1
The Role of Geotargeted Alerts and Warnings in Disaster Response
This report summarizes a February 2013 workshop organized by the National Research Council’s Committee on Geotargeted Disaster Alerts and Warnings: Current Knowledge and Research Gaps. In the context of alerts and warnings,1 geographical targeting, or geotargeting, refers to the effort to transmit alerts only to those recipients physically located in a geographic area affected by an event and/or are at risk.
Geotargeting is a two-step process. The first is the geo-definition of the targeted area is (e.g., a county or a geographic polygon). The second is the geo-delivery of the message to recipients within the targeted area. Both steps are susceptible to imprecision. In the case of geo-definition, some alerting systems only allow the definition of an area down to the county level, even if the actual affected area is only a section within it. In the case of geo-delivery, receipt of wireless transmissions cannot be limited precisely to a specific region. Any imprecision in one or both steps results in imprecision in the overall geotargeting.
At a 2011 CSTB workshop, it was observed that “[l]ocalization of
_______________
1 An alert notifies the recipient that something significant has happened or may happen, and a warning, which typically follows an alert, provides more detailed information describing the event and indicates what protective action should be taken by the recipient. The distinction between alerts and warnings is not always clear-cut because a warning can also serve as an alert, and an alert may include some information about protective measures. Technology has further eroded the distinction. For example, sirens have evolved to provide both a siren sound (the alert) and a spoken message (which, depending on how much detail it contains, might be considered a warning).
… messages by county or equivalent jurisdiction might be too coarse-grained, especially in the case of large counties and highly localized events.”2 Past research has shown that specific and clear information, including which locations are and are not at risk, increases the likelihood that people take protective action. The less precise the geotargeting, the more likely the recipient will ignore the alert, or choose to opt out of the alerting system, because they are not sure whether the message applies to them. When alerts and warnings are delivered to broader populations than those actually affected by an event, more people than are actually at risk may be sent messages to take action. This chapter explores discussions held by panel members and attendees of the February 2013 workshop on public response to geotargeted alerts and warnings.
There are several systems that provide geotargeted alerts today, with various degrees of precision. Some, such as the so-called “reverse-911” systems, can dial groups of landline telephone subscribers and can achieve a high degree of precision because they are capable of calling subscribers located within a specific polygon. On the other hand, wireless-based systems, such as the Emergency Alert System (EAS), are inherently less precise because of the wireless fencing issue. In the case of the national Wireless Emergency Alerts (WEA) system, alerts are transmitted to cellular phones using cellular broadcast technology.3 Only cellular mapped to the geo-defined region broadcast the message. However, the geotargeting precision of WEA in its initial rollout was additionally affected by a design decision to limit geo-definition to the county level. Another system is the National Oceanic and Atmospheric Administration (NOAA) weather radio, which uses dedicated radio frequencies and special-purpose receivers. It delivers weather and other hazard alerts and allows users to limit alarms to only those alerts designated for their location by specifying regions that are largely aligned with counties or portions of counties. Other services allow recipients to subscribe to alerts for geographic areas of interest to them, regardless of their actual physical location. Generally, such systems are not considered to possess true geotargeting capability.
Better localization might be provided by refinements to existing alerting systems or the use of new technologies. For example, some tighter localization is possible with the current WEA technology, but overlaps in coverage of individual cellular towers limit the precision that is possible. Additionally, if alert messages include information about the target
_______________
2 National Research Council, Public Response to Alerts and Warnings on Mobile Devices: Summary of a Workshop on Current Knowledge and Research Gaps, The National Academies Press, Washington, D.C., 2011.
3 WEA was formerly known as the Commercial Mobile Alerting System.
region, then software running on the receiving mobile device may be able to filter the alerts based on the device’s location. Existing technologies allow mobile phone positions to be determined with sufficient accuracy for most applications, at least outdoors, and emerging technologies promise significant improvements to indoor location measurement. Much of the second day of the workshop was spent exploring changes to existing technologies or new technologies for increasing the precision of geotargeted alerts; these discussions are explored in Chapter 2.
CURRENT AND FUTURE VISION FOR THE INTEGRATED PUBLIC ALERT AND WARNING SYSTEM
The Federal Emergency Management Agency (FEMA) oversees development and operation of the Integrated Public Alert and Warnings System (IPAWS), a national system for delivering emergency alerts and warnings to the public. One component, WEA, which is in the process of being rolled out, delivers alerts to cell phones using a special broadcast channel in cellular telephone systems. The message and associated metadata are formatted according to the Common Alerting Protocol (CAP) standard. Presentations by Denis Gusty from the Science and Technology Directorate of the Department of Homeland Security (DHS S&T), Wade Witmer from FEMA, and Mike Gerber from the National Weather Service (NWS) described the current state of IPAWS and WEA and outlined future plans for both.
The Federal Communications Commission, in cooperation with cellular telephone carriers, established a cell phone alert program, originally known as the Commercial Mobile Alert System. DHS S&T and FEMA have worked with the cell carriers on deployment and testing of the program, which is now known as WEA.4 A voluntary program for the cellular carriers, it specifies that participating carriers target government-originated emergency alert messages to the cell towers that lie within the counties affected by an alert. Messages are limited to 90 characters, which limits WEA to providing brief alerts to inform recipients that an event is occurring and that they need to seek additional information. It provides three types of messages: alerts issued by the president, alerts involving
_______________
4 WEA was established in response to the Warning, Alert, and Response Network Act (P.L. 109-347) passed by Congress in 2006. The Federal Communications Commission proposed and adopted the network structure, operational procedures, and technical requirements for WEA in 2007 and 2008, in cooperation with commercial wireless providers. Subsequently, the Department of Homeland Security Science and Technology Directorate and the Federal Emergency Management Agency have worked with the wireless carriers on deployment and testing of the system. The present design supports only 140-character messages and messages that fit into a single cell broadcast.
imminent threats to life and safety, and AMBER alerts (law enforcement bulletins in child-abduction cases). Mobile device users can opt out of all but the presidential alerts. However, some devices, such as those running the Android operating system, divide the imminent threats into two categories, extreme (e.g., tornados, extreme wind, or tsunami) and severe (e.g., flash flood, dust storm, or blizzard) and permit users to opt out of severe alerts but still receive extreme alerts.
WEA is designed to complement, not replace, other existing dissemination methods/channels supported by the IPAWS architecture (Figure 1.1). The central gateway, the IPAWS Open Platform for Emergency Networks, which is managed by FEMA, provides access to federal, state, local, territorial, and tribal authorities. Emergency managers are issued digital certificates to authenticate their access to the system and use commercial software to prepare and transmit messages.
The CAP standard supports the use of FIPS codes,5 which desig-
_______________
5 FIPS localization is based on standardized codes for county and equivalent geographical entities previously defined in the now-withdrawn Federal Information Processing Standards (FIPS) 6-4 standard and now defined by the American National Standards Institute INCITS 31:200x standard.
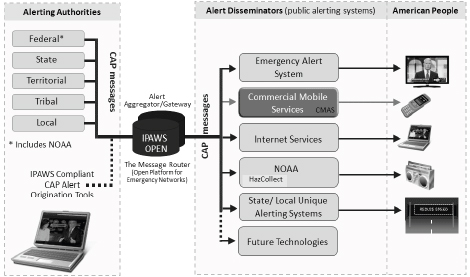
FIGURE 1.1 Structure of the Integrated Public Alerts and Warnings System. Source: D. Gusty, “Overview of the Commercial Mobile Alert System (CMAS) Research and Development Effort,” presentation at the Workshop on Geotargeted Alerts and Warnings, Washington, D.C., February 2013.
nate counties and subdivisions within a county, to define the targeted area. (Another standard, specific area message encoding, is still used by weather radios and is discussed in Chapter 2.) CAP also supports the use of a list of polygon vertex coordinates to specify the boundaries of a targeted area. The NWS has for a number of years defined smaller polygons for many of their severe weather alerts, and local agencies have found it beneficial to target alerts to areas much smaller than a county. Carriers have also developed approaches to target smaller areas than required by WEA, although neither perfectly targets the specified polygon (Figure 1.2). Today, each of the three major carriers uses one of these approaches to target only cellular towers in the appropriate portion of a county when subcounty-level alerts are issued.
Current Use of the Integrated Public Alerts and Warning
System and the Wireless Emergency Alerts
Today, over 150 entities—including approximately 75 counties, 25 states, and the Commonwealth of Puerto Rico—have access to the IPAWS-OPEN gateway, which allows them to transmit messages to cellular phones (using WEA), radio and television (using the Emergency Alert System), and NOAA weather radios. In addition, the NWS can send weather alerts, and the National Center for Missing and Exploited Children can send AMBER alerts. FEMA receives about four new applications a week for access to IPAWS-OPEN, and the system is projected to grow to include as many as 10,000 entities.
In 2010, the NWS was the first to use the system. Initially, messages were sent only to weather radios, but are sent now to other alerting systems, including WEA. For WEA, the NWS created template text for nine different types of warnings (a small subset of the templates for EAS). These templates are based on those designed for use in EAS but edited to adhere to the CAP standard and limited message length of WEA (Box 1.1). The NWS is currently exploring ways to give forecasters additional capabilities to customize messages and add geographic information.
Current Research Initiatives
DHS’s Commercial Mobile Alert Service (CMAS), Research, Development, Testing and Evaluation Program, established as a result of the Warning, Alert, and Response Network Act,6 is responsible for coordinating WEA testing, developing recommendations and guidance for its use,
_______________
6 Title VI of P.L. 109-347.
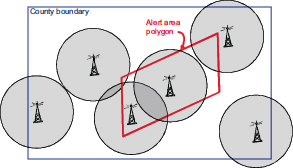
(a) Regulatory requirements require that a carrier targets an entire county area.
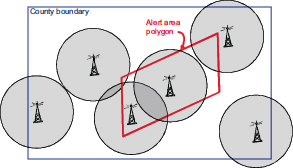
(b) An alert message is transmitted by each cellular tower located within the polygon.
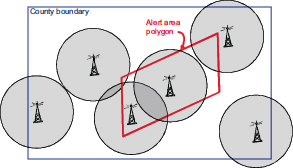
(c) An alert message is transmitted by each cellular tower that provides coverage in the polygon.
FIGURE 1.2 Options for mapping alert polygon regions to cellular towers. The circles surrounding each tower represent that tower’s transmission reach; the shading indicates that the tower is sending an alert. SOURCE: W. Witmer, FEMA, “Integrated Public Alerts and Warning System,” presentation at the Workshop on Geotargeted Alerts and Warnings, Washington, D.C., February 2013.
BOX 1.1
WEA Message Templates Originated by the National Weather Service
|
Tsunami warning |
Tsunami danger on the coast. Go to high ground or move inland. Check local media.–NWS |
|
Tornado warning |
Tornado Warning in this area til hh:mm tzT. Take shelter now. Check local media.–NWS |
|
Extreme wind warning |
Extreme Wind Warning this area til hh:mm tzT ddd. Take shelter.–NWS |
|
Flash flood warning |
Flash Flood Warning this area til hh:mm tzT. Avoid flooded areas. Check local media.–NWS |
|
Hurricane warning |
Hurricane Warning this area til hh:mm tzT ddd. Check local media and authorities.–NWS |
|
Typhoon warning |
Typhoon Warning this area til hh:mm tzT ddd. Check local media and authorities.–NWS |
|
Blizzard warning |
Blizzard Warning this area til hh:mm tzT ddd. Prepare. Avoid Travel. Check media.–NWS |
|
Ice storm warning |
Ice Storm Warning this area til hh:mm tzT ddd. Prepare. Avoid Travel. Check media.–NWS |
|
Dust storm warning |
Dust Storm Warning in this area til hh:mm tzT ddd. Avoid travel. Check local media.–NWS |
_______________
NOTE: tzT = timezone; ddd = three letter abbreviation for day of the week.
SOURCE: M. Gerber, National Weather Service, presentation at the Workshop on Geotargeted Alerts and Warnings, Washington, D.C., February 2013.
and funding research and development to enhance alerting systems. The act specifies research in the following specific areas:
• Improving geotargeting of mobile alerts and warnings, including geotargeting granularity, geotargeting in border areas, public response consideration to geotargeting, and alternative technologies to improve current and future geotargeting capabilities; and
• Improving public response to mobile alerts and strategies, including reaching special and diverse populations, information diffusion, and
public response to WEA initiation, message content, message frequency, follow-up, and source.
DHS is currently funding research by the University of Maryland’s National Consortium for the Study of Terrorism and Response to Terrorism on comprehensive testing of imminent threat messages for mobile devices and public response and social media (this work is discussed in the section, Current Research on Message Length, Geographical Information, and Geotargeted Alerts) and at the University of Southern Mississippi on geotargeting and other communication approaches for at-risk communities. A broad agency announcement for additional research and development has been issued, and additional awards are expected in 2013.
SOME CURRENT KNOWLEDGE AND RESEARCH ON GEOTARGETED ALERTS AND WARNINGS
In a panel exploring some of the current research on geotargeted alerts and the public response, Timothy Sellnow, University of Kentucky, discussed the role of geotargeted information in effectively communicating risk; Michele Wood, California State University, Fullerton, examined the various ways that geotargeted information can be communicated; Brooke Liu, University of Maryland, discussed hazard types and protective actions as they are related to geotargeted information; and Ken Rudnicki, City of Fairfax, Virginia, discussed tools used by emergency managers to geotarget alerts and warnings.
Wood summarized the results of decades of research on what types of alert and warning message content will motivate appropriate and timely action by the public (Box 1.2). Wood also discussed sense-making, a human process that occurs in the time between the receipt of an alert or warning and the time the recipient takes protective action. Message recipients will try to make sense of the message, confirm the message by seeking additional information, personalize the message to their own circumstances, and only then decide what action they should take. A key question is whether geotargeting can help reduce this delay in taking protective action.
Role of Geotargeted Information in Effectively Communicating Risk
Geotargeting allows an alert or warning message to be tailored according to the nature of the hazard faced at a particular location and the protective action appropriate for someone at that location. Receipt of a geotargeted message also strengthens the recipient’s perception that
BOX 1.2
What Is Known About Effective Alerts and Warnings
Several decades of research on public response to alerts and warnings have yielded an understanding of how to best formulate an alert or warning message. Key insights from this work are given below.
Message Content
• What (guidance). Exactly what protective action can be taken to best protect health and safety, and how will it be done.
• When (time). When protective action should be performed, when it should be completed, and when the threat has ended.
• Where (location). What locations are at risk and who should take protective action.
• Why (hazard and consequences). What the impending hazard is, what the potential consequences of the hazard are, and how the protective action can reduce harm.
• Who (source). Who is providing the message—which should be selected based on who would be viewed as the most credible source for the affected population, often several sources.
Message Style
• Clarity. Message is simply worded, free of jargon, and uses words that people can understand.
• Specificity. Message provides precise and unambiguous information.
• Accuracy. Message contains correct and complete information that is up-to-date, as free from errors as possible, and corrected when better information is known.
• Certainty. Message is stated authoritatively and confidently, even when there may be uncertainty about elements of the message content, especially about the protective action to be taken.
• Consistency. Message explains any changes from past messages and does not provide conflicting information that may create uncertainty.
Message Delivery
• Repetition. Messages may need to be sent multiple times during an emergency.
• Multiple channels. Messages should be sent using all available alert and warning systems.
Contextual Factors
• Status. Demographic factors, including socioeconomic status, age, ethnicity, and gender.
• Family and community role. The roles of individuals within and outside of the family, including family size, child ages, pets, and greater community involvement.
• Experience. Personal experiences of prior disaster.
• Knowledge. Pre-event knowledge related to the hazard, the protective actions, and the warning system.
• Environmental cues. Indicators in one’s environments such as rain, wind, or smoke.
• Social cues. Seeing or hearing about others taking the recommended protective action.
SOURCE: M. Wood, CSU, presentation at the Workshop on Geotargeted Alerts and Warnings, Washington, D.C., February 2013, drawing on work by Dennis Mileti and John Sorensen.
BOX 1.3
Message Variance in Food Recall Experiment
Message 1: Risk certainty (certain consequences) and expert opinions (cognitive salience).
Message 2: Risk certainty (certain consequences) and concrete experience/ personal stories about sickness and death (emotional salience).
Message 3: Expert opinions (cognitive salience), personal stories (emotional salience), ambiguous risk cause (uncertain consequences), multiple behavioral options (multiple efficacious actions).
Message 4: Risk certainty with specific and geotargeted behavioral directives.
he/she is indeed at risk and should take protective action. Finally, because receipt of a geotargeted message can substitute for lengthy descriptions of what areas are at risk, the message content can focus on the hazard and recommended public actions. (The latter is of particular value in systems that strictly limit message length.)
Timothy Sellnow reported a recent experiment testing the different wording for a message on a food safety recall—for example, Do message recipients understand how to protect themselves? and Do they intend to follow the instructions? Box 1.3 lists the various message variables tested. The fourth test message was geotargeted by stating explicitly that the affected food product was distributed in the recipients’ area.
Sellnow and his colleagues had two hypotheses: (1) the efficacy scores for behavioral intention, which indicate that a recipient intended to take protective action, would rise after receiving any of the four messages, and (2) the geotargeted message (message 4) would result in the highest level of efficacy and behavioral intentions. Hypothesis 1 proved true; recipients’ had a greater sense of behavioral intention. This confirms that those who receive a specific message about appropriate response believe they have the skills and intend to take suggested action. Perhaps more related to the workshop topic, hypothesis 2 also proved true; when a message is geotargeted, messages attract more attention, and recipients better understand potential risk. Sellnow stated that they have found this consistently across several experiments that examined geotargeted alerts and warnings. Additional key observations and open questions offered by Sellnow include the following:
• Past work has shown how an optimal message can be communicated in a limited time, but further research is needed on whether and how an optimal message can be conveyed in limited length (e.g., in WEA).7 • Some elements of geotargeting have been shown to improve self-efficiency—that individuals know what the appropriate action is and believe they can complete it—but further work would improve understanding of how other message variables, such as message source or alert type, structure, and delivery systems, affect response.
• The previous experience of message recipients with disasters remains a potentially confounding factor that this work did not control for. What impact might such experience have, and how might it be controlled for in future experiments needs further research?
• Recent research in health communications has shown that differences in recipients’ learning styles, or the way in which an individual best acquires or processes new information, may significantly affect their efficacy. How do learning styles affect the efficacy of geotargeted alerts?
• What are the optimal strategies with respect to the number and timing of messages at various points in an emergency? For example, when is it helpful to issue alerts as soon as a potential risk emerges? and Are there circumstances under which alerts are best deferred until the actual event onset?
• What types of hazards need what types of alerts or warnings? How does the prevalence of a particular hazard affect public response and alert needs?
Communicating Geotargeted Information
Michele Wood discussed the three general ways to communicate what areas are at risk: text that names locations or describes the boundaries of the area, pictures that show a map of the area, or geotargeted delivery of alerts or warning messages so that only affected populations will receive the messages.
Text-Defined Geolocation Information
Many alerting systems can transmit only text messages and thus must rely on text to convey geographical information. Possible approaches include the following:
_______________
7 B. Reynold and M. Seeger, Crisis and emergency risk communication as an integrative model, Journal of Health Communications 10:43-55, 2005.
• General text: “Tornado warning in this area until 12:00 PM Mountain Standard Time, take shelter now—NWS.” Although the message is short, recipients may not be able to tell whether they have been geotargeted (unless the message explicitly states they were) or whether they are, in fact, located in the affected area.
• Named locations: “Radiological hazard warning in Los Angeles, Orange, and Riverside counties until 12:00 AM PST. Take shelter now.—DHS.” This message names all the locations affected. However, this type of message is longer than necessary (and possibly longer than can be accommodated in systems that only transmit short messages). Additionally, the boundaries of the area affected by a hazards may not correspond well with the boundaries of cities, counties, or other named places.
• Descriptive boundaries: “Fire warning in area bounded by North West Parkway/E-470 on the north, Highway C-470 on the south, Highway 285 on the west, and the eastern boundaries of Adams and Arapahoe counties until 12:00 AM PST. Take shelter now.—NWS.” Although this approach makes it possible to define more precisely the area at risk, it does so with greater message length. Furthermore, it can be difficult to identify suitable boundaries that precisely describe the area at risk and that can be easily understood by recipients. Messages that depend on detailed local knowledge are especially difficult for visitors or new residents to interpret.
Using Maps and Images to Geotarget Messages
Maps are, of course, the canonical way to represent geographical regions. Map data are generally readily available, and it can be easy to clearly mark areas at risk through shading or coloring. Adding a marker for the recipient’s location further personalizes the information. If the system does not allow the recipient’s location to be shown (which relies on capabilities in the device receiving and displaying the message), a recipient may not readily see whether he/she falls within the affected area. Maps can also be difficult to display on devices with small screens (such as cell phones) or with low resolution (such as non-high-definition televisions). Another challenge is that not all message recipients will be adept at interpreting the map.
Geodefined Message Delivery
The third method for geotargeting messages is to target delivery of the messages to affected areas and provide the recipient with an indication that the message was targeted. For example, the message might include the text “If you receive this message, you are at risk,” so the
recipients understand that they are within the targeted area and are at risk. This strategy will work best if the alerting and warning system can target a sufficiently fine-grained location. (See Chapter 2 for a discussion of these capabilities.) Messages that purport to be geotargeted but are, in fact, delivered well outside the region actually at risk may be ignored because the recipient is not sure whether the message applies to him/her specifically.
Current Research on Message Length, Geographical Information, and Geotargeted Alerts
Brooke Liu, Michele Wood, and their research collaborators, are currently studying the relationships that text alerts, length, and geotargeting have on public response. The research considers how to optimize messages within the length constraints of major text alerting systems—WEA (90 characters), SMS and Twitter (140 to 160 characters), and the instructional field of an EAS message (1,380 characters). The research team is attempting to answer the following questions:
• How can 90-character messages be optimized? How is public response affected by location specificity, the sequence of the location information, and the source of the information?
• What is the relative importance of the key message elements in 1,380-character messages?
• Can these findings be generalized across different types of hazards?
• What is the relative efficacy of different (message length and location specificity) message types?
Because WEA messages are limited to 90 characters, additional research and thought are needed to understand what should be communicated to people first, second, third, and so on. In thinking about this question, Liu developed a matrix of imminent threat hazards and a sequence of protective actions that may need to be taken by an affected population.8 For example, a primary action in response to a chemical spill might be to shelter in place, and a secondary action might be to get decontaminated. The open question is when geotargeting makes the most sense for which alerts. Liu and her team believe that this is affected by several factors: alert type and format, hazard type and available content,
_______________
8 The complete matrix can be found in National Consortium for the Study of Terrorism and Responses to Terrorism, Hazards and Protective Actions Sequence Matrix: Comprehensive Testing of Imminent Threat Public Messages for Mobile Devices, 2013, available at start.umd.edu/start/publications/HazardsAndProtectiveActionsSequenceMatrix.pdf.
and lead time. Additional open research questions identified by Wood and Liu include the following:
• How does geotargeting affect people who are visually impaired?
• How does map literacy affect public response to geotargeted alerts?
• Does precise location language reduce time spent milling? Is this true across hazards?
• What limits does technology place on the ability to geotarget alerts?
• What is the most efficient combination of text, image, and geo-delivery?
• What public education is needed to help the public understand geotargeted alerts and new alerting systems?
Use of Geotargeted Information by Emergency Managers
Ken Rudnicki discussed the capabilities emergency managers have to issue geotargeted alerts and warnings. Each tool has different geotargeting capabilities, as follows:
• EAS provides information to television viewers and radio listeners. Although the messages generally contain descriptions of what areas are at risk, because they reach everyone served by a broadcaster or cable system, they are often disseminated to a large number of people who are not at risk.
• NOAA weather radios can be kept in constant standby mode, have alarms that can wake people who are sleeping, and support those with impaired vision. However, radios must be purchased and kept powered on by the end user.
• Subscription-based SMS text systems are used by many jurisdictions and institutions to send text messages that provide alerts about hazards and other items of interest, such as severe traffic alerts. Although these systems typically allow users to sign up for particular geographical areas of interest, the technology does not support delivery based on the recipient’s current location. As opt-in systems, they reach only people who sign up for the service.
• Reverse-dialing systems, currently one of most precise geotargeting systems, allow emergency managers to telephone individual homes within a given geographical region quickly. The population coverage of this technology is diminishing now that an increasing number of households no longer have a landline telephone.
• Third-party smartphone applications have also become more popular. These systems can use the phone location to provide alerts. Similar to subscription SMS text systems, users must opt in by downloading
the application on their phone. Additionally, since a third party manages applications, emergency managers have no understanding of who is receiving the alerts.
• WEA has numerous advantages over prior alerting tools; however, the very short message limits what can be communicated to recipients. While WEA provides county-level geotargeting by cell tower, there is still the potential for bleed over into unaffected areas. Furthermore, as it is a newer system, some practitioners and recipients are not fully aware of the capability or how best to use WEA.
The second session focused on the geotargeting needs and challenges for particular hazards. Thomas Cova, University of Utah, discussed wildfire events; Steven M. Becker, Old Dominion University College of Health Sciences, discussed radiological and nuclear incidents; and Peter LaPorte, Washington Metropolitan Area Transit Authority (WMATA), discussed transportation system emergencies.
Wildfire Events
Wildfire events provide significant challenges and opportunities for geotargeting alerts. While some wildfire movement is slow, allowing for proactive evacuation, shifting winds can quickly alter the course of the fire, which results in a need for fast evacuations of very specific areas. Thomas Cova presented the following case studies to illustrate how geotargeted messages might be used in wildfire events:
• The evacuation area for the 2012 High Park Fire in Colorado was described as “CR44H three miles south to just north of Stringtown Gulch Road, the entire Rist Canyon area, CR27E to Stove Prairie and south to Davis Ranch Road and Whale Rock Road.” Such a description poses two challenges: first, it cannot be understood by someone not very familiar with the area, and second, it turns out that this description does not, in fact, define a closed polygon.
• The evacuation zone established for the 2007 Angora Fire provides an example of how a very small and precise evacuation zone can be established using polygons. The evacuation order had 100 percent compliance for two reasons: (1) the warned area was small and highly targeted and (2) the flames from the rapidly moving fire provided environmental cues that action needed to be taken. The Angora fire also illustrates some of the complexities posed by geography. Because many of the roads in the neighborhood led into the fire’s path, many evacuees had to flee on foot.
• In the case of the 2000 Cerro Grande Fire in Los Alamos, New Mexico, emergency responders had as much as a week to carefully plan and carry out evacuations. They were also aided by very detailed emergency plans already in place, given the proximity of the U.S. Department of Energy laboratory. As the time to evacuate approached, houses in each designated zone were notified using a reverse 911 telephone dialing system of the need to evacuate and given instructions on when and by which roadways they should evacuate. The evacuation was completed quite swiftly, in 2.5 hours, and with almost 100 percent compliance.
Geotargeting could also provide an opportunity for time-sequenced changes in the recommended protective action for those who have not followed previous instructions. For example, the first alert within an area would instruct recipients to evacuate, a second would recommend that remaining residents shelter in place, a third would recommend sheltering in a refuge, and a fourth would recommend finding a safe area (a protective structure or body of water).9
Radiological and Nuclear Incidents
There are different types of radiological and nuclear incident types, including the unintentional release of radioactive material from a container break, nuclear accident at a nuclear power plant or nuclear fuel processing site, and an intentional radiological or nuclear incident, either a radiological dispersal device (i.e., dirty bomb) or a nuclear explosion of an improvised device. For each type of event, the right protective action information needs to be disseminated to the right people as quickly as possible. Steven Becker discussed the substantial challenges of messaging during radiological and nuclear incidents, including the following:
• Uncertainties in determining the composition and direction of radioactive plumes, changing conditions that require frequent changes in information, and, when terrorism is suspected, concern about additional attacks.
• The potential for widespread fear, profound sense of vulnerability, and a continuing sense of alarm and dread, which research has shown to be associated with emergencies involving radiation. Fatalism is particularly high with radiological events, and reportedly especially high within
_______________
9 T.J. Cova, F. Drews, L. Siebeneck, and A. Musters, Protective actions in wildfires: Evacuate or shelter-in-place? Natural Hazards Review 10(4):154-162, 2009.
minority populations.10 There is a high propensity to flee in these situations, and compliance with shelter-in-place instructions may be poor.
• The complexity of and unfamiliarity with radiation-related concepts and terms.
Although there are messages, templates, and questions and answers that have been developed and vetted for technical accuracy and efficacy, less is known about how these messages can be communicated in a shorter format. There is also a large demand by affected populations for graphics of the affected area, especially in regard to plume maps. Messages also need to be tested and developed that can address the problem of fatalism.
Fukushima Dai-ichi Nuclear Accident
During the March 2011 Japan Earthquake, the Fukushima Dai-ichi Nuclear Generating Station, one of the largest such installations in the world, was severely damaged. It would become clear that large amounts of radioactive material had been released, that there were threats of additional releases, and that a large area needed to be evacuated. Although plans had been created for areas immediately surrounding the plant, the evacuation zone became much larger, complicating evacuation planning and execution. The event provided valuable lessons in communicating during nuclear and radiological incidents:
• Evacuation orders for radiological events need to include information about direction of the plume so that people can take appropriate action. This information was not provided because scientists felt that the plume model was not fully developed and because emergency managers feared that people would panic if they were provided incomplete information. Unfortunately, the decision to withhold information resulted in people in some communities actually evacuating into the path of the plume.
• Emergency plans need to handle cases where the infrastructure is degraded. At Fukushima, individual emergency plans had been developed for earthquakes, tsunamis, and nuclear accidents. But when all three occurred nearly simultaneously, many of the shelters or evacuation routes were no longer usable. Similar concerns apply to the communication infrastructure needed to alert the population and coordinate emergency response.
_______________
10 S.M. Beck, Communication and information issues in terrorism events involving radioactive materials, Biosecurity and Bioterrorism 2(3):195-207, 2004.
• Messaging strategies and preparedness education need to include methods for the public to recognize genuine communications and identify misinformation. Various credible-looking but false messages were sent to people in the affected area. This resulted in people taking potentially unsafe or useless actions, such as purchasing large amounts of iodized salt in the false belief that this would provide useful protection against radioactive iodine isotopes.11
Public Mass Transportation Systems
Peter LaPorte, director of emergency management for WMATA, discussed the challenges of communicating with riders of public transportation systems. Most messages to the public relate to system delays or temporary closures, while a much smaller number are issued when passengers are directly affected by breakdowns or other problems. Many alerts are to notify riders about delays owing to train, track, or signal problems that require trains moving in opposite directions to share a single track temporarily. Alerts may also cover scenarios that have a larger and longer impact on riders, such as a broken rail or a station fire. In these incidents, it is important to convey what the public should expect in terms of delays or closures. Some scenarios, such as an individual on the tracks, pose a different challenge because authorities are trying to understand a complicated and potentially serious situation at the same time that the public and the media also want to understand what happened. Did someone jump? Was someone pushed? Did someone fall?
Messages are delivered through multiple channels. Within the system, WMATA can use electronic message boards and public address systems in the stations and public address systems on board the trains. WMATA also provides text message and email alerting and allows customers to subscribe to alerts by line and time of day. WMATA alerts regarding major delays are also picked up by alerting systems operated by local jurisdictions and the media. In some scenarios, such as when a train is disabled between stations, responders may be needed on the scene to directly communicate appropriate action and to avoid unsafe actions by passengers.
The various capabilities for alerting the public all have certain limitations. For example, cellular coverage in the underground portion of the system is not complete, although a congressional mandate to provide full
_______________
11 Discussion of ways to identify and correct misinformation during disasters is discussed in depth in the previous report, National Research Council, Public Response to Alerts and Warnings Using Social Media: Report of a Workshop on Current Knowledge and Research Gaps, The National Academies Press, Washington, D.C., 2013.
coverage is expected by the end of 2014. In addition, public address systems in the trains and stations may not be audible to all riders.
WMATA’s alerting process also includes alerting and contacting local-jurisdiction emergency or transportation staff. WMATA works closely with the federal Office of Personnel Management (OPM) during severe weather events to consider the impact of service disruptions on the federal workforce; many private organizations also follow the OPM’s lead. WMATA also works with local trade organizations to communicate with local workforces. Responding to emergencies within the system involves close cooperation and careful coordination with county and city authorities and first responders in Maryland, Virginia, and the District of Columbia.
DATA SECURITY AND PRIVACY CHALLENGES
Panelists Patrick McDaniel, Pennsylvania State University, Marc Armstrong, University of Iowa, Darrell Ernst, private consultant, and Kevin Pomfret, Centre for Spatial Law and Policy, examined data security and privacy concerns associated with geotargeted alerts and warnings.
Defining Security and Privacy
Security was defined by Patrick McDaniel as when a device, system, or service acts as expected. When a system is secure, information is legitimate and unmodified, only authorized parties can participate, access is available, and, where needed, secrecy (not to be confused with privacy) is available. In the context of alert and warning systems, security concerns include ensuring that only those who are authorized can send alerts, that messages cannot be modified or forged to misinform the public, and that messages cannot be suppressed through damage to or overload of the delivery system.
Privacy, as defined by McDaniel, means that an individual controls what information about that individual is exposed and to whom, when, and for what purpose. Privacy is often a negotiated and constantly evolving term. The issue is mostly of control, not exposure, and privacy starts with informed consent. Users often trade some information for a benefit; they need to understand this implicit transaction. If a company collects information for a benefit then uses that information for an undisclosed purpose, that is a violation of privacy. While the majority of privacy conversations involve knowing a user’s physical location, collection of location over time can provide a very detailed outlook of an individual. Users often have different reactions to a service provider having location
information versus the government having the same information.12 The design of an alert and warning system is influenced by both security and privacy, and retrofitting a system to consider these concerns is difficult.
A geotargeting service might adhere to some of the following basic, demonstrable, and testable principles and standards to provide security and privacy:
• All alerts must be delivered without modification.
• Only authorized parties are able to transmit alerts.
• All alerts must be received within a specified period. An example of this is E911, which requires that a location of a user within 300 meters can be found within 6 minutes.
• Alerts must be delivered only to the designated area.
• Alerts must not substantially affect the infrastructure over which they are transmitted.
• Users must be able to control or know what personal information is exposed to the service provider and how the service provider will use the information.
Defining Geoprivacy
Marc Armstrong defined geoprivacy as an individual being secure from unwanted observations and tracking. Currently there are requirements involving location data and mobile devices. This includes E-911, which requires that mobile devices periodically report locations based on Global Positioning System (GPS), cellular towers, or Wi-Fi locations. Similar location data are often shared with third-party application developers, who may also then share the data with others. Risk associated with this behavior includes further disclosure of information, consumer tracking, identity theft, threats to physical safety, and surveillance.
There are some techniques to preserve geoprivacy while still providing location-based services. One is areal masking, in which location information is sent only when someone enters a particular region. Travel within the region would not need to be known. However, this would delay the immediate arrival of geotargeted notifications to the end uses. Current work is being done that highlights these masking techniques and a recently founded company, iGeoLoqi, has developed tools that incorporate some of these techniques, which provide location information and broadcast push notifications, and individuals trigger the messages by entering, staying, or leaving a location.
_______________
12 U.S. Government Accountability Officer, Mobile Device Location Data, 2012, available at http://www.gao.gov/assets/650/648044.pdf.
Legal Issues Around Geotargeted Alerts
Kevin Pomfret defined spatial law as the set of legal issues associated with geospatial technology and the collection, use, and transfer of location information and other types of spatial data. Spatial law involves a range of issues, including privacy, intellectual property and licensing, data quality and liability, national security, open records, the Freedom of Information Act, and other government regulations. Location information creates challenges distinct from those created by traditionally protected personal information (such as social security numbers and financial information). For example, someone who does not have other information about a person’s identity can, nonetheless, readily infer where the person works and where the person lives. In addition, location data are generated differently from other sorts of personal information, making the definition of “public”—long an analytical tool used in assessing privacy and other impacts—a challenge. For example, individuals move (change location) through public spaces, and most government privacy policies have exceptions for “publicly available information.”
Even as compelling new applications for location information are being developed and deployed, privacy advocates urge careful consideration of how this information might be used and how to protect the privacy of users. Media scrutiny is having an impact on this discussion. For example, due to media coverage, organizations are pulling back the use of location tracking tools. Short Pump Mall in Richmond, Virginia, decided against using a mobile application after media scrutiny criticizing its privacy implications,13 and a New York community stopped using publicly available aerial imagery to identify unregistered and untaxed pools. Additionally, Congress has considered several pieces of legislation addressing location privacy, and regulatory authorities are examining ways to address this issue. However, geolocation information is often just part of a longer list of issues surrounding privacy.
Previously enacted privacy legislation—such as the Commercial Privacy Bill of Rights Act of 2011, BEST Practices ACT, Do Not Track Me On-line Act, Consumer Privacy Protection Act of 2011, and an update to Children’s Online Privacy Protection Act—may provide a foundation for future legislation protecting location information. Many of these laws are
_______________
13Richmond Times-Dispatch, Town Center’s Monitoring Policy Creates Backlash, posted November 26, 2011, available at http://www.timesdispatch.com/business/town-center-s-monitoring-policy-creates-backlash/article_7b6bd70f-7bc8-5564-a417-7856266079f5.html.
based on the principles of fair information practices (FIP).14 Elements of FIP include notice and transparency, consent and use limitations, access and participation, integrity and security, and enforcement and accountability. However, there are challenges in applying FIP to geolocation information: How will “precise geolocation information” be defined? How do you provide adequate notice on a mobile device? In which contexts are opt in or opt out the appropriate forms of consent? What is a consumer’s right to have geolocation information corrected or deleted? and How long should geolocation information be permitted to be stored?
The Federal Trade Commission (FTC) is examining privacy-protecting practices and has broad authority under Section 5 of the Federal Trade Commission Act. These actions include bringing action against companies that do not comply with their own privacy policies and against companies that do not adequately protect personally identifiable or other sensitive personal information. A December 2012 FTC report, “Protecting Consumer Privacy in an Era of Rapid Change—A Proposed Framework for Business and Policymakers” provides a list of the FTC’s best practices for mobile privacy (summarized in Box 1.4).15
Technologies That Support Privacy
In 1992, Darrell Ernst began developing a technology to geotarget alerts while preserving privacy. This technology would send an alert to a wide area, and a location-aware device would determine if the alert was relevant to individual users. The technology was originally developed to aid in risk communication to military personal (information regarding detected missile launches is broadcast to specifically programmed handheld devices carried by personnel in the field). If a device received such a message and determined it was in the warning area, it would notify the user. A general application of the technology could allow for more privacy-sensitive alerting. Since the device itself assesses and filters messages, the authorities sending the messages do not need the ability to track where end users are. Receivers for this type of alert broadcast could be placed in a wide variety of devices, including in-home appliances that are programmed with their static location. Called GEOcast, SquareLoop
_______________
14 Fair Information Practicies (FIP) were developed by the Federal Trade Commission in the mid-1990s in response to concerns of how online entities collect and use personal information. Current FIP principles can be found at http://www.ftc.gov/reports/privacy3/fairinfo.shtm.
15 Federal Trade Commission, Mobile Privacy Disclosures: Building Trust Through Transparency, Staff Report, February 2013, available at www.ftc.gov/os/2013/02/130201mobileprivacyreport.pdf.
BOX 1.4
The Federal Trade Commission’s Best Practices for Mobile Privacy
Provide timely privacy disclosures to consumers and obtain their explicit consent before allowing apps to access and collect certain sensitive data and content;
Consider developing and implementing a visual “dashboard” that displays for consumers the types of data accessed and collected by apps;
Consider designing, testing, and implementing intuitive and simple icons to depict certain app privacy practices;
Implement and enforce contractual obligations for, and promote best practices and educational information to, app developers that address mobile privacy;
Consider providing consumers with clear disclosures about the extent of prerelease review and postrelease compliance checks that platforms undertake for apps that can be downloaded from the platform; and Consider offering a Do Not Track (DNT) option.
SOURCE: Federal Trade Commission, Mobile Privacy Disclosures: Building Trust Through Transparency, Staff Report, February 2013, available at www.ftc.gov/os/2013/02/130201mobileprivacyreport.pdf.
licensed this technology and continues to further its development for alerts and warnings.16
Workshop attendees noted that some current alerting systems use similar privacy-protecting methodology. For example, with WEA, cellular towers determine if they are within a given alerting area and send alerts to all phones within the designated area. Much of the second-day discussion at the workshop focused on technologies, such as the one described above, that would support better localization by the device itself. If a device had more precise knowledge of its location, this information would not necessarily need to be shared with alerting authorities.
_______________























