2
Understanding Counterfeiting
Examining the counterfeiting threats from technology and developing novel counterfeit-deterrence features for future implementation require a full understanding of recent trends in counterfeiting and of the evolving characteristics and competences of counterfeiters. Since the committee, like the majority of this report’s expected readership, was not composed of currency experts, it concluded that two important steps in determining how to deter identified counterfeiting threats are to understand (1) who is doing the counterfeiting and (2) what the different steps in the counterfeiting “system” are. These issues proved to be useful tools for evaluating the effectiveness of potential features.
PORTRAIT OF A COUNTERFEITER
The portrait of a counterfeiter is intrinsically linked to the evolution of the technology of currency production and the evolution of technologies that can be used to replicate and simulate currency features. Five classes of counterfeiter can be characterized by the technologies and the methods that they use—primitive, opportunist, petty criminal, professional criminal, and state-sponsored. Table 2-1 summarizes the key attributes of each class, and Table 2-2 characterizes their activities and methods of passing notes. Table 2-3 shows what access to various kinds of current digital technology the different classes of counterfeiter have. The relative threats associated with each criminal class are depicted in Figure 2-1. These portraits are expanded on below.
TABLE 2-1 Classes of Banknote Counterfeiter, Their Tools, General Location, and Impact
|
Class |
Typical Practitioner |
Primary Tools |
Location |
Impact of Activity |
|
Primitive |
Unusually motivated individual |
Manual artistry |
Domestic or foreign |
Very low |
|
Opportunist |
Opportunistic young adult, typically works alone |
Home office equipment |
Domestic |
Created largest increase in $20 domestic-passed currency |
|
Petty criminal |
All ages, criminal intent, typically works alone |
Home office equipment plus specialty materials and processes |
Domestic |
Low, stable level of activity |
|
Professional criminal |
Criminal, trained in printing technology, often part of a criminal group |
Offset printing, high-end ink-jet printers, specialty materials and processes |
Domestic or foreign |
Low, stable level of activity |
|
State-sponsored |
Professional, profiteer or terrorist, member of a large organization |
All materials and processes, including specialty paper, intaglio and offset printing, security features |
Foreign |
Strategic concern |
TABLE 2-2 Methods and Extent of Dissemination of Counterfeit Banknotes, by Class of Counterfeiter
|
Class |
Production Level |
Stockpiling |
How Notes Are Passed |
|
Primitive |
Very small |
None |
Individually, by counterfeiter |
|
Opportunist |
Small, as needed |
None |
Individually, by counterfeiter or friends |
|
Petty criminal |
Small to moderate, often over years |
None to moderate |
Individually, by counterfeiter or criminal associates |
|
Professional criminal |
Large |
Large |
Through criminal networks |
|
State-sponsored |
Large |
Unknown, presumably large |
Through various legitimate and illegitimate networks, often by unwitting accomplices |
TABLE 2-3 Digital Technology Access, by Class of Counterfeiter
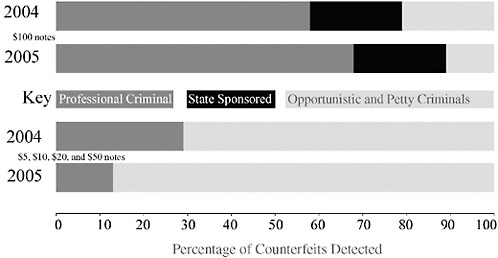
FIGURE 2-1 Comparison of the percentages of counterfeit notes—created by professional criminals, state-sponsored counterfeiters, and opportunist and petty criminals—detected in 2004 and 2005. The two upper bars represent the percentage of $100 counterfeits by source and show the primary source to be professional criminals. The two lower bars represent percentages by source for the sum of $5, $10, $20, and $50 counterfeits, showing the growing dominance of opportunist and petty criminals (the light-grey segments). Note that state-sponsored counterfeits are identified only for $100 notes (the black segments) and that primitive counterfeiters do not account for enough counterfeits to appear on this chart. SOURCE: Data provided to the committee by the U.S. Secret Service.
The Primitive Counterfeiter
The criminal perpetrator of primitive counterfeiting may use manual artistry to modify a piece of currency in order to increase its value and obtain financial gain. The phony notes thus produced are easily detected by attentive cash handlers and, upon examination, by the general public. An example is a note that has cut-and-pasted numbers increasing the denomination of a $10 bill to $100.
The primitive counterfeiter’s products are often obvious to the point of parody. They are clearly incompatible with automatic currency-authentication equipment and must be passed person to person. If the substrate is an existing Federal Reserve note (FRN), the counterfeit note retains the correct feel of genuine currency and may have advanced security features such as a watermark and a security strip, albeit for the wrong denomination.
Such a note may be passed in a number of ways—for example, the counterfeiter may try to distract the cashier to prevent scrutiny of the counterfeit. He or she may also rely on the reluctance of a cashier to question the authenticity of a banknote in a point-of-sale situation.
The Opportunist Counterfeiter
Over the past decade, desktop publishing has become the dominant tool for counterfeit printing operations in the United States. In fiscal year 2001, 93 percent of suppressed counterfeiting operations used digital processes; this is a very significant increase, from less than 20 percent in 1995.1 This trend, begun in the United States, has continued worldwide. Digital publishing tools, including color copiers, scanners, and ink-jet printers—all typically found in a college dormitory room or home office—powered by information available on the Internet, are the engines that impel opportunist counterfeiters to undertake this criminal activity. Increasingly, opportunist counterfeiters are also using all-in-one, combination scanner-and-printer devices. The devices may be controlled by a computer with image-processing software to modify the image and connect to the Internet. Instead of learning from master engravers and operators of offset printers, the opportunist uses Internet searches to obtain know-how and may tell no one else or might share the information with a few friends. The designation of “opportunist” implies that this counterfeiter uses only equipment that is commercially available and that has been obtained for more legitimate uses.
Opportunist counterfeiters are typically young adults, with a median age of perhaps 18 years. They work as individuals, making only a few notes at a time and printing them “on demand” from their residence or place of employment. They typically pass these notes personally or via friends in retail transactions. Their counterfeits span a wide range in quality, from single-sided notes2 to impressive duplications requiring many hours of refinement in touching up colors, aligning front and back images, and refining enhancements to the printed image to simulate advanced security features using arts-and-crafts supplies. The $20 note is the denomination most commonly produced by this class of counterfeiter, because it is the note expected in many transactions.
As is true for primitive counterfeits, the vast majority of counterfeits made by opportunists are detected at or near the point-of-sale. They rarely are passed more than once and generally are discovered before circulating back to a Federal Reserve Bank (FRB). Eighty percent of these counterfeits are turned over to the U.S. Secret Service by commercial establishments, financial institutions, and law enforcement.3
|
1 |
U.S. Department of the Treasury. 2003. The Use and Counterfeiting of United States Currency Abroad, Part 2. The second report to the Congress by the Secretary of the Treasury, in consultation with the Advanced Counterfeit Deterrence Steering Committee, pursuant to Section 807 of Public Law 104-132. P. 60. Available at <http://www.federalreserve.gov/boarddocs/rptcongress/counterfeit2003.pdf>. Accessed February 2007. |
|
2 |
How Counterfeiting Works. Available at <http://money.howstuffworks.com/counterfeit.htm>. Accessed February 2007. |
|
3 |
United States Department of the Treasury. 2000. The Use and Counterfeiting of United States Currency Abroad. Report to the Congress by the Secretary of the Treasury, in consultation with |
The opportunist’s typically youthful age and exploratory approach often lead to situations with unexpected consequences. For these reasons, widely informing the public of the U.S. Secret Service’s conviction rate—higher than 90 percent4—of counterfeiters may significantly reduce the opportunist’s temptation to “make a little money.”
The Petty Criminal Counterfeiter
The petty criminal counterfeiter has a clear and systematic intent to counterfeit repeatedly. These practitioners use the same digital tools that opportunists employ and may supplement their efforts with specific materials such as the best paper and inks. Using the Internet, they develop and share a set of tricks to improve their simulations and to help them pass their phony bills. The tricks include methods to bypass or negate certain authentication methods, such as the “iodine” starch-detecting pen, as well as ways to handle the encounter when their creation is questioned. This type of operation is still an individual or small effort, but it differs from the activities of the opportunist in duration, quantity, or distribution area. Some of the best counterfeits in this class display innovative ways to simulate the security strip, the watermark, and the specialty inks. This class of counterfeiter will likely be the first to challenge automatic currency authenticators.
The Professional Criminal Counterfeiter
The professional criminal counterfeiter class generates phony bills that are typically relatively easy to pass to the public. These counterfeiters simulate all of the critical features of genuine notes to some degree—in fact, the simulations often require additional criminal activity in order to acquire controlled materials such as security inks and paper. These counterfeiters are typically part of a larger criminal enterprise that can include dedicated specialists who sometimes have professional training in the printing business. Their efforts involve generating significant quantities of counterfeits, along with developing the necessary distribution methods—which may also be tied to other criminal endeavors, such as the counterfeiting of identification cards or other security documents. This type of distribution far surpasses that of the petty criminal.
The Secret Service actively pursues these criminal organizations, tracking their activity by classifying recovered counterfeits into groups. Each note received by the
|
the Advanced Counterfeit Deterrence Steering Committee, pursuant to Section 807 of Public Law 104-132. Available at <http://www.ustreas.gov/press/releases/reports/counterfhp154.pdf>. Accessed February 2007. |
Secret Service is characterized, classified with the telltale information that reveals the source, and put into a database so that law enforcement and commercial banking organizations around the world can assist in counterfeit identification.
Much professional counterfeiting activity is located outside the United States, although a substantial fraction of the counterfeit notes may be passed domestically. The target denominations of professionals criminals include the $20, $50, and $100 notes—with the $100 note being the most counterfeited overseas. Judging by the typical amount of currency seized when the government shuts down professional operations, this class of counterfeiter can pose a serious threat. However, continuous enforcement efforts by the U.S. government, often working with foreign governments to change and enforce laws, as well as attention to foreign currency-handling procedures and the introduction of the new currency designs, have kept the impact from this potentially significant source of counterfeits low.
The State-Sponsored Counterfeiter
State-sponsored counterfeiters not only plan for criminal financial gain but may also have a political goal—such as reducing global confidence in U.S. currency. Thus, they are willing to invest in technologies to duplicate U.S. banknote features exactly. State-sponsored counterfeits may be passed by both apparently legitimate and criminal means. The very-high-quality so-called supernotes that duplicate nearly all of the security features of genuine banknotes are created by this class of counterfeiter.
Some state-sponsored organizations make their own paper with watermarks and colored threads, make their own specialty inks, and re-author the engraved image. They use the same printing methods—intaglio and letterpress—and may integrate their own forensic features that would enable their own internal discrimination. While these notes would fool most cash handlers and even some machine authenticators, they can still be identified by the Federal Reserve System and the Secret Service. The U.S. government has confirmed its suspicion that the North Korean government is involved in the state-sponsored production of supernote counterfeits.5 It has been reported in the media that more than $45 million is estimated to have been passed by this source since 1989.6
|
5 |
See <http://www.state.gov/p/inl/rls/nrcrpt/2006/vol2/html/62144.htm>, <http://losangeles.fbi.gov/dojpressrel/pressrel06/la041906usa1.htm>, and <http://www.usdoj.gov/criminal/press_room/speeches/2005_4193_rmrksOprSmokngDrgnNroylChrm082405O.pdf>. Accessed February 2007. |
|
6 |
B. Gertz. 2005. N. Korea charged in counterfeiting of U.S. currency. Washington Times. December 2. Available at <http://www.washtimes.com/world/20051201-103509-5867r.htm>. Accessed February 2007. |
Who Does What?
Forensic science can identify common characteristics among discovered counterfeit notes that can be traced to unique aspects of the counterfeiting process used and thereby allow the counterfeits to be classified according to their sources. Table 2-4 presents a snapshot of the magnitude of U.S. banknote counterfeiting for fiscal year 2005. These numbers are typical of the counterfeiting threat in recent years. The counterfeits are classified by the Secret Service according to their source, either domestic or foreign, and according to whether they were discovered before or after they were passed into circulation. These data provide some insights into the patterns and practices of counterfeiters.
A FLOW MODEL FOR COUNTERFEITING
Counterfeiting begins—but does not end—with the printing of bogus banknotes. After producing (and possibly stockpiling) notes of a sufficient quality and quantity, the counterfeiter still has work to do. To realize a profit from these efforts, he or she must then exchange the counterfeit notes for cash, goods, or services. After a counterfeit note has been passed, it will circulate until it is detected and removed from the system. Then, and only then, is the economic loss of counterfeiting realized: the last one holding the fake banknote loses.
Decisions about which particular feature (or combination of features) to incorporate into future FRNs must be based on many criteria: the difficulty of replication or duplication by various classes of counterfeiters, the clear ability of ordinary people to distinguish between legitimate and counterfeit notes, durability, cost, aesthetics, and so on. Gaining a consensus about how these factors should be combined into an overall figure of merit is not straightforward. The committee suggests one method to determine how some of these criteria can affect
TABLE 2-4 U.S. Banknote Counterfeiting in Fiscal Year 2005: Production Technology, Class of Counterfeiter, and Amount (in U.S. dollars)
|
Primary Production Technology |
Primary Criminal Class |
Domestic Passed ($) |
Domestic Seized ($) |
Foreign Passed ($) |
Foreign Seized ($) |
|
Ink-jet printing |
Opportunist, petty criminal |
29,153,845 |
5,940,531 |
29,984 |
642,841 |
|
Electrophotography |
Opportunist, petty criminal |
2,164,475 |
758,045 |
8,690 |
9,920 |
|
Offset press (domestic) |
Professional |
2,264,582 |
1,608,682 |
72,593 |
7,186,140 |
|
Offset press (foreign) |
Professional |
21,244,276 |
1,290,340 |
746,910 |
11,971,514 |
|
Intaglio press (foreign) |
State-sponsored |
1,401,300 |
5,083,200 |
3,939,200 |
531,200 |
|
TOTAL |
|
56,228,478 |
14,680,798 |
4,797,377 |
20,341,615 |
|
SOURCE: Data provided to this committee by the U.S. Secret Service. |
|||||
one important measure: the amount of counterfeit currency in circulation. This method uses a simplified model to map the flow of counterfeit currency from production to removal.
It is important to note that the committee does not suggest that this particular elementary model should be used to make policy decisions about adopting future features. Instead, the model is presented only as a device to provide a possible rationale for determining which features might be—in some sense—evaluated as being “better” than others. Moreover, for this (or any alternative) model to be used as an instrument for determining policy, it would have to be appropriately validated. As discussed below, this would require either estimating its parameters from existing field or experimental data, or running experiments specifically designed with this goal in mind. In any event, a truly useful model would have to be capable of considering sets of features together, since features do interact, in addition to overcoming the limitations of this quite-basic model. The model is presented as an aid in explaining the origins of the evaluation process adopted by the committee.
This said, the counterfeiting threat can be represented as a basic flow system, as shown in Figure 2-2, in which the boxes represent repositories of counterfeit currency (containing amounts measured in units of dollars). Counterfeit notes progress through the system from production, through stockpiling and, by means of a passing event, into circulation. These flows are indicated by the arrows in Figure 2-2. At each stage, disruptions to the system can be introduced by removing counterfeit notes or by deterring their production—shown as arrows pointing to the ovals that represent repositories of counterfeit currency removed from the system. The variables used to represent this system are defined in Table 2-5.
The topmost ovals in Figure 2-2 are special cases—representing counterfeits that are never actually made because of technology stoppers, or “blocks,” or owing to the difficulty of feature simulation. As such, these ovals are “virtual” repositories of counterfeits; no actual notes reside there. The effect of these virtual repositories is captured in ρ, the counterfeit production rate, which reflects the effects of technology stoppers or the difficulty of feature simulation for the purpose of feature evaluation. In particular, any increased flow to the virtual repositories will necessarily decrease the production rate, ρ.
In order to best analyze this system, the parameters for each feature and for each class of counterfeiter should be quantified. While the values of some of these are known, such as u (the amount seized by the Secret Service), many others remain unknown. However, a strong case can be made for estimating or measuring these variables, since they provide a basis for quantitative analysis of the effect of new features on counterfeit deterrence, as discussed below. Even for variables that are hard to measure in the real world—that is, s, the fraction of successful pass attempts—controlled experiments could provide some insight that would aid in modeling the system. With the aid of a fully characterized flow model, such as

FIGURE 2-2 A flow model for counterfeiting. The boxes indicate the components of the counterfeiting system. The ovals represent processes by which counterfeit notes are removed from the system. Arrows indicate the flow of counterfeit notes. NOTE: USSS = U.S. Secret Service. Variables are defined in Table 2-5.
the simplified one presented here, or a more sophisticated version,7 the impact of adding and subtracting features could be scientifically evaluated, and realistic cost-benefit analyses and feature comparisons could be made.
Appendix E shows the details of an analysis based on this extremely simple model and a number of simple, yet qualitatively reasonable, assumptions. The
TABLE 2-5 Variables in the Flow Model for Counterfeiting
|
Variables |
Definition |
|
Counterfeit repository (total $) |
|
|
u |
$ seized from stockpile by U.S. Secret Service (USSS) |
|
v |
$ culled from banking system by the Federal Reserve System (FRS) |
|
w |
$ turned in to USSS by a recipient |
|
x |
$ in stockpile, awaiting first pass attempt |
|
y |
$ in circulation |
|
z |
$ held by a recipient, but not reported or repassed Rates |
|
Rates |
|
|
c |
Confiscation rate of notes from stockpile ($ per unit time) |
|
β |
Rate of culling in the banking system by the FRS (per unit time) |
|
|
Rate at which first attempts are made to pass note from stockpile (per unit time) |
|
θ |
Rate at which repass attempts are made during circulation (per unit time) |
|
ρ |
Counterfeit production rate ($ per unit time) |
|
Other parameters |
|
|
h |
Fraction of pass attempts held and not reported to the USSS; h = 1 − s − r |
|
r |
Fraction of pass attempts reported by recipient |
|
s |
Fraction of successful pass attempts |
|
t |
Time since start of production |
result is a set of linear differential equations, which yield the temporal change of the amounts of counterfeit currency located in the boxes and ovals, and which provide the underlying dynamical relations among the parameters and variables in the system.
The most salient output of the analysis in Appendix E with respect to feature selection is the steady-state amount of counterfeit currency in circulation given by the following equation:8
(2-1)
Some of the parameters in this equation may not be linked to the particulars of note features. For example, c, the confiscation rate of stockpiled counterfeits, is likely influenced most by law enforcement activities, and β, the rate of culling from the banking system, is a function of how often all notes pass through machine authenticators in the banking system. However, the ability of a feature to decrease the amount of circulating counterfeits is related to its ability to do the following: (1) decrease the counterfeit production rate ρ via technology stoppers or difficulty of simulation, (2) decrease the fraction of successful pass attempts s because of unacceptable feature replication or duplication, and (3) increase the rate at which repass attempts are made during circulation θ.
Perhaps the most important insight provided by Equation (2-1) is the nonlin-
|
8 |
The derivation of this equation is explained in Appendix E of this report. |
ear, nonadditive contributions of the production and pass rates to the amount of counterfeit currency in circulation. This nonlinearity, which can result in surprising conclusions, illustrates the strength of the flow model as a tool for feature analysis, as shown in hypothetical examples in Box 2-1 and in Appendix E.
The model’s results, as exemplified in the Box 2-1, are salient to the committee’s task of evaluating the effect of potential security features in reducing counterfeiting. Although flow models such as this have been developed for representing the
|
BOX 2-1 Comparison of Features Using the Flow Model An analytical model can provide (perhaps non-intuitive) insights into the systems within which counterfeit notes circulate; such insights can then contribute to the decision-making process for the selection of promising features. For example, consider two potential counterfeit-deterrent features: Feature A is easy to simulate visually but also easy to detect. Feature B is difficult to simulate convincingly but also difficult to detect in a casual transaction. For illustrative purposes, assume that Feature A deters only 10 percent of counterfeit attempts, but deters 90 percent of passing attempts. Feature B deters 90 percent of counterfeiting attempts, but only 10 percent of passing attempts. These numbers are reflected in the counterfeit production rate ρ and passing fraction s shown in Table 2-1-1. Using an additive rating scheme with equal rates (a common first screen that one might use to assess feature effectiveness), the resulting “score,” ρ + s, is the same for both features, implying that they are equal in deterrence effectiveness. However, Equation (2-1) in this chapter allows calculation of the steady-state amount of counterfeit currency in circulation. It is assumed, for convenience,1 that θ = 50 (that is, average time between passing attempts is approximately 1 week), β = 10 (average time required for removal of the counterfeit note from circulation is approximately 1 week), and the stockpile con .scation rate c is proportional to the production rate ρ. (This calculation is presented in more detail in Appendix E.) Then Equation (2-1) indicates that Feature A is three times more effective at decreasing the amount of counterfeit currency in circulation than is Feature B. Even though the two features appear similar—even in terms of their overall “score ”—Equation (2-1) suggests that they are different in their effect on deterring counterfeiting. TABLE 2-1-1 Counterfeit Production Rate and Passing Fraction for the Flow Model
|
amount of currency in circulation, to the committee’s knowledge they have not been used to analyze counterfeit currency flows. As mentioned above, other models, focusing on different flows, variables, and dependences, could also be used.
EVALUATING SECURITY FEATURES WITH THE FLOW MODEL
The goal of any anticounterfeiting effort is to minimize x, the amount of stockpiled counterfeit notes, and y, the amount of circulating counterfeit notes. A flow model can show how these amounts are affected by various flow rates and parameters.9 Analyzing and understanding the factors that affect the flow provide a basis for understanding the counterfeiting threats and evaluating the outcomes of potential new features. This section summarizes, by relevant flow model variables, the likely effects of various anticounterfeiting efforts that are related to banknote features. As explained in Chapter 4, these considerations were important in the development of a feature assessment methodology and thus were crucial to the selection of the innovative features that are discussed in Chapters 4 and 5.
Decreasing the Counterfeit Production Rate—Parameter ρ
The first opportunity to combat counterfeiting occurs with the deterrence of note production. An array of new, digital tools is increasingly being used by counterfeiters in their attempts to simulate banknotes. The low cost and accessibility of these technologies make them readily available to potential counterfeiters. These new tools continue to challenge the currency designs, especially image-based features.
One deterrence strategy is to prevent production directly, by limiting the availability, the capabilities, the materials, and the use of counterfeiting technology. In fact, this was the first anticounterfeiting strategy implemented by the U.S. government in the 1860s. The distinctive look and feel of intaglio printing could be achieved only by printing processes that were of very limited availability. Likewise, the substrate paper and some of the specialized inks are exclusive to the Bureau of Engraving and Printing. The usefulness of digital imaging tools can be limited both by technology in the printers and by limiting access to the tools themselves. By international agreement, commercial color printers prevent the printing of banknotes—they recognize certain features of various major currencies and refuse to process the image further. Similar technology is implemented in digital image-processing software and in digital scanners. Although these limitations undoubtedly deter casual counterfeiting, they are not foolproof against a determined hacker. Thus, technology stoppers, even when well implemented, are not a panacea, and if
|
9 |
For example, see Appendix E, Table E-1. |
TABLE 2-6 Committee’s Analysis of the Usefulness of Current Security Features in Deterring Counterfeiting, Evaluated by Class of Counterfeiter
they are poorly implemented they could have serious consequences for the operability of the equipment.10
A second way to deter counterfeit production is by incorporating features in the note design that are difficult to simulate. Current U.S. banknotes combine numerous features that present varying levels of challenge to counterfeiters in order to provide a layered defense against an array of counterfeiting threats. Although highly qualitative, Table 2-6 provides some insight for optimizing the use of the limited space on the note and avoiding a saturation of features; the table presents an analysis of the usefulness of current security features in deterring counterfeiting, evaluated by class of counterfeiter. The goal of selecting a feature set is to maximize the amount of time, effort, and skill required to create a convincing simulation of the note. This can be accomplished by selecting a complex design, or by focusing on a few, very-difficult-to-simulate features. The trade-off between a complex note
and a simple note is also affected by the ease of authentication, which is discussed below.
Although Table 2-6 indicates that the current feature set is not a significant deterrent to the professional criminal or state-sponsored counterfeiter, there is another line of defense. Since both of these classes stockpile and pass counterfeits in large quantities, they are vulnerable to law enforcement operations. The Secret Service has been very effective at shutting down large, professional counterfeiting operations and minimizing their impact, as discussed in the next subsection.
Emptying the Stockpile—Parameter c
There is no opportunity for counterfeit notes seized from a stockpile to cause harm, so seizing stockpiled counterfeit notes is an effective way to disrupt the counterfeiting system. A stockpile can be any storage location prior to the passing of the counterfeit; it could be a warehouse, a suitcase, or the pocket of a criminal.
The possession of counterfeit currency is a crime investigated by the Secret Service. To carry out its mission, the Secret Service works with state and local law enforcement agencies, the U.S. Department of the Treasury, and foreign law enforcement agencies to pursue counterfeiters. The committee believes that the expertise and methods employed by the Secret Service are an important component in the successful effort to reduce the counterfeiting rate of U.S. banknotes below that of other major currencies. The decrease in foreign counterfeiting volume between 1995 and 2004 supports this assertion.11 While there are no statistics to indicate what fraction of stockpiled counterfeits the Secret Service captures, the fact that the value of seized counterfeits (about $100 million in 2004) is vastly greater than that of passed counterfeits (less than $15 million annually) indicates great effectiveness in the disruption of the stockpiling of counterfeit banknotes.
Disrupting the Passing of Counterfeits—Parameter s
A counterfeit note does not profit the maker until it is exchanged for value and passed into circulation; if the note cannot be passed, there is no incentive to counterfeit. Therefore, efforts to combat counterfeiting must include strategies to disrupt the passing process. These efforts typically focus on educating the human cash handler to readily identify counterfeit notes and on employing reliable machine authentication.
People who use U.S. currency are the first line of defense against counterfeiting. Because the primary opportunity to pass a counterfeit note is the first point-of-sale,
the key people are those who handle currency as a part of their job. Therefore, the first line of defense is the public, which includes the often-inexperienced clerk at the counter or the taxicab driver and other like individuals who are the most likely points-of-sale for the criminal fraternity. In Canada, studies have shown that 78 percent of counterfeits are detected by individuals and businesses.12 Even the high-quality supernote was first detected not by a machine but by an experienced cash handler who noticed an improper “feel” to the note.13 Clearly, the most efficient way to prevent the passing of counterfeit notes is to design banknotes that can be authenticated at the point-of-sale, and the optimal human-perceptible security feature is visible, usable, and known.
An effective visible feature is one that is easy to authenticate regardless of light levels and the fitness of the note and that therefore creates minimum delay at the point-of-sale. A usable feature does not require out-of-the-ordinary methods such as a magnifying glass, transmitted light, or a machine. A feature that is both visible and usable provides an unambiguous signal in a short amount of time in a variety of environments. This feature is not obscured by a busy or distracting design or by “feature overload.” Because rejecting a banknote is an undesirable event to most cash handlers, the importance of both speed and certainty in feature evaluation cannot be overstated.
The last factor, ensuring that a feature is known, is the most elusive. Knowledge of features does not necessarily mean that a user can name them, but such knowledge may be evinced in an unconscious, habitual awareness. The number of features and the fact that older banknote issues are not devalued can make such education a complex and layered undertaking.
As a result of the public education effort for the new $20 note, public recognition of the currency features increased to 85 percent in the United States. While the impact of feature recognition has not been quantified in the United States, similar educational efforts in Canada have dramatically decreased the acceptance of counterfeit notes by cash handlers.14 Thus, educating cash handlers to recognize security features is undeniably an important factor in counterfeit deterrence.
One of the most basic yet revolutionary methods intended to disrupt passage of counterfeits is the growth of machine authentication. This is not a new concept—in the 18th and 19th centuries, gentlemen of business carried pocket-size scales to ensure that the coins they received were of the correct weight for their value. In those days of coin shaving, it was prudent and socially acceptable to authenticate coins before accepting them. In the 21st century, the concept is being revisited by electronic currency authenticators.
Over the past 15 years, advances in low-cost sensor technology have enabled the machine-reader market to grow in size and scope, while machine readers shrink in cost and footprint. Currently, over $64 billion passes through vending-type note acceptors per year in the United States, with 10 million to 20 million daily transactions;15 in addition, the retail and banking sectors process billions of dollars through machine counters yearly. As sensors continue to decrease in size and cost, machine readers will add authentication capabilities and will become pervasive, particularly in consumer cash-handling applications.
Because notes rejected by a machine reader at the point-of-sale are currently neither tallied nor removed from circulation, no comprehensive statistics are available on the impact of machine readers on the passing or attempted passing of counterfeits. However, industry representatives report that even low-end denominators detect and capture 90 percent of domestic counterfeits, with authenticators nearing 100 percent.16 Therefore, machine readers represent a significant deterrent to the passing of counterfeits. Because rejected notes are typically returned to the consumer, this tool does not require the cash handler to deal with the consequences of accepting a counterfeit, making machine readers particularly attractive to the retail sector. Such authenticators are already in widespread use in Europe and Canada, and their offer of hassle-free security from counterfeits may be attractive to U.S. retailers as well. An increase in the use of machine authenticators could result in a commensurate decrease in the frequency of counterfeits passing.
As machines replace human cashiers, they may increasingly become the first line of defense against the passing of counterfeit notes. It is therefore important to design notes for reliable machine authentication. Current machine denominators and authenticators sense a variety of features, and it is important for currency design to maintain and add features that target the requirements for both human and machine authentication. Specifically, the ideal machine-readable feature would have these characteristics:
-
It could be sensed by a point sensor moving across the note;
-
It would be readable from both feed directions—wide-end-first and short-end-first;
-
It would emit a strong and reliable signal;
-
It would be independent of the orientation and face of the note;
-
It could be reliably located despite manufacturing and reading tolerances; and
-
It would provide series identification.
Removing Counterfeits from Circulation—Parameters r, h, and β
Once a counterfeit note is finally identified, it should be removed from circulation. Even though repeated passing does not result in additional monetary damage, the final person in the chain will feel the impact. Unfortunately, removing counterfeits from circulation is not always straightforward. Several factors affect the efficiency of counterfeit removal and any subsequent law enforcement investigation.
Currently, there is no incentive other than “good citizenship” for the public interception of a counterfeit note close to the initial distribution point. In fact, there is a disincentive to turn in a counterfeit, as the finder receives no compensation and may even be subject to a considerable time penalty from questioning by law enforcement officers.17 The committee understands that a holder of a counterfeit note on balance might rather destroy it (or keep it as a souvenir) rather than contact the authorities. Similarly, manufacturers of currency-handling equipment report that some retailers tend not to purchase dedicated counterfeit-detection modules for their machine counters in order to avoid the inconvenience of dealing with counterfeits that cash handlers had accepted at the point-of-sale.18 There is no question that such an attitude toward counterfeit identification interferes with the identification and removal of counterfeit notes, as well as with the eventual capture of the responsible counterfeiters.19
It may be possible to provide incentives to citizens who turn in counterfeit notes. A primary objection to such a policy is that it would provide an opportunity to counterfeiters to exchange their products for genuine currency, and it might engender an impression in the public eye that counterfeiting is a victimless crime in which the government sustains the loss. However, a system that reimbursed or even rewarded cash handlers for turning in counterfeit notes when and if the counterfeiter was convicted would overcome some of these objections: certainly there would be no benefit to counterfeiters for turning in their own notes, and recipients of counterfeits would be rewarded for their role in the criminal prosecution. Regardless of the details, it is important that any incentive system decrease
the time, trouble, and stigma of turning in a counterfeit. A culture that encourages finding and turning in counterfeits to authorities would be a valuable aid to law enforcement.
As currency circulates, particularly domestically, it is processed through the banking system, often many times before it wears out. Branch banks typically process their cash deposits through desktop currency-counting machines, which incorporate authentication technology. Nearly all branch banks also use machine counter-sorters that can sort, face, count, authenticate, stack, and band notes. Both of these classes of machine have a near-perfect identification record for counterfeit notes, so when these machines are used, passed counterfeits are removed from circulation as they pass through a bank. Any counterfeit notes that might escape the branch banks’ systems are captured at a Federal Reserve Bank, which uses a proprietary machine reader that senses a wide range of overt and machine-readable features.
CONCLUSIONS
-
Five classes of counterfeiter—primitive, opportunist, petty criminal, professional criminal, and state-sponsored—can be characterized by the technologies and the methods they use. The counterfeiting threat posed by each of these classes is somewhat different. Opportunistic, casual counterfeiters pose a particularly onerous threat to the integrity of currency, given the diffuse nature of their counterfeiting activities enabled by affordable, highly capable advanced reprographic and digital technology.
-
The counterfeiting threat can be described by an analytical flow model that relates the steady-state amount of counterfeit in circulation to a variety of measurable variables.
-
Strategies that most effectively deter production, disrupt stockpiling and passing, and remove counterfeits from circulation may differ for each of the five classes of counterfeiter.
-
An analytical flow model can provide a quantitative basis for prioritizing features and feature sets so as to provide the best overall defense against counterfeiting.


















