The information in Chapter 2 clearly shows that disasters are equal-opportunity destroyers, and the viewpoint that an academic research institution can simply rebuild as it was and “get back to business as normal” is myopic and fails to see the wider perspective that encompasses both the tangible and the intangible losses that are suffered when the research is lost. In Chapter 4, the committee emphasized the importance of aligning the academic research institution’s disaster planning with the preparedness goals and procedures used throughout the nation. Chapter 5 focuses on potential actions from the prevention, protection, and mitigation areas that are specifically relevant to the research enterprise. The chief resilience officer for the research enterprise and the research enterprise planning committee, in coordination with the institution-wide planning committee, should consider these actions during the planning process. Significant gains in resilience can be made by considering prevention, protection, and mitigation actions.
PREVENTION PLANNING
The Federal Emergency Management Agency (FEMA) National Prevention Framework describes what the whole community—from community members to senior leaders in government—should do upon the discovery of intelligence or information regarding an imminent threat in order to thwart an initial or follow-on terrorist attack (FEMA, 2016b). While prevention is a common term that is defined differently by various disciplines, FEMA defines it in this framework as what leaders and practitioners at all levels of government, private- and nonprofit-sector partners, and individuals do to prevent, avoid, or stop a threatened or actual act of terrorism. Though the other frameworks focus on all hazards, including natural disasters, the National Prevention Framework focuses solely on terrorist activities—and specifically on imminent threats or acts of terrorism. Imminent means that there is intelligence or information that warns of a credible, specific, and impending terrorist threat or an ongoing attack. While prevention is largely the responsibility of law enforcement, academic research institutions and their research enterprises also have a role to play.
The National Prevention Framework is rooted in three important principles: engaged partnerships; scalability, flexibility, and adaptability; and readiness to act (FEMA, 2016b). A well-established capability to quickly collect, analyze, and further disseminate intelligence becomes critical in imminent-threat situations, and academic research institutions should develop and maintain relationships with local, state, and federal law enforcement partners to benefit from actionable information that can help prevent incidents in their communities before they occur. The prevention of criminal events and acts of terror perpetrated against academic research institutions and their research enterprises will be enhanced through operational coordi-
nation and information sharing with law enforcement, homeland security, and emergency management agencies (FEMA, 2016b). Academic research institutions and their research enterprises should nurture relationships with these partners through their campus police departments, emergency management departments, or designated homeland security liaisons. Having a trusted relationship with these entities is important, as information of this type is most often highly sensitive and distributed only to authorized parties. Established partnerships facilitate the smooth passage of information that can help prevent criminal acts that potentially disrupt the activity of the research enterprise. Academic research institutions and their research enterprises will benefit from the routine exchange of security information with law enforcement agencies. The odds of a catastrophic disaster involving the assets of the research enterprise could be decreased through a mutual awareness of threats, alerts, and warnings, which includes understanding, recognizing, and preventing crimes and other activities that are precursors or indicators of terrorist activity and violent extremism.
The research enterprise can house select high-consequence pathogens and high-risk radiological sources, which may be targets for criminal activity. Risks to laboratory security include (NRC, 2011, p. 256)
- The theft or diversion of chemicals, biologicals, and radioactive or proprietary materials (such materials could be stolen from the laboratory, diverted or intercepted in transit between supplier and laboratory, at a loading dock, or at a stockroom, and then sold or used, directly or as precursors, in weapons or the manufacture of illicit substances);
- The theft or diversion of mission-critical or high-value equipment;
- Threats from activist groups;
- The intentional release of, or exposure to, hazardous materials;
- Sabotage or vandalism of chemicals or high-value equipment;
- The loss or release of sensitive information; and
- Rogue work or unauthorized laboratory experimentation.
FEMA’s National Prevention Framework suggests academic research institutions and their research enterprises should consider maintaining situational awareness of the current threat environment and should assist in preventing terrorism by identifying and reporting potential terrorism-related activity to law enforcement (FEMA, 2016b). They should also consider taking appropriate measures to prevent terrorist acquisition and transfer of chemical, biological, radiological, nuclear, and explosives (CBRNE) materials.
The type and extent of security needed for a particular research enterprise depends on a number of factors, such as regulatory requirements or guidance, intelligence regarding groups or individuals who pose a threat, or the pres-
ence of valuable materials (NRC, 2011). For example, the National Emerging Infectious Diseases Laboratories (NEIDL) at Boston University (BU), which is a biosafety level 4 laboratory, presented its Personnel Reliability Program to the committee; this program discusses the steps and procedures taken to ensure that the laboratory’s personnel are able to contribute to a safe and secure work environment (Mellouk, 2016). The steps and procedures include
- Mitigating the potential risks of theft, loss, and intentional or accidental release of agents by individuals who have been approved for access in a manner that does not impede the progress of science.
- Striking the appropriate balance between personal privacy, safety, and security.
- An initial assessment with an ongoing evaluation and monitoring program.
- Promoting the reporting of safety and security concerns based on a culture of trust, respect, cohesiveness, and responsibility.
- Enabling leadership to make timely operational decisions consistent with the highest standards of personnel reliability.
- Providing tools for the employees to be able to recognize behaviors and conditions that may be detrimental to a safe and secure working environment, as well as creating an environment for reporting such situations in a manner that is supportive and free from fear of reprisal.
- Providing training and guidelines related to monitoring activities and expectations.
- Assessing employees’ behavioral suitability, reliability, and willingness to comply with the heightened security and safety procedures required within the NEIDL.
- Assessing employees’ acceptance of responsibility with respect to safety and security requirements, as well as BU policies and procedures.
- Providing plans for those that are temporarily or permanently denied access to NEIDL facilities.
In laboratories using CBRNE materials, the academic research institution should ensure safe disposal of CBRNE materials consistent with regulations and established protocols. To prevent criminals from acquiring radiological materials, some institutions have identified and acquired alternative technologies to meet the needs of their researchers and have been able to decommission and remove high-risk radiological sources, such as cesium-137 irradiators, from their communities (see Box 5-1). The National Nuclear Security Administration’s (NNSA’s) Global Threat Reduction Initiative has collaborated with academic research institutions
and other private and government partners to enhance existing radiological security and, in some cases, to remove radiological sources altogether. The NNSA has recovered more than 31,000 disused and unwanted radioactive sealed sources in the United States, eliminating more than 1,000,000 curies of activity (NNSA, 2013).
PROTECTION PLANNING
The FEMA National Protection Framework describes what the whole community can do to safeguard against acts of terrorism, natural disasters,
and other threats or hazards (FEMA, 2016c). The chief resilience officer for the research enterprise and the research enterprise planning committee, in coordination with the institution-wide planning committee, should consider the following protection actions during the planning process.
Partnerships and Coordinating Structures
Given that an academic research institution and its research enterprise are large, complex systems that face unique challenges and that have a large array of vulnerabilities, they require a multitude of partnerships. The development of strong community partnerships with both private and government entities to facilitate planning, information sharing, and mutual assistance is also important (Kapucu and Khosa, 2012). The National Protection Framework relies on existing structures to promote integration, coordination, and resilience across various entities (FEMA, 2016c). These coordinating structures include operations centers; law enforcement task forces; the critical infrastructure sector, government, and cross-sector coordinating councils; governance boards; regional consortiums; information-sharing mechanisms, such as fusion centers; health surveillance networks; and public–private partnership organizations (FEMA, 2016c). These partnerships allow for the exchange of expertise and information and provide a source of potential resources through mutual aid agreements. Academic research institutions and their research enterprises should identify relevant coordinating structures locally, regionally, and nationally to facilitate the sharing of timely information and best practices and to coordinate planning and response activities for the research enterprise. For example, under the Emergency Planning and Community Right-to-Know Act, local emergency planning committees (LEPCs) must develop an emergency response plan, review the plan annually, and provide information about chemicals in the community to citizens (EPA, 2016). These plans are developed by LEPCs who include, at a minimum, elected state and local officials; police, fire, civil defense, and public health professionals; environment, transportation, and hospital officials; facility representatives; and representatives from community groups and the media. This is a great opportunity for academic research institutions to participate in planning with the local community.
Partners across the whole community can use the National Protection Framework to inform and align relevant activities designed to enhance security for communities, organizations, and jurisdictions (FEMA, 2016c). Structuring planning, training, exercises, and operations around the protection core capabilities enhances national preparedness (FEMA, 2016c). If possible, representatives from local and state agencies should tour the research facilities. For example, NEIDL’s Comprehensive Emergency Management Plan has been disseminated and reviewed by external agencies that
would likely provide support during an incident (NEIDL, 2014). There may be concerns about information sharing with external parties due to sensitivity about making laboratory details available, in which case the research enterprise should work with its general counsel or legal department to develop guidelines governing the sharing of information with external parties (Durkee, 2013). It is important that local first responders have advance knowledge of the research enterprise planning to understand the unique research environments they may be responding to (e.g., animal facilities, chemicals, or biological agents) and to set response expectations and identify aspects of planning that may need to be revised.
National and international peer networks for academic research institutions and their research enterprises also exist. In 1998, FEMA and the University of California, Berkeley (UC Berkeley) funded research and development for the Disaster-Resistant University (DRU) initiative (Comerio, 2003). UC Berkeley conducted research on hazards identification, modeling of losses, and planning for physical retrofit of buildings and contents, as well as planning for disaster recovery in teaching, research, business resumption, and facilities reoccupation. As the pilot for the national program, UC Berkeley trained five other institutions from across the nation. These institutions were tasked with the job of creating mitigation strategies and plans for their institutions and, upon completion of the program, sharing their best practices (FEMA, 2003). Results from the program yielded a grant program and a handbook, Building a Disaster Resistant University. The affiliated DRU grant program was short-lived, lasting only one funding cycle, and fewer than 20 schools received grant funding for campus mitigation planning (National Disaster Resilient Universities Network, 2015). After the grant program ended, many of the institutions that were funded through the grant program understood the value of institutional disaster preparedness and continued to pursue a nationwide approach to creating disaster-resilient institutions. Additionally, the U.S. Department of Educations funded the Emergency Management for Higher Education (EMHE) grant program which supported institutions’ projects designed to develop or to review and improve and to fully integrate campus-based all-hazards emergency management planning efforts (ED, 2014). The EMHE program awarded more than $7 million annually between 2008 and 2010 to improve emergency management planning at institutions (NCCPS, 2016). Congress defunded the program in 2011. Kapucu and Khosa (2012) found that grant programs have had a positive impact in improving the level of preparedness and resiliency at institutions.
A number of the institutions that participated in the DRU grant program wanted to continue to enhance disaster planning on their campuses. So in 2005, after a national meeting of DRU campuses at the University of Washington (UW), the University of Oregon started the Disaster Resilient
Universities® Network listserv (DRU Network, 2015). The membership listserv was initially designed to be a peer-to-peer network for university and college emergency management professionals and practitioners to be able to share information and engage in discussions and dialogues concerning campus emergency management. The DRU Network collaborates with the International Association of Emergency Managers–Universities and Colleges Caucus (IAEM–UCC). The platform serves as a place for emergency management professionals to share information and technical resources (such as templates, after-action reports, and best practices) and to engage in discussions and dialogue related to institutional emergency management (IAEM–UCC, 2017b). An additional list of partnerships and peer networks is included in Appendix B.
Key Protection Capabilities
The National Protection Framework identifies a number of core capabilities that are necessary to create conditions for a safer, more secure, and more resilient nation and which are germane to the academic biomedical research community (FEMA, 2016c).
Cybersecurity
One core capability for the protection of academic research institutions and their research enterprises is cybersecurity (FEMA, 2016c). Cyber attacks can span a broad spectrum from the high end of threatening critical infrastructure to the low end of intellectual property theft involving data; compromises of personal information such as medical data; and denial of service attacks that prevent rightful users from accessing online resources (Lin and Kerr, 2017). Ransomware, a type of malware that infects computers systems regardless of operating system to extort money from its victims, has increasingly affected institutions over the past several years (Mallard, 2016). While viruses, malware, and other threats have been found in these environments, ransomware can corrupt data and destroy both current and historical data (Mallard, 2016). Lin and Kerr (2017) also discuss another type of cyber attack called information/influence warfare and manipulation (IIWAM). IIWAM operations are activities that seek to affect the information environment in any one, or all, of the physical, informational, and cognitive/emotional dimensions in ways that provide advantages over the adversary.
The National Institute of Standards and Technology Framework for Improving Critical Infrastructure Cybersecurity (NIST Framework) (NIST, 2014), is set of standards, best practices, and recommendations for improving cybersecurity at the organizational level. The academic research institution can use the NIST Framework as a key part of its systematic process for
identifying, assessing, and managing cybersecurity risk. FEMA’s National Protection Framework suggests academic research institutions and their research enterprises should be diligent by not only establishing policies that plan for cyber attacks, but by taking actions to mitigate the risk. Academic research institutions and their research enterprises should protect—and, if needed, restore—electronic communications systems, information, and services from damage, unauthorized use, and exploitation (FEMA, 2016c). Actions for consideration include
- Physically and electronically secure critical cyber networks, applications, and systems from harm.
- Mirror data locally and on a secure site in the cloud to permit access locally when the network is down and remotely when the local site is inaccessible.
- Maintain copies or a long-term archive off-line in different geographic regions, and update sequentially from the working store, with sufficient temporal separation so that a corruption has time to be detected before the oldest copy is overridden.
- Formalize partnerships with cyber incident response teams to facilitate efficient responses to incidents.
- Ensure shared situational awareness of cyber threats with local, state, and federal partners.
- Create resilient cyber systems that allow for the uninterrupted continuation of essential functions and the preservation of irreplaceable data.
Access Control and Identity Verification
The access control and identity verification capability relies on the implementation and maintenance of protocols to verify identity and authorize, grant, or deny physical and cyber access to specific locations, information, and networks (FEMA, 2016c). Surveillance, both internal and external, is an important measure for this capability. FEMA’s National Protection Framework suggests academic research institutions and their research enterprises should ensure that physical, technological, and cyber measures are in place to control admittance to critical locations and systems within the research enterprise before, during, and after a disaster. If an academic research institution is used as a shelter, evacuation center, or first-responder staging area during or after a disaster, it is even more important to ensure measures are in place to control admittance to research facilities. Designating the campus shelter areas as medical-needs-only shelters could limit general public usage and focus on delivering services to individuals who require medical support.
For example, the University of Kentucky (UK) reviewed its state of physical security on campus and found that different colleges and units had varying levels of security on campus (Sorrell and Brown, 2014). UK also found that the security of a facility was not a shared responsibility between the UK Police Department, UK Physical Plan Division, and the individual units. In response to these findings, UK set about to provide each college or unit the opportunity to invest in, expand, and manage its own security system that would be reported and monitored centrally. Installation of this system included access control, security cameras and various alerts to include motion detection on the digesters, gunshot detection, and basic alert notifications for propped doors and access granted or denied. Due to limited resources only a number of prioritized buildings were selected; however, all new security devices on campus were required to integrate with the new system. The project also identified a building security authority in each building, who was responsible for determining the public and nonpublic areas and operating times of the facility, setting the schedules and access rights, and, in concert with officials, determining the appropriate alerts based on the security threats in and around the facility.
Physical Protective Measures
Developing the physical protective measures capability requires academic research institutions and their research enterprises to implement and maintain risk-informed actions and policies to protect researchers, research-related assets, and systems associated with key operational activities (FEMA, 2016c). Comerio (2003) lays out a method for assessing risks and mitigation hazards specifically in laboratory contents. This report also describes the methodology (i.e., analyzing space usage, surveying the building contents, evaluating each item in terms of life safety hazards, and coding all items that scientists labeled as critical to research options) used to inventory and assess laboratory contents.
Most physical protective measures related to the research enterprise are good work practices that strengthen overall operations. Laboratory safety is an important part of the research enterprise, and training requirements for researchers are established by regulatory agencies, including the Occupational Safety and Health Administration, the Centers for Disease Control and Prevention, and other groups, and also by internal institutional guidelines (NRC, 2011). Appendix C contains a discussion of relevant laws, regulations, and standards for the research enterprise. Laboratory safety contributes to disaster resilience, and researchers should recognize the importance of maintaining a culture of compliance and strive to practice safe work practices in their day-to-day duties in order to minimize the cascading effects that typically follow a disaster.
In addition to the high-level strategies and planning efforts described in this report, individual researcher-based efforts are essential to achieving academic biomedical research community resilience. The committee found that while institutions as a whole are undertaking disaster planning, researchers, rarely, if ever, consider what might happen to their research should a disaster occur. Each researcher in a laboratory influences the culture of resilience there. Researchers should understand that if a significant cascading event occurs in the laboratory because hazardous agents or chemicals were released during a disaster, the damage will be escalated, recovery will be more complicated, and the laboratory will experience increased downtime (NRC, 2011). By following safe work practices and policies, researchers can decrease the likelihood of such an event occurring. Principal investigators (PIs) should note that a vital component of education is teaching research students how to identify the risks and hazards in a laboratory (NRC, 2011). Trained and conscientious workers thus help to increase the internal response capabilities at their institution.
Having robust procedures in place pre-disaster to identify and protect critical research-related assets, including data, samples, reagents, and specialized research equipment, is a key factor determining whether research can be conducted after the disaster (protection of research animals is discussed in more detail in Chapter 7). PIs could work to ensure that all research staff and students in the laboratory adhere to these standards and expectations in order to protect critical research-related assets. These expectations could be reviewed at orientation for new personnel and at least annually for all staff.
All written and electronic research data and laboratory records that have been determined to be critical should be regularly updated and protected with adequate security procedures, and backups should be maintained in separate geographic locations (FEMA, 2003). The research enterprise should document where data are stored, the method of storage, and the frequency at which data backups are conducted along with instructions for retrieving data from these backups (Mische and Wilkerson, 2016). Documented standard operating procedures (SOPs) that provide written instructions describing the procedures’ steps, required materials, potential hazards, and appropriate work practices are essential for business continuity. SOPs could be available in electronic and hard-copy formats. To ensure this practice is effective, it is important for staff members to be familiar with the contents of the SOPs and where they are located.
Researchers could consider using an electronic recordkeeping system to systematize and automate portions of the inventory and description process (e.g., an electronic laboratory notebook, or ELN). As much as is possible and practical, researchers should choose to store data centrally, where (ideally) it can be properly managed, systematically backed up with
copies stored offsite, and so on (CUNY, 2010). Researchers should store locally only that data they can afford to lose (e.g., temporary, working files) (Macrina, 2014). Best practices, including the effective use of technology (e.g., ELNs), should be encouraged. The institution and its research enterprise could provide researchers with incentives to make maximum use of central data storage options, if available at the institutional level. If institutional data storage solutions are not available or are too limited or costly, the research enterprise could work with deans and PIs to develop a department-level shared data storage option, to the extent possible. The department administration could encourage the use of a laboratory information management system (LIMS) among laboratories, if the institution supports such a system and resource (Mische and Wilkerson, 2016). LIMSs are increasingly providing software that supports remote monitoring and the use of core instruments. The research enterprise could determine which operations can be conducted remotely, the staff’s capability for conducting remote options, and the institution’s capabilities for supporting these activities (Mische and Wilkerson, 2016). The research enterprise could encourage adherence to adequate recordkeeping and the use of advanced techniques and technologies and should build these practices into the culture and expectations for the success of the laboratory. The sharing of best practices among laboratories regarding recordkeeping and the security of research data should be encouraged. Yale University developed the following checklist of business continuity considerations for critical documents and information technology (IT) (Yale University, 2016):
- Ensure that research notes, notebooks, letters, documents, spreadsheets, etc., are backed up to a network drive every day.
- Keep duplicate copies of irreplaceable notes, notebooks, manuscripts, and other documents in a safe location away from the laboratory or usual worksite.
- Regularly scan and save these items onto a network drive or onto an encrypted USB storage device.
- Regularly back up all information stored on laptops and tablets.
- The institution should offer assistance with data backup. It can provide guidance about available solutions to back up an entire department’s computers or just a single unit.
- Laptops should be routinely backed up, either to a network server or an encrypted USB storage device.
- Maintain a list of vital documents, files, and folders and include how they are backed up.
- In the event of a network problem in which software or files cannot be accessed, contact the department IT specialist or the IT help desk for assistance.
- Keep duplicate copies of important documents stored in a secure offsite location or on an encrypted USB storage device.
It is important to maintain current inventory, including a minimal description, of critical research samples and reagents, along with information about where they are located (Mische and Wilkerson, 2016). An accurate inventory is essential, particularly if there is a disaster. The research enterprise could implement policies to enable the duplication of critical samples. For example, the research enterprise could provide designated freezers and liquid nitrogen storage containers, and these duplication freezers should be located within a secure area of a well-constructed building. Mische and Wilkerson (2016) stress the importance of cryopreserving transgenic lines and storing biomaterials offsite to ensure research continuity and to protect samples for future awards and collaborations. Yale University developed a checklist of business continuity considerations for critical samples (Yale University, 2016):
- Maintain accurate inventory records for unique specimens and materials.
- Properly maintain and service all equipment and devices that secure these materials.
- Develop redundant storage for irreplaceable specimens (animals, plants, cell lines, DNA, etc.), if possible; preferably the storage should be both on- and offsite to maximize protection. Splitting the storage of vital specimens—separating the specimens, and storing separate collections in different locations—should be considered.
- Develop emergency procedures that specify what to do with specimens and how to shut down workstations and the laboratory in the event of a disaster or major disruption.
Another issue of great concern is the possibility of freezer loss. The research enterprise could identify freezer protection as one of its priorities and could develop actions to minimize loss. For example, the freezers could have emergency backup power, could be connected to electronic temperature monitoring equipment, and could be prominently labeled to make them easily identifiable. Adequate supplies of refrigerants (dry ice and liquid nitrogen) could be kept on hand or stored nearby at all times, which will enable the pre-loading of freezers and storage containers with the suitable type of refrigerant when a disaster can be forecast (e.g., a hurricane). Yale University developed the following checklist of business continuity considerations for a loss of power (Yale University, 2016):
- Be familiar with the emergency backup power system(s) for the area, including what is covered and how long the backup power can be relied upon. Contact the facilities manager or superintendent if unsure about backup power for the location.
- Verify that freezers, refrigerators, incubators, and other temperature-sensitive equipment holding critical materials are connected to an emergency power supply, if available for the lab. Consult with the facilities manager or superintendent before connecting equipment to emergency power outlets to avoid overloading circuits.
- Install an uninterruptible power supply (UPS) for equipment that is highly sensitive to slight power delays or fluctuations.
- Know how long freezers, refrigerators, incubators, etc., that are not connected to an emergency power supply will maintain proper temperatures in the event of a power failure.
- Maintain a list of essential equipment that may be damaged by a power surge when the power is restored.
- Maintain a list of essential equipment that may have an automatic “on” switch and may come on by itself when power is restored, even if no one is around. Consider unplugging or turning off this equipment during the outage to avoid harmful effects when the power returns.
- Identify equipment that may need to be reset or restarted when the power is restored. (i.e., centrifuges, computers, fume hoods, etc.).
- Maintain a list of all temperature-sensitive specimens in each location and the approximate time limit before the specimens will be adversely affected by a temperature change. This will help prioritize the relocation of specimens, if that is necessary.
- Ensure that the seals on freezers are intact. Most freezers will keep their temperature steady or below freezing for up to 10 hours if they are kept closed and properly sealed.
- Identify other freezers in the laboratory or neighboring labs that may have their own backup power or run on CO2 or liquid nitrogen which may be unaffected by a power outage, and discuss the possibility of sharing space in these freezers if necessary.
- Store or know where it is possible to easily obtain dry ice and coolers in the event of a prolonged outage.
Mitigating the impacts of disasters to research equipment is also prudent (NRC, 2011). Researchers could keep purchasing and other records that would be helpful for an insurance claim (refer to Chapter 9 for additional information). If equipment can be replaced, make note of where to find that equipment and the specifications needed. For custom-made equipment, keep the plans that show how it was built in case it needs
to be rebuilt. Make note of other laboratories or institutions with similar equipment or functions, and make arrangements, if possible, to use such facilities as a backup, if needed. For example, the strong shaking from earthquakes requires a research building and laboratory to be sufficiently earthquake resistant and the interior equipment and content to be adequately anchored and braced. Stanford University has implemented the ProtectSU Seismic Restraint Program to prevent the loss of high-value (purchase price > $20,000) laboratory equipment due to a seismic event (Stanford University, 2016). This program consisted of restraint guidelines, a matching-fund program for constraints, and a requirement for a universal restraining bar included in the facility design guidelines. Yale University developed the following checklist of business continuity considerations for specialized research equipment (Yale University, 2016):
- Maintain a list of specialized equipment that the laboratory relies on. Include information such as make, model, serial number, and where it was purchased.
- For equipment purchased through the procurement office, determine if the information is still maintained in their system.
- Determine if the building in question has alternate backup emergency power, such as a generator.
- Determine if critical equipment is connected to backup or emergency power.
- For highly customized equipment or experimental apparatus, keep duplicate copies of drawings, diagrams, plans, or specifications in a secure offsite location. Scan information if possible, and store offsite or on an encrypted USB storage device.
- Identify equipment with special utility requirements, such as process-chilled water, high voltage, and three-phase power.
- Ensure that equipment warranties and extended service and maintenance contracts are in force and kept up to date.
- Establish or adopt industry recommendations for routine calibration, testing, and preventive maintenance, and ensure that these get done.
- Keep copies of the inventory readily accessible in multiple locations.
Risk Management for Protection Programs and Activities
The risk management for protection programs and activities core capability requires academic research institutions and their research enterprises to identify, assess, and prioritize risks in order to inform activities and investments (FEMA, 2016c). One way this could be accomplished is through a process called enterprise risk management (ERM). ERM is a holistic
approach to risk management that provides a framework for entity-wide risk identification, the prioritization of key exposures, and the development of operational responses to adverse events, based upon a foundation of ownership, accountability, and transparency (Klein, 2016). ERM is discussed in further detail in the mitigation planning section below.
Supply Chain Integrity and Security
FEMA’s National Protection Framework suggests the research enterprise should strengthen the resiliency of its supply chain, to ensure integrity and security (FEMA, 2106c). Given that outside assistance will not likely be immediately forthcoming after a disaster, there must be a plan in place to procure and access research-related resources when needed in an emergency. The research enterprise could hold advance discussions with essential suppliers and consider establishing mutual aid agreements (MAAs) or memorandums of understanding (MOUs)1 to facilitate the delivery of appropriate research-related resources at the time of request. The research enterprise could also identify critical vendor and support service contact information and keep this information in hard-copy and electronic format. It is common for institutions to have established MAAs/MOUs for police, fire, and medical emergency support, but it is less common to have established MAAs/MOUs for research operations (Mische and Wilkerson, 2016). For example, IAEM-UCC developed the National Intercollegiate Mutual Aid Agreement (NIMAA),2 which is a source for academic research institutions who are providing and receiving assistance (IAEM-UCC, 2017a). MAAs/MOUs are predicated on the acknowledgment that one institution may not have all the resources needed to respond to an incident, and they may include provisions for requesting or providing the use or loan of facilities, equipment, or personnel in a variety of disciplines, including police, human resources, and crisis communications as well as direct access to resources at the other institution or from government agencies.
MAAs and MOUs can include a specific formal request, delineate who is in charge of overseeing operations, outline the level and type of services required, include and specify financial obligations, and help to formalize expectations in partnerships (Kapucu and Khosa, 2012). The implementation of pre-disaster mutual aid or advanced contracting arrangements
___________________
1 A memorandum of understanding (MOU) differs from a mutual aid agreement (MAA) in that a MOU is not necessarily a mutual benefit agreement. A MOU and MAA are both written noncontractual agreements between parties. If a research enterprise is considering drafting an MOU or MAA with external entities, it is recommended that this be discussed with the institutional legal counsel. The counsel can provide guidance on what is appropriate for inclusion (ZAHN, 2011).
2 NIMAA Fact Sheet, see https://public.3.basecamp.com/p/uqmGVP624NNMaERgUk4fQPqd.
provides both the institution and its research enterprise opportunities for obtaining specific expertise to augment existing staff for general recovery management, data management, specialized laboratory equipment repair, hazardous materials assessment and abatement, risk management for damage, and other claims management, among many other functions.
Other critical recovery resource networks to be developed before the disaster could include research space; the sharing of equipment and research core facilities with other academic research institutions (see Box 5-2); offsite storage of data, research supplies, and research materials; and life-sustaining services, which include accommodations, food, water, and other essential needs, for the affected population (APA, 2014). A majority of the planning considerations for life-sustaining services should be addressed in the institution-wide plan.
The research enterprise could request to be established as a priority customer for whom deliveries will be assured, dependent on the capability of the supplier (Roble et al., 2010). Research facilities could also establish MAAs/MOUs with critical equipment companies to supply maintenance and repair during a disaster. By pre-identifying critical resources and having a plan to access them immediately after a disaster, research enterprises increase the likelihood that they will be able to procure these resources in a timely fashion. The University of California (UC) created a MOU that includes all UC campuses and the Lawrence Berkeley National Laboratory. The MOU agreement states that the individual laboratory care units of each of the UC campuses agree to provide mutual aid and contingency services to each other on a voluntary basis when reasonably possible when the well-being of research animals is at stake (UCOP, 2013).
A disaster could force research operations to relocate (as seen in Chapter 2). The fact that New York University Langone Medical Center (NYU Langone) cores were providing research services within 2 weeks of Hurricane Sandy was attributed to the welcoming partnership extended by Rockefeller University, Memorial Sloan Kettering, the Mount Sinai School of Medicine, the Weill Cornell Medical Center, Rutgers University, and the New York Genome Center (Mische and Wilkerson, 2016). Academic research institutions should identify minimum alternate site requirements needed to resume operations and consider developing partnerships with other institutional departments and external laboratories or institutions that conduct similar research or use similar equipment (Yale University, 2016). Yale University developed the following checklist of business continuity considerations for essential vendors (Yale University, 2016):
- Identify specialized supplies that you rely on. This includes supplies that are difficult to obtain, require special authorization or handling, or are only available from limited vendors.
- Identify key vendors of essential equipment, supplies, and service contracts. Contact your business office to request a report of your recent purchases.
- Develop contact lists including routine and emergency after-hours contact information.
- Identify an alternate backup vendor for essential must-have items.
- Where feasible, increase standing inventories of crucial supplies and reagents, especially those that typically rely on just-in-time ordering.
- Review and update all contact lists on a regular basis.
- Keep copies of contact lists readily accessible in multiple locations. Share with others in your lab.
- Have a conversation with your suppliers about their business continuity plan. Propose the same scenario and ask how they plan to maintain deliveries of supplies following a disaster or other interruption to their business.
MITIGATION PLANNING
This section will focus on some of the long-term actions that academic research institutions and their research enterprises can implement to enhance resilience. FEMA defines hazard mitigation planning as “any sustained action taken to reduce or eliminate long-term risk to people and property from natural hazards and their effect” (FEMA, 2015, p. 1). One of the primary functions of mitigation planning is to enable the research enterprise to identify and diminish risks prior to a disaster so as to directly limit the impact of a disaster should one occur (FEMA, 2016a). Working from
an understanding of risk, priorities should be set and long-term strategies should be developed to avoid or minimize the undesired effects of disasters. Successful hazard mitigation plans increase awareness about hazards, build partnerships, and focus available resources on the most vulnerable areas of the community.
An important concept of hazard mitigation planning is that no threat or hazard exists in isolation. And while history has shown that there are seemingly an unlimited number of disasters that can occur, the effects of many of them will produce a similar set of problems in the affected community (refer to Chapter 2). For example, an ice storm, an influenza pandemic, and a flood may all disrupt the ability of employees to report for work. By using an all-hazards approach, planners focus on developing a framework that addresses essential functions and services.
Hazard mitigation actions for the research enterprise can involve such strategies as planning, policy change, and project prioritization, among others (University of Iowa, 2010). The research enterprise planning committee led by the chief resilience officer for the research enterprise, in coordination with the institution-wide planning committee, could develop a “master list” of all mitigation action strategies related to the research enterprise that could be implemented with unlimited resources. The research enterprise planning committee could assess the cost-benefit relationships and the overall feasibility of mitigation actions. The highest priority could be placed on feasible mitigation actions connected to high-priority hazards.
Mitigation actions for the research enterprise can be obtained from other academic research institutions and local, state, and federal agencies (e.g., FEMA publications such as Mitigation Ideas and Developing and Promoting Mitigation Best Practices and Case Studies). Funds from FEMA’s Hazard Mitigation Grant Program (HMGP) are available for a wide range of mitigation activities following a federal disaster declaration (FEMA, 2017). The funds are open to the entire state, rather than just the community and facilities within the declared disaster area. However, to be eligible for these funds a jurisdiction must have a FEMA-approved mitigation plan (see Box 5-3). To help fund the mitigation planning process, qualifying institutions may be able to apply for funds through FEMA’s Flood Mitigation Assistance Grant Program or Pre-Disaster Mitigation Grant Program. Additional funding pathways are discussed in Chapter 9. Many of the mitigation actions related to long-term vulnerability reduction, such as capital improvement planning; actions relating to the built environment, finances, and insurance, and the actions of research sponsors, are discussed in detail in Chapters 8, 9, and 10.
FEMA’s National Mitigation Framework employs a risk-based approach to reduce loss of life and property and to increase community resilience (FEMA, 2016a). By reducing risk, mitigation activities reduce
the resources needed to respond to and recover from disasters. Effective mitigation begins with risk identification, in which a community identifies the threats and hazards it faces and the likelihood of their occurrence. The community then conducts a vulnerability assessment to understand the effects that these threats and hazards would have if they occurred. Chapter 4 discusses the risk assessment process in more detail. Based on this understanding of risk, a community can choose one or more risk management strategies, including
- Risk avoidance—Preventing exposure to an event (e.g., using zoning laws and other standards to prevent the construction of homes in high-risk areas).
- Risk reduction—Minimizing vulnerabilities (e.g., retrofitting buildings to be more resistant to earthquakes).
- Risk transfer—Eliminating or limiting financial liability, without reducing vulnerability (e.g., purchasing insurance).
- Risk acceptance—Tolerating any remaining risk and liability (e.g., agreeing to pay a deductible) (DHS, 2015, p. 38).
In this section, the committee explores the concept of the enterprise risk management process as a strategy for risk assessment and management and
how business continuity planning contributes to mitigating the effects of a disaster on the research enterprise.
Enterprise Risk Management
To manage potential threats, an academic research institution can work from a basic operational level upward to fine-tune a strategy for mitigation using a process called enterprise risk management (ERM). ERM is defined as
a holistic approach to risk management that provides a framework for entity-wide risk identification, prioritization of key exposures, and development of operational responses to adverse events, based upon a foundation of ownership, accountability, and transparency. (Klein, 2016)
Emory University describes an ERM process, tailored to the needs of the academic institution, as enabling the institution to “manage its risk, prepare for adverse occurrences, and ensure that senior management is communicating with those in the field about key issues facing the university” (Klein et al., 2008). Emory University defines five objectives for its ERM process:
- Identify the risks that could significantly interfere with the university’s mission.
- Assess the major risks and identify vulnerabilities to determine whether investment in additional resources is warranted to mitigate it.
- Detail a plan for operational and communication responses to potential adverse events.
- Build processes to implement these plans.
- Eliminate surprises.
The ERM organizational structure engages executive leadership, senior administrators, operational managers, and subject matter experts to create an executive committee, a steering committee, and subcommittees focused on a broad range of risks (Klein, 2016) (see Figure 5-2). The research enterprise is represented in the ERM organizational structure. Each group is assigned a distinct scope of work. The executive committee, composed of the university president, executive vice presidents, and other members of the president’s cabinet, hears reports about the entire range of risks that are annually selected for review, and it has the authority to redirect the priorities of the ERM program. The steering committee is composed of senior administrators and functions as the core working group for the ERM process and coordinates the activities of the subcommittees. Members of
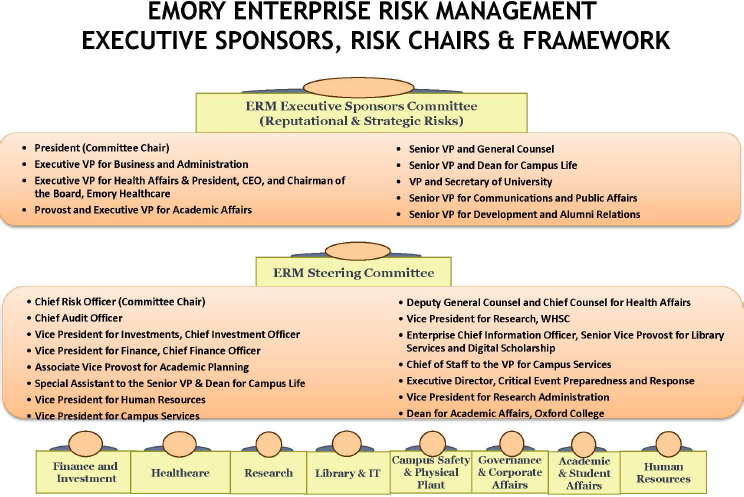
SOURCE: Klein, 2016.
the subcommittees are those who identify, analyze, and communicate about risks in their respective areas. This model is broadly inclusive of individuals both vertically and horizontally in the institution’s organizational structure, which fosters shared ownership and accountability (Klein et al., 2008).
The team then embarks on identifying the broad range of risks facing the institution, focusing on operational risks (strategic risks were considered later as the program matured). Each subcommittee convenes to create a comprehensive list of operational risks faced in each of their domains. By examining the risks and weighting them based on a scheme that estimates the likelihood of occurrence as well as the impact on the institution’s operations, the top risks are identified and presented to the executive committee.
To prepare for an executive presentation, a risk management process owner (RMPO) is identified. This individual is defined as the person on campus “sufficiently familiar with the risk and best positioned to execute a comprehensive risk management plan” (Klein et al., 2008). This individual is charged with creating a two-page plan that describes:
- The risk, its components, and examples;
- Steps being taken to manage the risk at an acceptable level;
- The operational response to an adverse event; and
- The communications plan for an adverse event (Klein, 2016).
The RMPOs annually present each of the risks to the executive committee in a face-to-face risk hearing, which occurs quarterly (Klein et al., 2008). While the time for each presentation is brief, this hearing provides a unique opportunity for executive leadership to hear directly about a range of risks from the operations-level personnel most knowledgeable about the issues. At the conclusion of the hearings the executive committee considers any gaps in the state of risk exposure and the institution’s risk tolerance, and the RMPOs are directed to prepare action plans to close the gaps. The goal is not to eliminate all risk, which would be paralyzing, but instead to accept risk judiciously, mitigate it when possible, and ensure a robust ability to respond in the event of an occurrence.
The ERM process is an effective adjunct to other activities (e.g., emergency management and business continuity planning) aimed at mitigating the effects of a disaster. The ERM framework affords an opportunity for the discussion of low-probability, high-consequence events, such as earthquakes, floods, or infectious disease pandemics. It creates a forum where these issues are discussed annually with executive leadership, who then have the opportunity to consider whether the institution is managing this risk at an acceptable level and, if not, to consider an action plan to better manage the risk (Klein et al., 2008).
Klein (2016) noted in her presentation to the committee that the framework is also flexible in allowing a more detailed examination of related issues. For example, a regional power outage may be broadly considered among the many low-likelihood, high-consequence hazards the institution at large is preparing to manage, but it can also be considered in a more granular fashion by another RMPO who is charged with examining the risk to the institution as a consequence of the loss of essential utilities or the loss of IT infrastructure. An earthquake can be broadly considered in a catastrophic-event risk management plan or be more granularly addressed by a group examining the security of highly sensitive radioisotopes and select pathogens. In the context of the research enterprise, a hurricane can be examined on the basis of the risk it poses to the security of irreplaceable research-related assets and the ability of the institution to recover and remain competitive for critical research funding in the research domain while also being examined in terms of risks to life and safety in the campus safety domain. The ERM process affords a platform for the integrated management of these risks, in contrast to a fragmented effort across various operational silos in the absence of a holistic ERM program (Shenkir and Walker, 2008).
Klein (2016) attributed the success of Emory’s ERM program in better managing the institution’s risk to the following characteristics of the ERM:
- Top-down driven.
- Engaged leadership.
- Broad-based ownership.
- Roles and responsibilities established prior to adverse events.
- Principled action.
- Transparent communication.
- Consistent messaging.
- Common sense.
Business Continuity Planning
The research enterprise is operating in a complex risk environment where, although people and animal life safety remains the highest priority, the concurrent protection and recovery of the infrastructure lifelines that research needs on an hourly and daily basis are also a very high priority.
In many ways, cores are small businesses that commonly are operated under the umbrella of a centralized core administration. To be successful, core directors and managers must keep their business running on a daily basis despite all the various exigencies and impediments that arise even in the absence of a disaster. Although this may not be formally acknowledged as business continuity planning, it is business continuity. What seems new is the recognition that academic institutions and research centers are also businesses that need to engage broadly and seriously in business continuity planning. (Mische and Wilkerson, 2016, p. 10)
Business continuity planning is the process by which critical operating functions and the risks that threaten them are identified, plans are developed for the recovery of these functions in priority order if they are compromised, and reviews and exercises to facilitate the plan’s continuous improvement are conducted (Hanover Research, 2010). The business continuity planning process informs disaster recovery strategies and potential investments in prevention and mitigation strategies, such as the relocation of critical infrastructure from high-risk areas. By embarking on business continuity planning, academic research institutions are acting to limit their losses in the case of a disaster and limit the impact of disasters on their research operations.
Business continuity plans (BCPs) will be unique for each institution and its research enterprise (Hanover Research, 2010). Developing BCPs requires determining what in the research enterprise is needed in order to deliver at least the minimum level of service and functionality. When
considering BCPs for a research enterprise, it is important that functions critical to the research enterprise are addressed and supported by the institutional plan. The definition of what constitutes the research enterprises’ critical or less critical functional operations or capabilities is a key outcome of each institution’s business continuity planning process.
- Safety and security—Functions that support the safety and security of students, staff, faculty, and visitors, including the university police, emergency notification systems, emergency medical services, food service, and housing.
- Business support services—Functions that support vital business functions such as payroll, procurement, accounts receivable, etc.
- Learning, education, and research—Functions associated with the academic mission of the university such as admissions, academic and research programs, etc.
The prioritization of the recovery of functions is determined based on the consequences of function disruption or failure and the tolerable downtime for each function. Business continuity planners for the research enterprise should be aware of the typical prioritization of recovery of business functions for the broader institution as determined by the consequences of function disruption or failure and the tolerable downtime for that critical function (Hanover Research, 2010).
Vogelweid (1998) wrote that from her team’s experience in developing plans for academic laboratory animal programs, the planning process fostered a realization that the impact of disaster on research business functions could be greatly reduced by planning ahead—“mitigation activities are a natural outgrowth of the planning process” (p. 56). Simple changes can protect against substantial losses and facilitate a rapid recovery. Table 5-1 provides an example of the evaluation of the essential services of the research enterprise as well as the allowable downtime and priority for recovery (Hanover Research, 2010).
The following factors have been cited as influencing the success of business continuity planning (Hanover Research, 2010):
- Identification of a highly and centrally placed leader with the authority to ensure engagement across the institution, who can serve as an objective facilitator of the process by which critical functions are identified and continuity plans are drafted.
- The support and endorsement of the executive leadership of the institution to ensure broad institutional participation and adequate funding.
TABLE 5-1 Critical Business Processes, Research
| Business Unit | Business Process/Business Function | Allowable Downtime | Priority for Recovery |
|---|---|---|---|
| ORAA | Pre-proposal routing and review | 1 day | High |
| ORAA | Electronic proposal/data submission | 1 day | High |
| ORAA | Electronic data entry | 2 days | Medium |
| ORAA | Electronic data management | 2 days | Medium |
| ORAA | Campus outreach | 5 days | Low |
| IACUC/LAC | Animal care and welfare | 1 day | High |
| IRB | Review and approval of applicable research proposals | 2 days | Medium |
| VPR | DRIF requests/research council activities | 5 days | Low |
| OTC | Intellectual property protection | 5 days | Low |
| IGS | Outreach to UM and the State | 5 days | Low |
NOTE: DRIF = Designated Research Initiative Fund; IACUC = institutional animal care and use committee; IGS = Institute for Genome Sciences; IRB = institutional review board; LAC = laboratory animal care; ORAA = Office of Research & Administration Advancement; OTC = Office of Technology Commercialization; UM = University of Maryland; VPR = vice president for research.
SOURCE: Hanover Research, 2010.
- A communications plan that reinforces the importance of the business continuity planning process for broadly pursuing the institution’s academic mission.
- Clear and straightforward documentation of the plan that is accessible to all participating operating units, avoiding overly burdensome and complex structure and language.
- Testing and refinement of the business continuity plan to accommodate changing technology, personnel, and institutional priorities.
Departments and operating units are the most knowledgeable about the resources (e.g., personnel, equipment, space, and critical infrastructure) required to perform critical functions. Senior leadership and the individuals whose operating units are responsible for the performance of critical research functions should share accountability for business continuity for the research enterprise. As the individual most knowledgeable about the critical functions within the research laboratory environment, it is important for the PI to provide leadership in developing and implementing BCPs. For example, UK relies on building emergency coordinators to complete departmental BCPs and building emergency action plans (BEAPs) (UK, 2012).
BEAPs are required by the Occupational Health and Safety Administration for evacuation and sheltering instructions.3 BCPs lack having federal and oftentimes state mandates, like those of BEAPs. However, in an effort to better prepare, institutions can develop policies to mandate business continuity planning. For example, at UW, executive leadership established policy in 2007, mandating business, academic, and research continuity planning (UW, 2007).
Northwestern University’s research continuity planning is facilitated by subject matter experts housed within the university’s Office of Business Continuity Planning working closely with research department chairs, faculty, students, and staff. The departments receive technical assistance to (1) develop principles, policies, and procedures for resuming business/financial and research operations following a disaster; and (2) outline and quantify the potential financial impacts should research activities be interrupted or damaged by a disaster (Northwestern University, 2017). UK uses a BCP departmental template which assists individual research departments in developing their specific plans and supports exercises to maintain and improve those plans annually (UK, 2012). Memorial Sloan Kettering has identified institutional business continuity activities for its 200 principal investigators working in 500 individual research laboratories with the intentional focus on the researcher’s career: “Safeguard your life’s work” (Neufield, 2016). Yale University has developed a video and quick-start guide that explains the basic concepts of a business continuity plan and the steps to take to develop a plan for research laboratories (Yale University, 2016).
Key business continuity plan deliverables by PIs may include the maintenance of current, accurate inventories of all research-related assets that could expedite the post-disaster recovery of the laboratory. A research-related assets inventory could include each item, a minimum of two or more vendor sources for each item, and the estimated purchase cost per item. Additional activities undertaken by PIs include assisting in the development of measures to get laboratory staff back to work as soon as possible—even if they must work at an alternative location. The research enterprise could identify alternative spaces, facilities, and equipment requirements and seek confirmation that arrangements for alternative facilities are funded and allocated.
All in all, after Hurricane Sandy, NYU Langone stressed the following when it came to business continuity planning (Mische and Wilkerson, 2016):
- Robust communication.
- An up-to-date inventory of supplies and services.
___________________
3 29 CFR § 1910.38, Occupational health and safety standards: Emergency action plans. See https://www.osha.gov/pls/oshaweb/owadisp.show_document?p_table=STANDARDS&p_id=9726.
- Knowledge of minimum space and power requirements.
- Cross-training and relationships with peer institutions.
- Caring for staff, and ensuring their safety and well-being.
- Implementing a mandated and supported cryopreservation policy for all transgenic lines.
- Implementing an institutional cold-storage policy, as offsite storage of all precious biomaterials is crucial to a timely recovery of research operations.
CONCLUDING OBSERVATIONS
Resiliency can be characterized by an academic research institution’s ability to minimize the impact of probable hazards and limit their interruption to its research enterprise, and this chapter highlights the importance of undertaking prevention, protection, and mitigation planning activities to strengthen resilience.
To address the prevention area, academic research institutions and their research enterprises should have a mechanism in place for developing relationships with local, state, and federal law enforcement and emergency management agencies in order to facilitate the smooth passage in either direction of information that could prevent a terrorist act that threatens the research enterprise or broader community.
Academic research institutions and their research enterprises should plan to protect (and, if needed, restore) electronic communications systems, information, and services from damage, unauthorized use, and exploitation. Academic research institutions and their research enterprises should ensure that physical, technological, and cyber measures are in place to control admittance to critical locations and systems within the research enterprise before, during, and after a disaster. The development of strong community partnerships with both private and government entities to facilitate planning, information sharing, and mutual assistance is crucial. Partnerships offer opportunities for the alignment of resources and innovation. Academic research institutions and their research enterprises should reach out to peer networks and associations to receive peer support for their disaster planning efforts and should hold advance discussions with essential suppliers and consider establishing MAAs/MOUs to facilitate the delivery of appropriate research-related resources at the time of request.
Develop, Enhance, and Leverage Local, State, and National Partnerships
RECOMMENDATION 3: Academic research institutions should actively engage with key local, state, and national agencies to establish a mutual understanding of the unique disaster resilience efforts necessary
for the research enterprise. Local agencies with the delegated authority to respond during a disaster should understand the unique laboratory conditions. In the event of disaster, the research enterprise’s resources could prove valuable to the local community.
Possible actions could include, but are not limited to
- Identifying a method of engagement with external community partners such as the local emergency planning committee, emergency management, law enforcement, fire, public works, weather service, department of transportation, and others.
- Developing a mechanism to engage the local emergency operations center.
- Establishing partnerships with suppliers and peer institutions so that crucial resources (e.g., food, water, emergency generator fuel) can be directed to the institution promptly following an interruption of normal supply channels. Examples of formal agreements include mutual aid agreements and memoranda of understanding.
- Developing a mechanism for peer institutions to engage in proactive dialogue about disaster management and resilience and to foster communication and transparency between institutions.
- Carrying out exercises together on a regular basis.
One of the primary functions of mitigation planning is to enable the academic research institutions and their research enterprises to identify and diminish risks prior to a disaster and to directly limit the impact of a disaster should one occur. Hazard mitigation planning, enterprise risk management, and business continuity are all approaches to mitigation planning that the academic research institution should consider implementing. The research enterprise planning committee led by the chief resilience officer for the research enterprise, in coordination with the institution-wide planning committee, should develop a “master list” of all mitigation action strategies related to the research enterprise that the academic research institution could implement with unlimited resources. In this chapter, the committee explored the concept of the ERM process as a strategy for risk assessment and management and how business continuity planning contributes to mitigating the effects of disaster on the research enterprise. To manage potential threats, an academic research institution and its research enterprise could work from a basic operational level upward to fine-tune a strategy for mitigation using a process called ERM. The business continuity planning process informs disaster recovery strategies and potential investments in prevention and mitigation strategies, such as the relocation of critical infrastructure from high-risk areas.
Conclusion: Besides best practices and recommendations, BCPs lack having federal and oftentimes state mandates. In an effort to better prepare, institutions could explore the possibility of developing policies to mandate business continuity planning for the research enterprise.
Individual researcher-based efforts are essential to achieving resilience in the academic biomedical research community. The committee found that while institutions as a whole are undertaking disaster planning, researchers rarely, if ever, consider what might happen to their research should a disaster occur (Mintzer et al., 2013). The researcher is the key element around which the academic research institution must build its support structure. Each researcher influences the culture of resilience in the laboratory. Whether researchers have robust procedures in place pre-disaster to identify and protect research-related assets, including data, samples, reagents, and specialized research equipment is a key determinant of whether future research can be conducted after the disaster.
Conclusion: As the individual most knowledgeable about the critical functions within the research laboratory environment, it is important for the PI to consider participating and providing leadership in the development and implementation of disaster resilience policies, plans, and procedures, such as BCPs.
Ensure the Preservation of Research Data, Samples, and Reagents
RECOMMENDATION 4: Principal investigators should work with their academic research institution to safeguard and preserve critical research data, samples, and reagents. As stewards of their research and creators of the valuable intellectual property of their academic research institutions, principal investigators should play a pivotal role in protecting the intellectual assets of their academic research institution through the development and implementation of policies, plans, and procedures related to disaster resilience. Academic research institutions should work to increase incentives for off-site storage and the duplication of critical samples and data. Protecting the research data, samples, and reagents of the research enterprise is ultimately the responsibility of both the principal investigator and the academic research institution.
Possible actions could include, but are not limited to
- Developing and implementing plans, policies, and procedures to ensure operational continuity.
- Ensuring critical research data are backed up using reliable, tested, and secure methods.
- Documenting and backing up research methodology.
- Storing selected duplicate samples in a remote location.
REFERENCES
APA (American Planning Association). 2014. Planning for post-disaster recovery: Next generation. Planning Advisory Service (PAS) report 576. http://www.fema.gov/media-library-data/1425503479190-22edb246b925ba41104b7d38eddc207f/APA_PAS_576.pdf (accessed September 7, 2016).
Comerio, M. 2003. Seismic protection of laboratory contents: The UC Berkeley science building case study. Institute of Urban and Regional Development Working Paper Series. http://escholarship.org/uc/item/7td3k79k#page-14 (accessed May 10, 2017).
CUNY (City University of New York). 2010. IT disaster recovery/business continuity recommendations. CUNY Business Continuity and Disaster Recovery Task Force, Information Technology Subcommittee. https://www.cuny.edu/about/administration/offices/CIS/security/pnp/CUNY-IT-DR-AdoptedRecommendations-9-16-10.pdf (accessed October 16, 2016).
DHS (Department of Homeland Security). 2015. National preparedness report. https://www.fema.gov/media-library-data/1432751954859-fcaf2acc365b5a7213a38bbeb5cd1d61/2015_NPR_508c_20150527_Final.pdf (accessed March 3, 2017).
DRU Network (National Disaster Resilient Universities Network). 2015. Disaster resilient universities (DRU) overview. http://www.nccpsafety.org/assets/files/misc/DRU_Network_Overview_123115_FNL.pdf (accessed October 16, 2016).
Durkee, S. J. 2013. Planning for the continued humane treatment of animals during disaster response. Lab Animal 42(10):F8–F12.
ED (Department of Education). 2014. Emergency management for higher education. https://www2.ed.gov/programs/emergencyhighed/index.html?exp=0 (accessed September 12, 2016).
EPA (Environmental Protection Agency). 2016. Local emergency planning committees. https://www.epa.gov/epcra/local-emergency-planning-committees (accessed May 10, 2017).
FAS (Federation of American Scientists). 2013. Global threat reduction initiative efforts to prevent radiological terrorism. https://fas.org/pir-pubs/global-threat-reduction-initiative-efforts-prevent-radiological-terrorism/ (accessed September 12, 2016).
FEMA (Federal Emergency Management Agency). 2003. Building a disaster-resistant university. https://www.fema.gov/media-library/assets/documents/2288 (accessed October 17, 2016).
———. 2015. Hazard mitigation assistance guidance: Hazard mitigation grant program, pre-disaster mitigation program, and flood mitigation assistance program. http://www.fema.gov/media-library-data/1424983165449-38f5dfc69c0bd4ea8a161e8bb7b79553/HMA_Guidance_022715_508.pdf (accessed September 12, 2016).
———. 2016a. National Mitigation Framework, 2nd ed. https://www.fema.gov/media-library-data/1466014166147-11a14dee807e1ebc67cd9b74c6c64bb3/National_Mitigation_Framework2nd.pdf (accessed September 6, 2016).
———. 2016b. National Prevention Framework, 2nd ed. http://www.fema.gov/media-librarydata/1466017209279-83b72d5959787995794c0874095500b1/National_Prevention_Framework2nd.pdf (accessed September 6, 2016).
———. 2016c. National Protection Framework, 2nd ed. https://www.fema.gov/media-library-data/1466017309052-85051ed62fe595d4ad026edf4d85541e/National_Protection_Framework2nd.pdf (accessed September 6, 2016).
———. 2017. Hazard mitigation assistance. https://www.fema.gov/hazard-mitigation-assistance (accessed May 18, 2017).
Gair, B. 2016. NYU Langone site visit. Presentation to the Committee on Strengthening the Disaster Resilience of Academic Research Communities. New York City, July 13. Available by request through the National Academies’ Public Access Records Office.
Goodwin, B. S., and J. C. Donaho. 2010. Tropical storm and hurricane recovery and preparedness strategies. ILAR Journal 51(2):104–119.
Hanover Research. 2010. Best practices in business continuity planning in higher education. http://www.planning.salford.ac.uk/__data/assets/pdf_file/0006/20697/20100908-Best-Practices-in-Business-Continuity-Planning-in-Higher-Education-Membership.pdf (accessed September 7, 2016).
IAEM–UCC (International Association of Emergency Managers–Universities and Colleges Caucus). 2017a. National intercollegiate mutual aid agreement. (NIMAA). https://public.3.basecamp.com/p/uqmGVP624NNMaERgUk4fQPqd (accessed September 7, 2016).
———. 2017b. Universities and colleges caucus (UCC). http://www.iaem.com/page.cfm?p=groups/us-caucuses/universities-colleges&lvl=2 (accessed September 7, 2016).
Kapucu, N., and S. Khosa. 2012. Disaster resiliency and culture of preparedness for university and college campuses. Administration & Society 45(1):3–37.
Klein, S. 2016. Enterprise risk management: A collaborative approach to risk mitigation. PowerPoint presentation to the Committee on Strengthening the Disaster Resilience of Academic Research Communities. Available by request through the National Academies’ Public Access Records Office.
Klein, S., M. Mandl, and S. Sencer. 2008. Learning to harmonize. Business Officer 42(6). http://www.nacubo.org/Business_Officer_Magazine/Magazine_Archives/December_2008/Learning_to_Harmonize.html (accessed March 3, 2017).
Lin, H., and J. Kerr. 2017. On cyber-enabled information/influence warfare and manipulation. Working paper. Palo Alto, CA: Stanford University Center for International Security and Cooperation. https://cisac.fsi.stanford.edu/sites/default/files/cyber-enabled_influence_warfare-cornish-v9.pdf (accessed May 10, 2017).
Macrina, F. 2014. Scientific integrity: Text and cases in responsible research, 4th ed. Washington, DC: ASM Press.
Mallard, S. 2016. Ransomware—Business continuity in the collegiate environment. Available by request through the National Academies’ Public Access Records Office.
Mellouk, K. 2016. Strengthening the disaster resilience at an academic maximum containment laboratory: Biosafety and biosecurity preparedness. Presentation to the Committee on Strengthening the Disaster Resilience of Academic Research Communities. Washington, DC. April 25. http://www.nationalacademies.org/hmd/~/media/Files/Activity%20Files/PublicHealth/04%20Mellouk.pdf (accessed October 17, 2016).
Mintzer, J. L., C. J. Kronenthal, V. Kelly, M. Seneca, G. Butler, K. Fecenko-Tacka, and S. J. Madore. 2013. Preparedness for a natural disaster: How Coriell planned for Hurricane Sandy. Biopreservation and Biobanking 11(4):216–220.
Mische, S., and A. Wilkerson. 2016. Disaster and contingency planning for scientific shared resource cores. Journal of Biomolecular Techniques 27(1):4–17.
NCCPS (National Center for Campus Public Safety). 2016. National higher education emergency management program needs assessment. http://www.nccpsafety.org/news/articles/national-higher-education-emergency-management-needs-assessment (accessed January 21, 2017).
NEIDL (National Emerging Infectious Diseases Laboratory at Boston University). 2014. Comprehensive emergency management plan. http://www.bu.edu/orc/files/2013/04/National-Emerging-Infectious-Diseases-Laboratories-Comprehensive-Emergency-Management-Plan.pdf (accessed September 7, 2016).
Neufield, J. 2016. Memorial Sloan Kettering Cancer Center: Research resiliency. Presentation to the Committee on Strengthening the Disaster Resilience of Academic Research Communities. New York City, July 14. Available by request through the National Academies’ Public Access Records Office.
NIST (National Institute of Standards and Technology). 2014. Framework for improving critical infrastructure cybersecurity: Version 1.0. https://www.nist.gov/sites/default/files/documents/cyberframework/cybersecurity-framework-021214.pdf (accessed May 10, 2017).
NNSA (National Nuclear Security Administration). 2013. NNSA, Temple University successfully remove radiological device from campus medical building. https://nnsa.energy.gov/mediaroom/pressreleases/templeuniv031113 (accessed March 3, 2017).
Northwestern University. 2017. Business continuity planning: Plan development. http://www.northwestern.edu/bcp/plan-development/index.html (accessed September 7, 2016).
NRC (National Research Council). 2011. Prudent practices in the laboratory: Handling and management of chemical hazards, updated version. Washington, DC: The National Academies Press.
Roble, G., N. Lingenhol, B. Baker, A. Wilkerson, and R. Tolwani. 2010. A comprehensive laboratory animal facility pandemic response plan. Journal of the American Association for Laboratory Animal Science 49(5):623–632.
Shenkir, W. G., and P. L. Walker. 2008. Ensemble performance. Business Officer 42(6). http://www.nacubo.org/Business_Officer_Magazine/Magazine_Archives/December_2008/Ensemble_Performance.html (accessed March 3, 2017).
Sorrell, T., and N. Brown. 2014. Security innovation award campus project winner: University of Kentucky standardizes its security footprint. http://www.securityinfowatch.com/article/12019064/university-of-kentucky-retrofits-its-physical-security-with-state-of-theart-technology (accessed May 10, 2017).
Stanford University. 2016. ProtectSU seismic restraint program. http://web.stanford.edu/dept/EHS/cgi-bin/protectsu/?q=node/43 (accessed September 6, 2016).
UCOP (University of California Office of the President). 2013. University of California memorandum of understanding for the care of laboratory animals in the event of emergency or disaster. http://www.ucop.edu/research-policy-analysis-coordination/_files/MOU_AnimalCare_EmergencyDisaster.pdf (accessed August 8, 2016).
UK (University of Kentucky). 2012. Business continuity plan departmental template. http://www.uky.edu/EM/documents/UK%20BCP%20TEMPLATE.pdf (accessed September 7, 2016).
University of Iowa. 2010. The University of Iowa pre-disaster mitigation plan. https://uiowa.edu/riskmanagement/university-iowa-pre-disaster-mitigation-plan-updated-4282010 (accessed September 6, 2016).
UW (University of Washington). 2007. Administrative policy statement: Ensuring business, academic, and research continuity (BARC). http://www.washington.edu/admin/rules/policies/APS/13.02.html (accessed May 18, 2017).
Vogelweid, C. 1998. Developing emergency management plans for university laboratory animal programs and facilities. Contemporary Topics in Laboratory Animal Science 37(5):52–56.
Yale University. 2016. Emergency management: Business continuity for laboratories and research facilities. http://emergency.yale.edu/planning/business-continuity-planning/laboratories-research-facilities (accessed March 3, 2017).
ZAHN (Zoo Animal Health Network). 2011. Memorandum of understanding/mutual aid agreement annex. http://www.zooanimalhealthnetwork.org/MOU_Annex.pdf (accessed March 3, 2017).
This page intentionally left blank.



































