3
Information and Communications
The technologies covered in this chapter include distributed collaboration, human-centered systems, intelligent systems, planning and decision aids, software engineering, communications and internetworking, and offensive and defensive information warfare. These technologies are listed in Figure 3.1 with some rough indication of interdependency.
Military Context
Many studies of future military needs and capabilities have made the following points, which are reiterated here because they informed the panel's deliberations as it considered information and communications technologies for the Navy and Marine Corps of the future:
- The size of the military will decrease—hence more will have to be accomplished with fewer people, platforms, weapons, and supporting systems.
- The nature of military missions will become increasingly more varied, with many crisis situations being of short duration and high intensity, and occurring simultaneously with other operations.
- The predominant mode of crisis intervention will be via joint task forces, often combined with international forces.
The above points require that distributed collaborating teams share a consistent view of the situations they face, allowing rapid decisions and coordinated action. The military leadership recognizes that information dominance is key to military success and that even the most advanced weapons cannot be leveraged
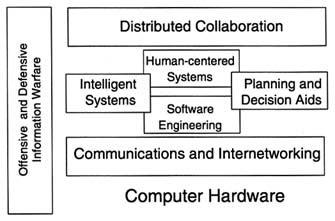
FIGURE 3.1 The key information technologies.
effectively without it. Given the naval forces' unique mission of force projection from the sea, they face unique challenges in the sphere of information dominance. Even these unique challenges, however, must be addressed within the context of interoperability with other Services and the forces of other nations.
Definition of Information Technologies
The technologies included under the heading of information are vast and strongly interrelated. Many information technologies feed other technologies and at the same time are dependent on the ones they feed. Because these interrelationships are so complex, it is difficult to organize the relevant technologies into some simple grouping with straightforward relationships to one another. Therefore, the following description should not be considered as a universal truth, but simply as one organizational perspective. Broadly speaking, information technology can be thought of as the underlying capability of computation and connectivity, and their interface with human operators, to apply reasoning power and distributed knowledge to various types of problem solving. Figure 3.2 illustrates the relationships of these elements. The first (inner)-level foundation is the computational hardware and the connectivity. The succeeding levels get at the raw physical capabilities of computation and communication through software. The third layer is that of intelligent systems combined with planning and decision aids and then the abilities of these systems to form effective partnerships with humans. These layers together provide cognitive support for distributed collaboration, which is in the outermost layer. The issues of offensive and defensive information warfare, illustrated in Figure 3.2 as bugs in the system, ultimately pervade the entire set of technologies as they work together to provide a knowledge-rich environment for the warfighter.
Distributed Collaboration
Description
Distributed collaboration refers to the use of human-computer interfaces, networks, and computer hardware and software technologies to mediate person-to-person interaction and communication. Three key goals of distributed collaboration are (1) the gathering of appropriate problem solvers together across time and space for rapid response in time-critical situations, (2) providing access to and ensuring availability of appropriate information resources across time and space within the context of a task, and (3) enhancing the effectiveness of collaborating problem solvers. In addition, there are two long-range goals for distributed collaboration. The first is to achieve a feeling of "as good as being there" through remote-presence technology. The second is to achieve a level of distributed collaboration efficiency that is "better than being there" through information augmentation. This second goal is important for improving collaboration efficiency even when the collaborators are co-located, particularly when the collaborative task takes place over time. It is expected that both of these goals will be met for normal commercial situations by 2035. The challenge for the Department of the Navy is to ensure that these goals can be met for situations unique to naval forces such as cooperative engagement.
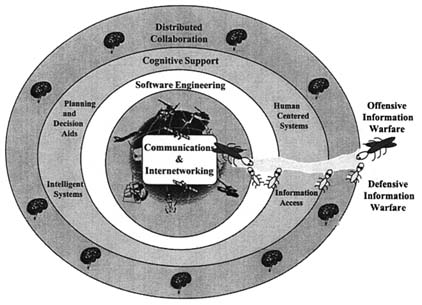
FIGURE 3.2 The layers of elements that make up information technologies.
Relevance
The information revolution has brought individuals the capability to access information through wireless and high-bandwidth wireline technologies with nearly ubiquitous coverage. Because of the large distances that often separate people and resources, the Department of the Navy especially stands to benefit from developments in this revolution through the effective use of people and information regardless of their location.
Technology Status and Trends
Today, naval communications are primarily accomplished via low-band-width voice and text. The operational use of distributed collaboration technology in its simplest forms, such as video teleconferencing, is uncommon. Higher-bandwidth communications via satellite will enable video teleconferencing among ships and shore assets. Commercial collaboration tools, such as "groupware" and shared whiteboards, will enable limited sharing of information in distributed groups. The commercial collaboration marketplace is rapidly evolving in four primary areas: groupware, such as Lotus Notes, newsgroups, and chat functions; two-dimensional and three-dimensional multiuser domains (MUDs), such as the Time Warner Palace and products from Worlds Inc.; teleconferencing tools, such as video teleconferencing and Internet teleconferencing; and World Wide Web-based tools, such as Netscape Navigator. Currently, these technology areas appear to be on somewhat divergent paths.
Future Impact of Technology Trends on Naval Operations
Higher-bandwidth interaction will enable widely distributed individuals to meet and understand time-critical information in a shared electronic environment that provides an adequate illusion of shared presence. Future command centers will exploit a range of technologies that are now under development in both commercial and military sectors, including speech recognition and synthesis, high-resolution projection displays (two- and three-dimensional), shared information visualization, resource and mission planning and simulation, and information finding and fusion. These technologies will be integrated in a cohesive system that provides the means for groups of individuals to understand complex situations. Together, shared presence and advanced information understanding will make distributed collaboration much more effective than any form of collaboration today. Most decision-making processes that involve multiple individuals will be affected.
Development Needs
Commercial collaboration will continue to target the mass market using low-end capabilities of computers and communications to address collaboration. Other key government-funded initiatives will be required to utilize high-end components and services and provide support for mobility between varying levels of capability. Basic technology advances needed include high-quality, low-cost, three-dimensional rendering; multimedia processing; speech recognition; speech synthesis, avatar (human representation) animation; three-dimensional MUDs; greater network bandwidth; global networks; symbolic compression; and improved network programming languages such as Java. Looking forward a few years, lower-cost, higher-resolution displays will make immersive interfaces more widespread, including personal (head-worn) displays and large-screen projection theaters.
The developmental challenges for the Department of the Navy lie in three areas. The first is rapid prototyping of collaborative support systems for naval-specific situations. An example would be sailors on multiple ships and marines on land collaborating over a crisis-resolution game plan. These prototyped systems would use primarily commercial components complemented with some capabilities coming out of the government laboratories. A second development challenge is the need to support collaboration with lower, rather than higher, bandwidth, which is contrary to commercial trends. The third challenge is the need to support research in those focus areas that, during the prototyping efforts, are found to have weaknesses. The emphasis should be placed on problems considered to be unique to the Department of the Navy. These would most likely include metaphors for collaboration that are different from the commercial trend of room-based metaphors.
Time Scale for Development and Insertion
Military use of distributed collaboration technology is currently under way and is benefiting greatly from rapid commercial growth. The key issues that must be addressed in the use of commercial technologies are difficult and will require significant R&D to overcome. These include information and battle-space visualization, personnel, network and information security, new methods of interaction, and global wireless coverage. Simple prototypes are being field-tested today and can become operational for the Department of the Navy within the next 5 years. Improvements in collaboration technology are dependent on improvements in many other technologies such as human-centered systems, communications and networks, displays, and communications.
Time Scale for System Insertion
Increased effectiveness through distributed collaboration will occur incrementally as the technology matures and advances in the commercial realm are incorporated into naval systems. Window-based video-teleconferencing tools will be incorporated as newer computing resources replace outdated equipment. Virtual presence and ''better than being there" capabilities should begin to appear within the next 10 years and continue to improve during the next 20 years. The challenge for the Department of the Navy is that the major benefits from successful insertion of collaboration technology will not be achieved without accompanying changes to naval processes. It has been demonstrated many times over the last several decades that simply automating or improving the current process with information technology provides only marginal improvements. Major gains are achieved only when new processes are developed to take advantage of the new technologies.
Foreign Technology Status and Trends
Significant resources are being allocated in Europe and Japan to develop tools and infrastructure to support distributed collaboration for commercial business. Telecommunications companies in Japan and Europe are conducting efforts in virtual teleconferencing. Large foreign investments are likely to continue and to grow in Web-based technologies that support collaboration.
Human-Centered Systems Technology
Description
Human-centered system (HCS) technology refers to the broad spectrum of hardware, software, and human factors disciplines that enable humans to effectively interact with information systems, computers, sensors, machines, and other humans. This technology draws from a variety of software fields (e.g., visualization, information presentation, human-computer interaction, computer graphics, human tracking, graphical user interfaces, distributed and object-oriented systems, speech understanding), hardware devices (e.g., visual, auditory, tactile, force displays, tracking sensors, graphics and general-purpose computers, networks), and human factors disciplines (e.g., experimental psychology, cognitive science, physiology). HCS technology involves multiple human modes of interaction and sensing. The goal is to enable information-processing technology to be of greatest benefit to humans. Achieving it requires completely natural means of interaction and the design of effective cognitive support.
Relevance
Any hardware or software system in the Department of the Navy that interfaces with humans will rely on HCS technology. The sophistication of modern technology has outpaced the capacity of humans to use it effectively. Information overload is a major problem that will only become more critical. For example, tactical combat information centers (CICs) are designed to provide operators with information from a bewildering range of sensors, including radar, surface radar, weapons radar, sonar, infrared-sensitive devices, and cameras, as well as the naval "infosphere" that includes maps, audio transmissions, and written information. Commanders and operators must rapidly integrate these data and make decisions based on real-time assessments of their situation. The time-critical, high-stress nature of the environment, in addition to the large volumes of information, can result in data overload and decreased efficiency and effectiveness. HCS technology aims to prevent human overload by enhancing human performance, complementing human strengths, and compensating for human weaknesses.
Technology Status and Trends
The Department of the Navy uses human interface technology in command-and-control systems, weapons system interfaces, mission planning aids, simulators, training, logistics, missile guidance, intelligence information access, as well as the traditional administrative functions.
The majority of human system interfaces in use today are based on the windows, icons, mouse, pointer (WIMP) interface or its derivatives, first developed in the late 1970s and early 1980s. The trends in human-centered systems are toward the use of multimodal interaction; visualization in three-dimensional, more immersive, virtual-reality systems; and intelligent assistants.
The Department of the Navy uses variants of the WIMP interface that typically include displays (sometimes color), function keys, and trackballs. Leading-edge efforts are under way to develop and evaluate multimodal interaction techniques and three-dimensional visualization for naval operations such as the Air Force Threat Evaluation and Weapon Assignment (TEWA).
Future Impact of Technology Trends on Department of the Navy Operations
Future system effectiveness will depend on human-centered systems approaches that enable humans to interact using systems in more natural ways with three-dimensional vision, hearing, speech, gestures, and touch. Improved situation assessment will result from full human involvement in the information environment, characterized by immersive virtual-reality techniques. Collaboration
will be facilitated via electronic means that enable individuals who are distributed around the world to interact and manipulate information jointly. Widespread information availability will require vast improvements in the interfaces for mobile and wearable computing systems.
Development Needs
The current ongoing revolution in computing and communications will drive dramatic improvements in machine and human interfaces, which will be required to realize the benefits of increased information and communications capabilities. These improvements will be enabled by technologies such as high-resolution miniature image sources for personal (head-mounted) displays and projection systems; wireless human tracking and monitoring technology; continuous, speaker-independent speech recognition; and low-cost, portable rendering hardware. Information presentation will be a key component of future systems and requires extensive research and development to identify modes and methods of visualization and multisensory presentation.
Much of this technology will be developed in the commercial realm because there are large consumer markets driving rapid development. On the other hand, the use of these enabling technologies in applications of interest to the Department of the Navy, such as command-and-control operator workstations, will require extensive adaptation and testing to be effective, much more so than in previous interfaces. This is a result of increased coupling and synergy between the human-computer system and the task at hand. The key to exploiting the advances in technology will be to take a human-centered systems approach to the creation of specific applications, exploiting the strengths of both the human operator and computer. We have only barely scratched the surface in the development of revolutionary new methods of interaction, and careful evaluations of iterative improvements of these systems are almost nonexistent. The Department of the Navy needs to take a rapid iterative approach to refining the development of human-centered systems. This would include human-factors design and rapid-interface prototyping based on immersive multimodal interaction, followed by evaluation and reprototyping in a number of potentially high payoff applications.
The commercial world will drive the development of enabling technologies such as displays and CPU performance. It is unlikely, however, that sufficient effort will be aimed either at the basic science underlying human interaction or at the specific application of new technologies to the Navy Department domain. The Department of the Navy should fund both types of efforts. In particular, the DOD has not focused sufficient resources on the use of immersive interaction technologies outside of the training domain.
Foreign Technology Status and Trends
Both Europe and Japan are investing in next-generation, human-centered system technology including visualization, virtual environments, and hardware. Significant application use of advanced HCS technology in foreign commercial markets such as entertainment and education is expected within the next 5 years.
Time Scale for Development and Insertion
Currently, evaluation of a large number of next-generation human-centered systems in a rich naval infosphere is not possible. Prototypes that span the spectrum of possible approaches should first be evaluated without resorting to operational situations on board ships. Virtual prototypes of human-centered systems provide a means for testing concepts and envisioning future possibilities (such as the Naval Research and Development [NRaD] Command Center of the Future); however, rich, interactive simulations of the naval infosphere that can support evaluation of revolutionary new approaches are not accessible.
Post-WIMP interface technology is beginning to be developed for Department of the Navy applications and should be available in fielded prototypes within 5 years. Much more research is needed to exploit the vast potential of human-centered systems.
Virtual environment (VE) technology is beginning to be developed for naval applications (other than training) and will accelerate within the next 5 years as more immersive displays and more stable tracking systems are developed commercially. Prototype three-dimensional visualization systems, the first step toward the use of VEs, have been tested in naval applications (e.g., Air Force TEWA) and should become more prevalent within 5 years. Evaluations that identify benefits of these technologies are needed.
More advanced interaction techniques such as direct brain interfaces are possible in the 20-year time frame but will require significantly greater understanding of brain function to be of general use.
Intelligent Systems
Description
In general, intelligent systems are considered to be those systems that do not follow a simple set of procedural instructions and do not provide a single predictable solution to a problem, but instead involve heuristics, sometimes have natural language understanding as an element, are predicated on some set of captured knowledge, and frequently have the ability to learn.
Relevance
Intelligent systems share the ability to be of greater assistance to people in a greater range of complex situations. Intelligent systems will also be used for machine control, but the emphasis here will be for people-in-the-loop systems. Many of the software systems of the future will be considered to be intelligent, and hence everything said for software engineering also applies.
Technology Status and Trends
Intelligent system components show up in a variety of places today. Some examples are pattern matching for automatic target recognition (minimal success here), image understanding for assistance to image analysis, scheduling and resource allocation, sensor fusion, and some expert systems in simulation and maintenance assistance. Some experimental command-and-control systems today use knowledge-based database access.
Future Impact of Technology Trends on Naval Operations
In the future there will be extensive use of better agents in a wide range of areas. Speech and gesture recognition will be used as a common human-system interface along with head-mounted virtual-reality displays. Machine translation will be used to provide real-time translation of military messages from one language to another. Unmanned underwater vehicles will become common, ATR will continually improve, and medical needs on board manned ships will be fully met with telemedicine and telesurgery. Intelligence will become a part of almost all software applications.
One of the limitations of intelligent systems has been the great difficulty of capturing better knowledge in order to have a base of common sense. Another limitation is the difficulty in establishing a hierarchy of knowledge. If knowledge has been captured for one application, it is difficult to take advantage of that knowledge for a new application. These difficulties are currently being addressed, and the expectation is that significant improvements will be forthcoming. Intelligent agents are software packages that are endowed with a certain amount of knowledge that makes it possible for them to carry out tasks autonomously and to respond to changes in their environment. There is an increase in the availability of systems that have embodied in them a knowledge base and can respond to a greater range of situations rather than simply incorporation an embedded sequence of instructions. Intelligent agents may have a role to play in military mission planning and rapid response to changing events. The complexity of the battlefield is such that ordinary software cannot provide much assistance to a commander in the course of rapid replanning.
Future systems will include intelligence systems support enabled by intelligent
agents or other forms of intelligent systems technology. All of them will require layers of intelligent systems, each of which will have embedded in it significant knowledge. Intelligent agents will be continually monitoring the battlefield situation and will be able to make predictions and take the appropriate action.
Impact of Trends on Naval Operations
The role of ships in land-strike missions will continue to grow in conjunction with the increased accuracy and potency of smart munitions. Precision-strike capability, increased battlefield awareness, smaller crews on ships and submarines, better collaboration with joint forces, and in general a higher level of preparedness will be enabled by the proliferation of intelligent systems.
Developments Needed
In order for the Department of the Navy to capitalize on the general advances in intelligent systems technology, the Navy must invest in application domain centers of excellence and begin to develop shared ontologies and common knowledge bases. Groups at these centers must insist on vendors using common knowledge representations so that they all can utilize the shared ontologies and ever-expanding sets of knowledge bases.
The development of intelligent systems technology will be driven by a combination of the commercial world and DOD. The Department of the Navy must collaborate with other elements of the DOD to help in developing the necessary standards or at least a useful level of interoperability across ontologies and knowledge representations. The Department of the Navy must then do the application domain work for itself; coupled with work in software architecture, this will allow the Navy Department to conduct intelligent acquisition, guiding vendors in exactly the direction it needs, with each acquisition complementing the others.
Time Scale for Development and Insertion
Ontology work for a selected small domain could begin now, with prototypes being ready in a year or two. In the near term, the use of agent-based programming and the Java programming language to implement agents is progressing rapidly. The Department of the Navy can begin to insert some of this technology now. It should be pointed out that the implementation of Java will give rise to significant security challenges that must be addressed.
In the mid term, over the next 10 years, advances in the area of knowledge capture will reduce the cost and time required for the Navy Department to develop and evolve expert systems. The hardest problem now is that of building hierarchical intelligent systems. Such capabilities as knowledge reuse, knowledge interoperability, and new ways of accomplishing reasoning over large
knowledge bases will probably not be ready for naval operational use for another 20 to 30 years.
Vendor systems using Navy-built ontologies and simple knowledge bases could be prototyped 1 to 2 years after the prototyping of the ontologies. These systems could be ready for advanced concept technology demonstration (ACTD) level use 2 years after that.
Planning and Decision Aids
Description
Planning and decision-aids technology is intended to support a wide variety of decision-support applications. These include logistics, resource allocation, inventory planning, mission planning, force structures selection, creation of the master target list for air campaigns, and so on. A significant amount of planning and decision-making will be done by distributed collaborating teams. This section does not address general distributed collaboration support technology but concentrates instead on lower-level algorithm support for decision-making. The types of technologies that can have a significant impact are generative planning, case-based reasoning, inferential reasoning, neural nets, genetic programming, information fusion, optimization, and scheduling.
In the past the military has focused on increased communication to support planning and decision-making. Today, there is an emphasis on the broader aspects of information access to support situation awareness. Even with accurate and timely situation awareness, however, plans and decisions must be made in the context of complex, rapidly changing situations, where frequently the best course of action is not obvious. The volume of details and options can be overwhelming and, even with the best information-accessing capabilities, commanders will be faced with incomplete or ambiguous information.
Relevance
A frequently cited goal of the military is to be inside the enemy's decision loop and to increase the tempo of war to a level at which the enemy cannot function effectively. To accomplish this requires high-quality rapid decision making and planning in the face of many uncertainties. This is true even in many non-warfare crisis-resolution missions, which require rapid reassessment of plans and decisions in the face of changing conditions. The key point is that there is significant value in being able to reduce the time it takes to plan and replan courses of action and to increase the quality of such plans so that they are definitely executable, require fewer resources, cost less, and endanger fewer people.
Technology Status and Trends
Over the last decade, significant research on planning has been carried out by both the operations research (OR) and artificial intelligence (AI) communities. The AI community is pursuing techniques that require the use of captured knowledge and many algorithmic and statistical approaches have been developed by both the OR and AI communities. At this point, however, practical success has occurred only in very focused areas such as resource allocation, task scheduling, some logistics planning, and pattern-matching with neural nets. The future will bring longer-range reflective planning and near-real-time reactive planning much closer together in a seamless way. To achieve faster replanning when an original course of action becomes inappropriate, lessons learned from real-time plan updating for robotic control will be combined with longer-range planning techniques within a single intelligent-agent-based system. These advances would not be possible if it were not for the interdisciplinary efforts that have begun recently in the areas of OR, AI, and real-time control.
The above advances will be complemented by advances in knowledge representation and reasoning, which in turn will improve generative planning and case-based reasoning. The hallmark of AI research has always been the effort to develop systems that can learn. In practice such systems have had little success. However, along with increases in computational power, memory size, and other software advances will come advances in machine learning and automatic system adaptation. These advances will provide significant advantages for systems that support fast mission planning and replanning. By 2010, we should begin to see practical success with human-in-the-loop automated planning in a number of areas that will directly contribute to increasing the tempo of warfare to a level at which the enemy cannot function effectively.
Current Impact of Technology Trends on Naval Operations
The Commander in Chief, Pacific (CINCPAC) has participated in several advanced technology demonstrations testing software to aid in distributed collaboration. These systems contained little analytical help for developing courses of action or decision-making, however. The Air Force has experimental systems that aid in some aspects of air campaign planning. Transportation Command (TRANSCOM) during Operation Desert Storm began using some advanced software from DARPA to plan logistics. The Atlantic command is now participating with DARPA in an ACTD that assesses force readiness.
Future Impact of Technology Trends on Naval Operations
A large number of possible future applications could benefit from technology to aid planning and decision-making. Some examples include general mission
planning, courses-of-action assessment, optimization and selection, logistics, medical care planning, and semiautomatic shipboard disaster response. Courses-of-action assessment includes target selection, force-application selection and coordination, resource allocation, results prediction, and so on. Many of these applications are aspects of dynamic mission planning and are discussed in Chapter 10, Technologies for Enterprise Processes.
Developments Needed
The Department of the Navy should work closely with DARPA and the other Services to ensure that the base technology is continually developed. Integrated feasibility demonstrations and advanced technology demonstrations then need to be sponsored that focus on the emerging planning technologies in ways that best benefit the Navy and Marine Corps. The underlying tools will often be developed commercially, but naval applications will likely be highly specialized and domain-specific. This leads to a need within the Department of the Navy to support the development of experimental planning applications.
Time Scale for Development and Insertion
The DARPA-sponsored research coupled to commercial efforts can be leveraged more effectively to meet naval force needs if the Department of the Navy establishes a testbed to facilitate the continuing identification of metrics and collection of data from the experimental use of decision-support technology. With such a testbed in place, it should be possible to increase the rate at which new operational capabilities are introduced into the fleet.
Software Engineering
Description
Software, the set of instructions that governs the execution of digital hardware, includes (1) embedded software for real-time systems with execution response times of milliseconds and with the software and hardware tightly bound together to drive some piece of equipment and (2) nonembedded real-time software, which typically governs the execution of standard COTS hardware such as microprocessors and larger processors. The following sections touch on both categories of software but focus on nonembedded software.
Software can usually be divided into layers. The lowest-level layer consists of compilers and operating systems and is usually referred to as system software. The layer above that is middleware—the layer of services that rides on top of the operating system and provides support for the applications that are in the top layer. Of the three layers, applications, middleware, and the systems, this discussion
focuses on the top two. The state of the art today is such that very seldom does any customer ever develop his or her own compilers or operating systems at the lowest layer.1
Software engineering encompasses the overall approach, strategy, processes, and tools for developing software. This section focuses on those related strategic issues and technology trends that the Department of the Navy must pay particular attention to if it is to ride the wave of technological developments to the best advantage.
Relevance
Nearly all of the electronics-based products in the Department of the Navy's current inventory have a significant portion of their functionality delivered by software. Even missile systems derive a great deal of their functionality from software. Perhaps even more important is software's great impact on missile evolution, which can be thought of as enhanced functionality over time. Software is dominant in almost every type of system the Department of the Navy uses, from administrative software for payroll, inventory control, and health care to the mission-critical software for command and control, surveillance, intelligence gathering, and processing of imagery. With so much functionality and cost contributed by software, it is vital that the naval forces take the best advantage of current technology trends. There is a great deal of discussion today within the Services about using COTS software, and there is no doubt that COTS technology will play an important role.
Technology Status and Trends Today
A number of exciting software technology trends are under way, including distributed systems (peer-to-peer and mobile agents), agent-based programming, services-oriented layering, loosely coupled systems, reusability, domain analysis, software generation, and high-confidence systems.
The productivity of digital designers has long been considered to be greater than that of software engineers. In both disciplines, the key to increases in productivity is reuse in one form or another. An important aspect of reuse is enabling engineers of one specialty to use components developed by engineers from another specialty. Historically, software developers have been particularly poor at this—typically, each developer has adopted a unique approach.
Lack of software reuse has held true both for large defense contractors and for commercial software development companies. This is an area in which the
hardware world has been ahead of the software world. Achieving greater reuse of software will be critical for the Department of the Navy. Some positive examples of current software reuse are evident. Today, nobody would write his or her own word processing program or develop his or her own database management system. Spreadsheet software is another wonderful example of a common problem-solving paradigm encapsulated in common reusable software. Today only a handful of commercially available spreadsheets systems prevail. The goal, then, is to extend these examples and develop reusable software modules for command and control, mission planning, and the like. The goal in systems development should be to enable reuse of many types, not just code for major components.
Several different trends are discussed below as if they were separate, but in truth they are tightly interrelated.
Distributed Software
Over the years client-server software has become extremely common. It is in use in many areas of the Department of the Navy and will continue to be so in the future. An emerging trend, however, is the move from client-server to peer-to-peer software where the same piece of software might function as a server in one scenario and as a client in another scenario. The key to distributed software technology is that pieces of software that render certain functionality can collaborate to deliver even higher levels of functionality. These software peers can also be referred to as objects or perhaps even agents. In the past, object-oriented software tended to be objects within the context of tightly integrated systems. Those objects are now trending to behave more like automata and are often referred to as agents. Such agents can be distributed in a network with a peer-to-peer type of arrangement across a distributed network.
Agent-based Programming
Agent-based software is an advance over object-oriented software. An agent is considered to be a self-contained object that understands its environment and can react to and interact with it, as opposed to only responding to messages that are passed to the agent itself. Although some consider that agents will be capable of solving all imaginable problems, agent-based software will be no more of a panacea than object-oriented software was. It takes a step further the notion of having software as separate and somewhat independent entities that can carry out higher-level tasks on behalf of their requester. Many agents will require embedded knowledge and will also be endowed with the ability to learn. A key attribute of agents is mobility; that is, both the state and behavior of the agent can traverse a network and execute on remote nodes. This feature helps address system-load balancing, communication bottlenecks, and constraints on access. However, some approaches to agent-based software limit the functionality available to the
mobile agents in order to solve security issues, e.g., to inhibit software viruses that may be disguised as agents. Agent authentication and authorization mechanisms will be needed and are being developed.
Services-oriented Layering
The concept of software architecture in layers has not always mapped directly onto the realized architectures. Today, however, the notion of layers is increasingly more representative of the actual structure of software packages. A module that is considered an application today might be a server tomorrow, and hence other software could use it in the process of running an application. This paradigm exerts a major influence on the manner in which software is written. For the first time, developers are thinking about how the software they are developing might be utilized by others in ways that may be different from what was originally intended. In other words, software development is moving toward the production of software that is inherently more flexible. The DOD is designing this software layering into the next generation of command-and-control systems.
Loosely Coupled Systems
Historically, a good architecture was represented as a system that would be tightly integrated. The more tightly integrated, the higher the performance. The problem is that the more tightly integrated the system, the harder it is to make any changes. It is almost impossible to extract a module from a tightly integrated system and replace it with a newer one. The trend today is toward much looser coupling. Objects, agents, and peer-to-peer protocols are all examples of software partitions or segments that are loosely coupled to those that call them or to the ones that they in turn call. This trend has been enabled by the availability of faster hardware. Looser coupling is achieved through message passing that is typically much slower than other means of module communication. Thus, performance is dependent on improving hardware performance capability, particularly processor and bus speeds.
Reusability
The exciting aspect of all of the above technology trends is that, for the first time, it may be more feasible to reuse existing modules for new applications, rather than to develop new ones. Achieving full reusability requires that attention be paid to software architecture and standards.
Domain Analysis
Another trend that builds on all of those noted above is domain-analysis and domain-oriented software development, which involves planning for reuse at the
macro level as opposed to worrying about micro-reuse—the reuse of small software functions such as linklist manipulation. Experimentation with domain analysis and domain-level reuse in the military context started with the System Threat Assessment Report (STAR) program in DARPA.2 Many commercial companies or defense contractors that do business in a given domain have already recognized the value of this method and are practicing it extensively. Unless software is developed at the domain level, many of the technological advances available in the near future will not be able to be realized by the Department of the Navy. Within the STAR program, it was determined that nearly 80 percent of the command-and-control software in Cheyenne Mountain consisted of more than 20 systems that could be reused. Significant reuse is also feasible for various families of ships where the software is very common and when great savings can be achieved if a domain approach is taken.
Software Generators
Another trend is the development of software generators for common functions that occur frequently within a given domain and are identified as being worth the additional engineering effort to create the ability to automatically generate the software for those particular functions. In the area of scheduling, for example, software has been generated in a fraction of the time needed to generate it by hand, and it has produced schedules that were 10 times faster than those of the software that was manually constructed. Domain analysis is required to identify functions that may warrant automatic software generation.
Generators can also be thought of as very high level domain-specific languages that are produced by analyzing domains, determining exactly what kinds of processes and functions occur frequently, and embedding that knowledge into the software system, thus enabling the application developer to specify the desired functionality at an extremely high level. This is but another example of reusable software. Reuse can be achieved either by inserting a complete module as it stands or by using generators or high-level languages.
High-confidence Software
One last important technology trend is the development of trusted, or high-confidence, software. One problem for the military is the need to test and certify weapons systems control software. Historically, some minor success has been achieved in the area of formal proofs. It is now possible, however, to analyze mission-critical software and determine which aspects must be verified. The
Services should take maximum advantage of the most recent developments in this area to reduce the cost of recertifying weapon systems control software after even small changes are made. It is expected that formal proofs will be adequately advanced in the next 20 years to allow for automatic recertification of reasonably sized critical segments of fire-control software.
Future Impact of Technology Trends on Naval Operations
Software engineering is expected to become more component based with the ability to dynamically configure systems for the task at hand. Future systems will likely be more distributed and agent-based and will have more flexible coupling between modules. Architectures and high-level languages for generating components will likely be based on domain analysis. Progress has been made in the last 20 years, but it will occur more rapidly in the future. How well the Department of the Navy deals with resolving software issues will have a significant impact on its competitiveness and on its ability to leverage limited resources.
Development and Adoption Needed
A number of developments are taking place today that, if successfully deployed, will have the potential of decreasing the cost of software acquisition. Two examples are the maturing of object-based and client-server products, and the evolution to agent-based, Web-based, and peer-to-peer software. New advances will be made in dynamically reconfigurable systems—systems in which modules advertise their capabilities and systems that have task-driven controls and that can find and link together modules with advertised capabilities.
Life-cycle software costs will be greatly affected by an organization's ability to take advantage of the above capabilities and to utilize the same components across an entire domain instead of developing stovepipe systems. The Department of the Navy should begin to develop centers of excellence for key application domains and key software technologies. An application center should perform domain analysis and develop domain-based architectural strategies that are updated as the domain needs change and new technologies become available. Such a center of excellence would obtain expertise in the use of the state-of-the-art tools for domain analysis and the capture of formal representations of requirements, types of modules that would be needed and their potential interplay, and reference architectures that facilitate plug and play of the various kinds of modules, whether they are commercial or not.
The centers would understand the acquisition of knowledge about the domain, which in turn could potentially be used for software generators and higher-level, domain-specific languages. An important aspect of such centers would be the creation of testbeds that would facilitate rapid experimentation. Contractors
or vendors for the Navy Department could use the testbeds to determine the best architectures and components for naval systems.
There is a need for highly reliable, trusted, and certifiable systems. This is a major bottleneck in the recertification of weapons control software. Aggressive use of formal proof techniques should be pursued. Europe is far ahead of the United States in this area. Capabilities exist today for being able to certify small systems from the hardware up through the operating system to the application for at least portions of the system. It is not necessary to certify all aspects of a system but perhaps only the critical features. This is an area where the Department of the Navy should aggressively work with DARPA and the other Services to reach critical investment levels. Such critical funding does not exist today.
The commercial world will be the key driver in all areas except certification of weapon systems software. DARPA will be a player, but its investments will have a greater impact on systems survivability and the concept of taskable agents.
Time Scale for Development and Insertion
The technologies discussed above can be incrementally developed and continually prototyped. The key issue for the Department of the Navy is to adopt domain analysis, particularly when it must be done jointly with other Services. The benefits of domain analysis have been demonstrated by the DARPA STAR program. The real benefit of the emerging technologies will not be realized unless the Navy commits to establishing teams that (1) control the acquisition of software across a domain and (2) perform the prerequisite domain-based engineering. After domain analysis begins, beneficial results could be realized for any application domain in 2 to 3 years.
Foreign Technology Status and Trends
As indicated above, the one area where European technology, in particular, is ahead of the United States is that of formal proofs and high-assurance software. The United States could probably gain from a greater collaboration with European research centers in this arena.
Communications and Internetworking
Description
The defining requirement of naval communications is ship-to-shore and extended-range (beyond line of sight) ship-to-ship communications. The extended ranges and extended durations of ship deployments create unique challenges and complexities. These must be met, in general by satellite communications (SatCom) resources, in an environment of constrained budgets and dynamic (usually increasing)
requirements. For example, satellite video teleconferencing has grown in popularity, and some would see a requirement on almost every ship for off-board diagnostics and repair assistance. This is consistent with commercial experience, where videoconferencing has grown exponentially in recent years. It has been reported that nearly 80 percent of all switched 56-kbps and switched 64-kbps data calls in 1992 were for videoconferencing.
Other requirements for additional communications capacity result from the increasing tactical availability of overhead and other sensors that are not organic to the battle force. This trend is certain to continue. Supplying a dedicated channel to each communications task is increasingly untenable.
Prior to the launch of the maritime satellite (Marisat) (Gapfiller) 20 years ago, ship-to-shore communications consisted of a few 75-bps semireliable high-frequency (HF) radio circuits and sometimes-available HF voice. At this time, ultrahigh-frequency (UHF) satellites (Gapfiller, fleet satellite communications, and successors) have become the backbone of naval ship-to-shore communications. The fleetwide increase in total communications capacity has been revolutionary. Yet the standard 2400-bps circuits now seem constraining, especially in a time when commercial users commonly employ link rates 10 to 12 times higher still for data and facsimile. More than 200 ships have been equipped with INMARSAT (follow-on to commercial Marisat) terminals, making ship-to-shore telephony readily available. This service has become nearly indispensable to the Department of the Navy.
With the new capabilities afforded by UHF SatCom and INMARSAT, general-purpose communications (voice, data, and fax) use by fleet units will begin to resemble that of modern commercial users. With INMARSAT, for example, the shore termination is to the public switched telephone networks. Use of commercial equipment and standards as well as networks is a natural development. Costs of service and effectiveness to be gained are the driving factors governing usage.
Each of these mainstays, however, suffers critical vulnerabilities in conflict situations. For example, any current UHF SatCom transponder can be seriously degraded by as little as a determined hobbyist anywhere in the Earth-coverage footprint using an inexpensive scanner, a surplus military UHF transceiver, and a homebuilt antenna. HF radio offered at least a measure of jam resistance, despite its various shortcomings, by the multiple operating frequencies and geographically varying propagation conditions.
Use of INMARSAT is burdened by treaty provisions limiting the Intelsat Consortium services to peaceful purposes. Substantial discussion with treaty signatories has not resolved the issue. U.S. Commander in Chief, Pacific (CINCPAC) policy issued in 1993 is that Department of the Navy use of INMARSAT in a conflict situation for more than safety and rescue purposes is permitted if the action being taken is pursuant to a United Nations Security Council resolution. But what about situations where U.S. action is taken unilaterally? The risk was illustrated
recently when the terminal of a West Coast-based ship was deactivated by INMARSAT (fortunately on the way home) because of a billing dispute. Both of these examples point to vulnerabilities that need some resolution.
A Vision for Future Naval Ship-to-Shore Communications
A vision for the future of naval ship-to-shore communications must seek to reconcile powerful opposing influences. New capabilities (data, fax, imagery, video) with vast increases in communication channel rates must be added to traditional requirements for content security, jam resistance, and protection from service disruption. Moreover, increased emphasis on nontraditional operations suggests a need for interconnection with the global public switched telephone network complex. At the same time, the outlook is for continued budget pressures, reduced ship manning, and reduced margins for error.
The possibility seems remote that every ship can be equipped for the most demanding requirements (e.g., high-quality imagery and full-motion video), and a natural delineation might be those ships with and without embarked commands. In this environment, a reasonable vision might consider the following principles:
- Seamless normal and conflict communications. Operational effectiveness as well as personnel efficiency would be well served by a smooth continuum of communications resources and practices between normal and conflict operations. This suggests that issues of potential service degradation or interruption be considered beforehand and suitable resolutions determined in advance. This principle would imply that every ship would possess some ship-to-shore capability with at least moderate jam resistance, and ships with embarked commands would possess substantially more. In general, some reduction in total channel capacity would result from the tradeoff between communications rate and vulnerability level.
- Seamless underway and pierside communications. Personnel efficiency can be improved by smooth transitions of both data and voice communications when ships arrive or depart pierside. This implies operating procedures and physical interfaces on board and on the pier for shifting from satellite to wireline interconnect to the public switched telephone network and to data networks. Already under way in some areas, these measures are considered useful for fleetwide implementation.
- Parity of general-purpose (voice, data, fax) capability with similar-sized modern commercial units. Aside from unique communications requirements of a battle force, efficient conduct of operations is leading to a convergence in the use of general-purpose communications. This trend is assumed to continue and implies continued or expanded interconnection to public switched telephone networks and available channel rates in the near mid term (3 to 5 years) of at least 64 kbps for data, facsimile, and moderate-quality video conferencing on all ships.
- Both naval and commercial requirements for these applications can be expected to continue growing. For example, trends toward graphically oriented, versus text-oriented, communications might require channel capacities of 1.5 Mbps on every ship during the forecast period ending in 2035.
-
Maximized/optimized military SatCom capacity. Current requirements and trends suggest that planning should envision ship-to-shore channel and total capacity increases of 30 to 100 times the current capability, similar to the capacity increases resulting from the transition to satellite communications in the 1970s. This would be reflected in ship-to-shore channel capacities of 64 kbps, increasing to perhaps 224 kbps during the next 6 to 10 years.
Some of these needs will undoubtedly continue to be fulfilled by INMARSAT or other commercial offerings. However, military satellite resources at UHF, super-high frequency (SHF), and extremely high frequency (EHF) offer vital and unique advantages, including dedicated spectrum, DOD system control, and jam resistance (in some instances). For these reasons, military SatCom is expected to continue its role as the backbone of ship-to-shore communications. It follows that these systems should be optimized for capacity increases and operational improvements. - Virtual access to off-board databases. Modern commercial practices today employ a wide array of means for remote access to databases and electronic data interchange for parts and supplies management. The Department of the Navy uses some of these innovations, and it is envisioned that considerable potential remains to exploit this developing application area.
Relevance
Nontraditional missions, budget pressures, reduced manning, compressed decision time lines, and reduced margins for error combine to produce extraordinary pressures for communications improvements. Technology advances, whether in the military or commercial sectors, offer valuable potential. Because satellites figure heavily in naval ship-to-shore communications, innovations in that transmission means are particularly relevant. Also, applications developments that improve efficiency or offer new capabilities to remote units are similarly relevant. Examples include the terminal equipment and data compression algorithms employed in video conferencing.
Technology Status and Trends
Technology in communications may be described as falling into four principal areas: transmission, networks, applications development, and termination/application equipment. The areas overlap, as might be expected, and each is experiencing rapid and continuing development. In general, communications technology today is driven primarily by the commercial sector.
Communication transmission has progressed from its wireline analog beginnings such that it is useful to distinguish network trunk transmission from subscriber access loop from intrafacility wiring. In developed countries, trunking is now all digital and conveyed via optical fiber or digital microwave. Satellite trunking is increasingly limited to access to developing countries and remote cities. Subscriber access continues mostly on wireline, but with trends toward a digital format and a wireless medium. Intrafacility wiring means now include coaxial cable and optical fiber as well as copper wire.
Networks are now electronically switched and have progressed from circuit-switched hierarchical configurations for telephony and data to packet-oriented data networks and new signaling control mechanisms for telephone and other stream applications. Communications applications and related termination equipment now form a virtual continuum, expanding from traditional messaging and telephony to data, facsimile, imagery, and live video. With these applications have come continuing fundamental changes in how business (and military operations) are conducted.
Rapid advances in communications technology are currently paced by commercial interests, and in many areas commercial technology is more advanced than that used in the military arena. For example, ordinary cellular phones can access public switched telephone networks and, by extension, such public networks worldwide. Progress in encoding methods for data compression continues, and asymmetrical approaches are being made in many applications, wherein brief queries to databases, for example, elicit voluminous responses of graphic or other data.
Some developing areas considered to have key implications for naval communications include the following:
- SatCom PCS. Several proposed SatCom personal communications systems (PCS) promise global service for handheld telephones. One of them, called INMARSAT-P, is a private-venture spinoff of INMARSAT and may constitute a solution to the current vulnerability of INMARSAT for Navy use. Others are proposed by larger U.S. firms and aim for initial service availability in the late 1990s. Planning has also begun on at least one satellite system for more advanced needs that is capable of worldwide voice, video, and high-speed data links.
- ISDN-related equipment. The long-envisioned integrated services digital network (ISDN) has spurred development of high-quality facsimile equipment and moderate-quality videoconferencing equipment operating at the ISDN basic rate (64 kbps) for medical and other imagery needs. Expanding applications are following. Nearly 80 percent of all switched 56-kbps and switched 65-kbps data calls in 1992 were for video conferencing.
- Asymmetric channels. Much of modern communications is highly asymmetric in character, highlighted by uses of the Internet, where brief requests for
- information commonly result in downloads of voluminous graphical data. Some alternatives being examined employ a relatively lower-rate channel for executing the request and a high-rate, one-way channel (cable modem or direct broadcast satellite) for transmitting the response. For example, a recently announced service employs a regular phone line in one direction to elicit large volumes of data for rapid delivery by satellite.
- Intranet/multilevel access. Intranets employ the infrastructure and standards of the Internet and World Wide Web but are cordoned off from the public Internet through software programs known as firewalls. Access is granted to designated corporate interest groups such as customers or employees. Intranets (as well as the Internet) have grown geometrically. Established by many of the largest firms in corporate America, uses range from furnishing order or shipment status data to customers to supply ordering via an electronic catalog to disseminating employee information. Key to continued success is reliable access control, and development in this area is ongoing.
Future Impact of Technology on Naval Operations
In many respects, advanced communications constitutes an enabling capability for nontraditional littoral missions where ships may frequently be called upon to operate independently. Experiences of the past decade highlight risks to the ship, political risks of errors in targeting and other decisions, and the much compressed time line of engagements. Real-time operating orders and mission coordination are critical requirements, especially in stress periods when jamming may be present and commercial networks congested. Communications technology trends should have a favorable impact on Navy objectives of increased efficiency and reduced manning through more effective coordination of replenishment, repair, and personnel matters. In radio hardware technology, future progress in phased array and multifunction antennas could help to reduce superstructure congestion on surface ships.
Development Needed
Following is a list of developments and actions considered by the panel to hold unusual promise:
- Commercial SatCom Alternatives. Several low-Earth-orbiting (LEO) SatCom systems in development promise near-global service for mobile or hand-held telephones. These systems are driven by commercial interests, but an early Navy investigation of the alternatives is recommended, with the objective of equipping every ship with a minimum general-purpose (i.e., not necessarily jam resistant) communications capability consisting of global telephone access and 64-kbps data/fax capability.
- Since required communications capabilities seem certain to continue increasing, and since satellites will continue to be the principal means for ship-to-shore communications, a new look at how the SatCom capability is provided will likely be required. This would include examining the mid- to long-term potential roles of LEO systems in providing general-purpose ship-to-shore communications now provided by INMARSAT and military geosynchronous satellites. Such an examination should also include whether such candidate systems should employ military frequency allocations.
-
UHF satellite system improvements. Military SatCom is expected to continue its role as the principal resource in ship-to-shore communications during much of the present forecast period. In particular, the UHF follow-on satellites offer expansion potential. Current UHF transponders could support at least 10 times the current 2.4-kbps bit rates, and design changes in later flights could readily support 64 kbps or more. Exploiting the asymmetry in some needs and EHF/UHF cross-banding should provide additional improvements. Developments here will naturally be driven only by Department of the Navy initiative.
Reduction of vulnerability of critical links is another area in need of development. Vulnerability of the UHF SatCom uplinks to jamming or interference was recognized at the outset and the risks considered acceptable. In the fleet communications satellite and successor UHF satellites, only the fleet broadcast is cross-banded with an on-board processor to assure a jam-resistant capability. Experience has demonstrated the utility of this configuration. The general awareness of electronic technology worldwide, however, strongly suggests that some mitigation of this shortcoming should now be given some priority. A second SHF-to-UHF cross-banded broadcast channel, but with higher capacity than the present fleet broadcast channel, might be part of a solution in the shore-to-ship direction. In the meantime, signal processing and much reduced channel rates could provide a modest degree of protection in the ship-to-shore direction, where uplink power is limited. Low-rate EHF channels might play a wider role in ship-to-shore communications, especially if employed in an asymmetric channel allocation regime, e.g., an EHF request channel for SHF-UHF broadcast response. - Exploiting asymmetry in channel requirements. Pressures for even more capacity in ship-to-shore SatCom channels motivate an examination of the limiting factors. Two prominent limitations are available bandwidths in satellite transponders and, in some cases, uplink transmit power in the ship-to-shore direction. Focusing on possible improvements suggests considering asymmetry. Leaving aside the transmission of any on-board sensor system outputs, the normal flow in ship-to-shore communications involves a much larger volume of data bound for the ship than originated by it. Yet ship-to-shore links are commonly full-duplex, whether UHF or SHF, with equal capacity in both directions. Technology will support exploiting these asymmetries to achieve greater efficiency as well as robustness. Although different approaches to asymmetric applications
- are under way, largely driven by commercial interests, pursuit of specific naval applications will depend on the Department of the Navy development effort.
- Off-board databases. Several developing technology areas could assist in reduction of the weight and volume of hard copy records carried on board and potentially increase the efficiency of maintaining them. Some exploratory efforts are understood to be in progress, but the total scope could range from personnel and medical records to stores and parts and maintenance manuals. Approaches could range from virtual access to remote databases to electronically stored records on board backed up by master records at, say, the ship's home port. The technologies of databases and intranets for controlling dissemination and access to corporate data are well developed and continuing to advance.
Foreign Technology Status and Trends
Communications technology is very much a global development effort and capability is largely equal among the developed countries. Ironically, the status of commercial communications in some developing countries is more advanced because of the absence of previously installed infrastructure. In general, wireless telephony, which includes soon-to-be ubiquitous SatCom-based telephony as well as cellular technology, is expected to be adopted by the world's military forces as well, for reasons of economy and convenience. This should, in turn, offer more readily available means for joint mission coordination using commercial services.
On the threat side, the generally increased worldwide awareness of communications technology may represent an increased risk of jamming of vulnerable resources.
Time Scale for Development and Insertion
Time periods required for development and adoption for widespread fleet use vary widely among the recommended developments. In the following estimates, normal priorities and budgeting procedures are assumed. Evaluation and selection of a commercial SatCom service to augment or replace INMARSAT are expected to be required 1 year after the candidate systems are in service. After selection, budgeting, procuring, and deploying significant numbers of units throughout the fleet are expected to take about 3 years.
Different time scales are anticipated for UHF SatCom system improvements that are ground-segment oriented and those involving space-segment modifications. Studies and test programs for channel capacity increases and vulnerability reduction should be able to reach useful conclusions in 1 to 2 years. Adoption on, say, two satellites and a significant number of ships might require another 3 years.
Changes in UHF satellite designs for wider-bandwidth transponders or cross-banding
options may require more development time. A preliminary estimate would be 3 years for studies and engineering tests, followed by 3 years to incorporate the design changes into a spacecraft. To get the new designs in orbit in two satellites in a routine spacecraft replenishment schedule would likely require an additional 2 to 4 years, with another 2 to 4 years for fleetwide coverage.
Exploiting channel asymmetries and remote use of off board resources might be most effectively accomplished by adapting commercial sector developments in these areas. A concerted program to identify, adapt, and test candidates might require 1 to 2 years to develop fleet-ready applications, and another 2 to 3 years for deployment.
Changing future requirements and continuing rapid advances in communications technology can be expected to influence future technology development needs, especially toward the end of the forecast period of 2035. For example, trends toward graphically oriented versus text-oriented communications can be expected to require ever-greater overall channel capacities. Satellites will continue to serve as the principal means of communication because of the fundamental geometries of ship-to-shore communications.
However, budgets will surely continue to be constrained, and ships will continue to have limitations on power and topside space. A new look at how SatCom capability is provided will likely be required. It is useful to observe that commercial communications suppliers are shifting to LEO systems to provide voice, fax, and data capabilities (these now have limited channel rates, but higher-rate capability is planned). Numerous issues pertain, but some in the SatCom field believe that the era of large, expensive, geostationary satellites may be ending for such applications.
Navy Department examination of the issues and tests using commercial LEO-based services when they are available could require most of the next decade. If the conclusion favors a LEO system over the current geostationary UHF follow-on system, a dedicated system employing military frequency allocations would likely be desirable. Designing, procuring, and deploying such a system would likely require most of another decade, ending in the 2015 to 2020 time frame.
Summary and Recommendations
Naval communications, like commercial communications, has progressed in recent years from basic voice and messaging to additional functionality, such as facsimile, other than imagery and video conferencing, which requires higher channel rates. This added capability has supported new efficiencies and in some cases has enabled new ways of doing business that have transformed whole business segments. Similar benefits have been experienced by the Department of the Navy, and communications is expected to have a pivotal role in accomplishing
new nontraditional missions with reduced manning and within continued budget constraints.
The trend in requirements toward increased channel rates is expected to continue into the foreseeable future. As a result, an increase in total capacity will be required in the next two decades or so comparable to that achieved by the shift from HF radio to SatCom in the past two decades. At the same time, it will be necessary to mitigate vulnerability to service disruption.
The following are recommendations for utilizing and expanding available communications technology:
- Pursue the objective of equipping every ship with some measure of ship-to-shore jam-resistant communications and a general-purpose (not necessarily jam resistant) channel rate capability of at least 64 kbps in the near- to mid-term and perhaps 224 kbps during the next 6 to 10 years.
- Investigate and test newly developing SatCom alternatives for obtaining global access to public switched telephone networks to augment DOD SatCom facilities for general-purpose voice, data, and fax needs.
- Undertake a multiphase improvement program for UHF SatCom systems to increase channel capacities and reduce vulnerability.
- Examine what combination of SatCom capability (LEO versus geosynchronous and military versus commercial) is most appropriate for general-purpose ship-to-shore communications.
- Undertake a development and test program to exploit the asymmetry in certain applications to achieve greater communications efficiencies.
- Expand programs for virtual access to remote databases and automated electronic data interchanges.
Offensive and Defensive Information Warfare
Background
This section discusses emerging technologies and issues related to information warfare (IW) and electronic warfare (EW). The key results regarding offensive and defensive IW and EW of importance to the future naval forces are as follows:
- The proliferation of more sophisticated digital microelectronics into Navy and Marine Corps information and communications systems will make these systems more capable but will also make them more vulnerable to external disruption efforts.
- Actions to make information systems more interoperable by making better use of commercial hardware and software initiated by the promulgation of a DOD-wide, common, joint technical architecture for command, control, and communications
- (C3) systems will introduce many new vulnerabilities and present new attractive targets for enemy disruption.
- Forcing all military command-and-control systems to have a high degree of architectural commonality and incorporating commercial software and hardware into trusted military command-and-control systems will introduce additional vulnerabilities that can be exploited by the enemy.
- Emerging transmitter technologies capable of generating extremely high peak power ultrawide-band radio-frequency impulse signals pose a significant threat of disruption of microelectronic digital systems.
Background
Over the past few years, primarily since the Gulf War, many articles and books have been published regarding the nature of IW and its possible implications for the reliability and integrity of both civilian and military information systems.
Following the issuance of DOD guidance on information warfare by the Office of the Secretary of Defense (OSD), the military departments and the civilian telecommunications industry have tasked their various advisory or management oversight activities to carry out in-depth studies about the future implications of IW on their operations. For example, in 1994, the Defense Science Board (DSB) examined the manner in which IW is utilized as well as possible defensive IW actions and has made a number of recommendations3 to the OSD regarding future management, organizational, and technology issues associated with IW.
Since the issuance of the OSD IW policy, the Department of the Navy asked the Naval Studies Board (NSB) of the National Research Council (NRC) and in a separate action the Navy Research Advisory Council (NRAC) to examine the nature of IW and recommend approaches that would optimally exploit IW for naval force purposes. The NSB IW study4 was of quite broad scope, whereas the NRAC study5 focused primarily on defensive IW concerns. Both studies made a number of important observations and recommendations regarding strengthening the Navy's ability to carry out both defensive and offensive IW activities. In large part, the recommendations from both studies are still valid and constitute an appropriate background for consideration by the Panel on Technology.
In part stimulated by the results of the studies noted above, President Clinton recently chartered a new Commission on Critical Infrastructure Protection6 that will attempt to bring military and civilian knowledge about IW issues together to ensure that the critical national infrastructure—telecommunications, transportation, power, medical services, and so forth—receives appropriate attention with respect to protection from both physical and IW threats. Because of the Navy and Marine Corps' operational dependence on the nation's infrastructure, the Department of the Navy should participate in this activity and assist in the development of appropriate protection measures.
Clearly the viability of information systems in use today, in both the civilian and military activities, is of considerable concern in light of IW threats—particularly as they are exploited by other nations that might be potential adversaries of the United States.
Categories of Computer and Information System Disruption
To establish the context for introducing the emerging disruption technology associated with very high peak power UWB RF impulse technologies, the scope of the variety of major computer and information system disruptions is described below.
Software Attacks
System disruptions of information networks and their supporting computers may be caused by use of external computer terminals—such as those used by hackers. The media have given particular attention to these kinds of disruptions because of the perceived and often colorful role of the hacker in carrying them out.
System disruptions may occur as a result of improper software code, either inserted in the system as it was developed or inserted into the system after it became operational, perhaps by a hacker. The improper code may be the result of software errors of commission and omission or the result of tampering. Software is particularly vulnerable to tampering during the development process because many people may have access to the low-level code during development. Security and integrity of the software development process were serious issues in the Strategic Defense Initiative.
Some system software threats associated with IW are categorized below:
- Computer virus. Probably the best known of these threats, although not usually considered in that context, computer viruses are those programs that stealthily infect other programs and then replicate and spread within a computer
- system or network. Typically small, they are difficult to detect; some of the more recent versions have active antidetection protection measures. Modern computer viruses may be encrypted, compressed, or polymorphic to reduce the probability of detection.
- Covert channel. A communications channel that allows information to be transferred in a way that the owners of the system did not intend. Variations include cover storage channels and cover timing channels. Use of a covert channel could be a way to insert a virus into a computer system.
- Data manipulation. With the increasing technological capability for manipulation of data come opportunities to use those capabilities for nefarious purposes. The composition and content of pictures as well as databases are vulnerable to advanced techniques of manipulation.
- Flaw. A flaw is defined as an error of commission, omission, or oversight in a system that allows protection mechanisms to be by-passed. The insertion of a flaw into a system could be enabled with other IW weapons, such as the use of coherent RF weapons, over networks from remote sites or could be designed in by an agent-in-place.
- Logic bomb. A logic bomb is a piece of code buried within a larger computer system that executes when a specific system state is realized. An example could be a program that checks for the presence of a piece of data within a file, say, an employee's name within a payroll list, and when the specified logic state is reached—the existence of the employee's name is false—the bomb explodes; for example, the software program may command that the entire system memory be erased.
- Logic torpedo. Weapons like viruses are essentially uncontrolled. A weapon that can be aimed at one or more specific systems and then released through cyberspace to hunt down its target, known as a logic torpedo, would be very useful.
- Time bomb. Similar to the logic bomb, this type of software program waits for a specific time to be realized and then executes. Timing weapon. Also thought of as insidious clocks, these weapons affect the timing of internal clocks to throw off system synchronization.
- Trap door. A trap door is a hidden software or hardware mechanism that permits system protection mechanisms to be circumvented. It is activated in some nonapparent manner—such as a special random key sequence at a terminal. Anyone who has ever programmed knows that despite best efforts, no program ever works correctly the first time (or even the first 10 times). Trap doors are a common safety step used to make sure there is always a way into the program to fix bugs, no matter what the problem may be. The utility of a trap door to provide access for IW purposes is self-evident.
- Trojan horse. As the image invoked by its name implies, a Trojan horse is a computer program with an apparently or actually useful function that contains additional functions that surreptitiously carry out tasks that the user of the
- program would not necessarily execute willingly. For example, a spreadsheet program could contain additional logic to make surreptitious copies of all of the data files on a system. The user of the spreadsheet program would not be aware of those activities occurring while working with the legitimate functions of the program.
- Worm. Similar to viruses, worms are self-replicating but not parasitic; that is, they do not attach to other programs. As demonstrated dramatically by the Internet worm of 1988, they can deny legitimate users access to systems by overwhelming those systems with their progeny. Worms illustrate attacks against availability, whereas other weapons may attack integrity of data or compromise confidentiality.
Disruption Caused by External RF Signals
Radio-frequency energy at the right amplitude and frequency can affect the performance of microelectronics hardware used in computer and information systems. Depending on the nature of the RF signal, a wide range of deleterious effects can occur such as burning out electronic components, disruption of internal logic that may require rebooting or reinitializing the system, interference with the reception of desired signals (jamming), and the introduction of spurious and confusing information (spoofing).
RF signals that can disrupt information and communication systems can be classified as follows: extraneous radio signals from other RF systems, EW jamming and spoofing signals, nuclear-produced EMP signals, high-power microwave energy (HPM), and as a subset of HPM, the very high peak power UWB RF impulse signals. UWB RF impulse signals have both an offensive (disruption capability) and defensive aspect (mitigation)—both aspects need to be considered.
Extraneous Interfering Radio Signals
Computers and information systems can be disrupted by radio signals coming from other systems. Although the disruption may not be purposeful, these interfering radio signals can nevertheless be extremely deleterious and may not be mitigated easily. Some of these interfering signals may be generated by local oscillators in adjacent systems or by static electricity. Lightning-generated impulses have been found to interfere with the guidance computers on space launches; static electricity generated by carpets has caused the failure of computers, and precipitation static generated by aircraft has interfered with the functioning of aircraft computers when not properly dispersed by appropriate wicks.
For example, the Global Positioning System (GPS) operates with virtually a zero signal-to-noise ratio. Almost any other signal that falls within the bandwidth of the GPS receiver can disrupt the ability of the GPS receiver to provide position, track, and velocity information. In one instance, the 13th harmonic
from a local oscillator in an aircraft very high frequency omnidirectional range (VOR) navigation receiver was of sufficient strength to totally disable the functioning of the GPS system. Because of concerns about interference, the British have expressed alarm over the U.S. Federal Aviation Administration's plans to discontinue the support of the existing VOR navigation systems in favor of using augmented GPS in the Wide Area Augmentation System (WAAS). This is scheduled to happen in 2000, long before more capable satellite-borne high-power GPS transmitters will be available.
The vulnerability of computers and information systems to disruption by high-power interfering signals being radiated for other purposes is a vulnerability to modern information systems that must not be overlooked. To address this issue, the government has put in place a special organization, the Electromagnetic Compatibility Analysis Center (ECAC), to ensure minimal disruption of government systems resulting from improper use of allocated frequencies.
Electronic Warfare Signals
Electronic warfare has been an effective warfighting technology for some time. For the purposes of this report, EW activities related to the intercept and ion exploitation of enemy signals and spoofing are not discussed here as they do not by themselves lead to disrupted computers and information systems but involve the collection of electronic signal intelligence.
EW technologies underwent rapid evolution during World War II when new warfighting radio communications and radar capabilities used by both the Axis and Allied forces gave rise, in turn, to systems to disrupt these new communications and remote-sensing capabilities. Since World War II, EW capabilities have continued to evolve—prompted, in part, by perceived new radar and communication system threats, and as a result of the experience gained during the Korean, Vietnam, and Cold wars.
EW signals can be used to spoof, disrupt, or jam RF systems that are integrated into information systems. Disrupting signals can find their way into the RF front ends of the information network receiving systems or into the RF front end of sensor systems. The EW approach takes advantage of the fact that extraneous RF signals can disrupt functioning of the system by raising the noise level of the system being attacked, by introducing extraneous signals that overwhelm the processing capability of the system, or by using EW signals to spoof the ability of the system to carry out its intended functions.
EW offensive actions offer the tactical warfighter the operational capability to defeat the effectiveness of enemy electronics-based communications and radar sensor systems. The ability to operate U.S. information systems in the presence of jamming, especially by sophisticated signal wave forms, will require more attention by the developers of information systems.
Nuclear Weapon Electromagnetic Pulses
The detonation of nuclear weapons causes a number of different types of energetic radiation to be emitted. The high-energy x-rays, neutrons, and other emissions can disrupt the functioning of many solid-state electronic components. This type of disruption is labeled as transient radiation effects on electronics. Another type of disruptive emission is the very high energy EMPs produced by the detonation of nuclear weapons.
EMP concerns have prompted extensive Department of Energy (DOE) studies of how nuclear weapons generate such emissions and their possible effects on military systems. Following serious disruptions of power and other electronics systems during the U.S. nuclear test programs, the DOD subsequently initiated efforts to find ways to prevent EMP signals from entering C3 facilities and burning out electronic equipment. Based on many years of EMP interference measurements, a special set of handbooks was prepared and made available to system designers that describes in detail how to harden systems and facilities against the disruptions that can be caused by EMP signals. As a result of this engineering know-how regarding EMP protection, many important U.S. C3 facilities are appropriately hardened against EMP, and some satellite systems also incorporate EMP-hardening attention (e.g., MILSTAR).
High-power Microwave Disruptions
The identification of the existence of nuclear EMP signals during U.S. nuclear test programs raised the feasibility of developing nonnuclear HPM sources to destroy electronic systems. This concept encouraged a wide range of DOD-supported R&D activities in HPM transmitter developments, with research carried out in both government and industrial laboratories. These efforts have evolved, expanded, and matured into what has become known today as the High-power Microwave effort.
Until quite recently, virtually all of the HPM developments have focused on obtaining very large average power transmitters capable of disrupting or destroying electronic components. Laboratory-based experimental HPM facilities are very large—consisting of rooms full of equipment—and are not suitable for use in tactical warfighting scenarios. HPM sources may, however, have practical applications at fixed antiballistic missile (ABM) facilities as adjuncts to conventional missile-based ABM approaches.
In addition, interest in potential HPM weapons was stimulated by intelligence reports about Soviet advances in HPM-generation technologies—many still consider the Russians well ahead of the United States in HPM research. Although operational HPM weapons have entered the development process, to date none has been successfully fielded. As with EMP disruption, a set of engineering handbooks has been prepared that deals with the various techniques of protecting electronic systems from HPM disruption signals.
Ultrawide-band Radio-frequency Impulse Disruptions
Ultrawide-band radio-frequency impulse signals consist of very-short-duration, very-high-peak-power RF pulse signals. The duration of the impulses is on the order of one or two RF cycles (a nanosecond or two), and they may have peak signal powers of a few hundred kilowatts to hundreds of gigawatts, depending on the antennas used to radiate them. Most UWB RF impulse transmitters can generate repetitive impulses with pulse rate frequencies up to 100 kHz.
Some consider UWB RF impulses to be part of the HPM family. Proponents of HPM technologies have found that some electronics can be affected if the HPM signals are modulated with specific frequencies that match those in the electronics to be targeted. The panel has chosen to consider UWB RF impulse signals as a separate category primarily because they disrupt rather than attempt to destroy or burn out electronic circuitry. UWB RF impulse transmitters generate extremely high peak power signals, whereas most HPM transmitters attempt to generate high-average-power signals. Also because of the small-size, light-weight nature of the UWB RF impulse transmitters, they are more readily deployable than are HPM transmitters.
UWB RF signals can disrupt most of the computers and information systems in use today. UWB RF-induced disruptions are typically transient, but they can cause a system to require rebooting before it can again become functional. Variations in the pulse rate frequency can significantly affect the nature of the disruptions observed.
UWB RF impulse signals tend to be disruptive regardless of the existing internal clock rates, but their disruptive potential may be enhanced by matching the pulse rate frequency to the internal clock speed of the targeted equipment. The wide bandwidth of the UWB RF impulses—as much as several gigahertz in some cases—enhances their ability to disrupt a variety of systems, although detailed understanding of how UWB RF pulses couple to electronic systems is not currently available.
One type of fundamental UWB RF impulse technology is the bulk avalanche semiconductor switch (BASS). BASS operates on the principle that a solid-state chip, when illuminated by a laser, will short-circuit in a few picoseconds. When some 10,000 to 12,000 volts are momentarily placed across a GaAs semiconductor device, and the switch is placed in a simple RF circuit, the resulting avalanche of current produces approximately 1 megawatt of RF energy that is essentially one RF cycle in duration. A single BASS module, complete with timing circuits, is about 2 x 2 x 6 inches in size and weighs less than a pound. All it requires to function as an RF source is an external trigger generator and a battery.
The pulse repetition frequency that can be achieved with BASS devices is on the order of 10 kHz. As a result, the average energy in the repetitive pulse train is small, and it is the peak power that affects digital microelectronics functioning. RF impulses with center frequencies from 50 to 2,000 MHz have been generated
using the BASS technology. Through the use of precision timing, several BASS switches can be combined to form a much higher peak power system. When configured in the form of an antenna array, peak power levels of 1 GW have been obtained, and because of the gain of the array, a 100-GW ERP can be obtained. The individual BASS units making up the array can be timed—equivalent to phasing in a more conventional phased array antenna—so that the beam can be steered over a 60° angular cone.
Because of the high bandwidth of UWB RF impulses, they have noise-like characteristics when detected by most narrow-band receivers. Using UWB RF signals as a jammer source introduces the possibility that enemy systems could be jammed, whereas friendly systems could be designed to accommodate the periodic impulses. A possible application of this concept is the ability to jam GPS and deny it to an adversary but still allow friendly forces to continue to use it without degradation—a scheme that might be called intelligent jamming.
Because UWB RF impulse transmitter systems are relatively small and light-weight and require only modest levels of prime power, they appear to be suited for tactical applications. They also appear to be the only RF disruption technology compact enough to be deployed on satellites.
Information Warfare Related to Space
The possibility of conducting offensive IW actions against space systems has been considered, including interfering with the functioning of ground terminals and interfering with the functioning of satellites by using ground-based HPM systems. In most instances, such electromagnetic-based antisatellite (ASAT) efforts have been based on HPM technologies that are capable of burning out or destroying electronics in the satellite systems but that require huge facilities and copious amounts of power. Moreover, there are treaties and space laws that preclude such destructive actions. The recent emergence of new transmitter technologies that permit the generation of UWB RF impulses opens the door to new disruption capabilities—and using such transmitters in space seems particularly practical.
Do UWB RF Impulse Systems Pose a Threat to U.S. Information Systems Now or in the Future?
Countries other than the United States have extensive background in the development of RF weaponry. For example, the former Soviet Union pioneered the development of UWB RF impulse technology, and this technology is now being offered to other countries by both Russia and the United States. It is expected that in future conflicts the United States will encounter enemies using UWB RF weapons to disrupt U.S. information systems, and this will require that U.S. information systems be appropriately protected. Some protection approaches
are available from prior EMP hardening efforts, but additional methods are needed to counter extremely high peak powers and high-frequency components of UWB RF impulses.
Other Related Technologies
High-average-power transmitter systems from the HPM program may still have practical utility, especially when such microwave signals are modulated in ways to have a maximum effect on digital electronics. High-average-power HPM transmitter systems that are best suited for large ground-based facilities may find use in ballistic missile defense applications.
The existence of very-high-power HPM RF transmitter sources will allow for other kinds of directed-energy weapon (DEW) disruptions, e.g., linear accelerators that can be used to generate a focused beam of secondary x-rays—where RF shielding and filtering protection approaches are totally ineffective.
Development Drivers
The U.S. military does not have to develop all of the defensive IW capabilities independently of the defensive IW technologies available from the commercial sector. In most cases, the technologies that will support military defensive IW needs in the hacker and software categories are being developed more rapidly in the civilian information system environments than they are in the military environments. Defensive and offensive IW activities associated with emerging UWB RF impulse technologies will be more suitable for military development than commercial. A major increase in efforts is warranted to develop defenses for information and communication systems that offer protection against this new capability. Offensive developments of this technology not only should be considered for disrupting enemy information infrastructures but also should be used to evaluate the vulnerabilities of U.S. information infrastructures.
The panel believes that the Navy Department must make every effort to work on both the defensive and offensive IW development programs in close coordination and cooperation with the other military departments, with joint chiefs of staff, and with operational commanders.
The Department of the Navy should establish close working relationships with the recently formed presidential commission for the protection of critical infrastructure and undertake, where appropriate, cooperative efforts to protect infrastructure critical to naval operations, even though such infrastructure may be in the commercial sector.
Time Scale for Development and Insertion
There are some defensive and offensive IW prototype concepts involving the
UWB RF impulse technologies, but to date little has happened to bring them to the operational naval forces. As such hardware and software offensive and defensive IW concepts are brought into existence, the Department of the Navy should undertake an expanded set of IW-related advanced technology demonstration exercises in which these new concepts, ideas, and capabilities are brought together and experimentally evaluated and verified.
Development of both offensive and defensive IW capabilities is going on now at a modest pace. Developments should be accelerated and expanded and should be expected to continue indefinitely into the future for some time to come. Today, the United States probably has better offensive IW capabilities than it does defensive ones. The proliferation of more complex information system architectures with attendant large-scale integrated circuit electronics has caused the defensive posture associated with Navy and Marine Corps information systems to currently be far short of the robust levels needed for achieving information dominance and winning future information wars.
Concluding Observations
The panel presents the following observations:
- Emerging new UWB RF impulse transmitter systems are small and light-weight, require relatively low levels of prime power (average), and are suitable for tactical or terrorist applications.
- Because of their very high peak power signal, UWB RF impulses have unique capabilities to disrupt nearly all digital microelectronics hardware used in information systems.
- UWB RF impulse signals have the potential to pose a very serious threat to the cyber portion of the critical infrastructure.
- UWB RF impulse transmitter technology is being made available outside the United States and is becoming available to terrorists and potential enemies.
- UWB RF impulse transmitters have such low cost and complexity that many nations who might want to take down or disrupt both military and commercial information and communication systems can readily acquire the technologies to do so.
- Concerns exist about the paucity of defensive capabilities to mitigate these emerging UWB RF impulse weapon threats.
- To date, there are no confirmed examples of any use of these emerging UWB RF impulse technologies to disable U.S. military or commercial information system hardware.
- It is probably only a question of time before a UWB RF impulse disruption is experienced.
Recommendations
Information and networking are expected to play a dominant role in future military engagements. Rapid access to appropriate knowledge at all levels will optimize warfighting and crisis response capabilities. Within this context a number of key information-processing technologies are discussed here. Recommendations regarding these technologies for Department of the Navy consideration are as follows:
- The Department of the Navy should exploit evolving commercial technologies in knowledge extraction, data management, and data presentation, together with unique military technologies in data fusion and automatic target recognition to deal with the increased complexity and tempo of warfare.
- The Department of the Navy should engage in early exploitation of the rapid growth in commercial communications capabilities, including satellites and fiber-optic communications, to acquire the necessary increased bandwidth and diverse routing for future networking needs. The Department of the Navy should also prepare for graceful degradation of these systems at times of warfare.
- The Navy Department information systems should be protected against increased software and electromagnetic information warfare attacks and other vulnerabilities. The Department of the Navy should develop offensive information and electronic warfare technologies to find, identify, and attack adversary systems and to strengthen naval systems.
Specific recommendations regarding IW are as follows:
- The segment of the Navy Department that is involved in and concerned about the survivability of the its information and communications systems should become familiar with possible disruption threats associated with UWB RF impulse signals.
- Ways to use these new emerging UWB RF impulse signals as offensive IW weapons should be integrated into operational systems by the EW technical community, which has an established track record of working with the military forces.
- The Department of the Navy should recognize both the disruption and protection aspects of the UWB RF impulse threat. Successfully solving the protection problems requires understanding how UWB RF impulse signals disrupt systems.
- To ensure that the United States maximizes its ability to conduct both defensive and offensive warfare, the current restrictions separating the two activities should be eliminated so that both defensive and offensive IW aspects can be considered in an integrated fashion.
- All hardware and companion software associated with information systems
- should have their vulnerabilities to UWB RF impulse disruption signals evaluated and mitigated where practical. Particular attention should be given encryption systems and emerging microelectromechanical systems technologies.
- The Department of the Navy should encourage its own intelligence activities as well as National-level7 intelligence activities to make it a high priority to track the proliferation of UWB RF impulse technologies.
- The Department of the Navy should make every effort to enter into cooperative activities in support of the recently formed presidential commission for protection of critical national infrastructure components as their protection will ensure that naval force uses will continue to be robust in times of military conflicts.









































