern Interconnect, he was able to show how one such control algorithm, in conjunction with fast-acting controls, could rapidly stabilize the blackout, reducing the number of line outages from almost 6,000 to just 11 for a particular initial outage. Such a combination of controls with real-time analytics is one way to dampen the impact of even a widespread terrorist attack.
The utilities are relatively well prepared for physical attacks on the grid infrastructure that are dispersed, uncoordinated, and limited according to Dr. Kassakian. As William Ball, Southern Company Services, noted, restoration procedures are well documented for an unplanned line or generator outage or a case where one or even two transformers or other equipment are affected (what are called “n-1” and “n-2” contingencies).
According to Dr. Kassakian, much more challenging is the case of a widespread coordinated attack. For instance, in the case of the 9/11 World Trade Center attack, there was a significant communications issue, as multiple agencies had different protocols that hindered a coordinated response. Furthermore, such an attack might take place across multiple nodes in the system,
which can result in the types of cascading blackouts mentioned previously. Such attacks also typically occur without warning, reducing opportunities for pre-emptive mitigation strategies. Transmission lines are vulnerable to air attack in numerous ways. He also pointed out that an attack on a switching station, which serves as an interconnect between multiple lines, might be just as disruptive as a coordinated attack.
One particularly damaging and coordinated attack could utilize the threat of an electromagnetic pulse (EMP) weapon. While there are some parallels to a geomagnetic disturbance such as the one that shut off power throughout the northern reaches of the United States and Canada on March 13, 1989, an EMP device has a far more localized and targeted impact. Massoud Amin, University of Minnesota, and Dr. Kassakian both noted that an EMP weapon, which could be as small as a briefcase, could be used to attack the control systems of the grid at the same time as an attack on the physical infrastructure, thus significantly compounding the effect of the physical attack by disabling some of the inherent balancing mechanisms in the grid. A cyberattack combined with a physical attack on the infrastructure may have a similarly crippling effect, as is discussed in Chapter 3.
As Steve Whitley, New York Independent System Operator (NYISO), noted, however, nature can launch its own devastating, widespread attack. While utilities may typically be prepared for an “n-1” or “n-2” event, Mr. Whitley noted that Hurricane Sandy was an “n-90” event. Long Island lost all ties to Connecticut and New Jersey, and New York City lost all ties to New Jersey (Figure 2-2). Over 8 GW of generation capacity went offline, both through loss of transmission and, more directly, through flooding, resulting in over 2 million customer outages in the immediate aftermath.
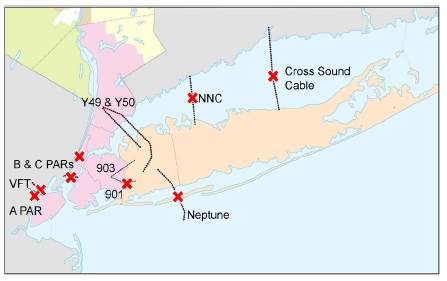
FIGURE 2-2 Interconnections in the New York/New Jersey area after Hurricane Sandy. A red X denotes an outage. SOURCE: Steve Whitley, NYISO, workshop presentation, February 28, 2013.
However, Mr. Whitley pointed out that Hurricane Sandy proved that there were a number of things that had been done to mitigate the impacts on NYISO’s customers. Because of the advance warning, regular transmission line maintenance had been cancelled, and generators on planned maintenance outages were recalled so that they could be immediately put to best use immediately following the storm. Furthermore, by contacting other grid operators in the region, it was possible to coordinate possible responses to outages and ensure that everyone in the affected area could be on the same page. During the storm, Mr. Whitley noted the difficulty of maintaining integrity of the interconnected system; however, because declining customer load coincided with a
simultaneous loss of generation capacity, it did ease efforts to maintain 60 Hz in the regions that did not lose power. Such regions were also helped by New York City’s requirements for local generation and blackstart capabilty, which is further discussed in Chapter 4. Throughout the recovery period as well, NYISO and the rest of New York’s utilities were able to operate within power transfer limits, and communications and computer systems worked properly throughout the ordeal.
Mr. Whitley, in recapping the implications of the Hurricane Sandy experience for the New York power grid, noted that with such potential for devastation of the physical infrastructure of the grid in to the wake of natural disasters and terrorist attacks, it is important to recognize the potential for lessons learned and what can be done moving forward to improve the resilience of the system. Above all, a frequent theme by participants was simply the importance of planning—communication and action protocols are critical. And Mr. Whitley quoted Abraham Lincoln: “Give me six hours to chop down a tree, and I will spend the first four sharpening the axe.” This theme emerged across all aspects of resilience.
Particular to the physical infrastructure, one major concern was the susceptibility of substations to terrorist attack. Dr. Kassakian pointed to the need for additional security measures and possible physical hardening beyond a simple fence to reduce substation vulnerability; a recent working group of the Institute of Electrical and Electronics Engineers (IEEE) is developing a standard for such security measures, including facility monitoring and improved access protocols to deter intrusion. However, as Dr. Kassakian pointed out, while such deterrence may limit access, it is optimal to have a system robust to substation failure because it is impossible to secure every facility against a physical attack.
The use of a spare recovery transformer was seized upon by many in attendance as a serious option to reduce the vulnerability of the system to failed equipment. While the components of a substation are relatively easily replaced, the difficulty of and lead time necessary for replacing a transformer is a hindrance that can slow down the mitigation response. Anjan Bose, Washington State University, currently on leave and serving on the Department of Energy’s Grid Tech Team, did mention that the recent rebirth of transformer manufacturing in the United States, as described by Mr. Ball, does reduce the amount of downtime a utility might expect for replacement. However, it was the achievements of the DHS RecX program (Box 2-1) presented by Ms. Mahmood that truly represented a significant step forward in this area. Richard Schuler, Cornell University, noted that if these transformers truly are a comparable economic investment, it should not be an impediment for many state commissions. He added that because the industry commonly subsidizes public goods, having this redundancy seems like an obvious and worthwhile investment. Jay Apt, CMU, did point out that a number of organizations at this point remain underinformed about the developments of the RecX program, and Dr. Amin expressed concern about a lag of as much as 10 years for these transformers to get out to industry given the timeline of development thus far.
BOX 2-1
The Department of Homeland Security Recovery Transformer Program
Sarah Mahmood, Department of Homeland Security, described the successful deployment of a recovery transformer outside Houston, Texas. The RecX recovery transformer program is designed to act as a rapidly deployable spare for a 365 kV:138 kV/200 MVA transformer, reducing the amount of time for transport and installation from 2 or 3 months down to about a week. The key design feature is to replace the three-phase transformer with three single-phase transformers. Each is smaller and weighs much less than a full three-phase transformer, allowing it to be delivered by truck rather than train or barge. While the transport of the transformer requires state permitting in advance, the convoy design enables rapid installation by transferring its oil, cooling equipment, and other ancillary equipment (control cabinets, bushings, etc.) along with the transformer. Part of the rapidity of installation also stems from the use of an MA65 trailer, which is analogous to a Schnabel car in design and allowed for the rapid positioning of the transformer at the CenterPoint substation. In addition, the standard modular design could be manufactured much more quickly than large custom-designed transformers.
Although the RecX recovery transformer was initially designed to be a spare that would be replaced after 2-3 years, extensive testing has proven the reliability and efficiency of the transformer to be comparable to a typical 365:138 transformer. Furthermore, at $7.5 million, the price of the RecX transformer is on a par with other 365:138 transformers on the market ($6 million to $10 million), which means that a utility could consider this as part of its sparing strategy. Currently, DHS is focused on outreach to get stakeholders RecX-certified.
Paul Parfomak, Congressional Research Service, remarked that there had been significant concern for the replacement of larger transformers, but Ms. Mahmood replied that the basic design for this transformer is applicable to the larger 500 kV and 765 kV classes of transformer as well. However, because there is no longer funding for the RecX program, replacements for these larger transformers are not being developed at this time. Until those transformers are designed, the highest capacity part of the transmission system is still vulnerable to long-term outages. There was a further question about the susceptibility of these transformers to attack—while Ms. Mahmood agreed that these transformers are just as susceptible to a physical attack as those they replaced, the RecX transformer is slightly less susceptible to ground-induced currents and, therefore, EMP weapons.
A final strategy to improve the resilience of the physical infrastructure is improved use of a synchrophasor network, as suggested by both Dr. Bienstock and Dr. Kassakian. According to Dr. Kassakian, real-time measurements of the grid using a synchrophasor network could enable better control of the load, which is of particular concern during outages involving large portions of the system. This is similar to the arguments of Dr. Bienstock, who illustrated the effectiveness of real-time control algorithms in the case of multiple line failures. In his example, such algorithms limited the cascading losses to 11 outaged lines and 25.5 percent yield as compared to the case without such controls (39.3 percent lost yield and 5,959 outaged lines). However, Dr. Kassakian highlighted the complexity of the problem as well as the resources and timescales involved, noting that such real-time control was only in the demonstration stage in limited regions of the country and was not likely to be widely deployed in the near future.