2
Systems Approach to Security at Civilian Nuclear Facilities
Key Issues
The key issues noted here are some of those raised by individual workshop participants, and do not in any way indicate consensus of workshop participants overall.
• Weapons-usable material must be kept out of the hands of adversaries who may be trying to get their hands on this material and could use it for malevolent actions.
• No material is absolutely safe, and any material is vulnerable at some level.
• Nuclear security is a continuous, dynamic risk management job and requires constant and vigorous efforts.
• Program resources were to be used for both safety and security. The balance of risk and security as well as the balance of resources needs to be maintained to not undermine employees’ interest in maintaining high-quality science as well as a vigilance of safety and security measures.
• In India, the primary security concern at civilian nuclear facilities is sabotage.
• Several safety features can be incorporated into reactors, which also aid security.
• Material categorization is also essential to the security design process because there is a direct relationship between the protection required and the quantity of the material and its enrichment level.
• Apart from resource extension, the closed fuel cycle can be designed to be more proliferation resistant.
Promising Topics for Collaboration Arising from the Presentations and Discussions
These promising topics for collaboration arising from the presentations and discussions do not necessarily represent the consensus of the participants, but are rather a selection of the topics offered by individual participants throughout the presentations and discussions.
• There is little sharing of experience among experts working in fuel cycle facilities in some countries, which indicates that there is opportunity for communication in this area.
• Due to the high consequence to the public if a malevolent act were to occur, proper protection planning, design, and implementation approaches are well documented and shared within the global security community. However, thus far Indian and American experts have not had an opportunity to fully exchange experiences, therefore more such opportunities should be sought bilaterally and within the broader security community. This offers the opportunity for more Indian-U.S. exchange.
• The problem of how to assess quantitatively the probability (frequency) of attack in the security and safeguards areas may be one possible joint research project.
• Commonality in the measure of consequences across safety, security, and safeguards is a possible area of joint cooperation.
• At many nuclear installations there is a need to augment communication resources for purposes of both security and safeguards.
• Consequence management training tools, such as the development of a plume simulator for handheld instruments, could be another area of cooperation.
• Exchange programs for students would be beneficial for both countries.
Overview of Civilian Nuclear Security: A Systems Approach
Robert Kuckuck drew upon his experience as a former director of a nuclear facility and a principal deputy director of the National Nuclear Security Administration to provide his views on security for civilian nuclear facilities from a systems perspective. This perspective begins, he stated, with a global system and continues to the local, facility system. The global system involves policies and agreements; the domestic system also involves policies, enforcement, and oversight. Operational facility systems are embedded systems that involve the actual handling of materials and the actual implementation of nuclear security features.
Nuclear security systems from a facility and operational perspective have always had two principles for Kuckuck. The first principle is that weapons-usable material must be kept out of the hands of adversaries, and that adversaries are indeed trying to get their hands on this material and could use it for malevolent purposes. Responsibility for protecting the mateiral is the utmost priority.
Even though there has been a tremendous global effort over many years, there still are no agreed upon standards around the world for protecting nuclear material. Any individual state is only as safe or protected as the weakest link in the entire international system. A systems approach is very much needed on a global level. Kuckuck noted that dialogue among scientists is an important first step, and many, many more steps between India and the United States are needed. Scientists start with facts that are well understood on each side, and can make progress in forming understanding relationships and developing a path to the future.
Kuckuck’s second guiding principle throughout his career was that no material is absolutely safe, and any material is vulnerable at some level. Therefore, the task of nuclear security at the level of facility operations has always been one of risk management. How does one assess the quality and quantity of the material at the facility, and how does one assess the attractiveness value of that material to an adversary? What security measures are in place to protect that material? And what is the understanding and best estimate of the capabilities that an adversary can bring to bear against the facilities and operations? It is the balance of those factors, the risk management, that constitutes the nuclear security system at a facility-operations level.
All of these factors are dynamic, continually changing and uncertain. The capabilities of security measures change. The perception of the adversaries’ capabilities changes. The public’s perception of security measures and the adversary’s capabilities are every bit as important as the facility director’s understanding of the facility in real time. These are very real concerns to a facility manager, and particularly to a government official. This continuous, dynamic risk management job, which is what Kuckuck calls nuclear security, requires constant and vigorous efforts.
With these two principles, the facility director concludes that he or she always has to have his or her eyes open and mind active to decide if the balance of risk is appropriate.
To Kuckuck, the most important and fundamental element of facility security is the people. The security culture of the facility is critical to the effectiveness of the facility’s security system. A facility’s management has to convey and communicate a need for the security measures in place, “not just walk the walk and not just talk the talk, but to walk the talk.” Management has to act in support of those principles at all times with an organization structured with clear motivations, incentives, roles, responsibilities, accountabilities, authorities. Every person must be trained to know why they, and management, are taking these measures. The people must have the authority and the capability to do their jobs,
including the resources they need. If any of those conditions are violated, management loses an employee’s support; his heart is no longer in tune with the principles and this starts to weaken security culture. As a facility director, Kuckuck always felt that one of his biggest jobs was to maintain and sustain that security culture at his facility. Every person, from a custodian to a technician to a scientist to the protective force guards, needed to believe in and support the nuclear security program. That is what Kuckuck calls nuclear security culture.
There are many other elements in the nuclear security program at a facility with attractive nuclear material, be it a reactor, a materials processing facility, or a storage facility. Kuckuck began by asking himself if the facility was robust. Can the facility process the material, handle it, store it, take care of it?
The second element was how much material was at the facility and how should it be controlled and kept track of? How does the facility director know at every minute whether the material is still there? How does the director know that something hasn’t gone wrong and that nothing was missed or that material has not gone missing? To answer these questions, Kuckuck employed material control and accountability.
Next, he asked, “How do I control people’s access to the material?” The answer was to put up barriers. In the United States, facilities commonly have several concentric barriers of increasing magnitude. Outside barriers may not even be alarmed, merely patrolled. As one moves inward, toward the material, the barriers become much more robust. They are alarmed and are constantly monitored. This layered system is called a graded approach.
As one moves in, one reaches a hardened facility with even stronger barriers. At this level, access is controlled for each person. Each person’s motive and authorization for being in that zone is diligently investigated and understood. Each person is given credentials, which are the only way that he or she can access the secure zone. In some cases, individuals are allowed access, but must be accompanied by more than one person, use more than one key, and use more than one control system.
Now that the facility has the material controlled inside, and has only granted access to the right good guys (and there are lots of other good guys that are not granted access), how does the facility keep the bad guys out? This begins with surveillance. Barriers are monitored constantly, as are alarms. Protective forces are engaged and conduct patrols, and the like.
If an alarm signals or if there is some indication of a penetration of a barrier, or an attempted penetration, facility personnel, especially the protective force must be prepared to respond immediately. In some cases, additional barriers go into place automatically. Communication occurs across the entire facility so that everyone knows that there is an issue, prompting them to lock up their own material or do whatever is appropriate in their position. The protective force has an even more thorough communication system so that they know exactly what is happening at any point in time and can adjust their reactions accordingly. Finally, a pursuit and recovery operation is undertaken to either contain the intruders and/or recover the material. If needed, each facility has
very prescribed ways in which the protective force reaches out to supplemental forces such as the local police, the military, etc. As a facility director, this was the system that Kuckuck always had in his mind as he reviewed security.
However, he observed that there are at least three very important elements that underpinned this sequence of protections just outlined. The biggest one is the human aspect of nuclear materials security. Every person who is involved with the material system at any level is completely vetted with background investigations. This occurs every five years at a minimum. Employees are not vetted by the facility or by the director, they are vetted by an independent government authority so that there is no chance for conflict of interest by the director thinking he needs a particular individual and maybe does not do the investigation diligently.
Training is required in every aspect that is relevant to protecting the material during handling, storage, and so forth. Fitness for duty, which is different from training, is a daily inspection done in various ways. For example, for the protective forces, the supervisor of a small group on each shift does various tests or interrogations to make sure that every member of his team is fit for duty that day, is not sick, or does not have some other issue that may prevent him from doing what he needs to do.
Technology supports all of this, whether it be offensive or defensive weapons or alarms or capabilities. A major aspect of this technology is cybersecurity, both in the control and communications of the facility. Forensics also plays an important role in deterrence and resolution should an incident occur. One hopes that an adversary is deterred by the concern that he will be caught and brought to justice.
Finally, another underlying technology is just information security in general. Across the whole facility, how does the facility protect information that pertains to the classification of material, the location of the material, and how the material is protected. How is the information protected once it is classified? These are underpinning technologies, or underpinning elements, that are fundamental to the system of nuclear security at any facility.
Kuckuck then shared issues that arose during his time as a director of a facility and as a government official overseeing these facilities. One of the biggest difficulties as a director of a facility with nuclear operations was sustaining the nuclear culture. It is a constant task and there are many realities that try to undermine that culture. One is just plain complacency: years go by and no intruders come through the fence and there are no issues. If we lose the hearts and minds of the facility employees regarding the need for security, then they start doing that risk balance on their own. They start deciding that they do not really have to do a lock up or take a compensatory measure because it is not necessary. It is very important to not allow the security system to get into the position of being judged by the employees in a critial way that allows them to make their own risk balance. Complacency is a very serious issue.
Resources are another important issue. As a director, there is a constant balance required between using resources for the mission with the material and the security required to protect that material. That balance can be off in either
direction. Some people will argue that one cannot have too much security. But Kuckuck believes one can have too much of the wrong kind of security. This applies to safety as well. There may be multiple requirements for bureaucratic accounting of things that make no real contribution to safety and this begins to undermine the safety culture itself because employees become disgruntled and they do not follow the safety rules or they fake it or they just do not take it seriously.
The same thing happens with security, therefore it is important to maintain the balance of security requirements and actual risk. This requires the development of a design basis threat (DBT), which is established by government oversight organizations. Specifically, they define the threat that the facility has to use as the basis from which to build its nuclear security. The DBT is derived by using intelligence, understanding of an adversary’s past actions, and other input.
Kuckuck explained, however, that there is a cycle to DBTs. A force-onforce exercise, bringing in so-called armed adversaries to attack the laboratory, would be conducted to determine whether the security system could meet the DBT. If the laboratory forces defended every time successfully, the people that designed the threat felt that maybe they needed to escalate the threat a bit. They wondered where failure would occur: perhaps if the adversary had one more machine gun? Therefore, the laboratory would test beyond the DBT, and test to failure. Invariably, however, that would become the new DBT. This created periods where the DBT was totally out of alignment with realistic threats from an adversary. When that happened, people would start to lose adherence to the security system. They knew the threat was not realistic, they were bitter, and they made their own judgements. The situation also could go the other way. Program resources were to be used for both safety and security. The complacency factor would enter and resources for security would be cut. As stated earlier, the balance of risk and security as well as the balance of resources needed to be maintained to not undermine employees.
The second issue is very difficult. Kuckuck explained that in the United States, facilities are not guarded by the military, they are guarded by security companies or employees of the facility. These people must be trained. Most guard forces are recruited from among soldiers returning from Iraq or Afganistan. But they come home and complain that after a little while, they feel like night watchmen although they are expected to be soldiers, to train like soldiers, and to do combat exercises. They drive a car around all evening and nothing ever happens. It is very difficult for them to adjust to that, it is very difficult to keep them alert. There have been incidents when guards missed obvious events that were not even an exercise, someone trying to cut through a fence, for example.
Another significant problem is the degree to which the exercises are realistic. During a major exercise at a laboratory, there is a full security force on site right then that are not playing in the exercise—they are protecting the facility. There is another shift that is going to be exercised that night and they all
have yellow vests on and are using laser guns to shoot each other in the vest. There is a vast number of people out here in the yards: some are umpires, some are judges, some are observers, some are guys with vests who are playing, and some are guards that are ignoring them. It is very hard to have a realistic exercise of troops. Kuckuck has always worried about that problem.
Recently there was a situation in the United States, Kuckuck recounted, that raises a question about threats. An 82 year old nun and a couple of other gentlemen cut through the fence and entered a facility. In analyzing that incident, many of these factors came into play. They never actually got near the material and there was never a real threat, but there were a lot of lessons to be learned from how this happened.
Regarding accountability, as a facililty director, Kuckuck found it very difficult to explain to the public in the United States why the fact that kilograms of highly enriched uranium (HEU) or platonium would go “missing” every year is considered unclassified information. The material was held up in the pipes, or otherwise unaccounted for (see Santi’s talk). The argument of course, is there are ways that one can eventually account for that material by decontamination. This was a very difficult public relations issue.
Kuckuck concluded by asking “Are we using technology to our fullest extent?” He answered, “we know we are not.” There are more aggressive deterrence capabilities that could be automatically activated when someone came through a fence, but this may lead to an accidental killing, which underscores the need to balance safety and security. Are there other technologies not being used to either inhibit the intruder or to devalue the target they are coming after? Is there artificial intelligence that the guards can use to help them in their boredom so that they don’t miss something on the camera?
NUCLEAR MATERIALS SECURITY AT CIVILIAN REACTOR FACILITIES
Indian Perspective
Ranjit Kumar shared his experience working with civilian nuclear facilities in India and the associated issues of nuclear materials security that he has encountered. He began by noting that in addition to pressurized heavy-water reactors, which have been the mainstay of the India nuclear power program in the first stage of its development, India has developed advanced heavy-water reactors, which are based on low enriched uranium and thorium with several improved safety and nonproliferation or proliferation-resistant features. India also has a program on fast breeder-type reactors, with a research reactor now running for nearly 30 years. Also, India’s prototype fast breeder reactor will be ready in a couple of years.
India has various types of nuclear facilities encompassing the entire nuclear fuel cycle, starting from mining to power production and other uses of
nuclear radiation sources, to waste disposal. India has both back-end and front-end fuel cycle facilities in the civilian domain.
India is poised for extensive growth, including potentially the use of many more nuclear power reactors in the country. As nuclear power reactor deployment increases, there will be increased requirements of fuel fabrication and other fuel cycle services. Non-power applications of radiation are also growing across India, particularly in industrial and agricultural applications. There are large programs that have made a contribution to the overall economy of the country.
Regarding security at civilian nuclear facilities, the primary concern is sabotage. There have been several terrorist incidents that cause concern about potential sabotage attempts on a nuclear power plant, other civilian nuclear facilities, or any nuclear facility. These concerns have led experts in India to look deeply at the security of these facilities including various analyses right after the attacks of September 11, 2001. A review committee was established to look into security. Subsequently, regulations were developed and a great deal of oversight, audits, and reviews have taken place. Immediate measures have been undertaken and long-term goals have also been developed. Several design-related measures have been introduced in order to prevent and protect the nuclear facilities against sabotage attempts.
Although sabotage is the primary threat, theft is also a concern, not as much for nuclear power projects or nuclear power facilities or power reactors and research reactors, but rather for other facilities such as fuel fabrication facilities. Facilities such as reprocessing facilities have both sabotage and theft threats. As an end product, reprocessed material may be a theft target.
Kumar provided some examples of nuclear facilities and comments on their potential as sabotage targets:
• Nuclear power plants:
![]() core damage or containment failure, which can lead to radioactive release
core damage or containment failure, which can lead to radioactive release
![]() spent fuel storage: pool could be drained and lead to radioactive release
spent fuel storage: pool could be drained and lead to radioactive release
• Research reactors:
![]() target depending on the type of reactor
target depending on the type of reactor
• Fuel fabrication facility:
![]() not a primary sabotage target, but could be even though it will not cause consequences as severe as a sabotage attack on a facility with radiological materials or a reactor facility
not a primary sabotage target, but could be even though it will not cause consequences as severe as a sabotage attack on a facility with radiological materials or a reactor facility
![]() end product can be utilized to cause a disruption as well as to contaminate an area
end product can be utilized to cause a disruption as well as to contaminate an area
• Enrichment, conversion, and storage facilities
![]() spent fuel reprocessing facilities and waste disposal facilities are of greater concern
spent fuel reprocessing facilities and waste disposal facilities are of greater concern
![]() in a waste disposal facility, there is a heavy concentration of materials that may present a potential sabotage target
in a waste disposal facility, there is a heavy concentration of materials that may present a potential sabotage target
Based on International Atomic Energy Agency (IAEA) data, there have been attacks on facilities, and in many cases the aim has been sabotage. In some cases, theft was the motive. Kumar noted that India wants to avoid such incidents.
Attacks can take place in three major ways: stealth, deceit, and force. Physical protection systems should address all three methods of attack. That said, Kumar noted that civilian nuclear facilities, particularly reactors, are difficult targets for sabotage. There are several safety features incorporated into the design of the reactor itself. Specifically, he referenced several fundamental principles of design safety:
• Redundancy: ensure that safety does not depend on any single system functioning correctly
• Reliability: design to numerical reliability targets (999/1,000)
• Testability: ensure systems are testable to demonstrate their reliability
• Independence: ensure systems that perform the same safety function are independent
• Separation: ensure systems that perform the same safety function are spatially separated
• Diversity: ensure, where possible, that systems which perform the same safety functions are of dissimilar design
• Defence-in-Depth: multiple barriers and systems
• Fail safe: ensure system/component fails safe if practical
Kumar elaborated on the principle of “diversity.” For example, in a nuclear power plant shutdown system, there are diverse mechanisms or diverse methodologies used for this purpose alone, such as a cooling rod, which uses a neutron-absorbing material like cadmium. There are others, like injection of neutron poison into the coolant. Several such diverse mechanisms are utilized for safety purposes in order to address that single failure and ensure that the plant remains safe.
Many of these safety features also aid security in diverse ways. For example, to release radioactivity from a fuel core in a pressurized heavy water reactor the radioactive material would have to breach the fuel cladding to enter the coolant tube and then to the reactor calandria vessel, to the biological shield, which contains the leak. This all makes the reactor a hard target for sabotage, although the risk cannot be entirely eliminated. Risk can never be 100-percent eliminated.
New, evolutionary reactor designs are bringing security into the design drawing room itself to attempt to incorporate security features, which will aid security directly. This is known as security by design. This process begins with siting and continues to the design of the containment facility, and throughout the entire process. When considering security measures themselves, if they are incorporated into the design phase, they are significantly more cost effective than attempts to retrofit a facility. At times, certain security measures are impossible to retrofit.
The Indian nuclear power program is guided by certain regulatory prerequisites overseen by the Atomic Energy Regulatory Board (AERB). The AERB is responsible for oversight, as well as for all aspects of review and audit of plants already in operation and those in the design phase. Each plant design is reviewed for its applicability, maintainability, and upgradability, particularly if it is an existing operating nuclear power plant. These designs should be consistent with national and international guidelines, standards, conventions, and treaties. Kumar noted that India follows certain international guidelines, particularly those stipulated by the IAEA and other regulatory bodies. Experts in India try to understand the requirements and to compare and adopt similar policies as well as design philosophies most suitable for India.
The main elements of security at nuclear facilities include security organizations with a well-defined allocation of responsibilities, duties and reporting lines, and well-coordinated with state agencies. The following questions are answered by these organizations: What is the responsibility of the guard force? What is the responsibility of the security manager or the chief security officer? Whom should this person contact in local law enforcement agencies?
The next element of security is the engineering system for physical protection. This includes hardware systems such as fences and barriers, detection and alarm devices, access control and surveillance, and guards. The physical protection system is designed based on the performance of the guard forces and the design basis threat (DBT). These aspects of physical security all interact. Kumar noted that they are trying to analyze response times and appropriate response forces against the DBT. Contingency and emergency plans are also designed for both security and safety. This is a systems engineering approach that can be utilized for the physical protection of any critical infrastructure facility.
This process starts with the required analysis stage even before the design of the reactor, during which the target is identified in vital areas. This vital area identification is a separate process in itself because it is essential to determine protection equipment needs, with particular attention to the threat of sabotage. A detailed methodology is followed in this process to determine a minimum set of locations and equipment needed to provide full protection against sabotage and the release of radioactive materials. In particular, during the identification of vital areas, two sabotage scenarios are considered. The first scenario is a “direct” scenario during which adversaries sabotage the material itself (e.g., using explosives) with the aim of causing radioactive dispersal. In such a scenario, an adversary would use some explosives. The second scenario is an indirect one during which a safety system would be attacked causing the dispersal of material. Kumar stated that this is called an event of “malevolent origin” and the security systems—through the DBT—are designed to prevent such events, again, starting with the vital area identification process.
Material categorization is also essential to this security design process because there is a direct relationship between the quantity of the material and its
enrichment level with regard to vital area identification, although categorization of material does not factor in with sabotage threats. Kumar stated that there is an effort in India to categorize nuclear facilities from the point of view of radiological sabotage but it has not yet been established. There are efforts to define criterion for what is called an “unacceptable radiological consequence” (URC). Each state in India is to define what an URC would be and based on that definition, the vital areas to be protected would be defined. However, the physical security at a nuclear facility should protect against any sabotage scenario even those exceeding the URC criterion.
A design for these scenarios would follow the same principles of detection, delay, and response, which are interlinked. Until the detection takes place, there is no value of a delay. This systems engineering methodology brings in two competing timelines. One is called the physical protection system timeline and the other is the adversary timeline. In order for the adversary to be successful, he has to complete his task before the physical protection system (PPS) delay time. If the task completion time by the adversary is more than the PPS response time, then the security system is successful. To establish these timelines, the first step is identification of the critical detection point, and a definition of the role of early detection.
The security elements of detection, delay, response, and access control are the same for a nuclear facility as well as for nuclear materials. A good security design should include:
• balanced protection: the front end and the back end of a facility should be protected equally
• protection in-depth: layered protection measures, not only physical measures, should be applied
• reliability: the instruments and systems should be reliable
• information security: should not be neglected
• confidentiality: physical protection systems should be kept confidential to maintain the reliability of the system
• consideration of operational needs: security systems should not interfere with the operation of a facility
There is considerable interaction between safety and security systems and at times, they have contradictory requirements. Such contradictions should not be allowed in the case of security. To address these issues, dialogue is needed between safety and security requirements.
Indian nuclear power plants, from the inside out, have four layers of protection, starting with the operating island. There is a double fence around the inner and the vital areas. This is called the protected area. Then there is the main plant boundary, the outermost layer is known as the exclusion zone boundary, the second layer is the main plant boundary, which is 500 meters from the operating island. Third is the operating island, which is declared as a protected
area. Fourth is the vital inner area, where the target for the sabotage or theft is located. They have their own required security measures.
In the exclusion zone boundary, there are manual measures for detection and assessment, such as patrols. In the main plant boundary, there are manual, and in some cases automatic, measures. In the operating island, there is a complete automatic perimeter intrusion detection and assessment system. In the vital area and the inner areas, there are automatic systems for intrusion detection.
Access control is done in a similar graded manner. In the exclusion zone boundary, this is done manually. In the main plant boundary, this is done automatically, with RFID smartcards. In the operating island, there are RFID cards plus biometrics. In the vital areas, there are automatic RFIDs plus biometrics in some cases. The physical protection system is integrated, and includes a central alarm station, located inside the protected area, that monitors all activity. This area has access control measures. Perimeter intrusion detection measures include frisking and checking in at the main plant boundary. There are also measures against forced entry of vehicles and civilians. Kumar stressed that all of these systems were developed indigenously, originating either at Bhabha Atomic Research Centre (BARC), Electronics Corporation of India Limited, or other similar organizations.
Again, while there is a synergy between safety and security systems, security is governed mainly by the Central Industrial Security Force and local police, particularly the response forces. However, safety is governed by the facility operator, the Nuclear Power Corporation of India Limited or Heavy-Water Board, depending on the type of facility. This system is quite mature, Kumar noted, whereas the security aspect, including the regulatory aspect of security, requires more time to evolve.
Since at times safety and security measures aid each other and at times they contradict each other, appropriate attention should be given to this balance. Both nuclear safety and security have the same aim: protecting the public and the environment from harmful effects of radiation. They also share a common regulatory approach by the same regulatory body. There should be synergy between safety and security. Addressing the need of the one by the other and understanding the requirements of security by safety and plant operation is important.
Regarding the regulatory framework, all nuclear power plants and civilian nuclear facilities are governed by AERB. At the design stage for new plants, there are several guidelines for systems design, inspection, and event reporting. This process is broken into stages and is followed as the plant develops. Quality assurance for equipment and systems is the responsibility of the operator. They are periodically reviewed and audited, including the response aspect. Several aspects of physical protection for civilian nuclear facilities are audited and reviewed by AERB regulations.
The right mix of hardware, security personnel, and procedures have to be utilized for effective physical protection of nuclear facilities. Kumar stressed that
several of the technologies used in India are developed in-house, but standardizastandardization remains one of the requirements. The best available sustainable techniques and instruments should be used on a long-term basis because it is not possible to change frequently. Also, there is a requirement to connect with local agencies for additional support in an emergency. This is vital, particularly when off-site emergencies arise. Likewise, appropriate quality-assurance and emergency plans must be deployed and practiced. Kumar assured workshop participants that India’s nuclear power plants deploy some of the most modern security systems and equipment. Good procedures are also practiced, reviewed, and audited. Often licensing is completed based on the security review and auditing. In closing, Kumar stated that it is also important today to include the neighborhood in the effective implementation of effective nuclear security.
U.S. Perspective
Michael Browne began by stating that his presentation would address nuclear material accountancy and physical protection, as well as focus on how the aspects of material accountancy in particular are applied to heavy-water reactors (CANDU facilities), including how standard measures are employed to achieve material accountancy. Browne also referred to supplemental measures that can be employed at reactors to gain confidence in the results from the accountancy systems. He concluded his presentation with a case study of the application of accountancy systems specifically to a sodium-cooled fast reactor to improve or enhance nuclear security.
The ultimate goal of nuclear security is to protect the public. Browne said that there are two ways to do this: protect against the malicious use of the nuclear material, and prevent the sabotage of nuclear facilities. At reactor facilities, nuclear security is implemented by using physical protections to control access, limiting access to those people who have a need to access the reactors, and the nuclear material accountancy system to keep track of the material and detect theft and potential misuse of the material.
Accountancy systems are typically developed based on the type of facility and should employ a risk-based approach, Browne argued. Because different types of reactors have different types and quantities of materials, different inherent accessibility, different operations, and different regulatory requirements, they require different accountancy systems. The tools may be the same, but the way that the tools are applied may be different.
Principles Associated With Material Accountancy
The most important principle, the backbone, is the accounting system itself. The accounting system can be viewed as the medium used to keep track of inventory. There is a wide range of systems, from handwritten notes in a ledger, to an electronic spreadsheet, to a fully interactive electronic database that tracks nuclear material in real or near real time, such as the system used in the facilities
in the United States, the Local Area Network Material Accounting System.
That accounting system typically utilizes material balance areas and key measurement points, MBAs and KMPs, as sources of information. For reactors, MBAs are the places where nuclear material is either used or stored. Key measurement points are used to determine the inventory in MBAs. For a nuclear power plant, a key measurement point might be a neutron monitor that is used to verify that a particular item is still in a storage configuration. It may be a gamma detector, which is used to confirm that a particular item has moved from one material balance area to another material balance area. Accounting may require actual material balance or an item count (e.g., number of fuel assemblies). In reactor facilities, item counts are typically used because the material does not change form. One knows the enrichment level of the fuel coming into a facility and the changes that occur in the reactor can be inferred from the operating parameters of the reactor. When it is ultimately discharged as spent fuel, the basic block, which is the assembly, has not changed, therefore item counting can be employed for accounting.
Application of Material Accountancy to CANDU Reactors
Browne then applied this concept of material accountancy, MBAs and KMPs, to a CANDU reactor to illustrate how this case differs from a more complicated one discussed later in the presentation.
For a CANDU facility, there are essentially three material balance areas: the fresh fuel area, the reactor itself, and the spent fuel storage pool. There are two types of key measurement points associated with those areas: KMPs for inventory and KMPs for flow. The distinction between them is that a key measurement point in an inventory is usually employed in a static configuration to verify that the inventory is as expected. If one had 20 items before, the key measurement point for inventory may be to go back and count the items to verify that there are still 20.
The flow KMPs are the record-keeping mechanism to keep track of material as it moves from MBA to MBA. The flow of material is such that the fresh fuel goes in through the reactor containment building, goes past a series of radiation detectors or monitors, is loaded into the reactor, and then, when it is discharged, takes a separate path out past a core discharge monitor and then eventually into the spent fuel storage bay.
How do these MBAs and KMPs work to form material accountancy for a CANDU facility? For the fresh fuel receipt and storage, the traditional measure is simply item counting. For CANDU facilities, one bundle is essentially a little less than 20 kilograms of uranium. There is no method today for inventory counting in the reactor core. Rather, accounting is addressed largely by the flow KMPs.
For spent fuel storage, the inventory key measurement points are essentially item counting coupled with some mechanism to verify that what is being counted is indeed consistent with irradiated material. The Cerenkov viewing device, a CVD or DCVD, is a typical example.
The core discharge monitor is a neutron and gamma tool that actually examines direct gamma and gamma-n reactions to give a unique signature that should be consistent with the known operating parameters of the reactor.
Next, Browne discussed some supplemental tools that one could apply to increase confidence in the nuclear security regime for these types of facilities. He then applied them to the sodium-cooled reactor.
The first is unattended monitoring systems. In general, an unattended monitoring system (UMS) is a radiation-based system designed to monitor the movement of nuclear material throughout a facility, whether the moves are intended or unintended. It can track fissile material or radiological sources by looking for specific characteristics that indicate the type of material, and it can compare the findings with the declared facility operations. If the operators know how the facility is operating, then the material movements detected should be consistent within that framework.
The UMS is usually designed according to the facility layout and what type of equipment is present to move the nuclear material such as cranes, entry points, exit points, and shielding. All of these items are factored in when designing an unattended monitoring system. Often a UMS pulls data from other sensors to provide a comprehensive view of how material is moving around and the activities associated with that movement.
Another supplemental tool is a near-real-time accountancy system (NRTA), which uses modeling and simulation tools to give the operator an idea of the real-time location of the material. Browne shared an example for a CANDU facility: As noted above, the operator knows the fuel’s initial enrichment, and the operational parameters of the reactor, such as where the assembly is loaded, the total core burn-up, and the reactor core power profile. Based on these inputs, the operator can use depletion-code calculations to determine what the uranium and plutonium content of the fuel assembly is at the time of discharge. With that information in an NRTA system, the operator can track all the special nuclear material of interest for all of his assemblies. The NRTA system can be validated by taking a once-through simulation and comparing it against measurements either from NDA or analytical chemistry.
Containment and surveillance tools, such as cameras, tags and seals, and tamper-indicating devices, complement the accounting system. Cameras with attentive guards or an unattended monitoring system that records the information enhance security. Tags and seals, whether metal or digital (e.g., a fiber-optic seal) show that an item has been accessed and, in some cases, an indication of the time when it was accessed. If incorporated into a UMS system, a seal can also trigger alarms sent to the central alarm station for a response.
Finally, advanced material assay capabilities can be used if more quantitative information is required. This can be done either as a random sampling program, to instill confidence in the material accountancy system, it could be used just during inventory verification, or it could be used in times when an event has occurred and one needs to recover from a discrepancy.
Example 1: A CANDU Reactor
The movements of fuel in a CANDU facility illustrate the application of these different tools. As the fresh fuel is moved into the CANDU reactor, it moves past the core discharge monitor. Because it has not been irradiated, the fresh fuel is easily distinguished from spent fuel. The core discharge monitor often does not give a clear signature, which is why in this area there are two sets of radiation detectors that have a greater sensitivity to let one know that the fresh fuel has moved into the reactor area. They are also there to prevent the discharge of fuel back through this path.
As the fuel is discharged from the reactor after irradiation, it passes the core discharge monitor, giving a characteristic signature, and moved into the spent fuel storage area, where it again passes through some general radiation monitors, which provide motion detection and direction of motion over the general area. Finally, a series of cameras deployed throughout CANDU facilities provide surveillance. When the fuel assemblies are in a static configuration, the operators often will use tamper-indicating devices to make sure that nothing has been accessed.
Example 2: A Sodium-Cooled Fast Reactor
Browne then described the tail-end of a sodium-cooled fast reactor. Accountancy systems associated with this type of reactor facility are dramatically different than for a CANDU facility. The core of such a facility is located several stories up and the fuel is discharged into a spent fuel pond. There is a vehicle access area, a lorry hatch, which is used for bringing equipment into and out of the spent fuel area. There is a set of rail tracks, which goes into a lower area used for moving the spent fuel into dry storage. There are hot cells used for post-irradiation examination and for handling and repackaging of radiation sources. There is also a personnel access area to the spent fuel pond. A series of radiation detectors, as well as cameras distributed as part of an unattended monitoring system, are part of the security.
Why would a liquid sodium fast reactor facility require a dramatically different approach from a CANDU? Unlike a CANDU, where the fresh fuel is natural uranium and the output is very limited quantities of relatively unattractive plutonium, the sodium-cooled fast reactor uses fuel with higher enrichment (26 percent HEU in the hypothetical example given) and may be run to low burn-up, producing large amounts of weapons-grade plutonium. If a facility was at a heightened security posture because of external circumstances, a very advanced accountancy system would be employed to maintain a high level of fidelity on the location of the nuclear material. In such a scenario, a twofold approach would be utilized. First, all the material would have to be characterized exceedingly well and the characterization would have to be maintained for an extended period of time. Second, the material would have to be tracked continuously throughout the facility.
To address the first point in this design exercise, as the fuel was discharged each assembly was measured using an underwater neutron coincidence counter. Combined with information as to the initial enrichment, isotope composition, depletion code calculations, that coincidence neutron measurement yielded a total plutonium mass on an assembly-by-assembly basis. Then to address proliferation concerns, the six assemblies were repackaged together into a proliferation-resistant canister. This makes the fuel more difficult to steal because bundled together the fuel is bulkier and heavier, and it has a higher radiation dose rate at the surface.
In such a facility, an unattended monitoring system would be designed and installed to track the movement of this material and to make sure it did not go through the lorry hatch or was not pulled out through the hot cells up back into the reactor hull or prematurely taken out through the rail access point. This was implemented through a series of detectors, designed specifically to look for the characteristics of the fuel associated with a specific facility. One of the difficulties associated with this sample facility, Browne noted, is that it was also used in the construction and repackaging of radiological sources such as cobalt-60 sources, and cesium-137 sources for industry. It was also creating antimony beryllium and americium beryllium sources for the local oil industry. So the system had to be capable of differentiating between these movements and the movements of the fuel itself in an operational mode.
Cameras that recorded activity were incorporated into the security design at the hypothetical facility examined, but they were triggered by radiation events so as to not create copious amounts of video data that were difficult to store. There were also other sensors included in this design to monitor movement. There was a series of underwater detectors, which were designed to take a look at the places where the fuel could be moved out of the water, and incorporated with that were underwater cameras, as well as ultrasonic sensors to make sure that shielding was not moved in front of the detectors, thus obscuring the signals.
The data from this system was fed into two other systems, the nuclear material accountancy system, so that the operator knew, in real time, where the material was and could differentiate between the operations associated with the sources and the operations associated with the fuel. It was also fed into the physical protection system at the central alarm station.
In addition to these measures, Browne noted that at personnel entry and exit points controlled by the physical protection system in the form of turnstiles, the operator had the ability to lock out the turnstiles and then respond accordingly should a specific signature be seen. The set of signatures the system looked for was generated by considering different possible shielding configurations and, if necessary, a full spectral analysis. The systems were helium-3 detectors, fission chambers, ionization chambers, and sodium iodide scintillation detectors.
Integrating information from different types of detectors is essential. For example, one may receive video data, an operator declaration, and real-time data associated with either radiation detectors or other sensors. As an example, the operator might declare his/her location at a particular time, the material that
he/she is working with, the activity he/she is conducting, and who he/she is. What one would like to do is to correlate this with the other data that are being recorded to build confidence in one’s knowledge of what is occurring. In this case, the video data will be watched and analyzed, looking for the time stamp, comparing it with the clocks, and looking at who is doing the activity and confirm it against the operator declaration.
At the same time, one should chart the signatures associated with the activity itself, for example, by looking at a door sensor to determine whether a door is opened or closed. The next step is a total neutron count. The third step is from a sodium iodide detector, which can measure with moderate resolution the energy and intensity of gamma rays and can infer enrichment and other aspects of the composition to make certain that what is being seen is a signature consistent with the declared material.
The idea is to pull all these data together in such a way that they provide increased confidence that the accountancy system is keeping track of what is occurring. In the example above, this was done through time synchronization of all the data generated by sources at a location. Associated with sharing data between a nuclear material accountancy system and a physical protection is the need to ensure that there is a consistent time base when trying to determine what is happening. In particular, if there is an inventory discrepancy to be resolved, having a consistent time base is critical.
Browne then discussed spent fuel. Currently, quantifying plutonium and spent fuel for security purposes is very difficult. It is not such a problem for the reactor, but it is a big problem for shipper-receiver differences, when the reactor ships it out to a reprocessing facility, and for input accountancy for reprocessing centers themselves. Currently, accountancy for spent fuel is, unfortunately, very simple. It uses Cerenkov viewing devices just to look for the Cerenkov signature or it uses detectors to confirm the presence of cesium-137 or fission to observe.
Recently, the U.S. Department of Energy and the National Nuclear Security Administration decided that they are going to take on the challenge of trying to improve the ability to directly measure plutonium content in spent fuel. This project is a several-year effort that is designed to examine the most promising technologies for the measurement of spent fuel, narrow that set based on agreed criteria, and then design and deploy the detectors to international partners around the world with whom the United States conducts spent fuel measurements. This is one area in which the United States hopes to improve nuclear security by improving operators’ capability to measure plutonium from reactors.
Browne then discussed how to align the interface between physical protection systems and nuclear material accountancy systems. It may be obvious that the nuclear material accountancy and physical protection system should be integrated in order to effectively promote the protection of the material. But in particular, it is important that the physical protection zones and the nuclear material balance areas overlap. If the material balance area is spread between two physical protection zones or vice versa, the ability to effectively respond to
an incident is reduced. It is best to ensure that there is consistency between these areas.
There is certainly a need to exchange information between the nuclear material accountancy and physical protection systems. Access to facilities is controlled by physical protection. But those responsible for physical protection also need to have intrinsic information about the material that is being protected there: What are the types of emissions? What are the dose rates? An example would be that the physical protection system should know what is required to move a particular source. Is a crane required? How much shielding would be required? Where is that shielding located? Sharing of this type of information enhances security.
In the interface between the nuclear material accountancy and physical protection systems, the nuclear material accountancy is designed to detect the material removal and the physical protection system is designed to prevent that removal. The security function relies on the same accounting systems used for bookkeeping. Then on the physical protection side, there is everything from the vulnerability assessment to the concept of operations regarding how to respond to actual removal. But there is a fair amount of overlap in between, in the form of the material balance area and the characteristic information.
Knowledge and information or data from both operations and the health/safety aspects are important for both accountancy and physical protection systems, and for overall nuclear security. Operations and occupational health and safety are additional pieces of information that help provide confidence in a security system. On the operations side, consider the question: Is a crane movement required for this particular process? If it is, then when that process is observed, one can be more confident. But if it is not needed and one sees the crane moving, then either from the physical protection side or the nuclear material accountancy side, further scrutiny is warranted.
With regard to health and safety, most facilities have contamination monitors. That information can be incorporated as well to provide an indication of abnormal conditions and potential theft.
Browne concluded his remarks with the following highlights:
• Nuclear security relies on a well-developed, integrated combination of nuclear material accountancy and physical protection.
• A risk-based approach is best to ensure that the fidelity is right. The nuclear material accountancy system for a CANDU facility is not necessarily the right match for a fast reactor.
• There are supplemental measures that can be incorporated to give increased confidence in a security system.
• Ultimately, the goal is to protect the public. This is a twofold measure. One is to ensure that the misuse of material or sabotage of a facility is prevented. But almost as important is to instill confidence in the public that the people at the facility are good stewards of the nuclear material.
Nuclear Materials Security at Non-Reactor Civilian Facilities
Indian Perspective
A.R. Sundararajan began his remarks by outlining the components of an effective control system for ensuring safety and security of radioactive sources. Via these components, the AERB ensures: an inventory of sources in the country, document control (monitoring the status of sources), regulatory inspections, secured sources at various stages of management, training of concerned public officials, and an Emergency Management System. Thus far, there have been no reports of major security incidents of nuclear material diversion from fuel cycle facilities involving individuals or groups of a criminal nature. However, complacency has to be avoided due to the potential significant consequences of a radiological event, and to maintain public confidence in the development of nuclear energy.
India has chosen to develop a closed fuel cycle because of its limited domestic sources of uranium. The closed fuel cycle allows for resource extension and sustainability, waste classification and isolation, a reduction in demand for repository space, and proliferation resistance (no plutonium mines leading to a reduced threat for future generations).
As part of the closed fuel cycle, India began its Fast Breeder Reactor (FBR) program with the construction of the Fast Breeder Test Reactor (FBTR), a 40 MWt (13.5 MWe) loop type reactor. The FBTR has been in operation since 1985. The Mark-I fuel has achieved a burn-up rate of 155 GWd/t at a maximum linear heat rate of 400 W/cm without clad failure. It has an expanded hybrid core of mixed carbide and high plutonium mixed-oxide fuel (MOX): 20 percent of the core has 44 percent plutonium MOX. There is an experimental Prototype Fast Breeder Reactor (PFBR) MOX fuel assembly at the centre of the FBTR.1 The 500 MWe PFBR was designed and constructed indigenously. Beyond the PFBR, India plans to build six commercial units of 500 MWe FBR (twin unit concept) similar to the PFBR with improved economy and safety by 2020. Subsequent reactors will be 1000 MWe units with metallic fuel, and the first unit is expected by 2027.
Sundararajan stated that there are certain proliferation resistant features of the fast reactor fuel cycle, which include modification of the plutonium uranium extraction (PUREX) flow sheet for co-processing of uranium and plutonium, higher contents of plutonium-240 and higher actinides, and the development of pyrochemical reprocessing for spent metallic fuels from future FBRs. The Indian fuel cycle strategy envisions using the minimum cooling period for fast reactor fuel and consequently the minimum out-of-pile inventory of plutonium. A versatile hot cell facility for testing the reprocessing process flow sheets and prototype equipment was commissioned in December 2003. After 2003, the
___________________________
1 MWt = megawatts thermal; MWe = megawatts electric; GWd/t = gigwatt-days per ton of initial heavy metal; W/cm = watts per centimeter along the fuel rods.
facility has processed FBTR plutonium-carbide fuel rods with burn up of more than 150 GWd/t with a cooling period of about two years and fission products with specific activity of about 700 curies per kilogram.
Bulk processing of plutonium from fast reactor fuel especially in concentrated form provides great potential for covert diversion by skilled adversaries. High burn up plutonium, particularly from fast reactors with large contents of plutonium-240 and higher actinides is not attractive for nuclear weapons, but stolen plutonium in view of its high toxicity and scare value can however be used in a radiological dispersal device (a dirty bomb).
To minimize the vulnerability of nuclear material, an integrated fuel cycle management system has been adopted. This includes minimizing the storage time of processed plutonium, minimizing the transportation of separated plutonium, and converting plutonium into MOX fuel. In fast reactor facilities, the vulnerability of the nuclear material increases vastly as the process moves from the front end of the cycle to the final product purification. The complexity of mechanical and chemical steps at the front end, due to high radioactivity requiring shielding and remote handling, acts as a great deterrent.
Nuclear safety and security serve a common purpose: protection of the worker, the public, and the environment from a large release of radioactive material. There is a growing recognition that it is prudent to have an all-hazards approach to national security that addresses a range of threats from natural disasters to man-made accidents or malicious attacks. There is one agency to oversee safety and security. Many of the principles of protection for safety and security are common, although the implementation may differ. Both objectives are pursued using a defense-in-depth approach through a number of redundant, diverse, and independent controls to reduce the likelihood of faults from occurring, to detect and control them when they occur, and to mitigate the consequences should the controls fail. The synergies between the requirements for these areas should be identified and any conflicts resolved.
Protection in depth requires an adversary to bypass or defeat a number of protective measures in sequence to attain a goal. These protective measures include physical security systems, administrative controls, and accountability. Some measures can serve safety and security functions simultaneously such as the massive shielding structure. Some measures may cause conflicts because of safety and security requirements. For example, the security requirement that the number of access points be kept to a minimum in a plutonium handling area can conflict with the safety requirement to have enough emergency exits to get out of the plant areas quickly in the event of a criticality accident. Likewise, security vulnerabilities could be created during an accident. Therefore, an objective optimization process is needed to support an integrated risk management plan. This has to be carried out at all stages of the plant from siting, design, to construction and operation. Site selection and design should take into account physical protection needs as early as possible and address the interface between physical protection, safety, and nuclear material accounting to avoid any conflicts and to ensure synergy among the three elements.
All plutonium facilities are subject to strict nuclear material accounting systems and physical protection measures. These include, protection in depth with multiple layers of protection, portal monitors sensitive to neutrons and gamma rays, containment and surveillance systems together with NMA provide a measure of confidence that potential diversion paths are not being used for clandestine purposes by criminal elements.
In plutonium reconversion/fabrication facilities where vulnerability is relatively high, near real time accountancy can be applied to improve the detection sensitivity for loss or diversion of plutonium. Concerted efforts are taken to include design, operation and control features aimed at reducing material unaccounted for and also to incorporate better plutonium measurement techniques.
The diversion of nuclear material from facilities can also be minimized by automating the process. Through automation, access to the nuclear material can be minimized and the number of operators can be reduced, thus reducing the possibility of theft or diversion. The International Commission on Radiological Protection (ICRP) recently reduced the exposure limit to the eye from 150 mSv to 20 mSv. To reduce the individual exposure in plutonium fuel fabrication areas, one has to deploy more people, which may conflict with security requirements to keep the staff at a minimum. Therefore, the need for automation of the fabrication process is driven both by security and safety requirements.
Remaining challenges to the security of a fuel cycle facility include: the need for automation of the process operations and material accounting, new vulnerabilities from increased use of computers, cyber attacks on computer systems used for process control, nuclear material accounting, and physical protection systems. The absence of structured guidance documents on security similar to the safety codes and guides is also a challenge. Currently, no hierarchical documents exist for security and there are concerns about inadvertent revealing of plant security vulnerabilities. Consequence analysis is essential and conducted using a design basis accident and a design basis threat. A primary distinction is that nuclear safety regulation is not prescriptive, whereas nuclear security regulation is prescriptive.
Finally, Sundararajan concluded that the lack of sharing of experiences from fuel cycle facilities in other countries remains a challenge. Likewise, there is a lack of standardization across facilities, which makes security difficult as well. He said that India has excellent probabilistic safety assessment models for safety assessment of nuclear facilities but does not have vulnerability assessment models for security assessment of nuclear facilities. The organization of appropriate training programs to promote security culture would be beneficial.
U.S. Perspective
Michael O’Brien began his presentation by stating that the protection of nuclear facilities has evolved over many decades. This evolution has been
necessitated by advances in technologies as well as the need to adapt to a changchanging threat. According to the IAEA Guide INFCIRC 225 Rev.5,2 which a vast number of nuclear facilities world-wide use as their principle guidance, nuclear facility physical protection should be based on a defined threat. This threat and the characteristics of the threat are defined at the government level in the United States. The facility physical protection system would be expected to adequately address sabotage and theft attempts by adversaries defined in threat guidance and therefore requires development of appropriate protection strategies and proper implementation.
When determining the threat, O’Brien stated that the threat guidance, generally referred to as a design basis threat DBT, describes the number and attributes of adversaries. A common DBT would define a group of outsider adversaries and one or more insider adversaries, and outsider adversaries colluding with an insider. The capabilities of the adversaries would also be defined in terms of their knowledge, skills, weaponry, and equipment.
The philosophy of protection in the United States includes the notion that nuclear facilities should be designed to allow for redundancy and defense in depth in the protection system to avoid single point failures and to force adversaries to defeat several protection elements in order to achieve their intended task. The facility layout may also be designed in a way to afford a layered or graded protection approach in which protection measures increase closer to target locations.
A protection system may encompass several principle objectives. These may include protection against: theft by outsider and/or insider adversaries, sabotage by outsider and/or insider adversaries, or cyber attacks. The combination of protection systems and protective force deployment must effectively mitigate each of these threats. This deployment may require the implementation of multiple strategies.
The protection strategies, containment, and denial, are specific to the type of threat one is protecting against. A containment strategy is used for protection against theft of nuclear material, through the use of appropriate detection, delay, assessment, and response capabilities. Protective force assets must be able to respond in time to interdict, contain, and neutralize an outsider adversary force before completion of an attempted theft. A denial strategy is used for protection against sabotage of nuclear material, through use of appropriate detection, delay, assessment and response capabilities. Protective force assets must be able to respond in time to interdict and neutralize an outsider adversary force prior to the adversary forces arrival at the target location thus denying their access to the location and their sabotage attempt.
___________________________
2 Nuclear Security Recommendations on Physical Protection of Nuclear Material and Nuclear Facilities (INFCIRC/225/Revision 5). IAEA Nuclear Security Series No. 13. http://www-pub.iaea.org/MTCD/publications/PDF/Pub1481_web.pdf.
Strategies against an insider threat encompass some appropriate combination of separation of duties, limited access, limited responsibilities, compartmentalization, two-person rule procedures, material surveillance, material controls and accountancy measures, as well as safety procedures and systems in order to increase the likelihood of detecting an insider attempt of theft or sabotage. A human reliability program may be administered to further enhance an insider protection program.
A strategy against a cyber threat encompasses analysis of electronic networks and the identification of appropriate electronic measures to detect network penetration attempts.
According to O’Brien, a strong physical protection system (PPS) design effectively integrates people, procedures and equipment to meet the objectives of the system. The protection system design must facilitate protection elements working together to assure protection rather than treating each single element separately. For example, to be effective, the manager should ensure that fences, sensors, delay systems, closed circuit television assessment systems, procedures, communication systems, and protective force personnel act as an integrated system meeting protection objectives. The primary PPS functions are to detect, delay, assess, and respond to adversary actions.
Intrusion detection may consist of an array of technologies designed to detect penetration by an adversary. Some examples include: exterior/interior sensor technologies such as microwave, active or passive infrared, vibration, magnetic field, and electric field. Delay systems decrease the adversary rate of progress toward the target allowing an adequate number of protective force personnel to respond in time to stop a malevolent act. Some examples include: fences, walls, doors, structural enhancements, vehicle barriers, smoke or fog visual obscurants, entanglement systems. Assessment systems aid in the visual verification of detected adversary actions, as well as aid the protective force in the subsequent engagement with the adversaries. Some examples include: closed circuit television cameras, lighting systems, and posted or patrolling protective force personnel.
Protective force personnel provide the response actions to interdict and neutralize adversaries. The response force is generally composed of tactically-trained primary responders, tactically-trained secondary responders, and posted or patrolling protective force personnel who augment the engagement by primary and secondary responders.
To achieve an appropriate level of system effectiveness, O’Brien noted, the entire protection system must operate in a complementary and integrated manner. Protection elements do not have to be physically integrated, but rather have to work in synergy to achieve the overall protection objective. Three noteworthy points of integration include:
(1) nuclear material controls, which allow material accountancy and physical protection to work in a complimentary fashion
(2) protection systems and protective force, which form the main core of the protection system
(3) command and control system integrating physical protection systems as a single command center operated by a protective force.
Nuclear material controls may include: material surveillance systems, point sensors, vault-alarm sensors, two-person procedures, material tie-downs, and entry control measures such as nuclear detection portal monitors, metal detectors, and electronic access controls.
Physical protection systems provide the means for the protective force to detect, delay, and assess adversary actions allowing the response force to tactically engage the adversaries in a timely manner. When needed in situations of shortcomings, compensatory measures for an integrated system can be either physical protection system elements or protective force personnel. Integration of physical protection systems into a single alarm control and display unit with assessment, entry control, and communication capability provides protective force personnel the ability to effectively operate the entire system for daily operations and in emergency situations such as adversary malevolent acts.
Protection systems should be in a constant state of evaluation. System effectiveness should be validated and any shortcomings addressed in a timely manner. This is often best implemented through a performance assurance program, which is a means to collect and store system data in a single location for use by analysts in verifying system effectiveness. A system testing plan should define the manner and frequency system components are tested for functionality as well as performance against design criteria.
O’Brien said that all critical systems and their critical elements should be performance tested regularly. Tests can be at the system level or component level. Test results should be documented and archived for use by system administrators, performance assurance program administrators and vulnerability analysts.
Protective force personnel should be subject to periodic testing to validate tactics, procedural compliance, and response times. Test results should be documented and archived for use by performance assurance program administrators and vulnerability analysts. Similarly, material control and accounting (MC&A) systems and their critical elements should be performance tested regularly. Tests can be at the system level or component level. Test results should be documented and archived for use by system administrators, performance assurance program administrators and vulnerability analysts. Vulnerability analyses and the documented system effectiveness level should be validated on an annual basis and when a change in operations or facility configuration occurs.
In summary, nuclear facilities require the highest level of security due to the high consequence to the public if a malevolent act were to occur. Proper protection planning, design, and implementation approaches are well documented and shared within the global security community.
Safety, Security, and Safeguards
Paul Nelson began by stating that his presentation would emphasize nuclear security, but that he also would refer to safety and safeguards as well. Together they make up what is known as the “3 S’s.” He also focused on the educational aspects of all three, especially security and research.
As has been stated by other presenters, public perception of safety and security is essential, especially in a democracy where public confidence is crucial to nuclear activities. For purposes of nuclear security, it is important to reassure the public that appropriate measures are being undertaken, while not revealing information that might be useful to any potential adversary. In the United States, the responsibility for security of civil materials resides with the (typically private) entity owning the material.
Nelson then provided an overview of the Texas A&M University’s Department of Nuclear Engineering at which graduate students do scientific and technical work with policy overtones. Other U.S. universities with similar programs in nuclear security include the University of California at Berkeley, the University of Missouri, the University of New Mexico, and the University of Tennessee. Nelson noted examples of possible research projects for Indo-U.S. collaborative efforts that could be conducted either through these universities or elsewhere.
He provided examples rooted in the so-called “risk equation.” Figure 2-1 defines risk as the expected value per unit time of the consequences of an adverse action. At that level of generality, the concept of risk is equally applicable to safety, security, and safeguards, and in fact probably has been most extensively applied to safety in the form of so-called risk-informed approaches to nuclear safety issues. The objective of the defending force is to minimize risk, but Nelson stated that probability and consequences should not be overlooked.
The problem of how to assess quantitatively the probability (frequency) of attack in the security and safeguards areas may be one possible joint research project. This could, if successful, move security toward the risk-based approach to safety. The currently accepted alternative is to design safety measures to the design basis threat DBT.
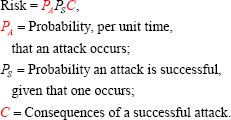
FIGURE 2-1 The so-called “risk equation” defines risk as the expected value per unit time of the consequences of an adverse action. SOURCE: Nelson, 2012.
A second research opportunity could be directed toward affecting some commonality in the measure of consequences across safety, security, and safeguards. The challenge is difficult, because consequences are not measured in the same terms (e.g., property damage vs. lives lost). Even within a single one of the “Ss”—for example safety—there are strongly held opinions regarding rational evaluations, and these differences are further confounded by lack of some basic knowledge such as the linear no-threshold hypothesis for very low radiation doses.
The third possible opportunity for collaborative research Nelson proposed lies in the area of information security. It is based on the observation that at many nuclear installations there is need for communication resources for purposes of both security and safeguards. It is therefore an obvious idea to achieve economies and efficiencies by sharing resources between these two needs. The problem of course is how to ensure integrity of the two data streams, especially given that for security the host nation is the protectorate, while for safeguards it is the presumed adversary. The research question very roughly could be how to use software-based methodologies to achieve that integrity.
The fourth and final example of a possible research collaboration is on consequence management training tools, such as the development of a plume simulator for handheld instruments, or even smartphone applications.
Nelson also noted that there could be a junior-level exchange program between Indian and U.S. students to jointly address these and other issues. From his perspective, an ideal arrangement would be an “experiment” in which a few U.S. graduate students in nuclear engineering, for example, could carry out research internships at appropriate Homi Bhabha National Institute (HBNI) campuses in the summer of 2013, to be followed by similar research-oriented visits by current HBNI students or recent graduates later in the fall of 2013. They could be matched-up in pairs to permit six months of continuous effort by the same people in the same problem area. The hope is that these exchanges would lead to substantial results. He noted that there are some universities in the United States interested in this idea. Hopefully there would also be Indian universities interested in hosting students from the United States as well.
DISCUSSION
The initial question was about personnel reliability programs and who, in the United States, has access to sensitive target areas. For example, would guards have access to sensitive areas, because this might constitute a type of insider threat if the person were to be ideologically inclined. There were three attacks on military targets, not civilian, likely due to insider threats.
O’Brien replied, that, yes, the personnel reliability program does apply to the guard forces. He noted that because their duties or responsibilities relate to the protection of the material, the majority of the MC&A personnel, material handlers in various functions at work that environment, will be under the
program. Protective force personnel are under the program. People who main-maintain the systems are under the program, and even some of the first-level supervision of those personnel. The main group of those who either have direct access or who could obtain access to the material are covered by the program in the United States.
Kumar replied that to the best of his knowledge, India uses the same approach. Anyone who could potentially be an insider threat, including the top manager, is covered by the program. This is always taken into account in the design phase as well. Other measures are also taken. He continued by stating that when new guard forces enter the system, or come to a new facility, a check is performed; there are always checks and balances.
A participant continued, in many of India’s security facilities, there is a layer of overall security, then there is the Central Industrial Security Force (CISF). There is separate training for CISF personnel involved in specific duties at some of facilities. These guards know that if they are assigned to a BARC facility, they have to have additional training. However, what is actually going on inside is something that they may not know at all. Access is granted on “a need-to-know basis.” They do have to be sensitized with additional information. They are also monitored. Also, the CISF forces are rotated perhaps as often as every one or two months.
A question was raised about security at nuclear facilities from the front end to the back end. Last year an IAEA Scientific Committee studied the effects of atomic radiation for a 20-year period, 1987 to 2007, and there were only three accidents. There were no deaths or injuries related to the absence of nuclear security. In fact, the IAEA safeguards group, to which safeguards accounting reports are sent every year for all members of the NPT with the exception of the nuclear weapon states, stated that all Indian facilities have nuclear security under control. There has been no diversion, which under IAEA Guidelines means that the probability of diversion of more than 1/3 of standard quantity is less than 1/3. So as far as the nuclear material at nuclear facilities are concerned, there is no guarantee that nothing will happen in the future but thus far there has not been any material breach of security.
On the other hand, the same IAEA scientific community said that orphan sources are a breach of nuclear security, and over the 20-year period from 1987 to 2007, 16 deaths have taken place, and there were 28 earlier incidents with more than 200 deaths, which means that the breach of nuclear security in the case of radiological material is far more serious than anything that has been contemplated in the nuclear facilities, and, of course orphan sources means they come only from industrial or medical applications. Those accidents are different. These orphan sources mean a breach of nuclear security, however, this was not discussed at the workshop. Is the real consequence of a breach of security for nuclear radiological materials far more serious and how do we adjust that? What are the concerns in coming years? There must be orphan sources in the United States as well as in India because there has not been a comprehensive check. There have been a few instances where Intercel radiography cameras
have been lost or nuclear gauges have been procured and not used lying idle for quite a long time. Some more attention should be paid to these sources. It is a public concern and serious, and in the case of Brazil, far more people were affected by unintentional radiation exposure from a radiological source in Goiania than anything that has happened in any other place. The offsite impact of Goiania is far more than the offsite impact of any nuclear accident at Chernobyl and recently Fukushima.
A participant noted that the Goiania incident was not a malevolent attack. In other words, incidents regarding orphan sources often arise out of ignorance. People who handled the materials did not know what the consequences would be, including the Mayapuri incident. After the Mayapuri incident, a system has been put in place in India to inventory all of the radiation sources and there is an exhaustive computerized database system. Today, with this particularly high category source, nearly 100 percent of the material has been inventoried. With lower category sources like that used in diagnostic radiology, the inventories are still to be completed because there is a very large number of sources dispatched. A large number of people have been trained in the last two years, as many as 2,000, in hospitals, in port authorities, in customs services, clearing agents; and all of these people have been sensitized with respect to the risk associated with this kind of source.3
Suppose a person receives a source from abroad, at the end of its useful life, it would not be exported. Ten years ago, there were no stipulations in India to address such incidents. Today, no one can import a source from abroad unless there is a commitment by the supplier to take the source back after its useful life in the country. The rules have been tightened and enforcement has been tightened. It is impossible to get a source imported without the clearance of AERB, and clearance for import, for use, for the operation, and for decommissioning and repatriation, without a license at every stage from the regulatory board.
Another workshop participant expressed surprise that a nuclear security breach includes an accident or a malevolent attack by a terrorist or a demonstrator. There is no distinction between an intentional or an unintentional act. Both are considered a breach. Second, in a 20 year period, 42 people died. For those 42 people, it makes no difference whether there was a breach of nuclear security because of a malevolent attack or a terrorist attack. Third, yes, these materials were handled, but they were handled not knowing what they were. Non-malevolent acts may also lead to complacency.
A participant from the United States added that in the early 1990s, requirements were added to conduct vulnerability analyses on special nuclear material, including what was defined as radiologically toxic material located at a
___________________________
3 Comptroller and Auditor General of India, Activities of Atomic Energy Regulatory Board, ReportNo. 9 of 2012-13. Available at http://saiindia.gov.in/english/home/Our_Products/Audit_report/Government_Wise/union_audit/recent_reports/union_performance/2012_2013/SD/Report_9/Chap_6.pdf. Accessed September 3, 2013.
site. Owners now have to analyze vulnerabilities, the risks associated with those items, and define security for those items, as well. And that has been going on ever since the early 1990s at Department of Energy (DOE) sites.
Another participant added that the problem seems to stem more from in-industrial radiography sources because a licensed person may wish to buy a source, but then pass it on illegally to someone else. What if it is lost? There was even a case some years ago when a disgruntled employee stole a source and threw it into a public body of water, and then it had to be retrieved. These sudsudden cases are far more difficult to resolve, but they need to be addressed in whatever way possible. There will always be some situations that cannot be ad-addressed.
The issue of retrofitting was then raised. How does this work? Architects are now giving us the option of greening older buildings for energy conservation with green technologies. How do you actually apply this design to an older building to make it secure and explain this to the budgetary authorities?
Another participant replied that this is a very good question because often these concepts and methodologies are presented as if we are dealing with perfect facilities, and in reality, no facility is perfect. The truest answer is that we do analysis, assess the risk, and sometimes we will end up with targets that are too close to perimeters or any number of issues. One just really has to do the best one can until the point is reached where one feels an adequate risk level has been achieved, and sometimes additional compensatory measures are unavoidable. All of this is driven by the scenarios analyzed at a particular facility. All facilities are different, of course. Whether you have done an adequate job or not is the end result of the risk equation. If that is not achievable, then the true measure is consolidation of material, movement of the material to other locations, and that happens as well.
A participant asked a follow-up question about whether or not decisions are made on a budgetary basis. Is a facility then declared as a high risk area? In reply, if the retrofit really truly cannot be done for whatever reason, the material is removed. In the United States, high-risk situations are not tolerated. The mission is moved elsewhere or that activity at that particular location is stopped.
Another participant added that sometimes regulations are prescriptive and not performance-based. An example would have been the requirement to have a Perimeter Intrusion Detection and Assessment System (PIDAS) around certain types of facilities. At the Savannah River Site, funding was requested to put the PIDAS around the separations facilities, but it just was not going to happen. There was not enough money in the budget. So, the risk was analyzed, and in that particular situation, it was judged that it was not necessary for the task being performed. The appropriate risk level could be achieved without funding that type of upgrade. So that would be an example where budget came into play, and the problem was reviewed and the decision was not to do the upgrade because it just didn’t make financial and security-base sense.
Raymond Jeanloz asked about avoiding a conflict of interest in that parparticular case. Were there outside reviewers, an independent audit or something
like that? Exceptions should be allowed without opening the door to conflicts of interest. In response, the participant replied that to the best of his memory, there was a congressional line item to do that upgrade, and the cost grew too large, so there was an independent analysis conducted.
Another participant recalled the earlier discussion about how the design basis threat DBT can drive costs up and down. There was an experience in the early 1990’s when a local DOE office asked to use the vulnerability analysis results, to conduct sensitivity analysis by adding and taking things away. They requested that certain items be eliminated, basically stripping the protection to determine how much money could be saved by taking protection away, and the facility was forced to do this. That was prior to the events of September 11, 2001. Subsequently, the DBT went up, and the facility was less equipped to ramp up to appropriate levels of security, and it cost quite a bit of additional money to have the right level of security. Therefore, as a note of caution, do not use the vulnerability analysis results as a kind of a cost metric. It is really a performance metric of the system, but it can also be misused, if the results are used the wrong way.
V. Venugopal agreed that previously, many of the radiological sources were not really properly accounted for, but now the bulk of radiation sources are more secure: sources associated with isotope technology are secured, databases have been completed, and frequent visits to the sites are made to see that everything is in place. This is one of the major issues with respect to radioisotopes in the public domain. It is a double edged sword. For example, Am241 were extensively used in various places as smoke detectors. And in the United States, 10 years earlier, a school student had collected large number of sources and material was dispersed in that area. His house was contaminated. The area was contaminated. So much money was spent. Now, this source was removed from smoke detectors. BARC has collected all of these smoke detectors and disposed of them after installing the new varieties. So these are the problems.
This is obviously a serious concern. At DOE, there are two programs dealing with this issue. One of them is well logging in the oil industry where radiological sources have been used and still are being used in reasonably large amounts. DOE is investing money to find an alternative to americium and beryllium sources and trying to see if one can receive neutron radiography not using radiological sources. The Department of Atomic Energy would certainly explore similar things. And the second one is DOE’s program, offsite sources recovery program. It is not about orphan sources, but rather an offsite sources recovery program by DOE and Los Alamos National Laboratory. They help remove some of orphan sources and secure them. There is a lot that can be done.
Communication also needs to happen because one can never completely avoid risk. It would be difficult to go to a drilling company and ask them to have all of their security measures consistent with those of nuclear and radiological facilities. How do we educate them? How do we procure orphan sources? Some of this is still being thought through.
Of these very technical issues, a participant stated that his source of concern is nuclear terrorism. During the Washington and Seoul Summits the Indian government and 40 other governments have committed at the highest level to nuclear security. So if one is concerned with nuclear terrorism, then one is concerned with security of materials of all forms, i.e. plutonium and uranium in the different forms, and irradiated fuel, and also radiological sources. Frankly, if there is a nuclear terrorist attack, we do not care what kind of material is used, the speaker said. The implications of a terrorist act with radioactive material is very serious. It is difficult to address because the sources are widely dispersed, which could increase the threat of an improvised explosive device. Is there currently a procedure in India to check every site of a bomb explosion for radioactivity, because without ever knowing it, there may have been radioactive material mixed with chemical explosives, only to be discovered much later. People who were exposed may have moved away. Maybe every chemical bomb explosion anywhere should also be checked for the presence of radioactivity.
































