3
Unmanned Systems Context
An examination of the U.S. Coast Guard’s potential to make greater use of unmanned systems (UxSs) should address the broader context of technology development, introduction, and diffusion. The Coast Guard’s research and development budget is small, extremely so when compared to that of the U.S. Navy. Budgetary constraints are an important factor in the Coast Guard’s approach to being a “fast follower” that leverages and adapts the technologies developed and introduced by others. A reliance on this approach makes it incumbent on the Coast Guard to be attuned to relevant technology developments elsewhere in the military and the federal government and in the commercial sector.
In staying attuned to these technology developments from other domains, the Coast Guard must make important choices about which technologies to acquire with a number of considerations in mind, some that apply to all organizations that leverage or “fast follow” and some that have particular relevance to the Coast Guard, such as ensuring cybersecurity. This chapter discusses some of these considerations when leveraging unmanned technologies from other domains and sectors, leaving the more detailed discussion of Coast Guard–specific circumstances to later chapters. This chapter begins with an overview of the terminology and nomenclature of the report, such as the specific terms used to describe unmanned vehicles and systems and the meaning of “unmanned” with respect to human control and onboard presence. The chapter then describes the breadth of systems and technologies that can fall under the rubric of UxS when considering the Coast Guard’s workflow. An important point is that the application of unmanned technologies is not limited to mobile assets such as the aircraft, ships, and underwater
vessels that execute the Coast Guard’s missions; it can also include capabilities onboard a vehicle (e.g., intelligent payload) and software systems that operate virtually to provide analytic and decision support.
Following this overview, the chapter discusses how the Coast Guard, like all fast followers that acquire technology from the other sectors, must consider how a candidate technology will integrate with its operations and systems. Systems engineering is especially important to the Coast Guard, which must be confident that UxS will be ready when needed, integrate with assets and personnel, and reliably perform as expected. An important element of that confidence is cybersecurity. When leveraging technologies from other sectors, including the commercial sector, the Coast Guard must be vigilant about cybersecurity risks given its many important missions, including those focused on law enforcement and national security.
Finally, when operating UxS in the air and on the water, the Coast Guard must consider a variety of legal and policy requirements intended to ensure the safety of the civil airspace and waterways, protect individual privacy, and further other interests such as adherence to federal and Coast Guard acquisition guidelines. These requirements are covered in detail in later chapters but are discussed briefly here because they are relevant to the Coast Guard’s ability to acquire and fully exploit unmanned technologies.
UNMANNED SYSTEMS TERMINOLOGY AND CONCEPTS
As UxSs and their enabling technologies have proliferated, a common terminology has taken shape but with a considerable heterogeneity. This section explains the report’s use of the term “unmanned” as opposed to other terms such as “unoccupied”; makes distinctions among remote, automated, and autonomous systems; and highlights the importance of considering a system’s applicability in a context broader than how it is controlled.
“Unmanned” Nomenclature
The term “unmanned” is sometimes replaced by the terms “un-crewed” or “unoccupied.” Although the reasons to use such gender-free terms are sound, the committee elected to use the term “unmanned” to remain consistent with the terminology in the study request and to avoid the implication that the study’s focus is on only vehicles, and even more narrowly on only vehicles with no crew or passengers. The term “unmanned” applies to a range of concepts, from vehicles with no human occupants or human controllers to vehicles with a crew but also some level of remote, automated, or autonomous control. It can also apply to systems and components of systems that are not vehicles, such as intelligent decision aids and autonomous payloads.
To align with this terminology, the report uses the following nomenclature to distinguish between unmanned vehicles and unmanned systems:
- UxV: Unmanned Vehicle, where the “x” can be
- A for Aerial (i.e., UAS is Unmanned Aerial System)
- M for Maritime
- U for Underwater
- UxS: Unmanned System, where the x takes the same values above but encompasses the vehicle as well as other system elements, such as off-board control and data processing, user interfaces, launch and recovery mechanisms, and communications links.
Remote, Automated, and Autonomous Control
The legislative request for this study seeks an assessment of current and emerging unmanned technologies, both autonomous and remotely controlled, for maritime domain awareness applications by the Coast Guard. A key difference between autonomous and remotely controlled systems is straightforward: the former implies a degree of independent action by the system, and the latter implies that a human operator exercises full control. The concept of autonomy, however, can be more difficult to pin down because of the varying degrees of independence from human intervention that a system can exhibit. Sometimes the term “autonomous” is applied to systems that are more appropriately characterized as “automated” because they are controlled by a programmed set of rules or instructions. Automation assumes an operator will make decisions when the automated sequence is not instructed to do through its programmed rules, such as algorithms or specific instructions that govern the course and speed of an automated vehicle. Autonomy, by comparison, implies that the system can independently formulate multiple courses of action and select one to pursue, albeit with human-prescribed objectives that it should conform to. As a practical matter, however, systems can depend on a combination of control mechanisms. Therefore, it can be difficult to draw a clear distinction between what constitutes an “automated” versus an “autonomous” system, or even a distinction between these systems and systems with some elements of remote operation.
Although numerous organizations and academic papers have proposed varying definitions of autonomy (see Appendix D for examples), it is not necessary for the purposes of this report to discuss these many distinctions, or levels of autonomy, in depth because the study charge seeks an assessment of the applicability to the Coast Guard of UxSs generally, presumably spanning the full spectrum of remote control to full autonomy.
Autonomy in Motion and Autonomy at Rest
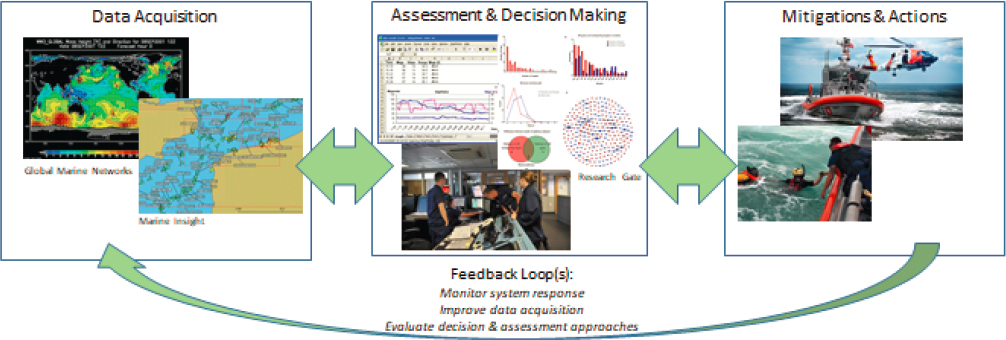
As noted above, UxSs, and especially the more autonomous end of the spectrum, should be viewed as encompassing more than vehicle control systems (i.e., autonomy in motion) to include cyber systems and other technologies that provide intelligent data analysis and decision aids (i.e., autonomy at rest). Figure 3-1 illustrates why both autonomy in motion and autonomy at rest are important considerations. The schematic depicts the workflow involved in deciding whether and when to execute a tactical action—such as deploying a manned or unmanned vessel for an interdiction. The workflow entails data acquisition, analysis, decision making, and action, all connected in a feedback loop that should improve operational and mission performance. Although this workflow has traditionally been performed by humans, autonomous technologies—from artificial intelligence and machine learning to advanced sensor and control systems—can be applied across all three phases to create a faster, more efficient, and more effective feedback loop.
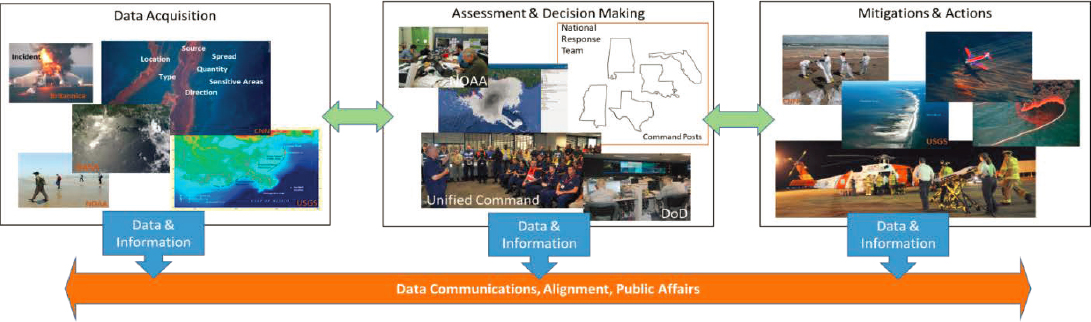
The ability to harness the power of unmanned technologies in all three phases of the workflow can be especially important in complex operations such as the pollution-response event depicted in Figure 3-2. In this example, in responding to the 2010 Deepwater Horizon platform explosion and well blowout in the Gulf of Mexico, the Coast Guard office in Louisiana was responsible for coordinating the deployment and actions of a workforce of 18,000 people and a fleet of 6,000 vessels involved in containment and remediation operations. The office had to align with national protocols for handling pollution-response operations and coordinate with numerous other federal agencies and state and local authorities. Decisive actions required significant quantities and types of data, from initial assessments of the situation to continual reassessments as conditions changed and mitigation activities ensued. Because this major incident occurred a decade ago, the workflow loop did not benefit from significant use of truly autonomous systems. However, its complexity would make it a candidate for the systems available today.
SYSTEMS ENGINEERING AND INTEGRATION
When one considers the applicability of a new technology or system, the desired functioning of that technology or system within larger systems into which it will be integrated must be assured. Indeed, one can point to many historical examples of unmanned technologies that were specifically designed to integrate well, largely because they do not present any special demands for integration. The Predator aircraft, for instance, was designed with enough range to perform reconnaissance missions over long
distances, including at sea, while being operated remotely from land-based facilities rather than placing demands on vessels at sea. Likewise, the Navy has developed both unmanned underwater vehicles and unmanned surface vehicles that can operate for thousands of miles, and can be launched and serviced from a port rather than shipboard.
Increasingly, commercial, off-the-shelf technologies are becoming easier to integrate, mainly because they require minimal integration. For example, it is possible to purchase torpedo-shaped underwater vehicles that can be launched from a ship to complete multi-hour side-scan mapping missions without supervision.1,2 Another example is the popular Roomba™ robot vacuum cleaner. A consumer takes a Roomba™ home, plugs it in, and lets it go. It is not integrated into a higher-level command and control system, lacks a complex user interface, and does not need high-accuracy global positioning system or even room maps. Users quickly learn what the Roomba™ can handle and which parts of the house (e.g., closed doors, stairs, steep thresholds) are barriers. The Roomba™ does enough work to be cost-effective without being perfect—indeed it serves as a good example of a system that is easy to integrate, fulfills a well-defined but limited “mission set,” and is operated with sufficient frequency for users to obtain an intuitive sense of, and trust in, its capabilities.
The Coast Guard, like the other military services, emphasizes sound integration through systems engineering because of the high expectation, or trust, that a system will properly execute its critical functions. A variety of approaches can be pursued to achieve that level of trust and functionality when leveraging systems from the commercial sector or other domains. One example is to leverage systems that can be operated by the supplier’s or contractor’s experienced personnel. Indeed, as will be discussed below, the Coast Guard has successfully used this approach in its ScanEagle UAS program. No special Coast Guard training has been necessary. Another approach is to leverage systems that require only limited integration, as typified by the Coast Guard’s procurement of small tethered underwater vehicles. In this case, a diver operates the vehicle from the shipdeck and generates pictures and verbal reports much in the same manner as during a dive. Here again, no new training or new interfaces are required to build trust in the system. When training is required to operate a leveraged system, its capabilities and integration could be ensured through test operations under a variety of conditions (e.g., sea states, day/night, meteorological).
Considering the premium that the Coast Guard places on shipboard space and crew time on board its ships, systems that integrate well with
__________________
1 General Dynamics. “Bluefin Robotics Unmanned Underwater Vehicles.” https://gdmissionsystems.com/underwater-vehicles/bluefin-robotics.
2 Hydroid. https://www.hydroid.com.
space and time demands can be major advantages. Examples of systems that might be attractive for these reasons are those that are
- Small enough to be launched from a vessel of opportunity, rather than dedicated space on a larger cutter;
- Autonomous enough for “fire and forget,” which means the mission can be carried out without constant monitoring;
- Capable of long enough range so that launch and recovery can occur from the shore, without using ship time;
- Affordable enough to be launched on one-way missions, without the need to expend vessel and crew time for recovery at sea; and
- Smart enough to do onboard sensor processing and only call home—through robust and secure communications links—with snippets of information or windows of images.
Ensuring that a candidate system integrates well involves several other considerations. Notably, when the U.S. Department of Defense (DOD) considers acquiring off-the-shelf technology, it examines its reliability, availability, and maintainability (RAM) as indicators of the technology’s suitability to be integrated into operations.3 Reliability is the probability it will perform a required function under stated conditions for a specified period of time. Availability is the degree to which it can be expected to be in an operable state for use at the start of a mission when start time is random. Maintainability is the potential for the technology to be retained in, or restored to, a specified condition when maintenance is performed by personnel with specified skill levels. RAM integration problems are viewed as the failure of systems engineering.
Conformance with standards is another factor to assess a technology’s potential for integration. Although very specialized high-performance systems may require all-custom development, most off-the-shelf systems will adhere to at least some government or industry standards intended to facilitate interchangeability and interoperability across various dimensions such as
- User interface
- Means of physically mounting payloads
- Communications links
- Power supplies and batteries and recharging connections
- Computing modules
- Sensor interfaces
__________________
3 U.S. Department of Defense. 2005. “Guide for Achieving Reliability, Availability, and Maintainability.” http://www.acqnotes.com/Attachments/DoD%20Reliability%20Availability%20and%20Maintainability%20(RAM)%20Guide.pdf.
The Coast Guard has already recognized the benefits of some of these standards. For example, the off-the-shelf ScanEagle (a small UAS discussed later) has multiple standardized sensor configurations for surveillance, including video detection and ranging (ViDAR) cameras for daylight use and alternative thermal (infrared spectrum) cameras for night sensing.
In addition, there is a growing family of military specifications for system architectures that may have relevance for the Coast Guard. For example, the Army is establishing system architecture standards for its Robots and Autonomous Systems thrust.4 It has adopted Interoperability Profiles as a means to define a set of physical, electrical, and software interfaces for a specific ground robotic system. In its Unmanned Systems Integrated Roadmap 2017–2042, DOD cites interoperability first among the priorities for autonomous systems.5 DOD has defined an Unmanned Systems Control Segment architecture for operator control stations that the Navy has been using extensively and the Army is starting to use. This architecture has transitioned to an SAE standard. Many other examples of DOD standard setting can be cited, such as the Army’s plan to base all future autonomy software on standardized next generation Robot Operating System (ROS2) software libraries and tools.
CYBERSECURITY
UxS can present cybersecurity vulnerabilities from network-based and other perimeter attacks on information systems, as well as from attacks that directly affect the behavior of the vehicles and other physical assets. The source of the attacks—especially in the case of leveraged, off-the-shelf systems—can originate in the product supply chain, including individuals who create application software, as well as post-acquisition, during system life-cycle support. A system with cybersecurity vulnerabilities by definition lacks the qualities of RAM and sound systems engineering, but the Coast Guard must treat this possibility very seriously because of its many sensitive missions, such as in the domains of law enforcement and national security. When leveraging unmanned technologies developed by others, the Coast Guard must determine the criticality of ensuring cybersecurity in light of the intended application, the availability and cost of cybersecurity solutions, and the prospects of the solutions performing as required and not creating undesirable operational challenges.
__________________
4 U.S. Army. 2017. “The U.S. Army Robotic and Autonomous Systems Strategy.” https://www.tradoc.army.mil/Portals/14/Documents/RAS_Strategy.pdf.
5 U.S. Department of Defense. “Unmanned Systems Integrated Roadmap 2017–2042.” https://assets.documentcloud.org/documents/4801652/UAS-2018-Roadmap-1.pdf.
The Coast Guard must therefore weigh the advantages of leveraging UxS against the requirements to ensure their cybersecurity. Although considerable attention has been paid to protecting information systems from cyberattacks in recent years, the rapid advancements in physical systems, including unmanned vehicles, are presenting new cybersecurity challenges. DOD, in particular, has been focusing on achieving cyberattack resilient physical systems, including conducting risk analyses to prioritize potential resilience solutions. With a UxS, cyberattack resilience is the ability to detect when an attack is occurring and reconfiguring the system to permit continued operation, perhaps in a deteriorated but still acceptable mode. For example, a UAS might be equipped with multiple sensors—each procured through different supply chains—to validate navigation measurements in the event that one or more is attacked and provides corrupted measurements. The use of artificial intelligence approaches is also emerging as effective means for detecting, responding to, and continuing to operate under cyberattacks.
Although DOD, and the Navy in particular, can help identify potential cyberattack likelihoods and corresponding security solutions, the burden remains on the Coast Guard to assess the consequences of attacks and to identify operational issues related to employing potential solutions, including the need for operational doctrine and corresponding personnel training. DOD’s experience suggests that systems must undergo considerable testing to assure proper implementation and effectiveness of security solutions. There may also be a need for data collection capabilities to support post-attack assessments and decisions related to protecting the attacked system. Addressing these technical and operational concerns may require development of an organizational structure that integrates people with cybersecurity and operational capabilities.
Certain Coast Guard missions pose less risk of adverse consequences from cyberattack, and these missions may be candidates for earlier applications of UxSs. The information needs of the Coast Guard’s missions vary across a wide spectrum; some, as Search and Rescue (SAR), actively seek and use publicly available information and support, and others, such as Defense Readiness Operations, require the highest degree of cybersecurity. The type of mission is the main driver of the cyber requirement; hence, lower-risk missions allow for greater risk in the cyber domain without adversely impacting other Coast Guard, law enforcement, or national defense systems. Missions such as SAR, Marine Environmental Protection, Living Marine Resources, domestic Ice Operations, and Aids to Navigation and Marine Safety may derive great benefit from public interaction and collaboration through systems with a relatively lower degree of cybersecurity than other missions with a security or a defense nexus that would require a higher level of cybersecurity. The implementation of security solutions in these cases (e.g., SAR), while
important, could be less technically and operationally challenging, and could provide the Coast Guard with opportunities to build its cybersecurity knowledge and capabilities related to UxSs.
LEGAL AND POLICY CONSIDERATIONS
To fulfill its missions and ensure consistency with its regulatory and maritime law enforcement roles, the Coast Guard has extensive legal authorities that accord with its functions as a regulator, law enforcement agency, and military service. Therefore, the Coast Guard’s ability to use UxSs to execute one or more of its missions may depend on it having the applicable legal authority, jurisdiction, and basis in policy. For example, the Coast Guard must abide by relevant legal protections for safety, individual privacy, civil rights, and civil liberties. When it operates UxSs in international waters and airspace, the Coast Guard must comply with international law.
In addition to determining the lawful operation of UxSs, the Coast Guard must ensure their compliance with Federal Aviation Administration (FAA) regulations if intended for use in domestic air space. The Coast Guard also needs to ensure compliance with applicable data and privacy laws, specifically, as they relate to maritime law enforcement (e.g., search and seizure), privacy rights, and data collection. While in principle, UxSs should be allowed for all statutorily authorized Coast Guard missions that can be executed by manned assets, the legal regimes governing some unmanned operations are emerging and unsettled and therefore can present legal uncertainties.
Thus, as the Coast Guard explores candidate UxSs, it must carefully consider whether it can use them in a lawful manner under prevailing legal domestic and international frameworks (see Box 3-1). If a survey of applicable legal authorities leaves uncertainty or raises questions about its ability to operate certain UxS in compliance with laws, the Coast Guard may need to seek legal and policy determinations about their lawful use based on the type of operation, envisaged platform, and location of operations. In some cases, the Coast Guard may need to secure special authorizations or permissions from a cognizant authority, such as the FAA.
Finally, even if the Coast Guard confirms both its legal authority and jurisdiction to use UxSs, it will need to consult relevant policy guidance that govern technology procurements, at the federal and Coast Guard levels. Although a wide range of acquisition authorities may be applicable, newly emerging technologies can fall outside historical procurement processes and therefore may require innovative acquisition methods (see Box 3-2). To this end, the Coast Guard has started to explore new acquisition options—some of which emerged over the past year—and has, for example, assigned fulltime Cost Guard liaisons with the Defense Innovation Unit to accelerate the adoption of commercial technology.
This page intentionally left blank.














