10
Design Considerations for Detect-to-Warn Defensive Architectures
The design of balanced, effective, and affordable systems for protection against biological aerosol attacks is a complex systems engineering task. The attacker has many biological agents and dispersal mechanisms available. The defender also has a large repertoire of options, although cost and logistical factors may impose limitations. Passive protective features can be incorporated to reduce inherent vulnerabilities and provide the basis for more effective active defenses. Active systems that detect and respond to an attack in progress can utilize protective capabilities that significantly reduce casualties. Technology limitations currently hamper the unambiguous detection and characterization of attacks. However, available systems based on rapid, nonspecific bioaerosol detectors (see Chapter 5) appear capable of timely initiation of meaningful responses in some important scenarios. An incremental deployment strategy for detect-to-warn systems might exploit current defensive opportunities while detection technologies mature sufficiently to provide protection in a wider range of attack scenarios.
This chapter examines architectural concepts for protection of two important target classes against the release of biological aerosols: buildings and extended military installations. A general discussion of the elements that must be considered in system design and the key principles for successful detection provide the context for more specific architectural proposals. The potential effectiveness of facility and distributed site protection systems is illustrated through simplified examples. Strategies are suggested that offer near-term, limited protection of important targets while capabilities are developed to enable more comprehensive defenses in the future. Finally, the committee offers its summary findings and recommendations on the design of defensive architectures.
SYSTEMS ASPECTS OF DEFENSIVE ARCHITECTURAL DESIGN
The overall architecture contributing to defense against biological aerosol attacks will consist of three components:
-
Passive and continuously operating systems,
-
Detection/Identification systems, and
-
Responsive protection systems.
The importance of balancing detection requirements with suitable responses has been introduced in Chapter 2. It is equally important to utilize passive elements where they are cost-effective. Passive defenses are those that are inherent features of the target and include systems that operate continuously
to provide protective effects. For example, HVAC filters and the isolation of internal air circulation zones are important passive elements in facility defenses. In an attack, these systems will reduce agent concentration and slow the movement of contamination throughout the facility. Physical security, including denial of access to the most threatening release points, is another important passive defense element. Some passive defenses can also enhance the capability of active response systems. For example, high-quality filters in a facility may reduce the biological aerosol backgrounds (including particle shedding transients caused by movement of building occupants), permitting nonspecific bioaerosol detectors to employ lower alarm thresholds. The effective isolation capabilities of well-zoned air handling systems also allow longer active defense time lines for the protection of occupants.
Effective detect-to-warn systems will also require a broad range of ancillary systems in support of the detectors. Video and other surveillance systems can provide information on unusual events in the alarm areas and on the status of occupants throughout the facility. Communication and decision support systems can provide situation assessment for the automatic controls and human decision makers who must confirm the alarms and responses. Enhanced HVAC options and perhaps controllable barriers can enable tailored airflow strategies that adapt to specific attack conditions. Communication and control systems can expedite other operational responses such as movement of personnel away from the threat cloud (evacuation or shelter-in-place) or employment of personal protective measures.
Much more systems analysis and process development are needed to define criteria for design of cost-effective defensive systems. Several general guidelines for reducing vulnerability for facility owners currently exist.1 This general guidance is useful as an orientation to first operational steps for facility protection but does not specify the more detailed process steps that would allow facility owners to complete credible assessments and response plans. Detector-based architectures, even the more straightforward detect-to-treat options, are also beyond the scope of current guidance documents. Because so many of the factors affecting detect-to-warn performance are site specific, effective ways of characterizing the potential for passive defenses and response options for active systems are essential. Criteria for considering and balancing investment in near-term upgrades of passive defenses with more advanced detect-to-treat and detect-to-warn capabilities are needed. These criteria will certainly depend on the function and importance of the protected site. For example, critical military facilities may demand a higher level of both passive and active defense than most civilian infrastructure facilities.
KEY PRINCIPLES FOR DETECTION SYSTEM DESIGN
A number of useful design principles have emerged from the consideration of nominal attack scenarios in light of current and anticipated biodetection capabilities. These have influenced the committee's recommendations on detector development pathways and on strategies for national implementation of detect-to-warn capabilities. These principles are outlined below and are illustrated in the examples discussed in this chapter.
Nonspecific, rapid (less than 1 minute response time) bioaerosol detectors can initiate significant responses for some scenarios.
Some release scenarios create potential detection sites at which agent concentration is much higher than background biological aerosol levels. For example, to attack a large facility, a rapid interior release in one of the rooms of that facility will result in very high local agent concentrations immediately following the release. Under these circumstances, nonspecific bioaerosol or standoff detectors will be able to generate a high-confidence alarm based on the abnormally elevated bioaerosol loading that could be used to initiate medium- to high-regret responses. A thorough assessment of the bioaerosol backgrounds for the defended facility is essential to the development of such a system.
|
1 |
See, for example: Department of Health and Human Services, National Institute for Occupational Safety and Health (NIOSH). 2002. Guidance for protecting building environments from airborne chemical, biological, or radiological attacks. Publication Number 2002-139. May. W. Blewett. 2001. Protecting buildings and their occupants from airborne hazards. U.S. Army Corps of Engineers Technical Instruction. Avaliable at http://securebuildings.lbl.gov. Accessed August 2003. |
Rapid (e.g., 1- to 5-minute response time) identification detectors will remain essential for more sophisticated threats. Low-level, extended-duration attacks that do not yield actionable alarms from nonspecific detectors must be addressed by detectors that employ more specific identification technologies. Many low-level releases that provide bioaerosol loadings near background levels can result in infective doses to unprotected personnel in a matter of minutes. For these attacks, continuously running identification detectors may be required to serve both the detection and identification functions simultaneously. Identification detectors will also be used to verify the initial alarms from nonspecific detectors and to expand the response if a biological attack is confirmed.
The committee focused on detectors that might achieve identification of biological agents in 2 minutes or less as the baseline performance requirement for the study. Such rapid identification will enable effective detect-to-warn responses for a wide range of scenarios. Initial analyses also indicate that significant benefits might be achieved even for somewhat slower detection time lines (e.g., 5 to 10 minutes) in some scenarios. Further analysis is needed to understand how predicted casualties decline in various scenarios as detection time lines drop from current levels of 25-30 minutes to the 2 minutes or less range postulated by the committee. Detection systems matched to available response options will yield the best performance.
Many different levels of response to biological detection alarms are often available for implementation in a specific defended site or facility. As discussed in Chapter 2, the highest level of protection can be achieved by the earliest initiation of protective responses consistent with the certainty of attack indicators. This principle can be implemented with a multistage detection architecture in which the fastest detectors are backed up by more sensitive and specific sampler-identifier systems.
Many other sources of information are available to the defense to supplement biological alarms from detectors. Some of these can be by-products of the detectors. For example, standoff detectors may be able to characterize the shape of the threatening biological cloud to determine whether it resulted from a deliberate release. The combination of reports from a network of detectors can also provide backup information to verify the reports from a single detector as well as spatial data on agent dispersion. Other types of information developed by sources beyond the detectors may be useful in verifying an attack. For example, the number of people or specific activities (e.g., cleaning) in a region of a facility may be correlated to biological backgrounds in that area. Inclusion of this factor into the decision algorithms that determine response to nonspecific detector alarms may allow use of adaptive threshold levels that better recognize attacks while minimizing false alarm rates. Integration of multiple, disparate sources of information is vital in characterizing potential biological attack events.
FACILITY PROTECTION ARCHITECTURES
Enclosed facilities are important targets and deserve special consideration for detect-to-warn protection. They may be the targets of choice of less sophisticated attackers since the required quantity of agent and the level of agent weaponization are reduced. A relatively inefficient dispersal mechanism may also be adequate. Facilities are also important owing to both their symbolic importance and, often, their vital military or political functions.
Facilities offer unique opportunities for significant detect-to-warn protection of their occupants. The fundamental defensive concept examined in this section centers on reduction of agent dispersion within a facility through the use of passive facility modifications as well as active, detection-based responses. Approaches suggested here will not assure protection for all occupants of a facility in the event of an attack. For example, if a release occurs in one room or region of a facility, detection and responses can be initiated in an attempt to reduce exposures throughout the facility. Unfortunately, such responses are unlikely to protect occupants from the very high agent concentrations near the release point.
However, for other building occupants, a number of factors can intervene to reduce the likelihood of infection. Normal transport delays, dilution in the HVAC system, and isolation of major air handling zones limit the rate of concentration buildup at points away from the release area. Active air handling responses to improve these natural mitigating factors include shutdown or redirection of airflows toward the release
area. Other effective responses include evacuation of building occupants along uncontaminated routes and use of temporary personal protection measures during the response or evacuation. In the case of outdoor attacks, the sheltering effects of facilities, perhaps enhanced by active response to enhance isolation, can play important protective roles.
Because facilities and their associated air handling systems and other response options span such a broad spectrum, it is impossible to identify detection requirements that will be universally applicable. Site-specific facility characteristics will have a dominant impact on requirements and resulting effectiveness of all defensive concepts. A thorough countermeasure analysis will also be required to determine whether unique site vulnerabilities might compromise the operation of a defensive system under consideration.
The nature of airflow characteristics within a facility is one of the most critical factors that influence the vulnerability of the facility to attack and the effectiveness of potential defenses. These issues will be discussed in the next section, followed by an example that illustrates the behavior of one hypothetical building.
Time Line and Zone Isolation Considerations
The transport of agent from the release point to other parts of a facility is primarily the result of pressure-driven flows induced by air handling fans. Other pressure-driven flows, particularly external winds acting through exterior openings, may exist. Flows induced by temperature differentials may also be important in some interior spaces. While these diverse flow drivers will ultimately result in a broad distribution of the agent within the facility, there are significant time delays and reductions in agent concentration in the process. Proper air handler responses can significantly increase these protective factors.
Examination of the time lines and losses associated with agent transport processes can inform questions regarding detector response requirements. The transport of an interior release consists of a series of steps. These include:
-
Mixing within the immediate region (or room) where the release occurs.
-
Intrazonal transport to the other rooms or regions supplied by the air handling unit in the release zone.
-
Interzonal transport, including exchange across zone boundaries that spreads agent to adjacent air handling zones.
Specific times associated with each of these steps will depend on the operational status of the air handlers at the time of the attack as well as the layout, ductwork, and physical barriers associated with the facility and the HVAC system. Since the flow of biological agents has a great deal in common with other types of vapors and aerosols, much of the literature regarding indoor air quality applies to consideration of these areas. Unfortunately, the dominance of site-specific factors places severe limitations on the ability to provide broadly applicable insights into transport rates. However, some general observations followed by a nominal example may be useful.
The time delays associated with mixing in the immediate room or region of the release will depend upon the internal air currents within that region and the overall air exchange rate driven by the HVAC fans. Some results indicate that the time constant for aerosol mixing in a room following a rapid point release is on the order of 2 minutes.2 This means that a concentration buildup at return ducts in a release area may allow detection at that point within 1 to 2 minutes. Experimental studies on aerosol dispersion in laboratory rooms have identified some of the factors that account for uncertainties in the delay time and spatial distribution of the agent in the region and have recommended detector deployment locations.3
Placement of detectors closer to potential release points can reduce time delay and increase the concentration of agent at the detectors, but it risks poor response times for releases that are placed away from the detectors. Tracer and modeling studies of the behavior of releases within areas of concern can assist in the analysis of site-specific flow patterns and the designation of detector deployment locations.
The rate at which contamination spreads from the release area to other areas within the same HVAC zone depends on both the rate of air exchange and losses due to agent deposition in the ductwork and filters of the HVAC system. The dilution due to mixing from nonrelease regions and the cleaning caused by HVAC filters can be reasonably well predicted. However, these effects will depend on the HVAC operational status (localized temperature conditions, fresh air fraction, air exchange rate, and so forth) at the time of the attack.
Transport of the agent across HVAC zone boundaries is quite difficult to predict. It is dependent on the design, operation, and isolation of each air handling zone as well as many other effects such as external temperature and wind conditions. In large open spaces served by several air handling units, there may be minimal independence and isolation of the flows between units. Furthermore, particularly in facilities with connected air spaces, the imbalance of widely separated air handling units (i.e., some units operating with excess supply and others with excess exhaust) can create net driven flows across wide areas. Many other uncertainties that are difficult to characterize and model can create very wide bounds on interzonal transport.4 The problems associated with the analysis and modeling of agent transport in large open spaces such as exist in convention centers, sports arenas, and airports are particularly difficult. These have been studied in some detail5 although the prediction of flows is so complex that empirical methods may be the best alternative for applied defensive system design.
Pressure-driven flows caused by external winds may also be important in determining both intra- and interzonal transport conditions in a facility. These flows are a function of many variables, including the inherent tightness of the building, status of building openings (i.e., doors and windows), direction and intensity of the wind, and the air handler operating conditions. As a result, the characterization and analysis of the impact of such flows on defensive responses involving airflow control can be complex. In some facilities, these factors may be so significant that they preclude the possibility of predictable, defensive airflows being set up by the air handlers in response to an attack.
An example that postulates a release inside a multizone office building is included in the following section to illustrate defensive concepts and the approximate time lines and agent concentrations resulting from a nominal attack scenario. While this example does not represent any particular building, the parameters used in the simplified model are representative of a modern office building designed with attention to airflow control and vulnerability reduction.
Example: Attack on a Multizone Office Building
A biological agent is assumed to be released into a single office in an office building served by three air handling units. The total volume in the facility is assumed to be approximately 3,000 m3. In this simple, illustrative example, each of three air handling zones in the facility is of equal size and the release room is assumed to comprise 10 percent of the release air handling zone (3.33 percent of the total facility). For the baseline scenario, an attacker releases enough dry anthrax powder of appropriate size to provide one hundred times the median infectious dose (assuming a 5-minute exposure interval) if the agent were instantaneously spread throughout the entire facility. The median effective dose for anthrax is assumed to be 8,000 spores, as shown on the plot of probability of infection versus dose (commonly called the probit curve) in Figure 10.1. The actual amount of powdered material required for the baseline
|
|
in a plutonium facility. Health Physics 72:734-743. Whicker et al., 2002. See note 2 above. |
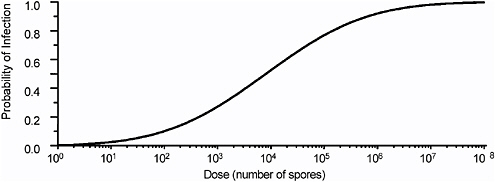
FIGURE 10.1 Probability of infection versus dose for inhalation anthrax.
release will depend on the efficiency of the release mechanism. For a perfectly efficient dispersal scheme (an impossible task even for sophisticated attackers), the release amount would be about 0.1 to 0.2 grams of high-quality anthrax powder. For more realistic release efficiencies, the amount required would be proportionately higher. Other cases for which the effective release quantities are much larger are also considered below. The agent is assumed to be released over a period of 5 minutes. If a more infectious agent were to be released (see Table 2.1), then the number of particles required for an effective attack would be smaller.
The nature of the assumed flows is diagramed in Figure 10.2. The agent is released in the release room. The other rooms in the air handling zone where the agent is released are designated as zone A1. The adjacent air handling zone is designated A2 and the final zone, A3. The air exchange rate between rooms within a single zone is determined solely by the air handler rate of 4 air exchanges per hour. Interzonal airflow is modeled as an equivalent air exchange rate of 0.4 air exchanges per hour with the adjacent zones. This value is not atypical of the rate that can be achieved in modern office buildings with well-designed HVAC systems.6
For this example, the only fresh air input is through the air handler inlets with no infiltration or

FIGURE 10.2 Airflows in the multizone office building.
|
6 |
See, for example, the case study in Sohan et al., 2002. See note 4 above. |
exfiltration of outside air through doors, windows, cracks, or other openings. For tight buildings, where infiltration and exfiltration effects might result in the equivalent of only 0.1 to 0.2 air changes per hour, this simplification is reasonable. However, there are many buildings for which these effects will have a much larger impact on intra- and interzonal transport and therefore would need to be considered in the analysis. For the cases discussed, 90 percent air recirculation through the HVAC air handlers and 98 percent HVAC filter efficiency are assumed. This filter efficiency is representative of filters currently installed in some modern infrastructure facilities (e.g., airport terminals) where interior isolation from outdoor pollutants is desired.
Agent concentration levels within the facility when no changes in air handler operation are initiated following the release are shown in Figures 10.3 and 10.4. Concentrations in the release area, in the air handler plenum for zone A1, and in other offices in zones A1, A2, and A3 are plotted. The concentration in the A1 air handler is calculated for the plenum upstream of the filters.
Figure 10.3 shows the long-term (about 200-minute) change in the relative particle concentration in the release room, other rooms in the release zone, and the other two air handlers in the building. Following an initial buildup, the long decline in concentration is due to the impact of filtration and make-up fresh air. It is notable that equilibration and reduction in concentrations to relatively safe levels takes several hours. The early time contours shown in Figure 10.4 show the wide differences in concentration in the various zones for the time intervals of interest for biodetection and response. For times in the 3- to 5-minute range, which would be reasonable for rapid detection and response using nonspecific detectors, the difference in concentrations between the release room and the adjacent air handler zones is quite significant. For example, at about 5 minutes following the release time, there is a five orders of magnitude difference between the release room and the adjacent zone and another two orders of magnitude drop in the third air handling zone. These can be viewed as protective factors that are gradually reduced over time as the agent is dispersed throughout the facility. The protective effect of filtration and good interzonal isolation of airflows in a facility can be quite significant.
The agent concentrations in the release room and in the return plenum of the A1 air handling unit (as shown in Figures 10.3 and 10.4) are expected to be well above biological aerosol backgrounds, particularly for facilities that employ good filtration and other design features to reduce background levels. (For a more extensive discussion of the determinants of biological backgrounds, see Chapter 3.) If this conjecture is verified by long-term background data from facilities of interest, then the use of nonspecific detection for initiation of medium- or even high-regret responses with low false alarm rates appears possible. Nonspecific detection from detectors in other rooms of zone A1 is not as promising due to reductions in agent concentration caused by the air-handler
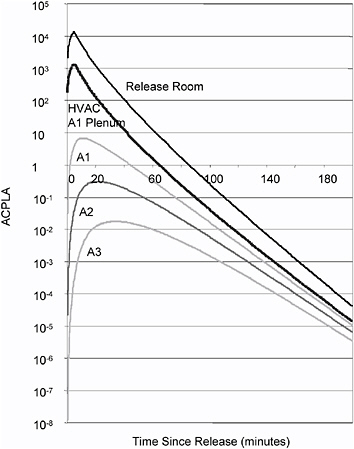
FIGURE 10.3 Anthrax concentrations for baseline release scenario, with no HVAC response.
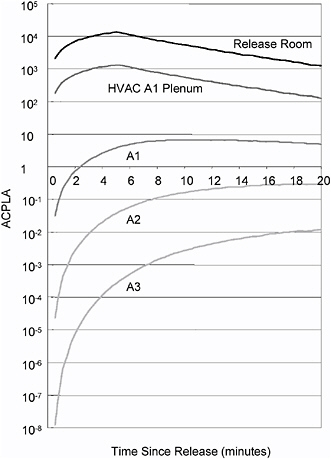
FIGURE 10.4 Early time anthrax concentrations, with no HVAC response.
filters. Hence, if detectors cannot be proliferated in rooms throughout the facility, the best deployment locations appear to be in the return plenums of the air handlers. Since site-specific factors determine both background levels and the intra- and interzonal flow characteristics of facilities, it will be important to measure long-term background levels as well as the airflow characteristics during the design of defensive systems. Note also that the curves in Figures 10.3 and 10.4 assume instantaneous mixing in the release region. In reality, there will likely be a several minute delay due to local mixing processes before these levels are observed in the release room return ducts or air handler plenum. In other cases, such as a release into the return duct to the air handler, the intra-zonal dispersion of the agent throughout the air handling unit will begin almost immediately. This condition might creat more favorable conditions for detection of an attack by sensors in the air handling unit but might also reduce the effectiveness of airflow controls in isolating other rooms or other air handling zones to reduce agent speed.
Estimates for the probability of infection of occupants in the various zones for the baseline scenario with no HVAC response and HVAC shutdown are shown in Figure 10.5. It is assumed that the occupants of the facility are unwarned and do not respond to the event. The solid curves show the increase in probability of infection when no HVAC response occurs. The lower, dashed lines indicate the reduction in probability of infection for HVAC system shutdown at 3 minutes following the release. These infectivity estimates are based on the probit curve shown in Figure 10.1. It is notable that the isolation of air handling zones and the effects of good filtration provide a significant benefit to the occupants of the facility away from the release room even in the absence of any protective responses. These benefits are due to a slower buildup of agent in air handling zones away from the release zone, which allows a significant time for a protective response to be mounted.
The probability of infection 90 minutes after the attack is 0.67, 0.36, and 0.12 in zones A1, A2, and A3, respectively, if no air handling response occurs and if occupants remain stationary (Figure 10.5). For the HVAC system shutdown response at 3 minutes, it is assumed that flows from the release room to A1 are halted and that interzonal flows are reduced from the assumed baseline level of 0.4 air changes per hour to 0.1 air changes per hour. One might imagine even more effective interzonal strategies if positive differential pressures were established in adjacent zones, causing a net flow back into the release zone to force a more rapid exhaust of the agent out of the release zone.
An attacker can reduce the time available for response and increase the threat in remote air handling zones by increasing the size of the attack. Larger attacks result in a greater amount of agent being transported to adjacent zones in the early stages of the attack, before response can be initiated by detection systems. The probability of infection for the unwarned (no HVAC or other response) case is also increased. The unwarned probabilities of infection for releases that are 10 and 100 times baseline level are shown in Figure 10.6. Even for the much larger attack sizes, the buildup of agent in the adjacent zones is still reasonably slow.
Figure 10.7 shows the increase in probability of infection over time in zone A2 for different attack sizes. Even at 10 minutes, the probability of infection in A2 for the 100x baseline case is approximately .53, significantly below the final unwarned level of .85. This slow change in infectivity even in the face of large changes in attack size is largely the result of the highly nonlinear probit curve. Because infectivity rises slowly with increase in attack size, responses in the few (1 to 5) minute range will have significant value, even for very large attacks. A sound understanding of the basis for current probit slope assumptions will be required before defensive system performance requirements can be specified with high confidence.
The impacts of different responses on the probabilities of infection for several attack sizes are summarized in Figure 10.8. For each bar representing a specific attack size and air handling zone, the top level represents the probability of infection for an unwarned population (no HVAC or other protective response). The next level reflects the reduction due to a shutdown of the HVAC 3 minutes after the attack. The lowest bar represents infectivity levels resulting from HVAC system shutdown at
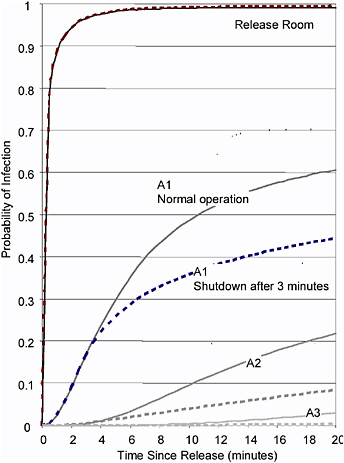
FIGURE 10.5 Probability of infection for unwarned, with no HVAC response, and with HVAC shutdown response.
3 minutes, followed by evacuation of the occupants of the facility into uncontaminated air 10 minutes later. Particularly for the remote air handling zone (A3), early shutdown appears to provide the most important contributions to reduction in probability of infection.
It is important to note that the larger attack sizes postulated in the 10x and 100x scenarios will result in very high biological aerosol loadings in the release room and in the air handler in zone A1. These levels would be so high above background that nonspecific detectors in the air handling unit of the release zone would likely provide a rapid and unambiguous alarm. For such releases, current bioaerosol detection technologies may be able to provide the basis for the most responsive shutdown and evacuation response, shown in Figure 10.8.
The nominal parameters used in this example demonstrate the potential for active detection and defense in a modern facility. The assumed flow values do not represent the measured response of any particular facility. Such low interzonal flow rates may not be present in most current facilities but are not unreasonable for modern HVAC system designs in buildings constructed with interzonal isolation in mind. More complete architectural studies and empirical assessments of the performance of real facilities are needed to fully assess the promise of these concepts.
Impact of Facility Design on Defensive System Effectiveness
Investments in facility and HVAC protective features can have a major impact on the passive vulnerability of a facility to biological attack. A balance must be sought between improvement of passive elements of facility defense and the active systems that respond to attacks. While a detailed exposition of these issues was beyond the scope of committee deliberations, several factors that bear on the performance of facility defenses are reviewed here.
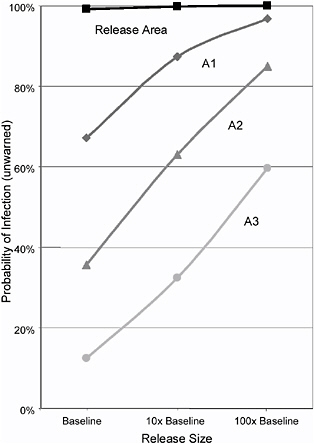
FIGURE 10.6 Probabilities of infection for larger releases, with no response.
Air Handling Zone Isolation as a Fundamental Strategy
The isolation of independent air handling zones to reduce transport of released agents is a fundamental defensive element in facility protection. If large, pressure-driven airflows mix the released agent rapidly across many air handling zones throughout the facility, the potential for reduction of casualties is significantly reduced. There are many ways in which this facility-wide mixing can occur. In extended open spaces, large drift flows can result from imbalance of air handlers serving widely separated regions or by external wind effects through doors, windows, or other openings. The intermingling of ductwork from two different air handing zones can greatly increase the rate of mixing. Finally, thermal effects can create significant mixing flows, particularly in open atrium areas exposed to sunlight through windows and in open vertical spaces of multistory buildings.
Major pressure-driven drift flows in large interconnected spaces have been observed in real facilities. For example, tracer tests and air velocity instrumentation in airport terminals have measured flows that would transport agent rapidly through several air handling zones.7 Flow velocities up to 1 to 2 meters per second have been observed in corridors where restricted flow paths exist between large-volume facilities. In cases such as these, reduction in interzonal flows is one of the most important defensive measures that can be implemented.
Provisions to reduce interzonal airflows are relatively easy to incorporate in new construction. Assuring that ductwork from several zones is not intermixed, that zones are physically separate where possible, and that flows driven by exterior openings are minimized are useful steps. The balancing of air-handler fans is perhaps the most important vulnerability reduction step that owners of existing facilities can take. Each isolated zone should be operated to equalize supply and return flows to minimize the pressure-driven flows toward or away from that zone. Other changes that increase interzonal isolation, such as separation of ductwork in adjacent zones or physical barriers to block flow from adjacent zones can be retrofitted into existing facilities, although costs may be prohibitively high.
Filters and Other Background Reduction Measures
High-quality filters can have a significant impact on the concentration of biological agents that are transported through the air handling systems. Filters with average removal efficiencies of about 98 percent for biological aerosols over the anticipated sizes of interest are currently being installed in airports8 and other modern facilities for air quality reasons. Even more effective filters are under
|
7 |
D.M. Edwards. 2002. Tracer release experiments at San Francisco International Airport to improve preparedness against chemical and biological terrorism. Sandia National Laboratories, Report SAND2001-8380. June. |
|
8 |
Edwards, 2002. See note 7 above. |
development, although higher operating costs and shorter replacement intervals are expected for these systems. Other more innovative filtering and air cleaning measures are currently under research. (See Chapter 3 for a more extensive discussion of air cleaning alternatives.)
The added benefits of filtering and other air cleaning technologies for protection against biological attack should be considered as a factor in decisions that relate to the quality of filters installed in new or existing facilities.9 In light of the growing perceived threat of biological attack, such considerations might justify larger investments in more effective filtration. When active defenses are planned for a facility, the potential added benefit of reduced biological backgrounds that enable enhanced detector performance should also be considered in the review of filtering options.
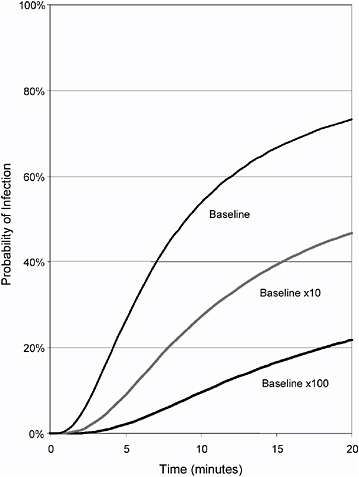
FIGURE 10.7 Probability of infection versus time (zone A2) for larger releases.
Implementation of Facility Defensive Features
Many performance trade-offs must be faced in the implementation of defensive systems in existing facilities and new construction. Analysis of the diversity and uncertainty in current and future threats must underlie design processes. Guidance for system design, including performance and cost-effectiveness criteria, could be developed and coordinated with facility owners and appropriate government oversight agencies. For existing facilities, approaches to tailor operational plans to site-specific constraints could be formulated. Security procedures should be reviewed for preventing unauthorized individuals from having access to locations vulnerable to agent release. Assessment and characterization processes to identify vulnerabilities and potential response options are needed. Incorporation of defensive features into building designs before construction will enable inclusion of passive and active defensive provisions at the lowest cost. Standards and processes for the design of new construction to reduce vulnerabilities and permit straightforward incorporation of active defenses, either at the time of construction or later, should be provided to architects and developers.10 Implementation must also consider the impact on performance of long-term system maintenance and personnel issues. Such factors as air-handler balancing, filter system maintenance, and facility changes that affect zonal flow isolation can dramatically impact the performance of a defensive system. Where system response depends on the intervention of a skilled operator, the effects of training and other human factors can also be very significant.
Other Facility Detection System Considerations
In the above example, the defense exploits locally high concentrations resulting from a relatively rapid release of an agent interior to the facility. However, there are other tactics that might be employed by a more sophisticated attacker to reduce the nonspecific signature of the attack. One is a slow release or trickle attack in which very small amounts of agent are released at an interior point over a long period of time. A second is the release at an exterior inlet for one or more air handling units.
Low-Level Attack Scenarios
Very slow releases can cause gradual buildup of agent so that concentrations remain near background levels throughout the facility. Mounting such an attack could take many hours and will require a more advanced dispersal system that can effectively dispense agent at a slow, controlled rate. The attacker also

FIGURE 10.8 Probability of infection for various release sizes and response options. (SD3, HVAC system shutdown at 3 minutes.)
faces the prospect that slower, more sensitive detectors and samplers that collect large air volumes will discover the release in time to take defensive action to disrupt the release. Finally, since the concentration builds up gradually across the facility, a small number of relatively slow, high-sensitivity collectors and detectors may be adequate to discover the attack in its early phases.
Releases at exterior inlets to the air handling system will also create significant bioaerosol loadings in the air handler if the release period is short. Concentrations at the inlet duct may be comparable to those resulting from interior releases if the air handlers are operating in a mode that recirculates a significant fraction of the uncontaminated interior air. For trickle releases at the air handler inlet, the detection and defense problems are expected to be comparable to similar slow releases at other interior locations.
Much more detailed analysis is needed to assess the range of potential attack scenarios and resulting demands on the biological detection architecture. It appears that the ability to implement continuous, highly sensitive identification detectors to protect against low-level attacks may be a requirement for robust facility defense. However, the response times needed to defend against such low-level releases are expected to be much less stringent than those required for the higher release rates considered earlier.
Distributed Detection Architectures
If detectors could be made cheap enough and reliable enough, one would ideally like to spread them throughout a facility, much as smoke detectors are used today. This would offer several potential performance advantages for detection architectures. Detection sensitivity requirements for distributed detectors can be somewhat lower than for detectors centralized in the air-handler units. This is because
detectors placed near the release will see the high local concentrations associated with that release as well as a more rapid change in biological background away from baseline levels. By contrast, the agents entering the air-handler plenum are diluted with uncontaminated return air from the nonrelease areas of the air-handling zone, increasing the sensitivity requirements of the detectors. Compared to distributed detection assets placed near the release, somewhat greater time delays will be experienced by the centralized detectors, associated with the flow of return air to the air handler and a slower rate of change in agent concentration buildup. One disadvantage is that the greater number of detectors in a distributed system could result in more false alarms. However, this effect might be offset by the ability to set higher detection thresholds in a distributed system to reduce the false positive rate per detector. Furthermore, adjacent detectors could provide overlapping coverage that will assist in ascertaining false alarms and other single-detector malfunctions.
The operating conditions of the air handling system will also impact the relative requirements and advantages of a distributed and centralized architecture. For example, when recirculation is low (fresh air fraction high), the detection sensitivity requirements on a detector in an air handling unit may be quite high owing to the large dilution factor caused by mixing of both fresh air and air from uncontaminated interior regions. This dilution due to fresh air mixing would not affect the concentration profile observed by distributed detectors in the release area.
Confirmation of initial distributed alarms with more centrally located identification assets will remain important for the foreseeable future. Hence, this distributed concept would not avert the need for multistage detection capability.
Facility Protection—Strategies and Priorities
A national strategy for protection of critical military and domestic facilities must balance the need for near-term implementation of systems that have constrained capabilities with the competing need for more extensive research, development, and demonstration of systems that can counter a broad range of biological attacks. A phased strategy that simultaneously deploys initial defensive systems in critical facilities and accelerates research on the most promising technologies for augmentation of these defenses could be the best path forward. A well-designed, modular approach to multistage detection and response architectures could allow for incremental improvements that would result in effective facility protection upgrades within 2 to 5 years. The key elements of a strategy that could be implemented in several phases are outlined below.
-
Phase 1 priorities. The use of currently available, nonspecific aerosol detectors to activate facility responses can significantly reduce casualties for some scenarios if facility passive and HVAC systems are designed and operated with this goal in mind. Initial implementation steps must include processes to characterize, analyze, and modify the facility systems essential for the protective response. Deployment of fast-acting detectors, probably in the air handlers initially, will provide triggers for environmental sample collection and perhaps other low-regret actions. Bioaerosol levels far above background might also provide a sufficient basis for higher-regret alarms. The foundation for defense against low-level and other sophisticated attacks will continue to be detect-to-treat sampling and laboratory analysis in this phase of deployment. A more complete understanding of background levels and variability and how they are affected by site-specific factors is essential for successful deployment of these nonspecific detection elements. More extensive analyses of the architectural concepts and the design bases for near-term systems are needed before commitment to widespread deployments.
-
Phase 2 priorities. The ability to confirm attacks at the facility rather than wait for the several hour (or longer) confirmation from an outside laboratory is an important augmentation of the initial deployment concept. If such confirmation can be achieved within 15-20 minutes, more significant HVAC and other responses can be taken to the nonspecific alarms since there is the capability to resolve the uncertain alarm and restore the facility to normal operations in a relatively short period
-
of time.
-
Phase 3 priorities. The ability to achieve rapid and sensitive identification of low agent concentrations is important for defense against low-level releases and other sophisticated attacks. In the most demanding of these scenarios, bioaerosol detectors may be of limited value, so initial alarms would need to be generated by continuously running identification detectors. It is expected that confirmation response times of 1 to 5 minutes will permit timely initiation of the complete response spectrum, minimizing the number of casualties. Somewhat longer response times (e.g., 5 to 10 minutes) might also be very useful in some facilities.
-
Phase 4 priorities. Extension of detection capabilities to permit low cost, specific detectors (biological smoke alarms) to be distributed throughout the facility will both improve system performance and make defensive systems affordable for a much broader range of facilities. The performance improvement results from placement of sensors closer to potential release points, causing a reduction in response time and enhanced ability to detect smaller attacks. The improvement in situation assessment afforded by integrating responses from a network of detectors may also be significant.
It is important to note that the committee addressed the full range of aerosol releases in both exterior and interior attacks in response to the guidance of the sponsor. The Phase 1 and Phase 2 systems provide for coverage against moderate to large-scale attacks, and the Phase 3 system extends the defense to small-scale releases and even trickle attacks within facilities. The effect of the diverse array of agents available to the attacker was also considered. Hence, the committee believes that a major portion of the threat space for aerosol attacks on fixed sites and enclosed facilities has been addressed. The high-level concepts of operation and examples included in the report provided a set of general insights that guided the technical consideration of detector performance, which was the primary focus of the committee's tasking. The capabilities of the proposed defensive architectures relative to variations in the specific attack characteristics (agent type, release size, release conditions) would require more detailed analysis of not only the detectors and their supporting systems but also the available operational responses and site-specific factors. While a more complete understanding of these sensitivities will be important in the engineering of defensive systems, the level of analysis pursued by the committee is seen as adequate to recommend technical development directions, as specified by the statement of task.
DISTRIBUTED TARGET DEFENSIVE ARCHITECTURES
Protection of distributed target complexes against biological attack is a high-priority goal for military planners. These targets include posts, air bases, and naval ports in the continental United States and abroad, airports and seaports of debarkation (A/SPODs), and deployed naval forces. This section addresses a military base containing both exposed personnel and facilities to represent this class of targets. Such bases are often surrounded by a buffer zone where physical security is tight. Outside that zone, an attacker has broad latitude to pursue either airborne or ground releases. Quite sophisticated attacks are assumed possible, including line releases of weaponized agent.
An attacker faces many decisions in the mounting of a line attack against a distributed target. One important decision is whether to generate the line release close to the target complex or further back from the secured area. The closest possible release that will allow cloud development will usually provide the most certain and efficient coverage of the target complex. More distant releases run the risk of misdirection and cloud breakup due to uncertain meteorological conditions with a resulting reduction of dose levels on the targeted site. However, under ideal conditions and with a sufficiently large release quantity, a more distant release could allow the cloud to expand, resulting in very long exposures at relatively low concentration levels as it passes over the target complex.
The size of a line release attack will depend upon the target elements that the attacker wishes to hold at risk. A minimal release might be sized to threaten primarily exposed personnel. However, since many personnel will be occupying base facilities, particularly in the early morning hours when
meteorological conditions are most favorable for the attacker, it would seem likely that the attack would be sized to yield high confidence infection of both exposed personnel and occupants of base facilities. In this case, the intensity of the attack would need to be sufficient to overcome any sheltering capability of the facilities. Smaller point releases that attempt to target a portion of the base or avoid detection assets are possible but run the risk that unpredictable meteorological conditions could alter the trajectory of the released cloud.
Detection Architecture Options
A detection system consisting of multistage spectroscopic point detectors deployed at the boundary of the buffer zone is assumed as the baseline defense. As in the case of facility defenses, the rapid, nonspecific element of the detection system can initiate identification processes and, if biological aerosol loading is far enough above background, higher impact responsive measures. For low-level attacks, rapid identification detection may be necessary to initiate response action. Attacks that employ broad, low concentration clouds make detection difficult for the defense. This case is analogous to the trickle release scenario against facility defenses.
Standoff detectors might be employed to detect the cloud as it approaches the boundaries of the buffer zone.11 Since standoff systems will have the capability of scanning the horizon, they can yield information on the structure of the approaching cloud that might help distinguish purposeful releases from natural phenomena.
Responses to detection of a threatening cloud could involve a range of actions. Some low-regret possibilities exist, particularly to improve the sheltering capabilities for base facilities in the path of the cloud. One might imagine a network that links base buildings and initiates operations to close outside openings and control internal airflows. Higher-regret measures might involve the use of personal protective gear for exposed personnel (and perhaps facility occupants as well) or sheltering strategies that move personnel to the least vulnerable nearby building. More effective responses can be incorporated into facilities to make them much less vulnerable to passing clouds if sufficient warning is available. For example, an independent air handling system using highly filtered air could establish positive pressure in the defended facility. Some of the facility defensive measures discussed in the previous section might apply here as well. For exposed personnel outdoors and away from the potential sheltering capabilities of nearby facilities, there are few low-regret response options in the absence of personal protective gear.
An example illustrating a nominal outdoor attack on a distributed target complex is described in the following section. The parameters are chosen to represent a sizable and sophisticated attack. A facility with characteristics similar to the one examined in the earlier example is used to illustrate the potential of protective, shelter-in-place strategies.
Example: Attack on an Extended Military Installation
An attack on a military base is assumed to be executed by a sophisticated adversary employing an aircraft flying upwind of the target and releasing dry, weaponized anthrax. The release is 4 km upwind of the perimeter of the base and utilizes 50 kg of anthrax (approximately one trillion times the LD50 of anthrax) dispersed 100 feet above the ground. Dispersal efficiency is assumed to be 20 percent. Very favorable meteorological conditions, including a 5 meter per second wind, result in a well-formed, uniform cloud being carried toward the target area. The concentration contours near ground level (1 meter) at the time the center of the cloud first reaches the defended perimeter (12 minutes following the start of the release) are shown in Figure 10.9. As the cloud passes over the target area, it creates a sizable zone (almost 35 km in depth) in which the probability of infection to exposed personnel is approximately 0.7.
|
11 |
Operational issues for standoff detection systems (for example, the extent to which UV lidar can be used effectively during daylight hours) are discussed in Chapter 5. |
This footprint is illustrated in Figure 10.10. The assumed line release is along the Y axis (X = 0 km) and extends for 10 km from Y = 0 to Y = 10 km. The cloud encounters the perimeter of the base at X = 4 km.
The agent concentrations at ground level as the cloud passes over the defended perimeter are low relative to those noted in the interior facility release. Current bioaerosol detectors using thresholds low enough to detect this attack would likely experience relatively high false alarm rates. Hence, any action initiated based solely on bioaerosol alarms would necessarily be low-regret. Networking of multiple detectors deployed in the defended area could reduce false alarm rates by providing additional alarms that could be assessed for consistency with possible release environments.
The potential benefits of standoff detection can be illustrated by considering the vertical contours of the cloud. These contours at the midpoint of the line release (Y = 5 km) are show in Figures 10.11 and 10.12 for 6 and 12 minutes following the release, respectively. The most generic benefit from a standoff system operating at the perimeter of the defended area
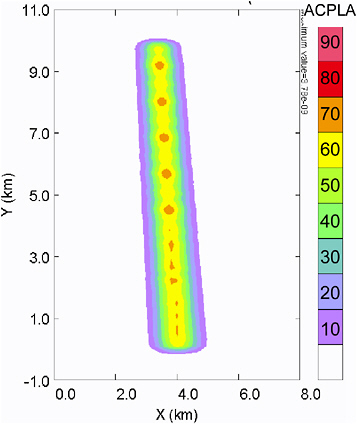
FIGURE 10.9 Agent concentrations at base perimeter.
is the increased time allowed for response to detection. At the 5 meter per second wind speed assumed in this example, each kilometer of standoff allows over 3 minutes of increased response time. The standoff detector also has a chance to exploit aspects of the release cloud that are denied the stationary spectroscopic point detector. For example, in the cloud described by Figures 10.9, 10.10, and 10.11, a standoff detector could presumably view the leading edge of the cloud, which lies well above ground
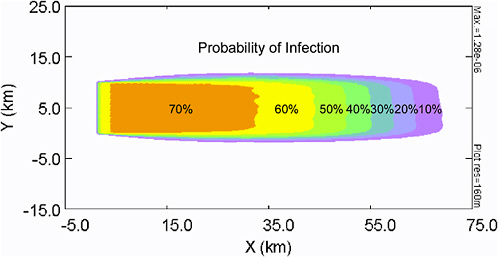
FIGURE 10.10 Infectivity contours for exposed, unprotected personnel.
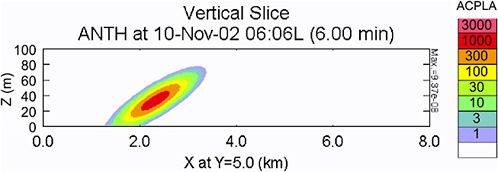
FIGURE 10.11 Concentration contours 6 minutes after the release.
level, to achieve even earlier warning. For clouds released near the perimeter, the standoff detection system might scan to detect the highest concentration level to differentiate an attack event from normal background. In the current example, the maximum concentration point does not occur at ground level where a stationary point sensor might measure it. Finally, a scanning standoff system might be able to recognize the uniform structure of a recently dispersed agent cloud.
Consideration of the protective effect of a building in the path of the cloud illustrates the importance of facility-related responses as an element of the defense against these attacks. A facility very much like the nominal office building examined in the previous section of this report is assumed placed within the defended area. The building has a filter efficiency of 98 percent and an air handler that produces 4 air changes per hour with 90 percent recirculation. (This is equivalent to 0.4 fresh air changes per hour and 3.6 recirculated air changes per hour.) The nominal infiltration rate is assumed to be 0.1 air changes per hour, which reflects, as discussed earlier, a well-isolated, modern building design.
For such a building operating in steady state (i.e., no airflow response to the attack), one can define a dose reduction factor that is the ratio of the dose a person inside the building would experience to the dose that an outdoor, unprotected person would be exposed to. Use of a simple single-compartment model of the building12 yields an estimate of 0.014 for the dose reduction factor in this case. This means
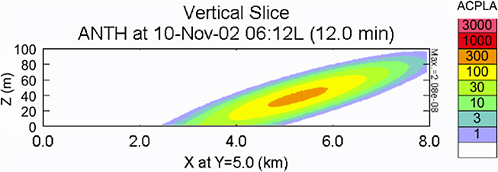
FIGURE 10.12 Concentration contours 12 minutes after the release.
that a person who stays inside the building will receive a total dose of 1.4 percent of the dose that would be received by a person standing outdoors through the passage of the cloud. The resulting infectivity contours for the current release scenario are shown in Figure 10.13. Even though the dose levels are reduced by almost two orders of magnitude, an infectivity level of 20 percent is predicted. Note that this is due to the relatively flat probit slope assumed for anthrax infection.
Greater protection of facility occupants might be achieved if certain low-regret facility options could be activated as the agent cloud approaches. Some improvement is possible by shutting down the air intakes for the HVAC systems. This is particularly the case if the systems are operating initially with a high fresh air fraction. However, the most effective approach would be to reduce the air infiltration into the building. This infiltration comes from a variety of sources including doors, windows, cracks, and other openings and is driven by a variety of means, including pressure-driven flows from the air handlers, external winds, and thermal effects.
Creation of a positive-pressure interior environment can reduce this infiltration to very low levels but requires a clean air supply and specialized air handler operations. In the absence of systems to reduce infiltration, some improvement in infectivity levels can be achieved by shutting down air intakes upon warning of agent cloud approach and moving building occupants outside after the cloud has passed. Figure 10.14 shows that the outdoor concentration level drops below the interior level about 15 minutes after the cloud first hits the building. The curves in Figure 10.15 compare infectivity levels for nonresponsive facility operations (infiltration = 0.4 ac/hr) with a strategy that includes initial closing of HVAC intakes (infiltration = 0.1 ac/hr) along with evacuation of occupants outdoors when concentrations drop below interior levels. The data shown indicate that the improvements resulting from this strategy are significant, particularly when the sheltering characteristics of the facility are good (i.e., a low infiltration rate). However, this strategy may be difficult to implement, since it requires the measurement and comparison of relatively low indoor and outdoor concentrations at the end of the attack.
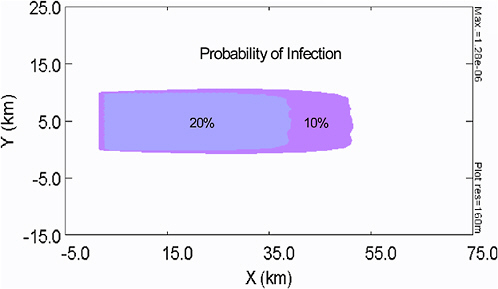
FIGURE 10.13 Infectivity contours for a building dose reduction factor of 0.014.
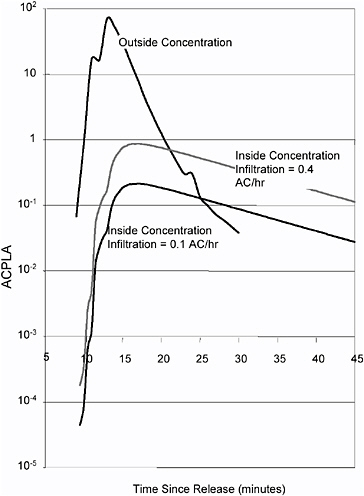
FIGURE 10.14 Outside and interior concentrations for targeted facility. This is the base case with no response.
While there is no sharp knee, or inflection point, in the curve, it is clear that 1- to 2-minute warning times provide significantly greater reduction in casualties than do 5- to 10-minute warning times. Therefore, a 1- to 2-minute warning has been the committee's focus. For nonspecific bioaerosol detectors, the committee believes this can be done with a reasonable signal-to-noise and hence low false alarm rate for moderate to large attacks on the facility, since the number of agent particles will far exceed ambient background particles. However, if a threshold for still smaller attacks is set, there will be more false positives if only a nonspecific detector is used. Therefore, the committee proposes adding a rapid identifier (2 minutes or less) to deal with the potential of smaller, or trickle, attacks while still providing a 2-minute or shorter warning for maximum casualty reduction.
Distributed Target Protection—Strategies and Priorities
Distributed target complexes, particularly military bases in the continental United States or abroad, are a high priority for implementation of biological defense systems. A strategy that implements near-term protection focused on detect-to-treat responses is already a part of the DoD chemical and biological defense program. Augmentation of these initiatives to add near-term detect-to-warn elements and broadening them to include a few key domestic complexes could be appropriate initial steps toward development of more widespread capabilities.
The philosophy underlying this strategy is similar to that recommended for facility protection. Available bioaerosol detectors deployed as close as possible to the release point can trigger identification detectors and might initiate other response actions for very large attacks that increase bioaerosol levels well above background. This triggering function is already employed in existing military systems to initiate agent identification. Exploitation of these same nonspecific detections, particularly in initiation of low-regret facility responses, could yield significant protective benefits. The capability of facilities to provide intrinsic protection, and even greater isolation if active air handling and isolation responses are employed, should be an important defensive consideration in these types of scenarios. The potential for standoff detection of higher-level releases also deserves examination as an independent source of early information on an approaching agent cloud. As was the case for facility protection, effective defense for the broad range of scenarios will require rapid, sensitive identification detectors for low-level attacks. These considerations lead to a phased R&D and deployment strategy. Priorities associated with the key elements of this strategy are outlined below.
Phase 1 Priorities
The use of bioaerosol detectors at the perimeter of the defended area to trigger confirmation of the attack and perhaps to initiate low-regret responses for high-intensity clouds provides a basis for initial detect-to-warn capabilities. However, development of protective response options may be equally important. For early deployments, this will likely involve improvements in facilities in the defended area to increase their effectiveness as shelters against the passing cloud. Some of these measures will also assist in the protection of the facilities against interior or air intake attacks. For critical military sites, attack confirmation may be accomplished in a 25-30 minute window using current multistage detection systems (e.g., JBPDS). Less critical military or domestic targets could employ collected samples processed in a remote lab for attack confirmation. This slower confirmation cycle could limit the intensity of the initial responses to bioaerosol detection alarms. A more thorough examination of defensive architecture trade-offs and concepts of operation are required for these architectures, partly because of the greater detection ambiguity expected for low-threshold bioaerosol alarms in outdoor scenarios.
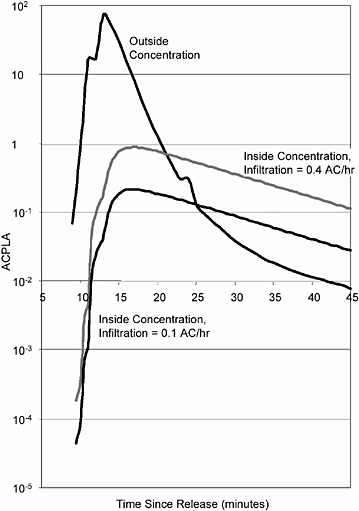
FIGURE 10.15 Probability of infection of facility occupants for responsive and baseline cases; ac/hr is air changes per hour.
Phase 2 Priorities
The improvement of standoff detection technologies may offer significant enhancements in the nonspecific detection of approaching clouds. Further investigation and development of a concept of operations that would allow exploitation of both concentration and cloud structure information are needed.
Phase 3 Priorities
Full detect-to-warn capabilities against low-level attacks will require rapid, continuously operating, sensitive identification and confirmation detectors similar to those targeted in the third phase of the facility protection strategy. However, in the case of distributed complexes, the time lines available for the corresponding functions are somewhat relaxed due to the transit time of the cloud from the perimeter of the defended area to key target elements of concern.
FINDINGS AND RECOMMENDATIONS
The committee's specific findings and recommendations for detect-to-warn defenses of facilities and distributed military installations are detailed below.
Defense of Facilities
Facility protection systems appear to offer opportunities for the application of both near-term and emerging detection technologies to achieve significant protection against biological attacks. The principal findings and recommendations in this area are as follows:
Finding 10-1: For rapid releases of biological agents into facilities, nonspecific bioaerosol detectors may offer reliable warning with relatively low false alarm rates in many attack scenarios of interest. Such unambiguous detection can occur when agent concentration well above background levels is created in the area of the release.
Recommendation 10-1: Nonspecific, bioaerosol detectors should be deployed in a diverse set of facilities to understand the performance of these detectors in interior spaces. The frequency and cause of false alarms should be investigated. Concurrent data on biological backgrounds in the facilities should be acquired to provide a basis for the assessment of long-term performance and design of robust defensive systems.
Finding 10-2: More sensitive and specific identification detectors have a role in facility defense architectures. They provide on-site confirmation of nonspecific alarms via a separate and independent detection technology. They can also provide the added sensitivity needed for detection of extended duration, low-level, interior releases. Response times on the order of 1 minute are highly desirable, although benefits may accrue to somewhat slower detectors in some scenarios.
Recommendation 10-2: Research should be continued in the most promising detection technologies that offer promise of rapid, specific identifiers. Perform a more complete analysis of representative scenarios and facilities to characterize the dependence of overall defensive system effectiveness on sensor response times.
Finding 10-3: In the longer term, widespread deployment of a network of low-cost, reliable detectors (biological smoke alarms) within a facility offers important advantages, including rapid response to releases and lower false alarm rates.
Recommendation 10-3: Research should continue to identify promising concepts for very low cost distributed detectors.
Finding 10-4: The ability to isolate HVAC zones, the quality of building filters, and other operational factors that determine airflows within a facility are critical determinants of inherent vulnerability and the ability to respond to warning of an attack. These features are highly site-specific and, in general, must be characterized empirically. Some facilities may require upgrades in airflow control and other response options before active defense can be implemented effectively.
Recommendation 10-4: Methodologies for analyzing facility vulnerabilities and characterizing airflow control and other responsive options should be developed.
Finding 10-5: Improvements in passive protection features of a facility (e.g., isolation of air handling zones, upgrading of filters) can reduce vulnerabilities and must be balanced against investment in active defenses. Design of a balanced detect-to-warn architecture is a complex systems engineering task.
Recommendation 10-5: Design studies leading to a methodology and criteria to guide facility investments in active and passive defenses should be pursued. A dialogue concerning appropriate baseline threat and protection levels should begin as a part of national homeland security initiatives.
Finding 10-6: Many facility design features that offer the potential for the most effective defensive responses can best be incorporated early in the planning process for new facilities.
Recommendation 10-6: Programs should be initiated that will modify architectural standards to incorporate the benefits of reduced vulnerability to biological attack as an integral part of the design process for new facilities.
Defense of Distributed Military Installations
Defense of distributed target complexes (e.g., military installations) against outdoor attacks can be addressed using some of the same principles that were applied to facilities. The task is made more difficult, however, by a more demanding detection environment and by the absence of effective low-regret response options, particularly for exposed personnel. Several specific findings and recommendations that apply to this scenario follow:
Finding 10-7: For outdoors releases, agent concentrations relative to backgrounds are often much lower than in facility scenarios. This reduces the ability of nonspecific, bioaerosol detectors to initiate responses and increases the importance of rapid (i.e., 1- to 5-minute), continuously running identification technologies. Such specific identifiers are likely to be required for all but the largest of outdoor releases.
Recommendation 10-7: Rapid, specific detection technology should be pursued as a baseline for outdoor detect-to-warn defenses.
Finding 10-8: Standoff detection systems, if effective, could significantly enhance installation defense architectures through their ability to provide earlier warning, to sense areas of highest agent concentration, and to characterize spatial features of the threat cloud.
Recommendation 10-8: A concept of operations for standoff detectors should be pursued that integrates realistic standoff data with other detectors and an installation defensive system.
Finding 10-9: The use of installation buildings in a sheltering and isolation role may provide the most effective means to respond to attacks on military bases and similar target complexes.
Recommendation 10-9: Cost-effective response options for improving the shelter-in-place capabilities of installation buildings should be explored, including cutoffs for air handling system intakes; reduction in the infiltration rate of outside air; and separate, highly filtered air supply systems.
General Recommendations
Two additional areas that were found to impact all defensive architectures were deemed noteworthy. Specific findings and recommendations in these areas are as follows:
Finding 10-10: The characteristics of biological aerosol backgrounds have a critical impact on the performance of detection systems, particularly those that employ nonspecific detectors for response initiation.
Recommendation 10-10: A more comprehensive program to characterize backgrounds in both interior and exterior environments should be initiated. This program should be conducted in conjunction with deployments of detectors in order to link background features to false alarm characteristics of candidate detection systems.
Finding 10-11: Achievement of very good performance in detect-to-warn systems (i.e., with less than 10 percent infectivity) can be a particularly demanding challenge. With current probit curve models of infection, very low concentrations of agent are required to achieve such a low level of infectivity.
Recommendation 10-11: The validity of widely used infectivity models should be reviewed before applying those models to generate defense system requirements.























