Proceedings of a Workshop
| IN BRIEF | |
|
March 2019 |
The Convergence of Violent Extremism and Radiological Security
Proceedings of a Workshop—in Brief
INTRODUCTION
Thirty scientists, engineers, analysts, and other security-oriented specialists from six countries gathered December 10-12, 2018, in Helsinki, Finland, for a workshop on the convergence of violent extremism and radiological security. Discussions focused on regional and national trends, particularly in politically unstable areas where extremists and disenfranchised groups could access radiological sources and use these sources as weapons of terrorism. This was the third workshop sponsored by the National Academies of Sciences, Engineering, and Medicine (the National Academies) and the Russian Academy of Sciences (RAS) concerning global concerns about the activities and intentions of individuals or dissident organizations that threaten security in a number of countries. Two-thirds of the participants were from the U.S. and Russia, with the remainder from Finland and three other European countries. In addition, senior officials from the Ministries of Defense and Foreign Affairs of Finland joined the conference participants at an informative reception during the second day of the workshop. The primary goal of the workshop was to contribute to U.S., Russian, and European appreciation of how, why, when, and where radiological terrorism could be a near-term outcome of the spread of violent extremism and highlight opportunities for international collaboration to prevent such terrorism. Also, the workshop was designed to consider the benefit of subsequent interactions between U.S. and Russian specialists with attention to the types of expertise, themes, and structure of such follow-on activities.
The workshop began with a welcome by Timo Hellenberg, a national security expert from Finland, who provided background on Finland’s interest in the challenge of radiological terrorism. During the first two days of the workshop, participants elaborated on abstracts they had submitted prior to the workshop. There were opportunities for all participants to comment on each presentation. Of particular importance was a keynote presentation by Matti Vanhanen, Chairman of the Foreign Affairs Committee of the Parliament and former Prime Minister of Finland. He linked political concerns at the highest levels throughout much of Europe to the theme of the workshop. During the second and third days of the workshop, participants divided into two Breakout Groups for in-depth discussions of (1) motivation, responses, and coordination, and (2) organizational and policy issues. Summaries of the Breakout Group discussions were presented in a plenary session followed by observations and discussion by workshop participants. The format worked well in encouraging contributions by all participants.
The following section summarizes the presentations by workshop participants and presents figures from the presentations. This section is followed by summaries of Breakout Group deliberations. The report concludes with a list of topics for future work and collaboration, as suggested by individual workshop participants.
PRESENTATIONS BY WORKSHOP PARTICIPANTS
Historical Perspectives
The first panel provided historical perspectives on violent extremism and radiological security and background on efforts to address these threats.
Risto Volanen, State Secretary of Finland (Retired). The Finnish Case of Building Democracy through Crisis While Taming Radicalization. In 1918, a large population of moderate citizens who had been involved in civic self-education was strong enough to prevent a socialist revolution and restrain a monarchist coup. Then, in the 1930s, civic and self-
![]()
education were again essential complements to government efforts to defend against a rising right-wing coup. Finally, when a Finnish minority and Russian counter-revolutionaries considered interventions along the Finnish-Soviet border, the United Kingdom intervened to help calm interventionist tendencies, while, on the Soviet side, the traditional Russian geo-political priority for Nordic stability prevailed.
Alexander Nechaev, St. Petersburg Institute of Technology. Once Again to the Problem of the Dirty Bomb. Seven large and a few small enterprises produce over 2,000 types of radionuclide sources for about 16,000 consumers throughout Russia. Nearly 200,000 sources are in use with activities up to 1016 becquerel (1 event of radiation emission or disintegration per second) per item. During the past 70 years, 355 over-exposure incidents have been reported in the USSR/Russia, with 94 incidents harming 171 victims, including 16 fatalities. The only approach to prevent "actions with unclear motivations" is ongoing improvement of strict control in executing regulatory, technical, and education measures of safety and security throughout the life cycles of radioactive materials and devices. (Figure 1)

SOURCE: Alexander Nechaev. (From Risovanii V.D. Rosatom. Forum “Cities and Nuclear Technologies,” Obninsk).
Glenn Schweitzer, National Academies of Sciences, Engineering, and Medicine. U.S.-Russia Inter-Academy Collaboration in Analyzing Violent Extremism and Radiological Security. Examples of early inter-academy collaboration were (a) the well-established Russian network for monitoring ethnic tranquility and conflicts throughout regions of the USSR and (b) American security approaches in protecting large metropolitan areas from terrorists with advanced weapons. At a previous workshop, participants visited waste storage sites in Russia. Other topics of interest for future collaboration include foreign fighters with technical skills in the Middle East, the role of social media in promoting extremist views, trends in radicalization/deradicalization, and transport of radioactive metallic scrap across borders, which has been reported in a number of countries.
Linkages Among Extremism, Terrorism, and Radiological Security
In the next panel session, presenters gave their perspectives on linkages between major workshop themes.
Roman Lunkin, Russian Academy of Sciences (RAS), Institute for Europe. Is There a Threat of Religious Terrorism? True and False Images of Extremists. Following 9/11, the escalation of conflict in the Middle East and the migration crisis in Europe, it became clear that a central problem for the relevant government agencies was difficulty in understanding the behavior, appearance, and inner-workings of religious groups in many countries. Security policy should preserve the balance between scrutiny of religious groups and adjustment of religious rules to accommodate interests of society, labor rights, and the economy. There are true extremists: the military involved in conflict, others prepared for action, and others demanding action. But there are also false extremists, such as religious fundamentalists who oppose secular rules, those who claim superiority of their identity, and missionaries who claim the superiority of their religious views in both sermons and politics.
Scott Atran, Oxford University. Terrorism, Revolution, and Intractable Conflicts. While ISIS may have lost its state (caliphate), it retains the allegiance of many supporters of its core values. The underlying political and confessional conflicts that caused recruits initially to embrace ISIS haven’t appreciably changed, and social networks remain an important source of volunteers for groups such as ISIS. Terrorists may seek ways to interfere with controls on radioactive materials through spoofing systems, false flag attacks, and flooding the field with misinformation, causing crises to escalate. Consideration should be given to a U.S.-Russia-China early warning cyber activity to share data, intelligence on threat, and attack practices. (Figure 2)
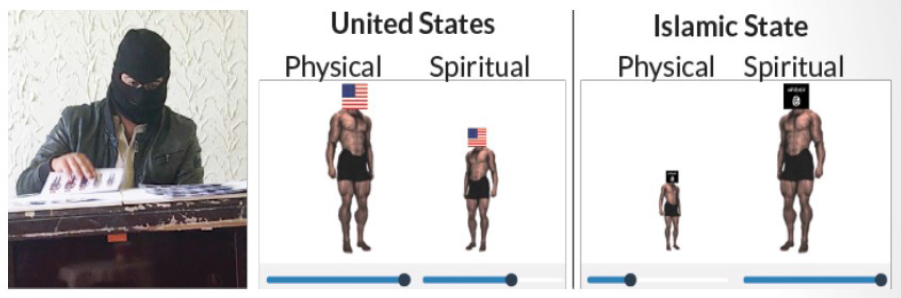
SOURCE: Scott Atran. (From Gómez, López Rodriguez, Sheikh, Ginges, Wilson, Waziri, Vázquez, Davis & Atran. “The devoted actor’s will to fight and the spiritual dimension of human conflict,” Nature Human Behavior 1, 674-679 (2017)).
Stepanov Kalmykov (Corresponding Member, RAS) Moscow State University. Nuclear Forensics: From Nonproliferation to Crime Cases. Nuclear forensics call for investigations of the source, age, trafficking, and isotope enrichment of the material of concern. One of the most common approaches is to study particle releases from venting systems and also during on-site inspections. By using various spectroscopic and microscopic methods, it is often possible to ascertain the origin and source of the material in question. Examples were presented of the application of the techniques for both environmental and criminal investigations (Figure 3)
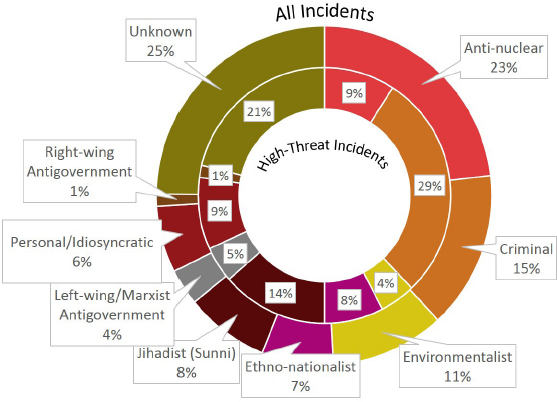
Gary LaFree, University of Maryland. Willingness and Capacity of Terrorist Organizations to Use Radiological Weapons. The world has experienced very few terrorist radiological attacks and no nuclear attacks by terrorists. One way to operationalize the threats of these rare forms of attack is to examine worldwide terrorist organizations in terms of their (a) willingness to mount mass casualty attacks, herein limited to chemical, biological, radiological and nuclear (CBRN) attacks, and (b) demonstrated technological capacity. For context, the Global Terrorism Database helps provide an overview of terrorist attacks over time and space and permits investigation of the most active organizations, the most fatalities from attacks, the deadliest attacks, and the most complex attacks. The data also indicate the most frequent sources of CBRN attacks, organizations receiving the most fatal CBRN attacks, those with the most total CBRN attacks, and those with the most fatalities from these attacks. Relying on these and related analyses, ten emerging hot spots concentrated in the Middle East, North Africa, and South Asia have been identified. (Figure 4)
Audrey Kurth Cronin, American University. Terrorism and Emerging Technologies. Traditional means of determining terrorist group weapons choices are outdated, putting us at risk of inaccurately forecasting future radiological weapon use. Models are based on data from the past 50 years or so, too narrow a historical lens
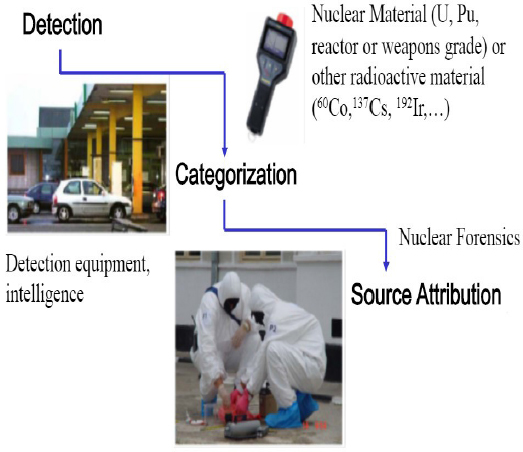
SOURCE: Presentation by Stepanov Kalmykov on nuclear forensics, December 10, 2018.

SOURCE: Presentation by Gary LaFree on willingness and capacity of terrorist organizations to use radiological weapons, December 10, 2018.
in a time of open technological innovation comparable to the late Industrial Revolution. Commercial processes now drive clusters of technologies such as small unmanned aerial vehicles (UAVs), additive manufacturing, smartphones, CRISPR technology, facial recognition technology, and simple robotics, which are available to everyone. To predict future radiological terrorism, we must move beyond “dual use” to consider a more complex range of individual actors, including highly trained “insiders,” professional consumers (prosumers), hobbyists, tinkerers, and amateurs—some of whom may have access to radiological material and nefarious purposes in mind.
Konstantin Bogdanov, Institute for World Economy and International Relations (Moscow). Unmanned Systems and Radiological Weapons: The Nexus of Extremists and Terrorists.The terrorist threat posed by drones, including those carrying weapons of mass destruction, is not new. But in recent years, the community of drone hobby enthusiasts has become booming with online forums that openly discuss technology aspects. This unprecedented development enables potential terrorists to improve their technical skills, recruit appropriate engineering talent, find suitable equipment suppliers, and order the manufacture of airframes or hulls for drones and guidance components. The counter-terrorism response is complicated with unequal tradeoffs of (a) personal freedom and technology progress for (b) security and predictability. (Figure 5)
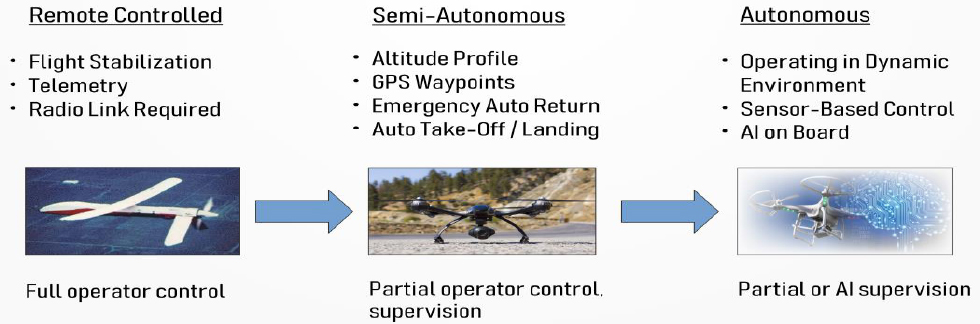
SOURCE: Presentation by Konstantin Bogdanov on unmanned systems and radiological weapons, December 10, 2018.
Gary Ackerman, State University of New York (Albany). Terrorist Threats to Nuclear Facilities and Radiological Materials: Trends and Emerging Issues. The Nuclear Facility Attack Database provides new insights into the threat of attacks on nuclear facilities holding radiological materials. It underscores the significant role played by insiders, opportunities provided to extremists by the increasing nexus between use of radiological materials and zones of instability, and impact of a variety of new technologies on facility security. Examples of particularly significant technologies are cyber threats (which could be facilitated by artificial intelligence) and unmanned or autonomous systems. Several cases of radiological-oriented terrorism illustrate broader findings from scrutiny of available databases. (Figure 6)
Thomas Bielefeld, Nuclear Security Research and Consulting (Erlangen). Evolution of Terrorists’ Tactics in Use of Technology and Means of Recruitment: Implications for Nuclear Security. ISIS and other terrorist groups have had access to radioactive materials in Syria and Iraq as well as the technical expertise to make dirty bombs. Although it remains unclear if ISIS actually intended to engage in radiological terrorism, their activities in the Middle East and in Europe relied on innovative elements, including drones, which may pose serious challenges for nuclear security. Insider threat detection and mitigation policies need to be adapted to address rapid and covert radicalization processes among ISIS-militants. Scenarios in which terrorists coerce trustworthy employees into facilitating attacks on nuclear facilities have become more likely.
SOURCE: Presentation by Gary Ackerman on terrorist threats to nuclear facilities and radiological materials, December 11, 2018.
The war in Syria and Iraq, wherein terrorists gained unimpeded access to radioactive materials, including from medical sources, offers a stark warning and showed that there are no international contingency plans. (Figure 7)
Sergey Krasnoperov, RAS Institute for Nuclear Safety. Research Priorities in Addressing Risks and Capabilities of Unauthorized Use of Radiological Sources by Extremists and Terrorists. Even if direct radiological consequences of an incident are small, the social and economic impacts can be significant. The scale of these impacts is determined by not only radiation parameters, but also by effectiveness of the response system, which should provide clear indications of safety. The major part of the social and economic damage from misuse of sources will come from limited radioactive contamination of critical infrastructure that is spread over large areas, and particularly where contamination exceeds health and safety norms. Special efforts to isolate contamination hot spots from the public may be necessary. (Figure 8)

SOURCE: Thomas Bielefeld.
National and International Policies and Programs
In the next session policies to address the challenge of radiological security were discussed.
Kenneth Brill, Former U.S. Ambassador to International Atomic Energy Agency (IAEA). U.S.-Russian-European Collaboration to Prevent Nuclear Terrorism: Using the Amended Convention on Physical Protection of Nuclear Materials (A/CPPNM). Despite international attention for securing nuclear and radioactive material, the global security regime remains largely a patchwork of non-binding recommendations, checklists, and voluntary action plans, with only a few narrowly focused legally binding agreements. The IAEA emphasizes nuclear security, but it can only inform and recommend, not compel action. In contrast to the largely static nuclear security regime, terrorist groups and nuclear technology are dynamic and evolving. The A/CPPNM, along with the leadership of key states, provides an opportunity for developing a global nuclear security regime that is capable of providing a sustained focus and action on evolving threats to nuclear and radiological security to prevent dangerous material from falling into the wrong hands.

SOURCE: Presentation by Sergey Krasnoperov on research priorities in addressing risks and capabilities of unauthorized use of radiological sources by extremists and terrorists, December 11, 2018.
John Bernhard, Former Ambassador of Denmark to IAEA. International Legal Framework for Radiological Security. In many countries, radioactive material is found in stocks of waste from nuclear power plants and such material is used widely in the health and industrial sectors. Since 1993, the IAEA has registered about 2,000 cases of illicit trafficking or loss of radioactive material. There is an obvious need for strong national and international measures to prevent access to radiological material by terrorists and other criminals. The importance of establishment of binding international standards and a credible regulatory regime for radiological security is clear.
Stiina Rajala, National Bureau of Investigation of Finland. Trans-Eurasian Organized Crime. At present there are no obvious linkages between organized crime and illegal acquisition or smuggling of nuclear materials in Finland or across Finnish borders. Of course there are concerns about the smuggling of drugs, cigarettes, and other goods, including some products that cause health hazards. Of possible future concern is the experience of the illegal drug market, which is in constant change and involves trafficking in electronics, counterfeit medicines and chemicals, power tools, and spare parts. Cross-border cooperation involving Europol, Interpol, Schengen, Eurojust, Frontex, and bilateral partners will continue to be important.
Anton Khlopkov, Institute for Energy and Security (Moscow). US-Russian Cooperation in Radiological Safety and Security. Two regional workshops in Central Asia have emphasized national threat assessments involving multiple agencies in each country, installation of radiation detection equipment along national borders, detection of illicit source trafficking, and table-top regional exercises. A number of regulatory documents on physical protection of sources in use, storage, and transport have been finalized. National regulations are being harmonized with guidance issued by the IAEA. Additionally, national orphan-source recovery campaigns have been initiated. Repatriation of disused sources that were sent abroad is vital.
William Courtney, Rand Corporation. U.S. Policy in Countering Radiological Terrorism. Through diplomacy, law enforcement, and other channels, the U.S. works with partners to stop illicit nuclear-related transactions, seize and dispose of sensitive items, and penalize associated individuals and entities. Also, the U.S. is addressing nuclear proliferation issues involving North Korea, Iran, India, and Pakistan, while supporting relevant global efforts such as the Proliferation Security Initiative to stop trafficking related to nuclear weapons. The U.S. Department of Energy is assisting other countries in improving their nuclear materials accounting systems and their reporting of incidents to the IAEA. For example, the Department of Energy has an incident response program to investigate and resolve reports of stolen or misplaced radioactive materials and attempts to assemble improvised nuclear devices.
Juba Rautjarai, Radiation Regulatory Agency of Finland (retired). Role of the Radiation Regulatory Agency of Finland in Implementing National Strategy for Comprehensive Security. The Finnish national authority referred to as STUK is responsible for supporting (a) the national strategy for comprehensive radiation security, and (b) chemical, biological, radiological, nuclear, and explosive (CBRNE) activities in two main ways: compliance with radiation regulations and maintenance of expertise as a real-time support service for radiation events. Of particular interest are (a) the national Radiation Nuclear Detection Capability Architecture and the related capacity-building project of 2012-2016, and (b) the Finnish-Estonian demonstration of cross-border expert support for nuclear security in November 2017. Coordination of national and regional capacity-building are complex due to necessary involvement of many different authorities and other stakeholders in the implementation of required activities.
Kari Perajarvi, Radiation and Nuclear Safety Authority of Finland. Remote Expert Support and Nuclear Security. In many countries, primary and secondary inspection instruments are operated by front-line officers. If needed, mobile expert support teams may also be deployed to carry out field activities. Both field actors may need remote technical, scientific, and/or operational support. Of critical importance are reliable and secure data transfer and communication channels along with data management and analysis tools.
Michel Bijak, University of Lódz, Poland. Preparedness of First Responders for Radiological Threats as a Key Element of a Public Security System. Police patrol officers, along with local firefighters, are often the first responders to serious incidents or accidents. They may confront unknown hazards, including radiological hazards. Police officers are in control of immediate actions at the scene and should be prepared to confront a range of often unique challenges, including recognition of radiological hazards. In some countries such as Poland, there are no CBRN training exercises; and throughout Europe there are large gaps in training for responding to radiological incidents. As one example, in April 2015 police were confronted with a number of industrial radiological sources that had been stolen by scrap metal collectors. The ability of police to respond to basic issues concerning contamination and health effects at the scenes of such radiation incidents needs prompt attention. (Figure 9)

SOURCE: Presentation by Michel Bijak on the preparedness of first responders for radiological threats, December 12, 2018. (From http://www.policja.pl/pol/aktualnosci/110914,Zatrzymano-podejrzanych-o-kradziez-izotopow-kobaltu.html).
Important High-Ionizing Radiation Sources
The following session focused on high-ionizing radiation sources.
Evgeny Papynov, Far East University (Vladivostok). Secure Matrixes for Ionizing Radiation Sources Based on Cesium-137 (137Cs) and Technology of Their Production. 137Cs is widely used in gamma-defectoscopy. Cores of ionizing radiation sources are made from cesium chloride. However, its high solubility in water and corrosion activity do not provide secure sealing, and they lead to possible radioactive contamination. Ceramic materials based on natural and synthetic alumosilicates obtained via Spark Plasma Sintering (SPS) technology are an appropriate alternative. SPS is unique due to heating provided by electric pulses passing through the powder material in the dye. The final product’s specified lifetime exceeds 20 years. This high-tech solution is unique. (Figure 10)
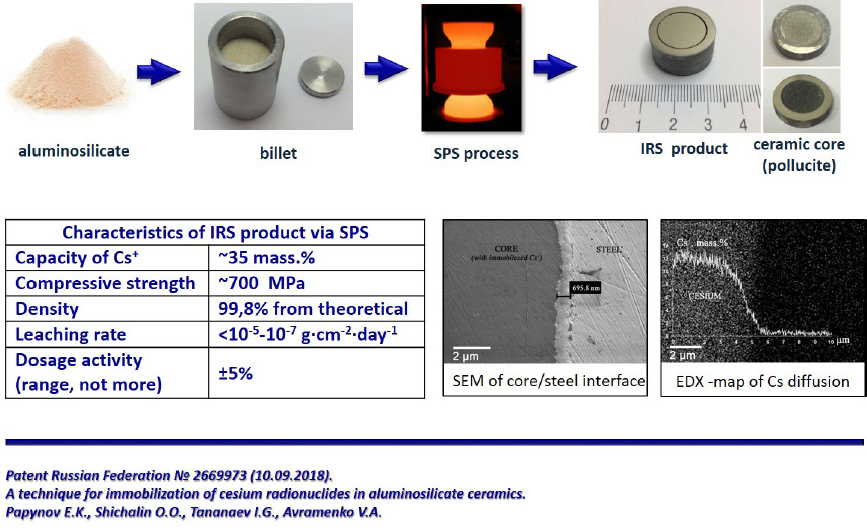
SOURCE: Presentation by Evgeny Papynov on secure matrixes for ionizing radiation sources, December 12, 2018.
Charles Ferguson, National Academies of Sciences, Engineering, and Medicine. Reducing Reliance on Cesium 137 and Other Sources of Concern. Progress has been significant in developing alternative technologies for uses of radiation sources—particularly Cesium 137—which is being rapidly phased out in the U.S. and a number of other countries. Other examples of alternative technologies for different applications that are being introduced include: (a) X-ray devices for irradiating blood to prevent graft versus host disease; (b) alpha particle accelerators for use as neutron sources in oil well-logging; (c) LINAC for tele-therapy cancer treatment; (d) ultrasonics for radiographic examination of welding procedures; and (e) use of eddy currents and thermal imaging for neutron gauges in the steel industry.
Dealing with Disposed, Damaged, or Lost Radiation Sources
In the final panel, challenges of safely dispose of sources of radiation were highlighted.
Laurin Dodd, U.S.-based Consultant. Radiological Challenges in the Chernobyl Zone. Sources of radioactive and contaminated materials of current and future concern include: (a) reactor fuel and irradiated structural material and mixes; (b) buried and stored contaminated equipment from construction of the sarcophagus surrounding Unit 4 immediately after the Chernobyl accident; (c) irradiated fuels from research activities; (d) massive quantities of spent fuel containing masses that will be removed from the New Safe Confinement Facility; and (e) cleanup and decommissioning of reactor Units 1-3 that have produced large quantities of liquid and solid radioactive waste. Since the 1986 accident, large amounts of radioactive substances have been lost due to inadequate security, possible misuse of materials due to delays in payment of employees, and pressure to generate funds from unauthorized use of materials. Also, the loss of Russian experts has left gaps in management of radioactive materials, particularly during research activities. (Figure 11)

SOURCE: Presentation by Laurin Dodd on radiological challenges in the Chernobyl zone, December 12, 2018.
Charles Streeper, Los Alamos National Laboratory. Sustainable Security through International Source Repatriation. Ensuring that there is a viable and effective pathway for identifying, packaging, transporting, and disposing of disused radioactive sealed sources is an essential component for end-of-life management strategies that support sustainable and permanent threat reduction. The Offsite Source Recovery Program is a U.S. Department of Energy program for the repatriation of disused U.S.-origin sources, and has involved repatriation of more than 3,000 sources totaling over 75,000 Ci (defined as 3.7 x 1.10 transformations per second) from 27 countries. Each mission involves a unique set of circumstances and planning challenges. However, the processes employed —from identification of the sources to packaging and shipping them—follow proscribed procedures. This abstract has been authored by Triad National Security, LLC under Contract No. 89233218CNA000001 with the U.S. Department of Energy/National Nuclear Security Administration. The U.S. Government retains and the publisher, by accepting the article for publication, acknowledges that the U.S. Government retains a non-exclusive, paid-up, irrevocable, world-wide license to publish or reproduce the published form of this abstract, or allow others to do so, for U.S. Government purposes.
Vladislav Petrov, (RAS Corresponding Member), Institute of Geology of Ore Deposits, Petrography, Mineralogy, and Geochemistry (Moscow). Experimental and Theoretical Modeling of Radio Nuclide Migration and Safety. Underground Burial of Liquid and Solid Radioactive Waste in Russia. Russia is the only country where injection of high-level and intermediate-level liquid waste in deep seated aquifers confined from top to bottom by low level permeable layers is carried out on an industrial scale. Half-lives of many radionuclides from the waste exceed thousands of years. Mathematical modeling is the only reasonable method for assessing their burial safety. Original computer codes have been developed for calibration of containment plume movement at the injection sites and for simulation of the movement with regard to buoyancy forces due to different densities of waste and formation water. (Figure 12)
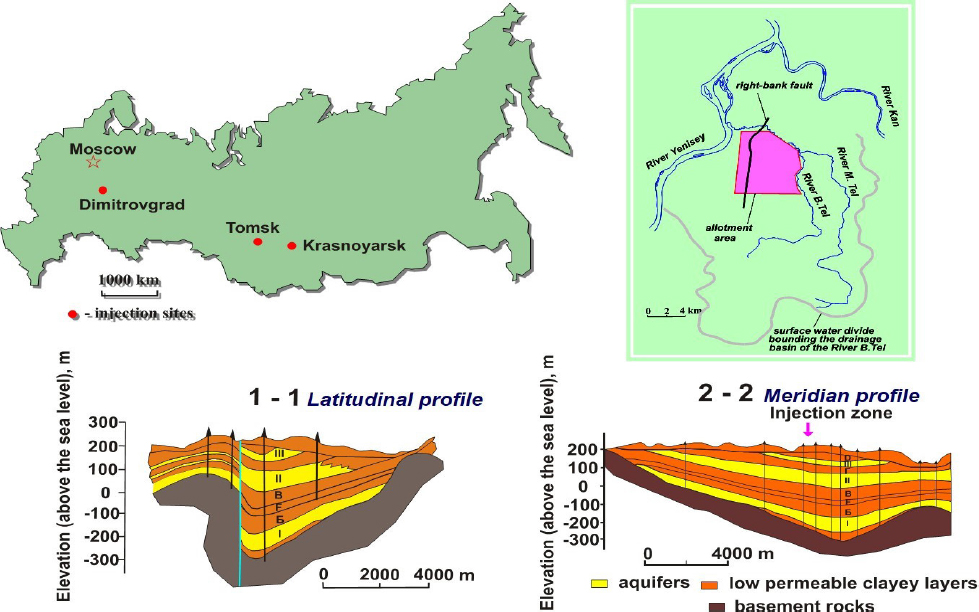
SOURCE: Presentation by Vladislav Petrov on experimental and theoretical modeling of radio nuclide migration and safety, December 12, 2018.
Mikhail Diordiy, State Enterprise RADON (Moscow). Spent Radiation Sources Storage in Containers to Prevent Terrorism and Extremism. Medium activity sources can create considerable anxiety. Often these sources are used in portable devices for gamma and x-ray defectoscopy in industry, medicine, and geology. Smoke detectors based on plutonium and other devices based on trans-uranium nuclides are of special concern. RADON has developed different container/storage facilities for the collection, conditioning, long-term storage, and disposal for a variety of types of sources. Also, special transportation equipment, monitoring/access control systems, and centralized facilities ensure the proper management of different types of spent fuel. (Figure 13)
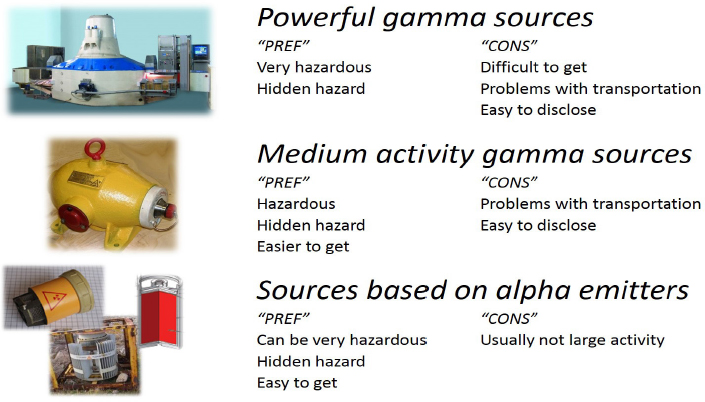
SOURCE: Presentation by Mikhail Diordiy on spent radiation sources storage in containers to prevent terrorism and extremism, December 12, 2018.
COMMENTS OF INDIVIDUAL WORKSHOP PARTICIPANTS
During the discussions following each presentation, individual participants highlighted emerging challenges, as well as positive developments for increased security.
Emerging Challenges
- Fortunately there has not been a major radiation terrorism catastrophe, but the likelihood of a disaster increases as the technology awareness and capabilities of extremists grow.
- It is not clear how/why dangerous and poorly protected radiation sources in Mosul, Iraq, were not used in radiological weapons by ISIS.
- Terrorist organizations will increasingly use social media in developing countries to raise awareness of the threat of stealing or otherwise obtaining radiation sources as they press their political demands.
- While potential uses of new technologies such as drones to mount radiation-based attacks deserve prompt attention, long-standing approaches of simply placing radiation sources in sensitive areas using ground vehicles should not be forgotten as terrorists search for any type of material or device that will cause havoc.
- Radiological security located near or within soft targets, including safety of audiences during large-scale outdoor or indoor events, needs more attention and calls for cooperation among many individuals and organizations that have broad responsibilities, such as mayors and other civic leaders.
- Extremism and terrorism (with political and religious motivations) are steadily infiltrating new areas, such as central Africa, where radiation sources are located.
Positive Steps Toward Increased Security
- Strengthening radiological awareness and security in Central Asia, provides the collaborative program of the Russian Center for Energy Security and the U.S. Nuclear Threat Initiative a framework for addressing similar issues in other developing countries.
- The U.S. Department of Energy program that repatriates currently unneeded radiation sources provided by the department is a model approach that should be considered by other countries that no longer need imported sources and by the countries that provided the sources.
- Joint exercises between governments concerning the security of radiological sources can be useful, as demonstrated by Finnish-Estonian cooperation. For example, in an illicit trafficking case, real-time expert support from the neighboring country enabled an efficient reaction and effective response to an emerging threat.
- Collaboration (and particularly regular information exchange on radiation issues) among international organizations such as IAEA, INTERPOL, Europol, and European CBRN organizations has been very important.
- Current efforts for developing specialized databases can link the location of dangerous sources with areas of interest to terrorist groups.
COMMENTS DURING BREAKOUT GROUPS
Following the presentations and discussions, two breakout groups were established. Below are selected comments made by individual workshop participants in each breakout group.
Breakout Group 1: Motivation, Responses, and Coordination
While it is impossible to predict individual radiological incidents, several group members noted that it is possible to anticipate both well-known and new tactics by dissidents to use radiological targeting or broad contamination as terrorist weapons. Participants discussed the need to enhance situational awareness within the security community to the spread of new technologies as well as to tactical capabilities for attacks with radioactive sources. These radioactive sources could be embodied in explosive devices, scattered from moving vehicles, or simply placed in crowded areas. Of particular concern is the psychological impact of radiological attacks that could lead to panic-evacuation of contaminated areas or other actions that disrupt everyday activities due to the threats of contamination.
A number of group members highlighted that the doctrines of dangerous groups which express interest in radiological weapons—such as the so-called “sovereign citizens,” religious fundamentalists, and extremists—should be studied, understood, and challenged. Monitoring of religious and political radicalism was also noted as important. Some data sets indicate that 90 percent of terrorist attacks are domestically based, but discussions of domestic threats are often constrained due to sensitivity of the topics. If the possibility of radiological activities is suspected, sensitivity increases.
Other participants noted that natural scientists often dominate international exchanges of experts in addressing radiological terrorism. These participants felt that the focus on technical aspects often lacks adequate sensitivity to societal risks and that social scientists should also be involved in exchanges. The social scientists’ experience in studying behavior of individuals and societies when faced with adversities deserves greater appreciation within scientific communities.
Some participants raised the need to prioritize improved security controls and alarms at facilities where radioactive sources are located, particularly in geographic regions experiencing political and/or economic instability. While many organizations and individuals routinely rely on radioactive sources for a variety of purposes, a limited number pose significant dangers. However, in the minds of the general population even small threats in the field of radiation are rapidly amplified.
Many breakout group members emphasized that greater attention needs to be given to responders to actual or perceived radiological assaults. These responders include: (a) first responders, who may have only rudimentary familiarity with radiation challenges but usually have regular contact with nearby hazmat units; (b) journalists who may be the first to communicate with the public; and (c) city officials who will be swiftly called into action. Additionally, crowd-sourcing detection of radiological threats, with smart phones available to collect data regarding threat levels, should be considered. While exercises have been held in some cities, they said, these simulations need to be more widely practiced, as well as further developed and evaluated by experts. The international conferences of city mayors and other leaders of urbanized areas may be good venues for underscoring cross-cutting interests through, for example, red-team and blue-team simulation exercises. Several participants also noted that there is an increasing need for innovative technologies to thwart malevolent use of radioactive sources.
Breakout Group 2: Organizational and Policy Issues
Many group members identified the 2021 review conference, called for pursuant to the Amended Convention for the Physical Protection of Nuclear Materials (A/CPPNM), as an opportunity to address gaps in the global security regime for nuclear and radioactive material. Planning for the 2021 review conference will be active during 2019 and 2020. The A/CPPNM review process will continue after the conference is complete and will provide opportunities to increase international attention to strengthening of the international regime for reducing the threat of nuclear/radiological terrorism while underscoring the importance of responsible handling of all radiation sources from cradle to grave.
This conference will provide an opportunity for important discussion and documentation of best practices, they said, with an emphasis on new and emerging approaches to enhanced management and security as well as practices regarding the handling of a wide range of radiation sources from acquisition to end-of-life disposal.
Breakout group participants were eager to continue and expand the deliberations initiated at this workshop. Several suggested creating a standing nongovernmental working group of experts from the United States and Russia, with partners from other countries as appropriate. Such continued discussions could complement and feed into the inter-governmental deliberations that will be held during the review process. This working group might have opportunities to develop fresh insights that could then be considered by governments and the IAEA for reducing risks from inadequately controlled radiological sources.
Individual participants suggested a range of topics that could be addressed by the working group:
- Assessing types and locations of global vulnerabilities regarding radiological sources in areas that have been familiar terrains for terrorist groups.
- Identifying gaps in current security requirements and practices and assessing ways to address them.
- Wider cataloging of sources, expanded search and recovery efforts, and improved storage and disposal practices in vulnerable countries.
- Development of a worldwide database, or multiple databases, for tracking exports and related disposition of sources, including use of distributed-ledger technology.
- Assessment of policies and methods concerning end-of life management of sources.
- Estimates of the quantity and types of sources of special concern by country—particularly those in long-term storage, at final disposal sites, or at unknown locations, if possible.
- Methodologies and technologies for search, identification, localization, and characterization of sources.
- Technologies for security of sources such as tagging devices for tracking sources.
- Alternatives to conventional radiological sources, including consideration of feasibility and life cycle costs in different regions: Reduced susceptibility to terrorist exploitation (e.g., ceramic encasements); non-isotopic technologies (e.g., x-ray).
- Secure storage and disposal of sources that are no longer in service.
- Research and development priorities, cross-border collaboration, and implementation of findings, joint decision making (TTX) and operational (LIVEX) exercises.
- Choices between known life-cycle costs of traditional radiation sources vs. costs of less certain innovative technologies, including liability insurance and security uncertainties.
- Infrastructure and operational costs: e.g., reliable power and support systems, system sustainability, workforce capability, and service/spare parts.
- Measuring performance of equipment in meeting requirements.
LOOKING TO THE FUTURE
During the final session of the workshop, participants expressed concern that important issues of radiological security may continue to be relegated to secondary status relative to the greater attention placed on aquisition of existing sources of nuclear weapons material. Several participants urged the prompt establishment of the aforementioned working group of experts, including but not limited to U.S., Russian, and European specialists, that could provide details of radiological security to the IAEA and directly to governments participating in the review of the amended Convention on the Physical Protection of Nuclear Material.
Individual participants also raised the following topics for future discussion:
Reducing Likelihood of Threats
- Encouraging U.S., Russian, and other interested researchers to join forces in providing affordable alternatives for 137Cs.
- Developing greater expertise and interest within the social science community concerning radiological terrorism and increased recognition within the natural science community of the importance of assessments of the psychological, social, and economic impacts of inadequately controlled radiation sources.
Identifying Threats
- On-the-ground assessments of capabilities and interests of extremists and disenfranchised scientists, engineers, and medical professionals to obtain access to radiation sources.
- Expansion and effective use of specialized databases that link location of inadequately controlled radiation sources with the presence of terrorist organizations.
- Examples of calls for closures of urban areas where radiation measurements have inexplicably risen to new levels, and resolution of real or perceived problems.
- Importance and cost of radiation monitoring of surface and subsurface water resources near waste sites for radiation-contaminated material and uncontrolled junk sites for scrap metal.
Improving Responses to Threats
- Identifying successes and missed opportunities in providing local law enforcement personnel with radiation detectors, related equipment, and expert support for identifying inadequately controlled sources.
- Increasing technology-related expertise of journalists who cover radiation incidents.
- Increasing operational-tactical CBRN exercises (live and table-top) using external experts in designing the threat scenarios, evaluating the outcomes, and suggesting improvements.
- Improving understanding and capabilities of first responders who determine threat levels associated with radiological incidents, since they are key in reducing politicization before, during, and after incidents.
DISCLAIMER: This Proceedings of a Workshop—in Brief was prepared by Glenn Schweitzer, Flannery Wasson, and Annalise Blum as a factual summary of what occurred at the meeting. The statements made are those of the rapporteurs or individual meeting participants and do not necessarily represent the views of all meeting participants; the planning committee; or the National Academies of Sciences, Engineering, and Medicine.
REVIEWERS: To ensure that it meets institutional standards for quality and objectivity, this Proceedings of a Workshop—in Brief was reviewed by William Courtney, RAND Corporation; Boris Myasoedov, Russian Academy of Sciences; Vladislav Petrov, Russian Academy of Sciences; and Jessica Stern, Boston University. Marilyn Baker, National Academies of Sciences, Engineering, and Medicine, served as the review coordinator.
SPONSORS: This workshop was supported by the Battelle Memorial Institute (U.S. Department of Energy), the Carnegie Corporation of New York, and the Richard Lounsbery Foundation.
For additional information regarding the workshop, visit http://www.nationalacademies.org/PGA/DSC.
Suggested citation: National Academies of Sciences, Engineering, and Medicine. 2019. The Convergence of Violent Extremism and Radiological Security: Proceedings of a Workshop—in Brief. Washington, DC: The National Academies Press. doi: https://doi.org/10.17226/25402.
Policy and Global Affairs
Copyright 2019 by the National Academy of Sciences. All rights reserved.












