Proceedings of a Workshop
| IN BRIEF | |
|
November 2018 |
Multi-Domain Command and Control
Proceedings of a Workshop—in Brief
On July 18-20, 2018, the National Academies of Sciences, Engineering, and Medicine’s Air Force Studies Board (AFSB) convened a workshop in Washington, D.C., on multi-domain command and control (MDC2)1 in the U.S. Air Force (USAF). The workshop focused on challenges and opportunities in the areas of operations, technology, acquisition, and policy. During the work-shop, the discussion gravitated toward several key issues and themes that characterized the challenges facing development and deployment of MDC2 systems. The information summarized here reflects the knowledge and opinions of individual workshop participants and should not be viewed as a consensus of the workshop participants, the AFSB, or the National Academies.
OPERATIONAL PERSPECTIVE—DEFINING MDO AND MDC2
Following a welcome from Workshop Chair Mike Hamel (Lt. Gen., USAF, ret.) and introductions around the table, the workshop proceeded with a discussion of the character of multi-domain operations (MDO) for which MDC2 systems are necessary and how it differs from traditional joint force and cross-domain operations. As noted by some of the participants, previous incarnations of what has been termed MDO have existed, initially as an evolution on previous forms of combined arms, joint operations, and cross-domain operations. Hamel noted that a concept from the 1990s called “network centric warfare” (NCW) held similar characteristics and potential, which is now ascribed to MDO. Although he noted the failure of the NCW concept to sustain itself over time—an issue revisited during the subsequent discussions at the workshop.
Brig. Gen. B. Chance Saltzman (Director of Current Operations, Deputy Chief of Staff for Operations, USAF) illustrated the distinguishing characteristics of modern MDO over previous, similar incarnations. He explained that true MDOs are more than just assets in one domain participating in operations in another, which has been the case with joint operations in the past. Combat air support for a ground mission or satellite guidance of a munition dropped from an aircraft are not, in Saltzman’s estimation, sufficiently MDO. MDO, as described by Saltzman, is the seamless integration of assets in all domains to create effects in any domain that presents challenges for adversaries that must be addressed in all
_________
1 Brig. Gen. B. Chance Saltzman noted that MDC2 is considered one of the Chief of Staff of the Air Force’s (CSAF) three “big rocks,” or key focus areas. The other big rocks are strengthening joint operations leaders in the USAF and revitalizing squadrons. One participant noted that the CSAF should emphasize that “squadrons” refer the support units of the USAF, and not just the operational combat squadrons, in order to ensure that they receive the necessary support as well.
![]()
domains. In his assessment, the distinguishing characteristic is the degree of “seamless integration of domains into a unified warfighting structure.” Ted Bowlds (Lt. Gen., USAF, ret.; chief information officer, FlightSafety International) noted later that in true MDO, there will not be separate doctrines but one that incorporates all assets across all domains.
Col. Douglas “Cinco” DeMaio (vice commander, Curtis E. LeMay Center, USAF), described the necessary end state of an MDO force, and used the example of a Marine Air Ground Task Force (MAGTF), which the Marines and Navy provide as an integrated multi-domain unit to the combatant commander. DeMaio outlined a future in which the USAF would be able to provide integrated multi-domain forces by seamlessly integrating space, air, and cyber assets to combatant commanders.2 DeMaio further suggested that the essence of MDC2 is really about data management and exploitation.
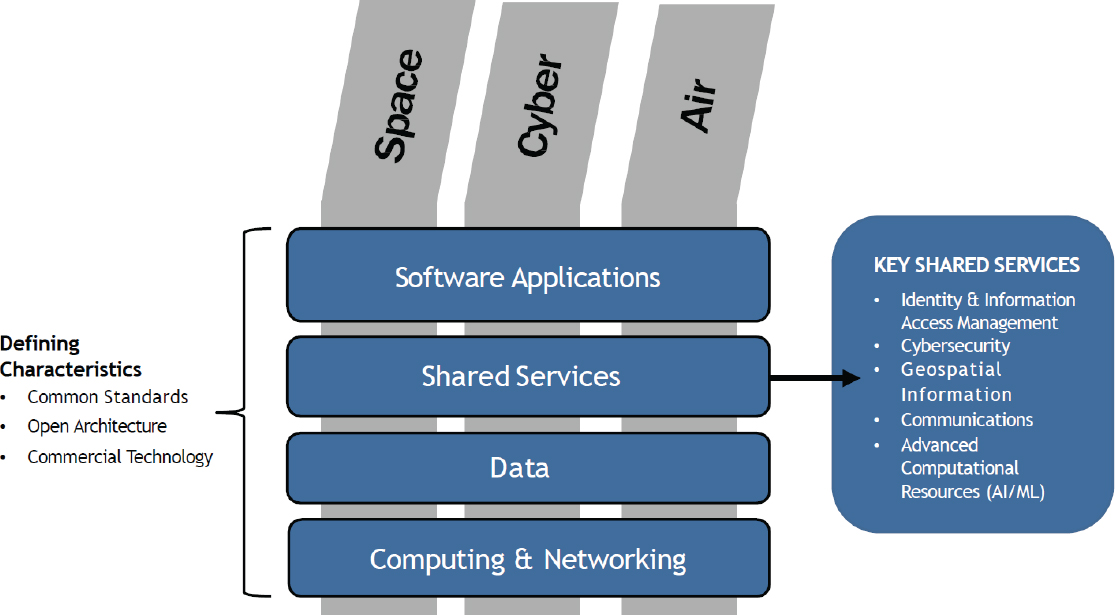
HORIZONTALLY ALIGNED STRUCTURES
During the discussion with Maj. Gen. Crider (chief data officer in the USAF), several of the participants emphasized command and control systems must be compatible across all systems under their control. While historically a common language, signaling system, or radio frequency would suffice, modern warfare, driven heavily by data exchanges from a diverse array of sources in a multitude of formats and delivered to a variety of users, requires extensive common command and control infrastructure. Several participants described this as a horizontal infrastructure that integrates across all other systems and domains, as opposed to the typical vertically aligned system meant to achieve a specific mission or mission set.
A common characterization used by several participants emphasized the importance of common or horizontally aligned structures, concepts, and policies. Specifically, several participants noted the importance of the following issues: a common and horizontally aligned information infrastructure and data governance; system requirements; MDO doctrine; common lexicon; data sharing; program manager (PM) ownership; and program office buy-in. Saltzman introduced the concept of horizontal integration and requirements, and several participants reaffirmed these needs. The section below summarizes each of these key issues.
Horizontal Infrastructure and Data Governance
Several participants, including Kirk Kern (chief technology officer, NetApp), noted the need for a common technical infrastructure, including a shared “data layer” and dedicated set of common core services that aligned horizontally across all systems and acquisition programs. Hamel noted that a common information infrastructure is a critical enabler of MDC2 and must be managed across the USAF enterprise. Marv Langston (independent consultant; former Deputy Chief Information Officer, Department of Defense [DoD]) noted that horizontal architectures have been propelling commercial best practices for decades, and the DoD is behind in adopting them and suggests that the push for horizontal architecture is a step in the right direction. Julie Ryan (CEO, Wyndrose Technical Group) added that setting common standards would be key to establishing a horizontal infrastructure.
A common horizontal C2 infrastructure among systems and programs is not adequate without a system to govern and manage data sharing and processing. While this may appear to be a primarily technical issue, Becky Winston (Winston Strategic Management Consulting) and several other participants pointed out that policy challenges regarding data sharing and interoperability remain primary antagonists to achieving horizontal data sharing. Bowlds and other participants suggested that ensuring horizontal data governance should be tied to the funding of development programs—an issue examined further as the conversation moved to horizontal requirements.
_________
2 A recurring point made by participants, including Workshop Chair Mike Hamel and others, was that the Service branches exist to recruit, train, and equip forces and that these forces are provided to regional combatant commanders who execute operations as a joint force.
Horizontal versus Vertical Requirements and Program Buy-In
A key point of discussion introduced by Saltzman concerned the difference between horizontal requirements that cut across programs and vertical requirements contained within a program. Successful MDC2 systems will introduce horizontal requirements across programs to ensure compatibility. Traditionally, programs are organized around vertical requirements. Bowlds noted that the requirements for an MDC2 system would need to “transcend any one platform or mission requirement.”
As Saltzman pointed out the concept of horizontal requirements is not entirely novel to military operations. Requirements for interchangeable fuel, shared parts, and common requirements for airfields and aircraft munitions mounts are all historic examples of horizontal requirements. He suggested they have become so ubiquitous in USAF systems that they are not recognized as horizontal requirements today.
Several participants, including Alden Munson (senior fellow, Potomac Institute for Policy Studies), Bowlds, and DeMaio, noted that this creates a central challenge to the “stove-piped” bureaucracy of the USAF acquisition community, which aligns its requirements vertically within individual programs. They observed the incentives for PMs reward success within programs, not across programs.
Saltzman, Bowlds, and Hamel suggested the USAF establish a PM responsible for the horizontal integration of MDC2 requirements and systems. Bowlds added the PM would need to control their own funding, and Winston added that incentives would also need to be put in place to ensure program buy-in. Currently, as noted by some participants, PMs are incentivized to focus on their project alone and not others. One participant suggested connecting funding approval to program buy-in and compliance with the necessary horizontal requirements of the MDC2 system. Winston and other participants noted that ownership across the USAF enterprise will be critical to ensure sustainability and integration. They argued that a dedicated, funded, and empowered PM for MDC2 horizontal integration, with a direct line to the Assistant Secretary of the Air Force for Acquisi-
GLOBAL TECHNOLOGY THREATS AND TRENDS
Mark Maybury (Chief Technology Officer, Stanley Black & Decker; Former Chief Scientist, USAF) presented on the importance of information warfare and how global technology trends will increase the threats and opportunities posed by information operations. Following a list of disruptive technologies and their potential role in “gray zone” conflicts, Maybury presented an example of a Russian military base in Syria that was allegedly attacked by Syrian rebels using a drone swarm. He predicted these types of gray zone conflicts would increase as technology affords novel capabilities to state and non-state actors.
Maybury maintained that information is a crucial lever for projecting national influence, but the United States and its adversaries envision information operations very differently. While the United States has an advantage in its adherence to the truth, U.S. policymakers have failed to prioritize information operations, and adversarial states have decades of experience manipulating the public narrative. Using Ukraine as a case study, Maybury stated that all levels of the Russian government coordinated to politically destabilize Ukraine, mislead the international community, and promote public support for the invasion.
While the United States is a global leader in research and development, China is trending to surpass the United States in vital technology areas necessary for multi-domain operations. Artificial intelligence (AI), autonomy, and block chain are just a few examples of technologies with substantial Chinese government investment. Maybury argued these technologies would significantly expand the threats and opportunities of the informational aspect of multi-domain operations. He affirmed that the United States should develop counter-offensive capabilities for information operations while leading advocacy for global policies that promote a right to personal privacy and security.
tion, Technology and Logistics (SAF/AQ) and USAF leadership, will be a critical component in ensuring its success.
Common Doctrine and Lexicon Across All Systems
DeMaio and Brian “Bingo” McLean (Curtis E. Le-may Center, Air University) each presented on the challenges related to the development of an MDO doctrine. DeMaio commented that there is currently no official MDO doctrine in the USAF, and there is a disconnect between space, air, and cyber doctrines—with no common doctrine among them. Moreover, each Service branch has its own concept of MDO, further complicated by joint force MDO—although DeMaio noted that recently some headway has been made in aligning USAF and Army MDO definitions. DeMaio argued the alignment of doctrine is a critical step toward MDO and MDC2 systems.
Development of an MDO doctrine is further hampered by the lack of a common terminology among the USAF and the other Service branches. Winston noted this extends to the policy and acquisition realm where stove-piping of programs hinders development of a common terminology in terms of both the technologies under development and the acquisition mechanisms available to streamline procurement. For instance, a lack of a common and consistent understanding of agile acquisition prevents its widespread adoption for acquisition. Sheryl Thorp (Air Force Life Cycle Management Center) added that this extends to industry as well, which uses a different lexicon than the USAF and other government agencies. Winston, Thorp, and Hamel argued developing and instituting a common lexicon will be a key step moving for-
ward on acquisition and integration of MDC2 systems.
Enterprise Ownership, Funding Ownership, and Leadership Buy-In
Given the horizontal nature of MDC2 infrastructure, integrated across all USAF systems and acquisition programs, Winston, Thorp, Saltzman, and several other participants stressed the importance of sustained leadership, ownership, and buy-in as critical to ensuring successful implementation, and even more critically for life-cycle sustainment. Specifically, as Bowlds noted, the ownership over funding is critical to ensure sustainment of the enterprise over a long period.
Leadership buy-in was identified as a critical component for the success of the horizontally aligned PEO. Gary Kyle (president and CEO, Persistent Agility) highlighted the importance of alignment between the CSAF and SAF/AQ, and the need for the horizontally aligned PEO to have a direct reporting line to them for rapid development and enterprise-wide integration.
Shared Data Layer and Accessibility
A key component of the horizontal infrastructure is a common and shared data layer that exists across all systems. As several participants noted, including Kern and Langston in their introductory presentation, for the data to be useful to the operator, it must be accessible, curated, tailored, and shared.
A key challenge in developing and establishing the data layer lies in the realm of policy. Several participants observed that data sharing across the USAF enterprise, between the Services, and across the whole of government has long been a challenge. Some participants observed that data is protected and tightly controlled by individual Service branches and agencies with little regard for the need to share the data across the whole of government. Some participants argued, as with horizontal requirements, data-sharing parameters should be a prerequisite for program funding. Kern observed the need for minimal data-sharing parameters for all programs and that these should be tied to the horizontal requirements. Crider observed the mechanism for sharing data is also important, and the desire to share is not adequate to ensure its dissemination.
Classification poses another challenge. Saltzman commented that many of the rules and regulations regarding access to classified information stem from the 1970s. Sharing information between classification levels poses major challenges when the operators have varying levels of se-
ADDITIONAL KEY POINTS
The electromagnetic spectrum is the real domain; cyber is the access point (extension of the human domain). —Col. DeMaio
Space is both geographic (orbit) and functional (providing communications, navigation, and intelligence gathering functions) in nature while cyber is functional but knows no geographic boundaries. —Col. DeMaio
A demonstration of MDC2 advantages may be key to achieving acceptance. —Brian McLean
Return to using the term DEVSECOPS instead of just DEVOPS to ensure security is factored in from the start. —Marv Langston
There is an emerging science studying how to structure search through platforms such as Google that can inform data curation in MDC2 systems. —Julie Ryan
For decades, because we have operated in a relatively benign environment we have not had to develop tactics, techniques, and procedures to fight in space. —Lt. Gen. Thompson
We need to develop institutional systems that maintain ideas through personnel rotations.—Lt. Gen. Thompson
curity clearances and the potential for classification by compilation3 exists. Saltzman suggested the information presented to the end user could be stripped of the details that make it classified while still providing information necessary for the operation.
Security of the “data pipeline,” a concept explored later, was also identified by several participants as a critical component of the larger system. Ryan observed that, in a conflict, the United States will want to ensure the security of its own pipeline while denying its adversary access to theirs. Crider suggested labeling data at the ingest point, to ensure pedigree, is critical for data integrity.
ITERATIVE AND CYCLICAL PROCESSES
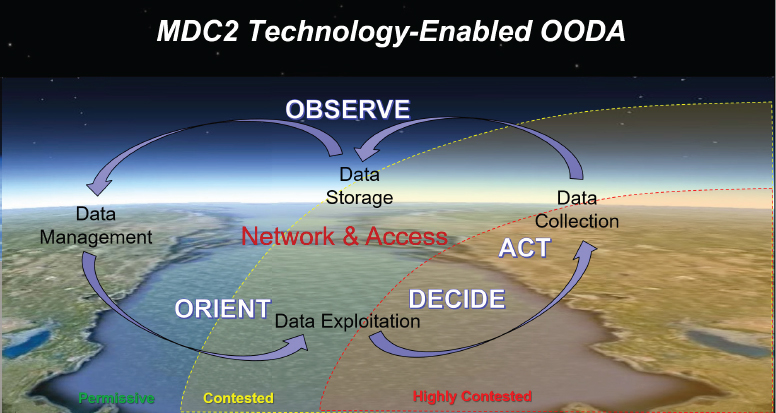
The remainder of the key themes and issues of the workshop were characterized by several participants as inherently iterative and cyclical processes requiring a continuous feedback loop with recurring iterations, rapid turnarounds, and insertions. These processes include the association of the “observe, orient, decide, act” (OODA) loop with MDC2, the iterative nature of data, the importance of iterative systems development, the feedback loops provided by close operator/support integration and prototyping, and the important role played by rapid acquisition methods to maintain pace. The section below summarizes each of these key issues in turn.
MDC2 as Data-Driven Activity: A Technology-Enabled OODA Loop
Some participants noted that C2 is an inherently data-driven activity and, as several participants noted, will be heavily reliant on effective data input, governance, and processing. Saltzman used the analogy of the OODA loop,4 a concept developed for fighter pilots, to describe the benefits of an MDC2 system and its data driven nature. The OODA loop describes the decision cycle a combat pilot undergoes in an engagement—they first observe the environment, orient themselves to the present circumstances, decide on a course of action, and execute. A few participants commented the OODA loop is an iterative and recurring cycle that occurs throughout an engagement. Victory goes to the combat pilot that completes the loop faster and thus manages to stay within the decision cycle of their adversary. Saltzman described this as the end goal of an MDC2 system—to allow commanders to get “inside the decision cycle of the adversary, to collect, process, plan, and act on information faster” (see Figure 2). A true MDC2 system, as described by Saltzman, allows the commander to more rapidly observe the battlespace and become oriented to make optimal decisions and act faster than the adversary. He described MDC2 as a technology-driven OODA loop.
As some participants observed, the potential for modern information technology systems is to dramatically increase the speed in which the C2 OODA loop can be completed and thus greatly enhance the effectiveness and speed at which military forces can be controlled to respond to an adversary’s actions and complete its objectives. Saltzman suggested future conflicts will be decided by which side obtains and maintains information dominance. Wallace Bow (Sandia National Laboratories) agreed by noting that data is essential to the commander’s decision cycle.
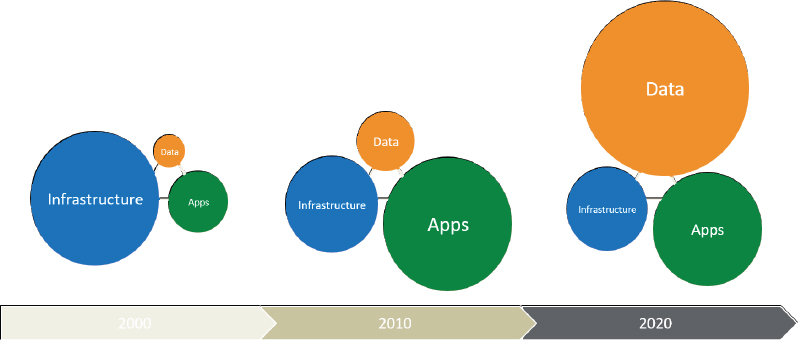
Data and the Data Pipeline
A recurring observation among several participants expressed the need for MDC2 systems to focus on the data with a particular emphasis on the software to manage, process, and disseminate the data—over the hardware itself. Langston and Kern, in their opening presentation for the technology section of the workshop, noted
_________
3 “Classification by compilation” refers to information that, while unclassified in isolation, becomes classified when juxtaposed and combined with other unclassified information.
4 The OODA loop concept was developed by USAF Col. John Boyd to describe the combat operations process. Although originally designed with fighter pilots in mind, the concept can be applied to the whole of military operations. In the decades since Boyd introduced the concept, it has been adapted for law enforcement, business operations, litigation, and other nonmilitary activities.
that this is already taking place in the private sector (see Figure 3). In the early 2000s, they reported, the emphasis in information technology was on the hardware infrastructure, but by 2010, the emphasis had shifted to applications. As information technology development approaches 2020, the focus has shifted to the data itself. They noted USAF MDC2 systems should follow the private sector and move toward data-centric systems.
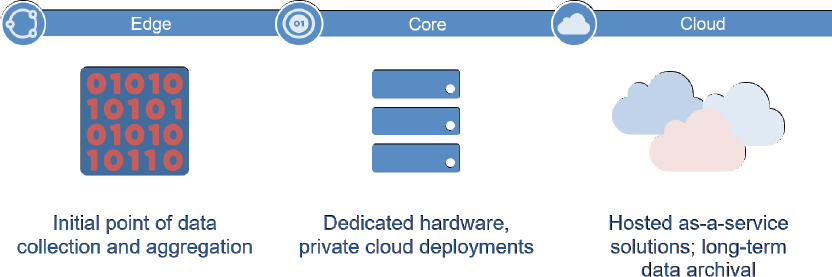
Kern and Langston noted a key aspect is the shift in data from being a static input to a pipeline of information input (see Figure 4, which illustrates in broad strokes the relationship between different points in the pipeline). In the pipeline model, data becomes iterative and refreshed with new inputs almost constantly.
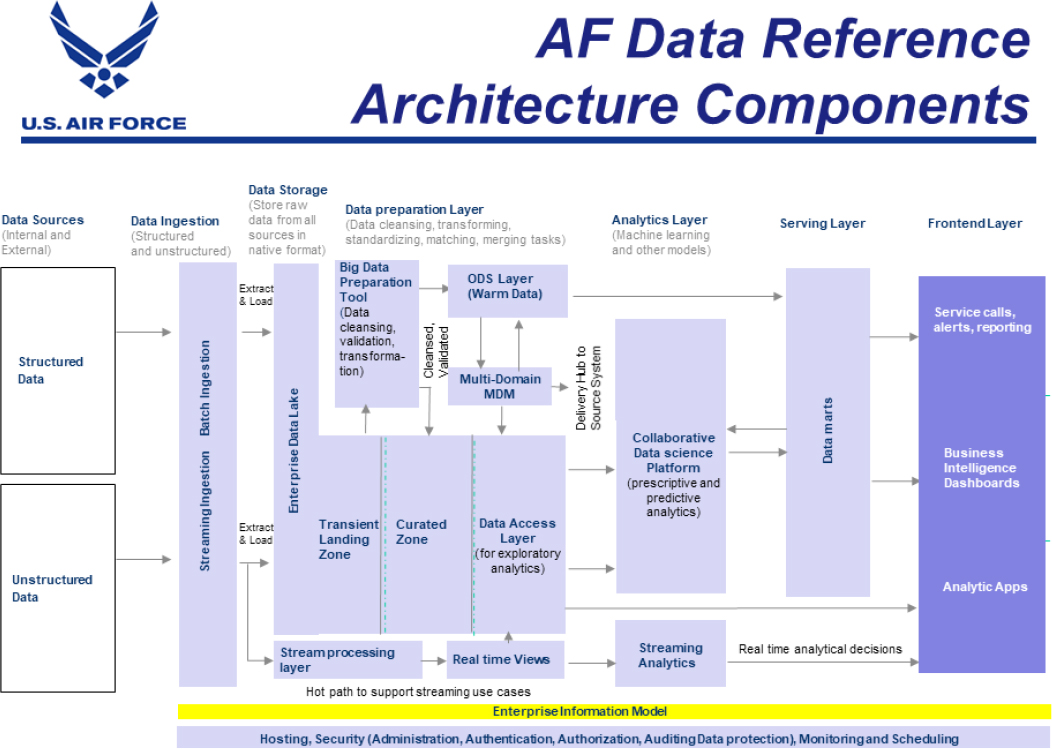
Data architecture must be focused on the pipeline process moving from source inputs through a curation process and provided to users. The USAF has already begun thinking along these lines. Crider described her proposed data architecture for MDC2 as a pipeline. Figure 5 shows an overview of her proposed data architecture pipeline.
A critical component for the data pipeline, noted by Hamel and other participants, is the need for data curation—lest the sheer volume of information from a multitude of sources overwhelms the operator.
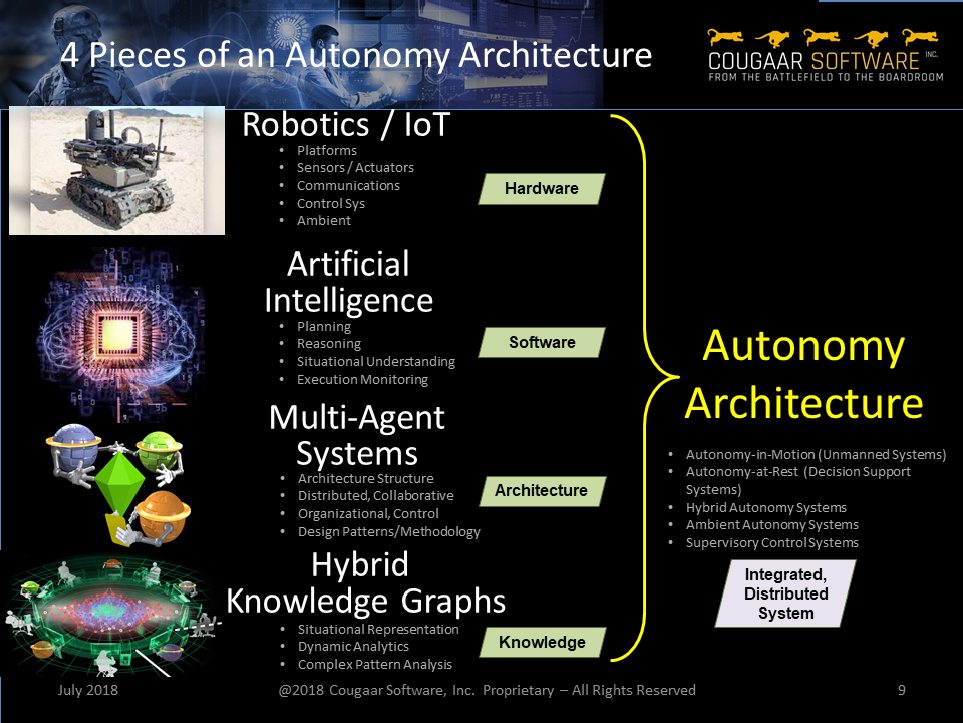
Data Curation and Autonomy
Todd Carrico (Cougaar Software, Inc.) argued for a need to move to an “autonomy infrastructure” to process and curate the data inputs from the battlespace. Several other participants highlighted this critical need to ensure the operator is not overloaded with raw data. Carrico noted that, generally, humans can only handle approximately seven separate concepts at any one time, but autonomous information systems can handle far more. Managing command and control across all domains simultaneously will require autonomous systems that can assist human operators with handling the information load and alert human controllers to events they must address. Some participants observed that data curation might align with the “orient” part of the OODA loop. Carrico described four components of an autonomy infrastructure in Figure 6.
In his assessment, and in agreement with Hamel and Langston, Carrico noted “cognitive agents” (i.e., tailored artificial intelligence programs) will be critical for curating and processing the massive data flows in a MDC2 system. Carrico envisions an MDC2 system contain-ing multiple cognitive agents working alongside human operators as a single team. In addition, cognitive agents are also capable of performing secondary and tertiary analyses to provide context for information. Hamel and other participants noted data curation and autonomy will be integral for handling the large data sets and presenting information to the commander for rapid decision-making.
Iterative Systems
Several participants noted in order to keep pace with the data flow and analyze data autonomously in support of warfighter needs, the core systems and software will need to undergo constant refresh—like the data they process, they too will need to be iterative in nature and not static. Winston commented this is a key facet of MDC2 that requires constant refresh and updates to handle the changing data load. As data moves through the pipeline where models and analyses are continuously updated, it changes the way in which future data is treated and often points to new important data sources. Often the data is unstructured, and new forms of data will be introduced to the system. As Hamel observed, MDC2 systems must be iterative and incremental in development, and capability increments should be manageable with practical schedules for scope, cost, and deployability.
Capabilities-Based Development and Support/Operators Integration
The USAF’s MDC2 systems will need to be developed iteratively with regular incremental adjustments, upgrades, and changes—especially in light of the accelerating pace of development in information technology and the rapid evolution of command and control requirements. Several participants throughout the technology and acquisition discussions highlighted this point. Thorp characterized it as the need to focus on capabilities-based outcomes rather than requirement-based processes. Normally, development programs are defined by a list of requirements that are informed by capability needs, but they are also “set in stone,” as one participant noted. To maintain pace, Hamel stressed the need to focus development of MDC2 systems on capabilities over set requirements. He added that it is nearly impossible to define detailed operational and systems requirements for rapidly evolving information technologies and C2 operational needs.
Hamel and other participants observed a development methodology based on the integration and continuous engagement among operations, developers, technical experts, and PMs is critical to ensuring the necessary iterative systems development aligns with needed capabilities in the field. Hamel stated it is impossible to envision and define detailed operational and systems requirements for rapidly evolving information technologies and operational C2 needs. Crider noted later that “data is close to the mission” and that the “mission owners” or operators have the most insight into the data, as they “collect it, store it, live and die by it.” Understanding the needs of such a system necessitates close collaboration with operators. Lt. Gen. Thompson (vice commander, Air Force Space Command, USAF) suggested the need to engage with the warfighter as early in the development process as possible.
Prototyping and Commercial Technology Adoption
Key to the strategy of iterative systems development will be prototyping and the use of com-
mercial technologies. As Hamel pointed out, the iterative development process will be informed by experimentation and rapid prototyping, including the adoption of available commercial technology where possible and appropriate. The private sector is far ahead of the federal government in data management systems, as noted by Langston, Kern, and other participants. Close monitoring of commercial developments and the rapid testing of new systems through prototyping will be critical to the development of MDC2 systems.
Langston suggested prototyping would allow the government to look into all buying opportunities and see what is available and feasible before committing to a program of record. Munson contended the government should act as the lead integrator of a prototyping process while partnering with an industry integrator who can take the prototype and develop it into what he termed an “industrial strength”5 design that can withstand the stresses of its intended mission. Munson also stressed prototyping and experimentation can provide constant information updates to the iterative development process and help the USAF explore means of technology insertion and testing. Langston suggested a tangible first step in prototyping for MDC2 would be to commission a series of rapid prototypes to test and flesh out infrastructure needs by starting with data sharing.
Langston described the DoD’s, and by extension, the USAF’s “make” instead of “buy” culture with a focus on inventing new technology over purchasing what is already available. Given the speed of commercial development, he added, this exasperates the challenge of maintaining pace with technological developments. He noted commercial technology often requires the government to purchase a license to operate, although he mused this does not seem to pose a challenge to desktop computers used by the government and questioned why this is an issue elsewhere.
Maybury observed that the “center of gravity” in information technology is in industry and not the government. If technology procurement and adoption are to keep pace with the warfighter’s needs, there will need to be strong commercial engagement, technology adoption, and acquisition. Hamel added that given the head start and faster development rate in the commercial sector, the adoption of commercial technology is inevitable. Cloud computing, storage and processing technologies for massive data sets, tailored interfaces and cognitive agents, and machine learning and artificial intelligence were identified by several participants as critical technologies, already ubiquitous in the commercial sector, that will need to be leveraged for multi-domain systems.
_________
5 Munson stressed that a prototype is designed to prove a concept and does not necessarily directly translate into a fully deployable system.
NEW ACQ METHODS AND AUTHORITIES FOR ITERATIVE DEVELOPMENT OF MDC2 SYSTEMS
Critical to the iterative development process of MDC2 systems will be rapid acquisition methods and mechanisms. Tailoring acquisition methods and mechanisms to the specific characteristics of a program was also stressed by several participants and was a focus of Jan Kinner’s (Professor, Defense Acquisition University) presentation. Presenters and other participants at the workshop introduced and discussed several potential acquisition mechanisms (both old and new) and newly delegated Service level authorities that may be employed to this end, including middle tier acquisition (MTA, also referred to as Section 804) and other transaction authorities (OTA).
Danny Nelson (Defense Innovation Unit) provided details on OTAs during his presentation. OTAs provide a mechanism for rapid-prototyping development when certain criteria are met, including when the prototype project is directly relevant to enhancing military effectiveness, when competition to the maximum extent is allowed, and when the data from the project informs follow-on production. Several participants noted its importance for MDC2 systems development. Carrico argued that while not ideal for all acquisition, OTAs are ideal for prototyping and rapid deployment. Hamel observed OTAs can enable more rapid development and deployment of operational capabilities.
MTA, as described by Brett Scheideman (Execution Oversight Division of the Office of the Deputy Assistant Secretary for Acquisition Integration (SAF/AQXE)), is an approach to rapid acquisition that focuses on delivering capability in short timeframes (2-5 years) via rapid prototyping and rapid fielding. MTA allows program
offices to avoid some of the bureaucratic hurdles experienced by other acquisition programs by focusing on the deployment of prototypes and upgrades for existing systems. Several participants commented on the usefulness of MTAs for the iterative development process critical for MDC2 systems.
CONCLUSION AND CLOSING THOUGHTS
The workshop closed with a “round-the-table” wrap up in which participants were able to identify their key takeaways and offer closing thoughts. The major themes and issues identified among the participants provided the outline for this proceedings. Many participants discussed the need for horizontal alignment in the following areas: information technology infrastructure, requirements, common doctrine, program management, the need to adopt cyclical and recurring processes in command and control, data management, systems development, operator/support integration, prototyping, commercial adoption, and rapid acquisition methods and mechanisms. Several participants observed that the development of MDC2 systems is a critical enabler of future military operations and necessary to deter and win future conflicts. In his closing statements, DeMaio noted the historical challenge facing the USAF as it adapts itself to future conflicts. He quoted the military historians Williamson Murray and Alan Millet who wrote, “Very infrequently do militaries choose to adopt that which is revolutionary and implement it and win.” Bowlds noted the last day of the workshop coincided with the 49th anniversary of the Apollo 11 Moon landing, suggesting that greater technological feats have been accomplished in the past.
DISCLAIMER: This Proceedings of a Workshop—In Brief has been prepared by Steven Darbes as a factual summary of what occurred at the meeting. He was assisted by Kevin Suchernick. The committee’s role was limited to planning the event. The statements made are those of the individual workshop participants and do not necessarily represent the views of all participants, the planning committee, or the National Academies. This Proceedings of a Workshop—In Brief was reviewed in draft form by Col. Douglas DeMaio, Curtis E. LeMay Center; Lester L. Lyles (NAE, Gen., USAF, ret.), Independent Consultant; and Starnes E. Walker, University of Delaware, to ensure that it meets institutional standards for quality and objectivity. The review comments and draft manuscript remain confidential to protect the integrity of the process. All images are courtesy of workshop participants.
PLANNING COMMITTEE: Michael A. Hamel (Lt. Gen., USAF, ret.), Workshop Chair; Charles H. Jacoby, Jr. (U.S. Army, ret.), Capitol Peak Asset Management; Mr. Kirk Kern, NetApp; Marv Langston, Independent Consultant; Mark Maybury, Stanley Black & Decker; Julie J.C.H. Ryan, Wyndrose Technical Group; Rebecca Winston, Winston Strategic Management Consulting.
SPECIAL THANK YOU: Ted Bowlds, Gary Kyle, Douglas DeMaio, Gregory Spanjers, and Sheryl Thorp for their support and advice throughout the planning and conduct of the workshop.
RAPPORTEUR: Steven Darbes, Research Associate, Air Force Studies Board.
AFSB STAFF: Steven Darbes, Research Associate; Kevin Suchernick, Research Assistant; Marguerite Schneider, Administrative Coordinator; Joan Fuller, Deputy Executive Director for National Security Programs; Ellen Chou, Board Director; Ryan Murphy, Program Officer; George Coyle, Senior Program Officer.
SPONSORS: This workshop was supported by the U.S. Air Force.
Suggested citation: National Academies of Sciences, Engineering, and Medicine. 2018. Multi-Domain Command and Control: Proceedings of a Workshop In-Brief. Washington, DC: The National Academies Press.
doi: https://doi.org/10.17226/25316.
Division on Engineering and Physical Sciences
Copyright 2018 by the National Academy of Sciences. All rights reserved.












