1
Introduction and Overview
BACKGROUND
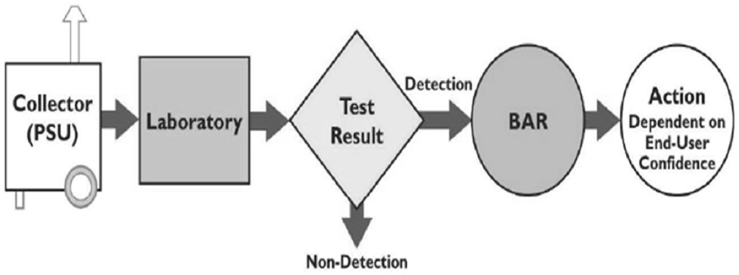
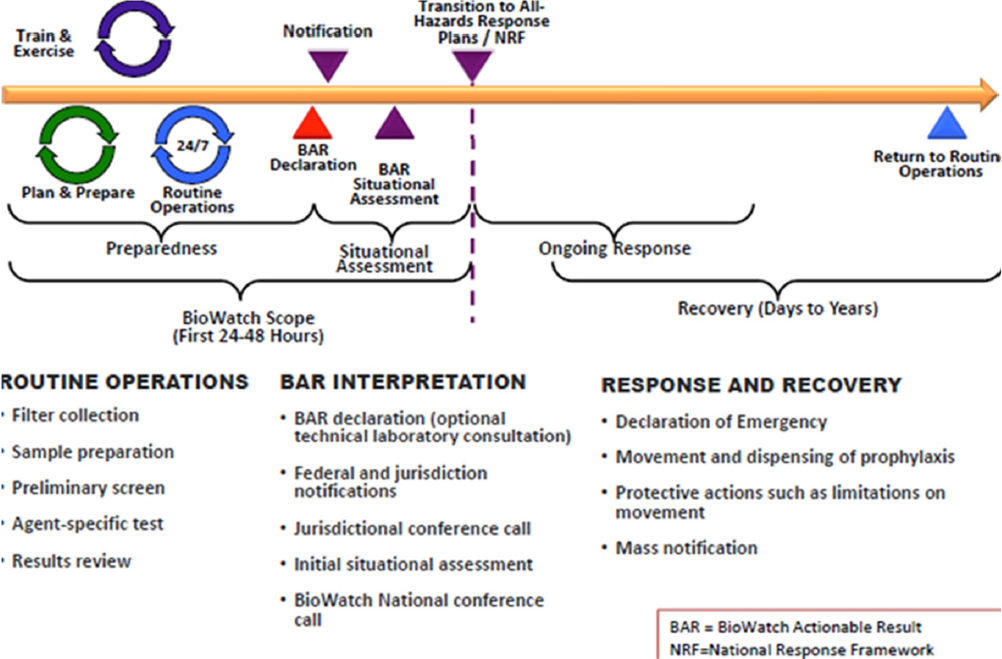
BioWatch is the Department of Homeland Security’s (DHS’s) system for detecting an aerosolized biological attack using collectors that are positioned strategically across the country to continuously monitor the air for biological threats. As currently deployed, BioWatch collectors draw air through filters that field technicians collect daily and transport to laboratories, where professional technicians analyze the material collected on the filter for evidence of biological threats. The entire collection and analysis process takes up to 36 hours to detect the presence of a potential pathogen of interest. A positive result triggers what is known as a BioWatch Actionable Result (BAR), an indication that genetic material consistent with a target pathogen was present on a BioWatch filter. Upon declaration of a BAR, local, state, and federal officials then assess relevant information and determine the course of action to pursue (see Figure 1-1). As noted by BioWatch program officials, to date all BARs were triggered by the detection of DNA from organisms that are naturally present in the local environment.
As part of the BioWatch program’s efforts to enhance its effectiveness and capabilities, particularly with regard to detecting biological threats in challenging indoor environments, DHS requested the National Academies of Sciences, Engineering, and Medicine (the National Academies) to hold a workshop to explore alternative and effective biodetection systems for aerosolized biological agents that would meet BioWatch’s technical and operational requirements, integrate into the existing system architecture and public health infrastructure, and be deployable by 2027. In response to the DHS request, The National Academies established an ad hoc committee to organize a 2-day public workshop to answer the following questions (see Appendix A for the full Statement of Task):
- What new technologies, both current and emerging within the next 10 years, are compatible with the existing architecture of the BioWatch detection system for aerosolized agents and would significantly improve current performance, particularly with respect to time, sensitivity, specificity, range of agents, indoor applications, autonomy, quality of confirmatory response and/or cost? Are there specific considerations for indoor surveillance?
- What new technologies, both current and emerging within the next 10 years, that are ideally compatible with the existing BioWatch architecture would enable detection of common public health threats, such as novel or known viruses and harmful volatile gases, as well as threat agents identified by intelligence assessments?
- Given the current state of technology for biological detection systems, how might technologies evolve and advance by 2027 so that one or more could serve as an alternative to the currently deployed polymerase chain reaction (PCR)-based system? In addition, are there other technologies available that could supplement or modify the current PCR system to enable greater flexibility of the detection system and provide a bridge to future detection solutions?
Overview of the BioWatch Program
In his introductory remarks to the workshop, Michael Walter, BioWatch program manager at DHS, noted that the presentations and discussions at a 2011 Institute of Medicine and National Research Council workshop (IOM and NRC, 2011) led to the conclusion that issues around cost, sensitivity, and available technologies meant it would be many years before the program would be deploying a completely autonomous detection system. “BioWatch is going to stay with collecting a sample, taking it to a laboratory and analyzing a result, and coming up with a response,” said Walter in reference to the current system. “We will come up with ways to make that better, but that is going to be the general way in which we are going to be operating.”
To get everyone at the workshop up to speed regarding what BioWatch does and what it is responsible for, Walter explained that the program was formed by an Executive Order signed in 2003. Its mission is to operate a nationwide aerosol detection system providing early warning across all levels of government to support public health and emergency management communities at the state, local, and tribal levels in order to prepare for and respond to biological incidents related to agents of interest as determined by the intelligence community, the Centers for Disease Control and Prevention (CDC), and other agencies. Walter characterized this mission as “relatively straightforward, but deceptively complex.”
The program’s success, he said, is the result of an extraordinary network comprising federal, state, and local shareholders, and any changes to the BioWatch system must help public health officials with the task of making what will ultimately be difficult decisions. The public health community is extraordinarily conservative, said Walter, so it will be imperative to market any new technology to them and demonstrate that it works better than the existing system before it will take the risk of adopting a new technology.
The BioWatch program has deployed portable sampling units at over 600 sites, including more than 50 indoor sites. The program also receives requests routinely to operate in additional indoor locations and to conduct operations for special indoor events. “BioWatch is getting pulled indoors at the state and local level. It is not something that I advocate and not something my director of public health, Emily Gabriel, publicly advocates,” said Walter. However, local and state officials see BioWatch as an answer to areas of vulnerability, such as when large numbers of people gather in indoor public spaces. In 2015 to 2016, BioWatch deployed detectors to support more than 110 national special security events and special events.
Today, the program analyzes between 235,000 and 250,000 samples annually from more than 30 metropolitan areas deemed to be at the greatest risk for a bioterrorism event. What this means is that any new technology should be able to accommodate that volume of samples, and it needs to do so more quickly and less expensively than the current system. Any new technology should also be scalable to meet the growing demand from states and cities.
In addition to the detection piece, the BioWatch program serves as a forum for networking among local, state, and federal public health officials and that should continue, said Walter, because no technology, automated or not, is going to replace the people who are going to make the decisions on the actions to take upon declaration of a BAR. Walter suggested that any new technology should also fit into the program’s extensive quality assurance program and address sensitivity issues (i.e., remain as sensitive to detection of specific pathogens) in the outdoor environment and time to response in the indoor environment.
The commercial sector will need to be the source of any such improvements, said Walter, because BioWatch is an operational program and does not have a research and development mission. “Whatever we deploy has to be a tried and true technology, and we have to know it works,” he said. “BioWatch is not allowed a false positive, and BioWatch is not allowed a false negative.” Of the two
results, the false positive is the worst because it means shutting down an airport, a subway system, or even an entire city. Such an event would be detrimental to stakeholder confidence in the BioWatch program.
As far as what the optimal future BioWatch system would provide, Walter said that it would be good if the system would identify not only the specific biological threat, but whether it was susceptible to treatment with specific antibiotics or if it was an endemic organism that represented a public health threat but not a nefarious act. In the indoor environment, speed is the current limitation, so any new system needs to be able to operate rapidly and in such a way that it supports real-time environmental dispersion modeling and response time. As he explained, a national laboratory modeling study showed that for the system to enable a meaningful response to a bioterrorism attack in an airport, for example, the answer needs to come in less than an hour. The ideal system would also be able to determine if an attack originated indoors or outdoors.
Though many people assume the outdoor environment is more complex than the indoor environment, working outdoors is actually easier. In the outdoor environment, Walter explained, “I do not have to worry about viability, I do not have to worry about rolling stock, and I do not have to worry about what we are going to do with the people who are in an airport without getting charged with kidnapping if we keep them there.” Another complication in the indoor environment has to do with who to notify when that venue is privately owned, what to tell them, and how to involve them in the decision-making process.
In concluding his remarks, Walter acknowledged that what he was asking for was not going to be easy to develop. “What we are asking you to do is not simple because what we do is not simple,” he said, “but we are depending on this group to help us figure out what track should we be taking, what technologies are out there, and what technologies are realistic for us to look at in the short term, the midterm, and the far term.” There will come a day, he added, when BioWatch will be autonomous. “I have no doubt about that, but the technologies we are going to ask you to talk about in the next two days have got to work in laboratories, too. It is great they are appropriate to go autonomous, but it is not a ruling factor.”
Organization of the Proceedings
The workshop (see Appendix B for the agenda) was organized by an independent planning committee (see Appendix C for the committee member biographical sketches) in accordance with the procedures of the National Academies. In accordance with the policies of the National Academies, the workshop did not attempt to establish any conclusions or recommendations about needs and future directions, focusing instead on issues discussed by the speakers and workshop participants. In addition, the planning committee’s role was limited to planning the workshop, and a rapporteur prepared the Proceedings of a Workshop as a factual summary of what occurred at the workshop. Statements, recommendations, and opinions expressed are those of individual presenters and participants, and are
not necessarily endorsed or verified by the National Academies, and they should not be construed as reflecting any group consensus.
This Proceedings of a Workshop follows the chronological order of the workshop. In Chapter 2 of this proceedings, workshop participants provide an assessment of the current performance of the BioWatch system. Chapter 3 provides a multifaceted look at the development of effective biological detection systems. Chapter 4 explores the potential integration of new technology into the existing detection architecture. Chapter 5 recounts the final discussion on major topics covered at the workshop and their context in the nation’s biodefense efforts. A set of invited papers was written and distributed to participants prior to the workshop to provide background on each of the main topics of the chapters above. The invited papers have been placed in Appendixes E through I.
SCOPE OF THE WORKSHOP
Planning Committee Perspectives
Before proceeding to the workshop’s presentations and discussions, the planning committee members laid out the scope of workshop as they saw it, with those who were leading sessions presenting an overview of their sessions. This discussion was moderated by the planning committee chair, Adel Mahmoud, professor in molecular biology and public policy, Princeton University. Bruce Budowle, director of the Center for Human Identification at the University of North Texas Health Science Center, said his session would address enhancements to the existing system with the goal of identifying pieces of the current system in which to invest research and development efforts. He considers such enhancements as midterm investments given the cost of any new technologies, the time and effort needed to validate them, and the time it will take to market them to the public health community. “We have to show [any new technology] is scientifically feasible and legally defensible,” he explained.
With that caveat in mind, the speakers in the panel discussion he would be moderating were going to focus on how to improve the collection of evidence and remove the resulting materials from the collection medium, noting that this challenge is often ignored when thinking about making improvements. The discussion will also highlight approaches for enhancing detection using real-time PCR assays that are robust in the face of working with dirty samples and that take advantage of multiplexing to achieve higher throughput. Budowle noted that there is a tremendous amount of data available in existing databases that can be used to interpret background signals.
John Clements, professor and chair of microbiology and immunology at the Tulane University School of Medicine, said the panel discussion he would be moderating would address the current quality assurance program and discuss the use of dispersion modeling to understand the probabilities of a potential threat. This panel would also describe a real-world situation in New York City and
examine how possible technology changes might impact quality assurance metrics and operations. Clements, who noted that he is a trained United Nations weapons inspector, said one concern he hopes the workshop addresses is that the ex-cipients1 needed to weaponize a biological agent might be capable of interfering with the assays for those agents. “We do not necessarily assess the impact of weaponized materials when they are delivered onto the filters,” he said.
David Cullin, vice president for research and development at FLIR Systems, said his panel would talk exclusively about indoor biosurveillance, starting with an overview of the challenges and presenting some potential solutions to those challenges. This panel was also going to talk about how the public health community might act upon information from indoor surveillance and about information that might be useful to those responsible for operating and maintaining the local BioWatch infrastructure.
Grace Kubin, director of the laboratory services section at the Texas Department of State Health Services, said the panel she would be moderating would examine the various operational considerations that go along with the introduction of a new technology. “Any type of new technology must be something that I as a lab director can stand behind and say, ‘Yes, I believe the answer that we are getting is correct,’ because I am the one that says ‘Yes, this is a BAR.’” It is important that she and her colleagues understand a new technology and its performance capabilities. She explained that her panel would also discuss the interdependencies between local, state, and federal levels and their interactions with the developers of new technologies to gain that understanding.
As a means of providing context for his remarks, Tom Slezak, distinguished member of the technical staff at Lawrence Livermore National Laboratory (LLNL), explained that he was a member of the team that created the predecessor system to BioWatch and built the chain-of-custody sample tracking system that BioWatch laboratories still use today. His team at LLNL also has some ongoing responsibility for BioWatch’s information technology system. One of his concerns today is about signature erosion: the fact that the incoming genomic data have some potential for false positives and false negatives. “So even as we pick the specific technologies used to identify agents we go after, it is important that we cannot consider the signatures that we use to be fixed endpoints,” said Slezak. “Rather, they should be seen as something that has to be evaluated regularly.”
Turning to the subject of the panel he would be moderating, Slezak said it would be examining a range of technologies that might be used in the 10-year timeline. In particular, the panelists would discuss how to follow up after an event to determine when an area is safe to go into and how clean it needs to be to be occupied again. The panel would also look at the issue of detecting known versus unknown pathogens, something that he believes will require two different technologies to address two very different missions. In his opinion, one challenge will
___________________
1 An excipient is the inactive substance that serves as a medium or formulation for a drug or biological agent.
be to understand the genes involved in various threats and the mechanisms of virulence and resistance, and then develop scalable systems to handle a wide range of potential agents.
Colin Stimmler, senior director for the Bureau of Agency Preparedness and Response, New York City Department of Health and Mental Hygiene, explained that as a response person it is he who thinks about how to break a complex problem into small, measurable pieces and then assigns tasks to address those pieces and fulfill an objective. That is the approach that his panel will take with regard to looking at detecting a biological agent release in a theoretical subway system and how state and local officials would respond to such a release.
Two of the planning committee members did not moderate panels but offered some thoughts on the workshop. Norman Kahn, president and principal at Counter-Bio LLC and a retired Central Intelligence Agency (CIA) official, provided some background on the role that the intelligence community plays with respect to BioWatch. Its first role is in threat identification, which he said is an extraordinarily difficult problem for the intelligence community. “The idea that the intelligence community is going to have a good handle on what the threat is, whether it is a state or a nonstate threat, let alone a lone actor threat, is probably a misconception,” said Kahn. The intelligence community, he explained, has a difficult time penetrating closely held programs, and biological weapons programs would be among the most tightly held of any program.
Where the intelligence community is of greater value is in after-the-fact attribution and determining if a BAR resulted from a deliberate release of an agent by a foreign actor. In that case, said Kahn, the CIA would want a definitive identification of the biological agent, down to strain characterization. He noted that the current BioWatch system looks at a limited number of biological organisms, and that the intelligence community, if it had its wish, would like to see that list expanded greatly.
Fred Rosa, Jr., senior advisor for homeland security at the Johns Hopkins Applied Physics Laboratory, provided some perspective on policy and strategy. The bottom line with respect to the threat of a biological attack, he said, is that the number of credible threat actors is proliferating and they have given clear indications they are actively pursuing bioweapons. In addition, the obstacles to success they face are diminishing over time, perhaps even rapidly, according to the United Nations, the World Health Organization, the Hague Center for Security Studies, and other well-respected institutions and government agencies. As a result, the work that would be discussed at this workshop is urgent, said Rosa. He then noted that the work discussed at the workshop plays into the nation’s biodefense strategy that the White House is developing as required by law. “Whatever strategy ultimately emerges, it will definitely be the case that biosurveillance and the BioWatch mission will figure very prominently in that strategy,” he said.
Rosa then reminded the workshop that the objectives in the Statement of Task were established to align with the BioWatch program’s mission needs statement and the capability development plan. This is significant, he explained, because the extent to which the discussions of the workshop align carefully with
these two documents increases the probability that these discussions would contribute in a tangible way to future budget allocations and real-world improvements. He therefore cautioned the participants to resist going after tangents that might arise and to keep the specific goals of the workshop in mind.
DISCUSSION
The open discussion began with Robert Serino from Science and Engineering Services asking the panelists if there would be operational value added if the BioWatch detectors could send an alert when something of interest began appearing on the filters as a means of beginning the next steps of the process sooner. Stimmler replied that such a trigger system has potential utility. The issue here, he said, is that most elected officials are binary—they want to know if there is a problem or not—and ambiguity can cause more problems than it solves. With that caveat, both Stimmler and Cullin said that if it was possible to develop a concept of operations (CONOPS) on how to respond to a trigger as an initial warning, an early alert could have value, though both predicted it would take a great deal of work to develop a CONOPS with which everyone agreed. Slezak noted that several trigger-based systems were tested in 2001 when he and others were building the system that eventually became BioWatch, and the problem in an outdoor setting was that it was “extremely difficult” to separate nonevents from events because of ambient particle levels in the outdoor environment. A trigger-based system might have a better chance of working indoors, he said.
Jonathan Kaufman from Joint Risk Assessment and Decision commented that quality assurance testing for BioWatch is analytically focused even though the overall system has not undergone a “red team test” in an open-air challenge with an actual agent or direct simulant. He asked if such a test exists, and if not, why not and how would such a test be used to demonstrate that the BioWatch system operates as intended? Kubin acknowledged it is challenging to identify the system’s performance characteristics and the approach she and her team uses is to first rely on approvals or test protocols from the Food and Drug Administration or the CDC, and then try to “break” any new method to find its weaknesses and strengths. Slezak added that aerosol tests were done in a test chamber back in 2001, some outdoor tests used Bacillus stimulants, and at least one of those used aerosol spraying, a potential release mode.
Stimmler said the DHS Science and Technology Directorate (S&T) sponsored a study in 2017 that focused on remediation in a subway system following a release using DNATrax, a PCR-detectable, DNA-based sugar designed by investigators at LLNL to serve as a bioweapon simulant. BioWatch filters collected that material over the course of a week and the results have informed modeling efforts and provided a better understanding of how airflow affects the potential spread of an agent. Walter reiterated that there have been several release tests done, including an outdoor ground-level release of Bacillus globigii, a harmless bioweapon simulant, at the Naval Surface Warfare Center. No tests have been
done using a live agent in an operational environment because, as he put it, “the term for that is bioterrorism.” He did note that the system has been tested in real settings using simulated aerosol and powder releases, and the large majority of those tests registered positive on multiple collectors. The entire system, from collection through analysis, has undergone chamber testing using a killed agent, which Walter said indicated where losses occur and enabled calculations to determine how much material would need to end up on a filter to be detected. BioWatch also funded independent tests of the system when it was considering various Generation 3 systems, and these also showed that the system works and helped develop performance characteristics for the current system.
Willy Valdivia from Orion Integrated Biosciences asked if the DNA signatures for the biological agents of interest have been verified since they were established in 2003. Slezak noted that BioWatch now uses Department of Defense (DoD) signatures generated by the Critical Reagents Program, and Norman Doggett from Los Alamos National Laboratory (LANL) said DHS S&T funded a review of those signatures by LANL. That review, based on current information in GenBank, generated new information that was fed back to DoD and provided to BioWatch.
Before ending the discussion, session moderator Mahmoud asked the planning committee members to reflect on which technologies could be implemented over the next 10 years. Budowle thought that multiplexing technologies and data mining will make an impact, and that there will be more work on defining false positives and false negatives. He also raised the possibility that something similar to the MinION technology (Lu et al., 2016), a portable, real-time device for DNA and RNA sequencing, could come online in a decade, though the technology as it currently exists has too high of an error rate for BioWatch’s purposes. Clements added that while something like the MinION technology will not substitute for regular sampling, it might be useful in transportation hubs, where answers are needed in minutes to hours rather than days.
In Slezak’s opinion, the specificity and speed of multiplex PCR sets a tough bar for any other technology to meet, though he also suggested that a silicon-based sequencing technology rather than a biologically based technology has potential to reach that bar at a lower cost. One hope of his is that research will increase the field’s knowledge about the mechanisms of virulence for organisms of interest, which could lead to the identification of the few genes that make an organism lethal to humans. Clements and Kahn said there is a need for research on assessing viability and virulence. While a terrorist may not care if an organism remains viable or if it is virulent—just the fact that it was detected could produce panic and economic impact—viability and virulence are key issues from a public health perspective. Kahn said one of his biggest concerns is that someone could engineer an otherwise benign organism, one the system may not be looking for, to express some virulence factor. Slezak stated that such work will require the relevant federal agencies to coordinate and fund research to answer these basic biology questions. Sanjiv Shah from the Environmental Protection Agency said his group and
researchers from LLNL have developed a rapid PCR-based viability test that currently produces results in 8 to 9 hours. Getting funding to shorten that time has been challenging, he said.
Cullin said he is concerned about the density at which detectors are deployed. “Everything we do is point sensing, and unless that point sensor is somewhere where the threat is, that point sensor will be completely useless,” he explained. The solution is increasing the density of detectors and that will require an inexpensive technology that can be deployed as a broad network of sensors similar to the “internet of things.”
As a laboratorian, Kubin said she believes that, as more genomic sequences are uploaded into GenBank and other databases, it will be important for this community to use that information to ensure that BioWatch is detecting what it needs to detect. She also said there is room for improving the sampling aspect of BioWatch.
Stimmler noted that an important and realistic paradigm going forward will be one of making continual improvement and refinement to the BioWatch system. One significant advance in biodetection that he believes is achievable within 10 years would come with the development of technology focused on instant characterization for use after a corroborated incident. A deployable technology of this sort could be used in the field to identify safe and unsafe boundaries, for example, and assist with response and consequence measurement, he explained.
Rosa, offering a comment from a nontechnological perspective, worries about what will happen when the nation first becomes aware of an attack through the appearance of symptoms in people. That raises a question related to political will and the investment the nation is willing to make to provide an order-of-magnitude-greater level of assurance that BioWatch can enable early detection on a wide scale. Cullin made the analogy to the price of insurance against the 1,000-year flood, where people will say it would be terrible but never happen where they live, and that attitude affects how politicians act. John Vitko, retired from DHS and BioWatch, said the issue of how much it will cost to produce an order-of-magnitude improvement requires identifying a metric against which to assess improvement. When BioWatch was established, that metric was the fraction of the population one wanted to protect against what level of attack as measured by the quantity of material released.
THE BIOWATCH PROGRAM
Overview: A Local Public Health Perspective of the BioWatch Program
Paul Biedrzycki, retired director of disease control and environmental health at the Milwaukee City Health Department, presented the first of five papers that the planning committee commissioned for this workshop (see Appendix E). Noting that he is not a scientist, Biedrzycki explained he was a BioWatch end user
since its launch in 2003, when he and the health department commissioner traveled to a regional workshop in Chicago to learn about the technology that was to be deployed a mere 2 weeks later in Milwaukee. “That is not the way you want to build relationships with state and local public health officials,” he said. “I would urge as technology is discussed and studied that we think about calibrating that technology against the current and future landscape of state and local public health.”
Biedrzycki began his review of BioWatch from an operational perspective by providing a brief overview of public health agencies’ essential services (see Figure 1-2), with prevention and control of communicable disease and emergency preparedness being important core competencies at the local level. Local public health, he explained, often serves as the broker in terms of messaging between government, the public, the media, and policy makers. With regard to public health emergency preparedness, the core competencies are modeling leadership, communicating and managing information, planning for and improving practice, and protecting worker health and safety. BioWatch, he said, does a good job cutting across these competencies, and he urged the BioWatch program to continue supporting, informing, and assisting state and local public health with these competencies, and particularly with modeling leadership. He did note the challenges associated with the ambiguity related to false positives and negatives and the declaration of a BAR—ambiguities that have significant consequences in terms of serving as a trigger for public health activities.

Turning to the subject of his review, Biedrzycki reiterated that BioWatch was launched in 2003 because of the perceived threat of bioterrorism related to foreign adversaries who may have weaponized select agents. Historically, BioWatch was defined as an early detection and warning system, though he is not sure it meets that definition given the current technology. The system, as others have noted, was designed to identify select aerosolized biological agents of public health importance in the outdoor environment, though it has since moved indoors. The system has been deployed in coordination and consideration primarily around environmental field operations and laboratory analytical metrics, and its primary focus is to reduce or limit widespread and severe morbidity and mortality associated with an outdoor aerosolized bioagent release through rapid identification, deployment of the Strategic National Stockpile, and timely treatment of the affected population. When initially deployed, the public health piece was missing, said Biedrzycki, but under the current program leadership, engagement with state and local public health as authentic, trusted partners has improved dramatically. He added that he was glad to hear planning committee members recognize there will be economic and social capital impacts in a community associated with even a failed bioterrorism event.
From a local perspective, the mission of BioWatch is threefold:
- Shortening the time between the accurate detection of aerosolized pathogenic biological agents and the deployment of effective public health prevention and intervention measures such as medical countermeasures, isolation and quarantine, social distancing, and canceling events;
- Promoting regional partnerships, collaboration, and relationships that ensure rapid, cost-effective, and meaningful public health emergency preparedness; and
- Enhancing local community preparedness, response, and resiliency to bioterrorism by leveraging existing expertise and assets along with federal and state coordination.
As Walter said earlier, the BioWatch mission is simple but difficult to carry out. One area, though, where BioWatch has been remarkably effective, in Biedrzycki’s opinion, based on spending 35 years in public health, has been in building regional partnerships and collaborations. He credited BioWatch’s efforts to improving regional partnerships and collaborations as benefiting a number of public health emergency preparedness initiatives, including those on pandemic influenza preparedness, the City Readiness Initiative, and even the response to the West African Ebola outbreak in 2015. In addition, public health has now expanded it coalitions to include a much wider array of partners, such as hospitals, acute care centers, nonprofit organizations, and even the private sector. “Corporate America has a very strong interest in biodetection and what occurs in our community in terms of preparation and planning for bioterrorism events,” said
Biedrzycki. He added it will be necessary to bring all of these partners to the table in future discussions about implementation, evaluation of new technologies, and enhancing local community preparedness response and resiliency to bioterrorism. Given that technological improvements have to be cost effective and value added, it will be important to leverage a wide range of partners over a much broader region than has been typical in preparedness activities.
The basics of the BioWatch program, some of which Walter discussed earlier, include
- Portable sampling units with high-volume air-monitoring units dispersed in networks in various jurisdictions that are operated continuously;
- State and local environmental field staff that collect and transport samples from the collectors to the laboratory;
- Dedicated laboratory capability, typically in the form of CDC Laboratory Response Network facilities and including extensive quality assurance and quality control components to minimize ambiguity in test results;
- Local BioWatch Advisory Committees (BACs) that analyze laboratory-reported data and provide oversight of local activities with federal coordination and support from the BioWatch program office, jurisdictional coordinators, the national laboratories, the Environmental Protection Agency, and the Federal Bureau of Investigation; and
- Integration with local public health preparedness and state and other local emergency management systems upon declaration of a BioWatch Actionable Result.
The collaborative space in which BioWatch operates includes routine operations, BAR interpretation, and response and recovery (see Figure 1-3). One role of the BAC in this space is to provide the foundation for interaction and coordination between local agencies and the BioWatch program office and other federal assets. Ideally, said Biedrzycki, BACs are a multidisciplinary and multisector constituency of federal, state, and local agencies, as well as organizations and individuals, that closely coordinate their activities with local public health departments. BACs serve as the primary focal point for policy-maker notification, public risk messaging, and all local response activities associated with BioWatch operational constructs within a community. He stressed that while BioWatch is technology coordinated, supported, and funded through federal agencies, it is implemented and actuated at the local level. As a result, the BACs play an important role in ensuring there is effective, strategic preparation and consequence management within their local and regional areas in response to declaration of a BAR.
Biedrzycki noted that what policy makers know and understand about BioWatch is limited, in terms of both the technology and the consequences of a BAR being reported, in part resulting from the security aspect of information exchange within DHS and the BioWatch program. “I think this is slowly being solved with clearances being granted to local public health officers and a little more freedom of transparency regarding program operational metrics,” he said, “but I think we have a ways to go.”
From Biedrzycki’s perspective, a BAR is the most important output from the BioWatch program, so any new technology that improves the ability to declare a BAR, to say there is a threat of exposure to a biological agent, is going to be incredibly interesting to state and local public health authorities. Today, a BAR is a confirmed laboratory finding of select biological agent genetic markers on a previously collected portable sampling unit filter. What a BAR does not provide is information on viability, susceptibility of the agent to available medical countermeasures, or any genetic modifications relevant to human health. A BAR serves as the action threshold for initiating national and local teleconferences between the local BAC and various federal agencies and assets, and it may activate provisions of the local consequence management plan in coordination with state and federal agencies. To date, said Biedrzycki, most BARs have been associated with the detection of naturally occurring microorganisms, but even when a BAR does not represent a bioterrorism event or an imminent public health threat, there is a cost to state and local resources because of the BAC activity it triggers. In fact, he said, BARs can result in significant actions, including
- Enhanced human, animal, and environmental surveillance for disease indicators;
- State and local public health epidemiologic investigation;
- Phase I and II environmental sampling;2
- Public messaging and risk communication;
- Heightened law enforcement intelligence gathering;
- Request and staging of medical countermeasures from the Strategic National Stockpile:
- Event reconstruction activities; and
- Alert notification to other BioWatch jurisdictions.
The extent of this list is why public health officials such as Biedrzycki continually advocate for new iterations of technology that can reduce the uncertainty associated with a BAR. He added that he always recognizes BioWatch as being a pioneer in environmental biosurveillance that can inform public health, and he
___________________
2 Phase I sampling refers to collection of field environmental samples at and around the actual portable sampling unit (PSU) site. Phase II sampling refers to additional field environmental sampling within a prescribed perimeter and distance outside of the PSU site and only if one or more Phase I sampling results are confirmed to be positive and informed by air dispersion modeling data.
sees one aspect of the program’s mission is to expand on that concept in a way that is meaningful for local public health officials.
One aspect of BioWatch that has improved over the past few years is coordination across BioWatch jurisdictions. This information sharing, said Biedrzycki, has helped public health officials better understand the idiosyncrasies of the system overall. He sees this improved coordination as one outcome of the BioWatch program office’s outstanding job of engaging state and local officials, producing guidance documents and technical assistance protocols, and organizing workgroups and webinars. The BioWatch jurisdictional coordinator program now places liaisons on the BACs that serve as intermediaries between the national program office and local public health agencies. These individuals help coordinate and broker conversations and problem solving across multiple jurisdictions, and many BioWatch exercises now include both intra- and interjurisdictional scenarios that support and inform public health emergency-preparedness funding objectives. Biedrzycki also credited BioWatch with being very responsive to local requests for both indoor and outdoor special event monitoring.
To conclude his presentation, Biedrzycki listed several limitations of the current BioWatch system and future considerations from a local perspective. The limitations he identified in his review paper included
- A limited array of pathogen and other threat analytical capabilities and rapid pathogen detection to enhance early warning and detection and subsequent public health protective actions;
- A limited and nonuniform distribution of air-monitoring technology within indoor and outdoor environments near or within critical infrastructure or high-risk target locations;
- Limitations in population coverage that fails to reflect changes in population demographics and where people live in cities and suburban areas;
- A lack of near-real-time event reconstruction capabilities for more precise environmental exposure analysis, efficient deployment of public health countermeasures, and better decision making in concert with policy makers;
- A lack of standards of practice for next-generation BioWatch technology and field deployment metrics that incorporate public health input; and
- A lack of adequate funding mechanisms to local public health jurisdictions and partners for sustaining BioWatch preparedness and response capabilities into the future.
Biedrzycki noted that public health departments are losing personnel while becoming increasingly dependent on grant funding. “If indeed this technology is going to be successful, we need to be sensitive to what is happening at the local level, what the landscape looks like, where the new partners are, and what the political priorities are in communities,” he said.
Going forward, Biedrzycki said early and frequent engagement of state and local public health agencies in authentic and trusted partnerships throughout the design, development, testing, and evaluation of technology is imperative. Any future technological improvements need to be made in the context of how they will impact state and local public health capacity and capabilities, particularly with respect to workforce development and proactive funding. In that regard, future BioWatch technologies need to be cost effective, sustainable, and compatible with public health biosurveillance that is becoming increasingly electronic, epidemiologic, and reliant on public health informatics. From a technology perspective, he would like to see the system’s sensitivity and specificity of detection improved and for the system to detect a wider range of organisms in a manner that identifies and defines real threats. In addition, he would like to see faster and more accurate reporting to state and local public health officials to produce more meaningful situational awareness.
On a final note, Biedrzycki offered that BioWatch technology should inform, support, assist, and advance public health emergency preparedness goals and objectives on the ground floor, and public health collaboration should be a key evaluation metric for any new technology. BioWatch technology, he added, should align with public health environmental biosurveillance and become a stand-alone national security initiative. He suggested that the program strive to develop cost-effective surveillance and monitoring best practices that integrate with and do not burden existing state and local public health agency operations.

















