3
Systems of Detection
INTRODUCTION
A positive indication of an explosive threat from a perfect sensor does not mean that an explosive is present. In reality, neither a perfect sensor nor a signal that is completely noise-free exists. Standoff explosives detection must take into account more than the single sensor indication, because a system that relies on only a single source of information is too likely to make decisions with excessive false positives (false alarms).
A signal from a perfect sensor, or from a network of perfect sensors, is not a decision. The essential function of the system is to decide what such detection means or implies. For example, if a sensor is designed to detect nitroglycerin, the detection of nitroglycerin does not necessarily imply that a bomber is present. The molecule could have come from an individual taking nitroglycerin for a heart condition. Other corroboration is required, and this need motivates other—generally orthogonal—information. In the example above, a terahertz image of the person may indicate an explosive vest loaded with dynamite, or a pill box.
More accurate decisions can be extracted from a set of diverse sources of noisy data than from any individual source alone. The intent of a system of orthogonal (i.e., diverse) detectors is successful standoff detection of an explosive when an explosive is present and very, very few indications of an explosive when there is none.
This is not a trivial task, nor is a system of orthogonal sensors a trivial artifact. The systematic resolution of conflicting or ambiguous sensor information requires careful system design. Consider an example of an analyte-specific chemical sensor, an active sniffing detector, combined
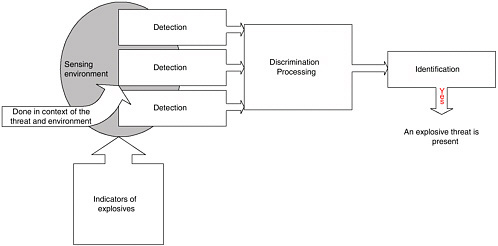
with a limited-resolution imaging device. If one returns a positive indication and the other a negative indication, what is the decision of the system: yes or no? Methods providing for resolution of the conflict must take into account sensor performance, its past credibility or reliability, context, ambient conditions, or other environmental factors. Figure 3.1 shows an architecture for segregating detection, multisensor conflict resolution, and decision.
Little work in the systems context is aimed at finding extremely rare events. Field tests and operational environments usually have some data to work with. Extending the systems approach expressed in Figure 3.1 to very rare true occurrences is a topic of research interest.
The definition and implementation of an effective standoff detection system involves a myriad of (sometimes overlapping) issues at varying levels of abstraction. Many such issues are discussed in the sections below, followed by a summary of related promising future research areas.
Background Noise Leading to Confusion
Background noise obscures positive indication of the explosive when an explosive is actually present. An effective system must discern the true signal in a cluttered background. Three levels of system effectiveness in the presence of noise can be distinguished:
-
Technology development is the exploration of the sensor itself. Generally, background noise is hardly present in this bench-top like development.
-
Laboratory development moves the sensor, and possibly the sensor system, to a less constrained environment, but one still largely free of background noise.
-
Field trial is the best test of the system in an uncontrolled environment. Technology and laboratory development are validated in the field trial only in the presence of full environmental and background noise.
Note that an active threat, intending to be surreptitious, may well be designed to look exactly like background noise. Also note that flooding the background with contamination or with mimics of the signal will effectively negate the operation of specific sensors using that detection means.
Orthogonal Improvement over Any Individual Detection Technology
A system that incorporates different, largely independent, modes for standoff explosive detection, while challenging, is better than a single sen-
sor in several dimensions. Consider an environment that contains a population of detectable indications of an explosive, as shown in Figure 3.1. The detection and decision goal is to search the environment, actively or passively, and detect as many of those indications as possible. (And at some point, as indications are detected, it will be possible to properly conclude that an explosive is present.)
A sensor searches the environment, but a particular sensor type can find indicators only of a particular type (e.g., an imaging sensor may find shape indicators of an explosive, but cannot detect molecular indicators.) Therefore, only a limited set of all possible indications can be found by a particular type of sensor. Multiple sensors of different types increase the number of possible indications that can be searched for in the environment. Eventually the increased number of indications permits the positive decision: yes there is an explosive present.
In the system using multiple types of sensors, sensitivity (the ability of the system to identify explosives if an explosive is present) is increased because the system will find more of the possible indications of an explosive. Specificity (the ability of the system to identify explosives only if an explosive is present) is increased because there are more sensor types, and they will jointly report finding indications only when an explosive is actually present. The probability of a false alarm is reduced because the several different sensor types are less likely to all report a false positive at one time. Both specificity and sensitivity can continue to increase with additional sensor types, as long as there are indications that each sensor type can find an explosive if an explosive is present during its interaction with the environment. The committee’s hypothesis is that very high specificity can be achieved with a detector-decision system.
An array, or multiplicity of identical sensors can provide temporal (movement) and spatial (location) information about an explosive device. However, an array of identical sensors does not necessarily increase the specificity of the system over that of one sensor, especially if a false alarm from a single sensor in the array results in a system-wide false alarm. A solution to increase the explosive detection system specificity would be to utilize multiple arrays of different sensor types and/or a single array of different sensor types along with an appropriate detector-decision scheme.
Robustness with the orthogonal system is also increased. The system can show robust, if somewhat degraded, response when subjected to various indignities. In the simplest case, some sensor types will continue to function if the system is presented with a single insult. For example, in an active war environment, molecular detection of military explosives will be problematic because the background amount of RDX from munitions will flood the environment. Backscatter soft X-ray imaging, however, will
be unaffected by that background. The potential partial degradation of the system must be countered by system design.
Similarly, during actual attack on the detection system, some sensor types are likely to be disabled or rendered otherwise ineffective. The orthogonal sensor-type system will still detect, but at reduced performance, until all orthogonal detection means are effectively disabled.
The result coming from a standoff explosives detection system is not static, nor is it desirable that it be static. Indeed, the likelihood of accurate threat assessment arising from the orthogonal multisensor-type system should vary with time, (i.e., as more multidimensional information is gathered, the detection estimate accuracy could increase or decrease). From the system point of view, time is inherent in the detector’s operation, in all processing and consideration steps, and in communication. In addition, time to react to the threat is increased by system and human response time.
Recommendation: Research into both new sensor types and new systems of real-time integration and decision making is needed. The sensor system research agenda should emphasize the principle of orthogonality in mathematical consideration, sensor system design, and design of information leading to true detection
Threat Analysis Qualifies System Capability
The effectiveness of the system is inherently dependent upon threats considered in the context of the environment. Novel threats or insults will be recognized only accidentally through overlap with threats currently considered by the system. Figure 3.2 shows this graphically. In the figure, sensor type A is capable of detecting explosive indicators T1, T2, and T3, while sensor type B is capable of detecting explosive indicators T1, T3, and T4. Tunknown is not detected by sensor types A and B but is serendipitously found by type C.
The environment is segregated into domains that: (1) we can control (e.g., control by design features) and (2) we cannot control: natural and background, some of which is predictable (e.g., sunset).
The threat context is itself corporate. It includes, at least, the following:
-
the chemistry or physics of the threat (e.g., material characteristics of the explosive or propellant);
-
the behavior (mode of operating) of the threat vector (a generalized notion of how the threat reaches its target); and
-
the threat embodiment, expressed in terms of differing technologies and the flexibility and capability of human actor(s).
Note: We must assume the threat is constantly changing. The system’s response—evolution—must be instilled as a requirement in the fundamental system design.
The choice of sensor types and system design must be integral with the nature of the threats. Threat analysis is used in the safeguards and security industries to identify the capabilities and motivation of adversaries to support assessment of the vulnerabilities of assets. Analysis of the vulnerability of assets includes assessment of the performance of security devices, structures, personnel, and processes. Thus, it is necessary in the case of standoff explosives detection to characterize the threats and assets (and the context in which detection must take place) to be able to develop effective technologies.
Threat Parameters
Figure 3.3 is an illustration of a partially completed threat analysis for a potential suicide bomber attack, using an event tree approach. While other approaches, such as probabilistic risk analysis, are also used for this type of analysis, this illustration shows a set of paths. Each path is made
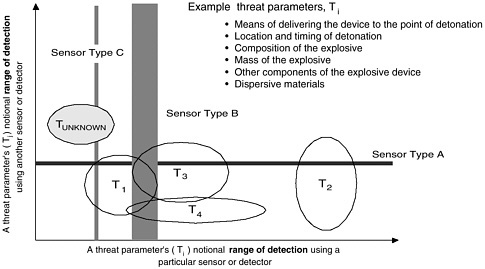
FIGURE 3.2 Notional threat space characterization showing dependence of the overall system shows effectiveness on the characterized and mapped threat. The effect of Tunknown on system effectiveness cannot be assessed.
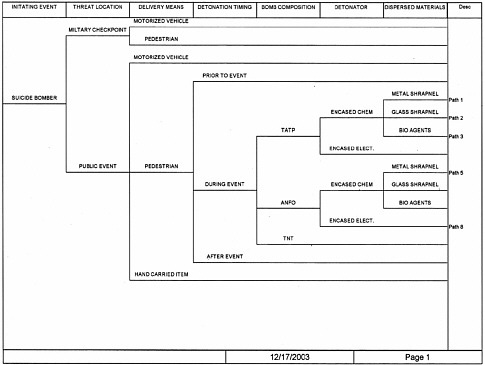
FIGURE 3.3 Threat evaluation via event tree analysis. Each path consists of a series of characteristics defining the specifics of a particular threat
up of a series of characteristics that define the specifics of a particular threat. These characteristics can be used to advantage when developing detection technologies and systems, and they also present challenges to detection success. For example, path 1 and path 5 (threats 1 and 5) are essentially identical except for the “bomb composition.” This means that detection based solely on a single type of bomb chemical composition will be effective only in the case of one threat or the other. On the other hand, detection technology that is based on the presence of potential metal shrapnel would potentially be effective in both cases.
These characteristics of the threats—threat parameters—can be used to identify the performance challenges and necessary capabilities when developing standoff explosives detection. The threat parameters include, at a minimum, the following.
-
Means of delivering the device to the point of detonation. Four distinct methods of bringing an explosive device into an area are (1) concealed on a person (e.g., under clothing); (2) in a hand-carried item such as a brief-
-
case, backpack, or purse; (3) in a vehicle (this could include airplanes and boats in some circumstances); and (4) via mailing or shipping. In some cases, the explosive material may be transported separately from other bomb components and the device assembled after passing through checkpoints or portals. For many scenarios all of the above four means will not be possible—for example, there are many places that a person can go but a vehicle cannot.
-
Location and timing of detonation. Location is critical because the effects of a detonation are dependent on the distance from the intended target. A rule of thumb is that the mass of explosive material required to cause equivalent damage increases as the cube of the distance (e.g., if the detonation-to-target distance is doubled, the required explosive mass increases by a factor of eight).1 Thus a good way to protect a specific potential target is to limit how closely a bomb (especially a large bomb such as a vehicle bomb) can approach the target. Oklahoma City and the Baghdad UN bombing are excellent examples: the effects of the blast would have been less devastating if it had not been possible to approach the buildings so closely. Timing is also critical in many scenarios, especially those in which harming people is the primary intent. A bombing in a sports stadium will have less impact if it occurs when the stadium is empty.
-
Composition of the explosive. The type of explosive (TNT, RDX, triacetonetriperoxide [TATP], ammonium nitrate-fuel oil [ANFO], etc.) is important both from the point of view of detection and because the explosive power differs for different compounds. The presence of other materials within the explosive, such as plasticizers, impurities, and taggants, can also be important. Plasticizers and other compounds that are added to an explosive formulation may reduce the vapor pressure of the explosive, thus making trace detection more difficult. However, these compounds may be detectable themselves, and may thus offer additional possibilities for detection. Impurities may also aid in detection, especially if they have high vapor pressures. An example involving drugs rather than an explosive is the detection of cocaine using canines: there is evidence that at least in some cases the dogs detect methyl benzoate, a volatile impurity in the cocaine, rather than the cocaine itself. Taggants can be of two types: (1) volatile compounds that are added to a formulation to aid in vapor detection (e.g., mononitrotoluenes in plastic explosives) or (2) chemicals that are added as a signature to trace the explosive to a particular manufacturer when doing forensic analysis after a blast. Both types are useful, but of course homemade explosives will not be tagged.
-
Mass of explosive. The mass of explosive in a device is critical in assessing how much damage it can do. Traditionally, explosive mass is converted to a TNT equivalent mass, TNT being a common, representative nitro-based explosive. Most common high explosives have from 0.6 to 1.7 times the explosive power (or heat of explosion) of TNT (4.2 kJ/g).
-
Other components of the explosive device. This can include the casing, detonator, shrapnel, and so forth. The detonator and casing may aid in detection using standard metal detection portals if they contain metal. The casing of a bomb can also influence the magnitude of the blast produced and the amount of trace material that is available externally for detection. Shrapnel, usually involving nails or other small pieces of sharp metal but possibly also glass or plastic, can greatly increase harm to humans under some circumstances. When a bomb is detonated in or near a building occupied by large numbers of people, the shards of flying glass that can be produced from shattered windows have the same effect as shrapnel, sometimes harming more people than the blast itself or the structural damage to the building.
-
Dispersed materials. In addition to shrapnel, the effects of an explosion can become much more serious if the bomb is used to disperse harmful materials such as radioactive materials, biological agents, or chemical agents. The dispersal of radioactive material using a so-called dirty bomb is outside the scope of this study.
The ambient environment is a factor in detection performance. Ambient conditions are normally of secondary importance, but they can influence detection, background, and the effects of an explosion. Ambient temperature affects the vapor pressure of the explosive and can thus influence detection, and some detectors may cease to function at extreme temperatures. Atmospheric pressure and humidity can influence some detection technologies such as ion mobility spectrometry (IMS), requiring at the least that detectors be recalibrated if these conditions change significantly. Detection of nitrogen-based explosives will be affected by the presence of other nonexplosive nitrogen-based substances in the environment.
Finally, additional considerations and risks are introduced with each human in the loop (entering data, operating detection equipment, and/or reading results).
Recommendation: Because discrimination of a useful signal in a noisy environment is always a problem, a research effort should be aimed at determining baseline ambient conditions and detecting changes in ambient conditions in real time.
Even in the presence of careful analysis and corresponding system design, there is a possibility that we cannot detect what we have not imag-
ined. Indeed, we may be able to detect only those things that we have postulated.
Anomaly Detection and Response
For standoff explosives detection in the scenarios under consideration here, there is a complication: explosives are not present very often, and false alarms are bad because they induce personnel to either disregard the alarm or disable it. Within the environment context of the operational system, conditions are either normal or abnormal. If abnormal, then they are abnormal for a reason. The system response to this condition is to investigate the abnormality in order to properly alarm and properly respond to changes in the threat environment.
When the architectural framework of Figure 3.1 is applied to the threat environment, some confounding considerations result, as shown in Figure 3.4. The dynamic variability of the threat and environment will produce a kind of dynamic barrier between detection and discrimination: this will be a probabilistic discrimination, whether explicitly so or not. Our natural inability to postulate all threat vectors will similarly produce a barrier between discrimination and the identification and decision element. In short, all systems will contain the possibility of both false negatives (reporting “no” in the presence of a true threat) and false positives (reporting “yes” in the absence of a true threat); therefore accurate assess-
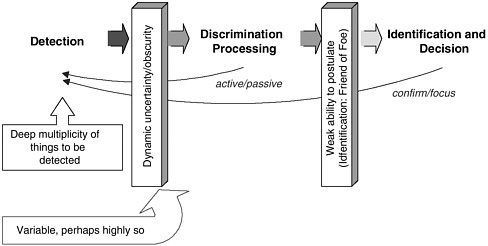
FIGURE 3.4 Information obscuration and the effect of weak threat parameter postulates.
ment of the sensitivity and specificity of system components and the system as a whole under a variety of threat scenarios is critical for accurate evaluation of the detection system.
Key feedback control signals are required in the system to increase its ability to properly determine the likelihood of an accurate threat assessment. Simply moving from a passive detection system to one that includes active elements, asking the processing steps to confirm or focus their attention, can profoundly the affect assessment of system performance.
Field validation is an explicit need and goal for system realization.
Design and Operational Requirements of a Threat Identification System
To meet the challenges of threat characteristics, dynamic ambient conditions, human in-the-loop variability, and information obscuration, operational requirements can be developed to achieve a threat identification system with maximum effectiveness:
-
Quick identification. The detection system should be able to respond quickly by detecting and identifying the threat with dispatch. However, this must be traded with system sensitivity to noise, which can lead to frequent false alarms that are disruptive. This is analogous to the trade-off between robustness and performance in the design of control systems.
-
Isolability of threat type. Isolability is the ability of the system to distinguish between different threat types. Under ideal conditions, free of noise and modeling uncertainties, this amounts to saying that the threat classifier should be able to generate output that is orthogonal to threats that have not occurred. Of course, the ability to design isolable classifiers depends to a great extent on the threat characteristics. There is also a trade-off between isolability and the rejection of modeling uncertainties. Most of the classifiers work with various forms of redundant information and hence there is only a limited degree of freedom for classifier design. For this reason, a classifier with a high degree of isolability would usually do a poor job in rejecting modeling uncertainties and vice versa.
-
Robustness. One would want the threat identification system to be robust to various noise and uncertainties in the threat environment. One would like its performance to degrade gracefully instead of failing totally and abruptly. In the presence of noise, thresholds may have to be chosen conservatively. Thus, as noted earlier, robustness needs are to be balanced with those of performance.
-
Identification novelty. One other requirement for the identification system is to be able to decide, given current threat conditions, whether the threat is a previously known type or a new, unknown kind.
-
Confidence measures. An important practical requirement for the identification system is in building the user’s confidence in its reliability. This could be greatly facilitated if the system could provide an a priori estimate of detection or classification errors that can occur. Such error measures would be useful to project confidence levels on the decisions by the system, giving the user a better feel for the reliability of the recommendations made by the system.
-
Adaptability. Threats and threat environments can, in general, change and evolve. Thus, the identification system should be adaptable to such changes. It should be possible to expand the scope of the system gradually as new cases and problems emerge and more information becomes available.
-
Explanation facility. Besides the ability to identify the threat, the threat ID system should also be capable of providing some explanations of why a particular decision or decisions were arrived at. This requires the ability to reason about cause-and-effect relationships in the threat environment to justify its recommendations. This could enable the threat monitoring personnel to interpret and evaluate the system’s decisions and take appropriate actions by utilizing their experience as well. One would like the threat identification system to not only justify why certain hypotheses were proposed but also explain why certain other hypotheses were not proposed.
-
Modeling requirements. The amount of modeling required for the development of the threat ID system is an important issue. For fast and easy deployment, the modeling effort should be as minimal as possible without sacrificing performance too much.
-
Computational requirements. Usually, quick real-time solutions would require algorithms and implementations that are computationally less complex but might entail high storage requirements. One would prefer a threat ID system that is able to achieve a reasonable balance between these two competing requirements.
Recommendation: Research is needed into the development of scenario-based threat parameters-decision trees for real-time decision making.
ROC of Systems—System Quantification; System Effectiveness
In the literature, the phrase “receiver operating characteristic” (ROC) is commonly used in conjunction with individual device performance to identify the effectiveness of the device. To avoid ambiguity and accommodate the assessment of a system built on multiple technologies, a measure called system effectiveness (SE) is used to characterize overall sys-
tem performance in the presence of environmental, threat, and other potential confusions. This SE is a function of threat characterization, technology, environment, and other factors.
System effectiveness will be algorithmically determinable. System and component requirements can then be stated without bias. The proposed system conceptual architecture provides a foundation for calculating system effectiveness.
Within the system context of orthogonal methods of detection, we still have false positives (false alarms) and false negatives (misses), and these are subject to a spectrum of influences, including the sensitivity and specificity of each component and the manner in which components are connected. Therefore, while the SE is a function of the sensitivity and specificity of the system, that system SE comprises the sensitivity and specificity of each piece of the system and the allied structure of the system itself.
A topic for research would be the mathematical formalism for system effectiveness evaluation and the related system decision making methods in the context of uncertainty.
Opposite to determining SE is the need to design a system so that it delivers a particular SE. This is a complicated task because information to support the decision is most likely expressed in a probability model, rather than a binary indication.
Recommendation: Research is recommended into methodologies to quantify system effectiveness (SE) for systems of sensors (a detection system) and for systems of detection systems allowing for noisy input from many sensors. Of particular importance is the definition and evaluation of a full spectrum of “false positive” signals ranging from detector reliability, legitimate signals that do not represent true threats, or operator interpretation of detector signals. Appropriate ROCs and other measures of performance for such systems should be developed.
Distributed System, Distributed Sensors
The architecture of a system of explosive detection devices and technologies for check-point and wide-area surveillance could consist of multiple arrays of different types of devices and technologies. The advantages of this type of system are
-
detection of potential explosive devices over a substantially larger area than with a single fixed detector;
-
ability to obtain spatial and temporal information about the explosive device in relation to the potential target;
-
provision of substantial standoff detection capability; and
-
decreased likelihood of successful defeat or avoidance of detection in relation to single-location detectors.
Arrays of detectors or sensors are currently being used and developed for many different scientific, public safety and security, and military applications including radio astronomy, fixed platform radar, optical sensing, and acoustic battlefield monitoring.
One example is the Department of Defense development of rapidly deployable marine and land-based acoustic-seismic sensor arrays. “Depending on the applications, these arrays may contain optical geophones, fiber optic hydrophones, and/or fiber optic microphones. On land, these sensor arrays may be deployed in all types of terrain for such applications as perimeter security and ground surveillance to name a few. Marine applications include harbor monitoring and fiber optic acoustic arrays for critical passive sonar platforms involved with anti submarine warfare.”2
Distributed arrays can be fixed in one location with multiple sensors or distributed over a geographical area. The most likely design for an explosive detection application, especially for wide-area surveillance, would be a set of spatially and geographically distributed arrays of orthogonal and/or partially orthogonal sensors. Although distributed arrays provide the advantage of broad coverage and increased standoff capability, they present some substantial technical challenges. The following are among the most significant:
-
Communications between sensors, arrays, and decision makers
-
Sensor sampling and refresh approaches and rates
-
Effective data transfer, integration, and assessment within an array
-
Fusion of information from different sensor or detection technology types
-
Sensor fault detection and isolation to maintain array data integrity
-
Operationally acceptable times to sense, analyze, and identify the explosive device
-
Intelligent aggregation of information for detection decision making
-
Ease of deployment, maintenance, and operation
Recommendation: Research is recommended into rapid, remote collection and concentration of explosives samples and into distributed, low-cost sensors. Included here are small (nano) and perhaps mobile sensors, distributed arrays of sensors, and the use of convective streams with or without airborne adsorbing particles to gather chemical samples.
Decision Fusion
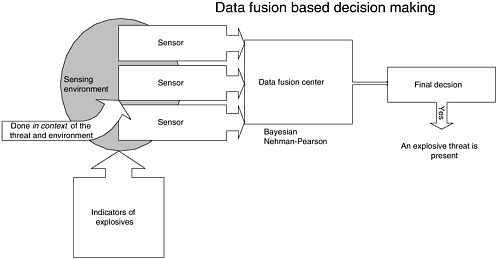
Figure 3.5 shows a sensor data fusion approach in which unprocessed sensor data are provided en masse to a data fusion center. Decisions are rendered on the basis of processing the amalgamated raw data.
Alternatively, Figure 3.1 shows multiple detectors providing disparate signals—considered input—to discrimination processing. This information is fused, resulting in qualified information leading to a decision. The detectors can, in this case, serve as relatively autonomous agent devices providing processed information for the explosives identification decision.
The goal of decision fusion is the combination of input from multiple sensors or detectors. There are several approaches, assuming conditional independence of the individual sensor indications (sensor alarms) permits an optimization of system performance using either Bayesian decision theory or Nehman-Pearson results.
Under the Bayesian alternative, for a set of conditionally independent sensors or detectors, the optimal fused decision is the weighted sum of the individual results. The weights depend on the sensitivity and specificity of individual tests or sensor system behaviors. Current areas of interest involve algorithms and approximations when sensitivity and specificity are unknown or are time-varying.
System dependency will require a substantially more complex structure for fusion. Winnowing processes and voting processes represent areas of current interest for decision making.
Recommendation: Research is needed on the integration of information from distributed orthogonal sensors to achieve real-time conflict resolution and decision making with high system effectiveness, and on integration tools based on data fusion and decision fusion. In addition, research coupling parallel sensors via decision fusion with sequential sensor systems may provide valuable insights.
Noise In-Truth Out
One of the underlying concepts for a system of orthogonal and/or partially orthogonal detection technologies is, as previously stated, that near-perfect decisions can be extracted from an accumulation of less than perfect information. This is especially applicable to current explosives detection technologies. Existing technologies all have limitations that can significantly impact either their sensitivity, their specificity, or both.
However, by combining diverse technologies in a system, it is possible to provide an aggregate detection result that is adequate for standoff applications. For example, consider a system consisting of a trace detection technology for nitrogen-based explosives and infrared imaging. When the trace detection is positive, it could indicate the presence of TNT, nitrogen-based fertilizer, or nitroglycerin tablets for a heart condition. When a suspicious image is obtained, it could indicate an explosive vest worn by a bomber or a back brace. Taken together, the two detector indications provide a more positive indication of the presence of an explosive device than each indication by itself.
There is a natural analogue for an effective system made up of imperfect (less than precise) individual detectors. Research on artificial olfactory systems at Tufts University discovered that the natural olfactory “system” appears to consist of many low-performance detectors (cells). Each of these detectors responds to a broad range of input providing amplitude, frequency, and temporal indications. Figure 3.6 is a notional illustration of the range of input that can be detected by two sensors. The area of overlap of the two provides more precise information than any one does. Research indicates that the natural olfactory system works in this fashion. It is a system made up of many imprecise detectors (cells) and processors for receiving and analyzing the information from each cell to resolve the odorant into a specific aroma.
Evolving Standoff Detection
A system for standoff detection cannot be static. Intended capability and ongoing performance must change to respond—at least—to new threats, new background conditions, changes in existing threats, and threats actively attempting to defeat the system.
Mechanisms for modifying system behavior and capability are an area of considerable research interest spanning a spectrum from identification of a new threat’s characteristics to structural change in the system design. Adaptation may be done in an evolutionary way or via manual alteration of the system. The system may successfully respond to parameter changes developed during adaptive parameter tuning or to more structural
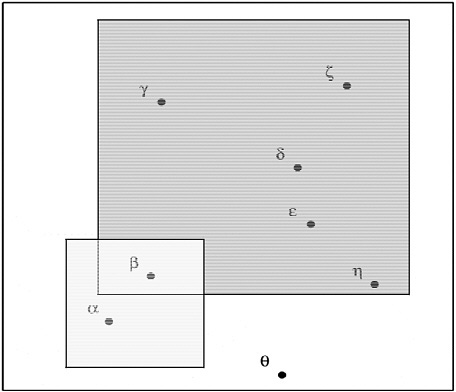
FIGURE 3.6 Illustration of precise detection with two imprecise sensors.
changes incorporating new algorithms devised during supervised learning, unsupervised learning, or combined hybrid techniques.
Given the proposed orthogonal nature of the system, the addition of new sensors that exploit novel orthogonal means of detection may be a highly appropriate response to compromised system capabilities.
Adaptation requires mechanisms for learning, and especially for learning from system detection failures expressed either as false alarms or as analogues of false negatives.
Recommendation: Research is recommended to envision and devise real-time sensor system threat detection that adapts to new threats, new backgrounds, and new threats that behave like background. A system that autonomously evolves should be a focus of research, including methods to evolve the system design to increase system effectiveness and orthogonality, given detection anomalies.
System Architecture
The system architecture of Figure 3.7 is divided into elements:
-
Detection: physical and/or informational methods to gain a signal in the presence of the background noise, whatever it may be, of that particular device or method.
-
Discrimination processing: the focus of algorithmic methodology to discriminate likely true threats from a multiplicity of signals arising above background. These methods may be objective, heuristic, physics-based, artificial intelligence (AI), or other. These discrimination algorithms operate in the presence of the several detection methods.
-
Identification: given processed information, is this a threat: decision yes or no. The identification approach, in general, would use several different signal inputs to arrive at the decision. The signals could be from different sources at the same time, or from the same source observed at different times or from a combination of both. If yes, some appropriate attribute information must be provided. Note that it should be possible to show a probability of this assessment being accurate, perhaps with a formal probability, and perhaps with an ordered listing of the sources of uncertainty.
While care must be taken in designing self-learning systems in a threat- poor environment (they may learn that nothing is a threat), there
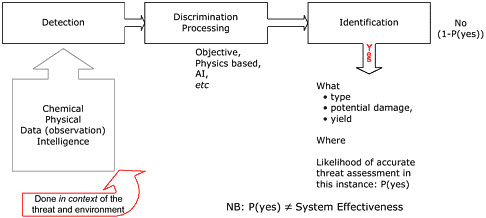
FIGURE 3.7 System concept showing segregation of detection—done in an environment—from the discrimination processing of the sensor signals and the identification of a threat, and from subsequent decision to report the threat.
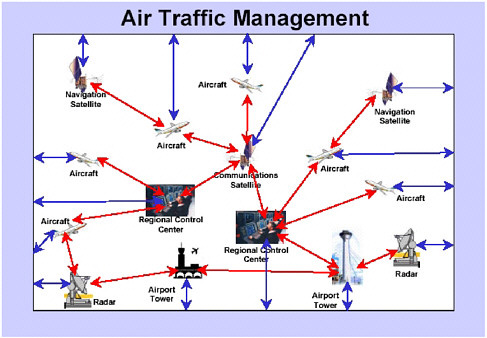
FIGURE 3.8 System-of-systems notional example showing independent, autonomous system elements carrying out their tasks and providing central authority (authorities) with discriminated information for final decision making.
should also be a feedback mechanism in the figure used to tune the system to improve its performance. Tuning would arise from whether the identification was correct or false. Thus, there should be a “model refinement” or “learning” capability in the system that is active during the detection experience, thereby mitigating the difficulty of tuning the system on simulated or artificial threats and yet requiring the system to identify very low rate real threats.
It is generally assumed that the detection methods involve several different technologies, operating in semi- or completely orthogonal modes. The degree to which they are orthogonal will impact system effectiveness. Detection is done in the context of potential environments amd the threats.
System-of-Systems Perspective
The detection system, especially for cases of a wide-area surveillance, could be designed as a system of systems. Implicit in this definition is the autonomous behavior of many parts of the system, especially remote sen-
sor-detector systems. Elements of the system execute tasks including detection and discrimination, all supporting the central authority of identification and final decision. The system effectiveness measure can serve as a metric for a dynamic allocation of resource optimization processes. A notional, compatible, example is show in Figure 3.8.
A system-of-systems approach provides a more complex solution, perhaps suitable to very complex, highly time-varying environments. It also increases autonomy at the sensor-detector and perhaps discriminator levels. Several principal issues are also exposed: detectors could demonstrate competitive behaviors, and interoperability requirements and implications will arise.