1
Overview and Context: The Commercial Mobile Alert Service, the Warning Process, and Public Response
This report presents a summary of the Workshop on Public Response to Alerts and Warnings on Mobile Devices: Current Knowledge and Research Gaps, held in April 2010 in Washington, D.C., under the auspices of the National Research Council’s (NRC’s) Committee on Public Response to Alerts and Warnings on Mobile Devices: Current Knowledge and Research Gaps. The workshop explored what is known about how the public responds to alerts (an alert indicates that something significant has happened or may happen) and warnings (a warning typically follows an alert and provides more detailed information indicating what protective action should be taken) and the implications of what is known about such public responses with regard to the U.S. Department of Homeland Security’s (DHS’s) Commercial Mobile Alert Service (CMAS).1 CMAS is currently being developed to provide a national capability to deliver brief text alerts to cellular telephone subscribers.
After the welcome and opening comments, the first session of the workshop introduced CMAS, and the second session provided an overview of what is known about how people respond to alerts and warnings.
In the first session, Denis Gusty, DHS, discussed the origins and current status of CMAS and the program’s requirements. In the second session, Peter White, AT&T, discussed the use of text messages for alerting and the technical and operational considerations that factored into
planning for CMAS. Michael Lindell, Texas A&M University, provided an overview of what is known from past research about the process of sending alerts and warnings and how people respond to them, and Joseph Trainor, University of Delaware, went on to debunk key misconceptions about the public response to alerts and warnings and about other behavior during a disaster. Garry Briese, Briese and Associates, moderated the second session and commented on the use of CMAS to deliver alerts. This chapter provides an integrated summary of these presentations and the discussions that followed, organized by topic.
COMMERCIAL MOBILE ALERT SERVICE (CMAS)
Why CMAS?
Regarding the wide use of cellular telephones and other mobile wireless devices in the United States, CTIA—The Wireless Association® reported more than 290 million U.S. subscribers by mid-2010, a greater than 90 percent penetration rate.2 Cellular networks thus provide an attractive opportunity for delivering alerts and warnings, complementing the mechanisms used today—broadcast radio and television, cable television, National Oceanic and Atmospheric Administration (NOAA) weather radio, reverse-911 (which allows jurisdictions to dial a list of telephone numbers and play recorded messages), and sirens. Cell phones are generally kept close at hand in a variety of settings; their users can be reached on the street, in automobiles, and at home or at work, and audio alerts can even awaken people when they are sleeping. Also, the ability to target messages to a cell phone’s actual location makes it possible to target more precisely those individuals who would be most at risk in a crisis situation. Cell phones thus seem well positioned to fill gaps in message-receipt coverage by traditional systems—as well as additional gaps that may open up as the reach of traditional broadcast media diminishes.
Establishment of CMAS
The Warning, Alert, and Response Network (WARN) Act of 2006,3 which establishes a national all-hazards alert system and calls for the use of multiple technologies, including wireless telecommunications, was
|
2 |
Statistics from CTIA Semi-Annual Wireless Industry Survey, available at http://www.ctia.org/advocacy/research/index.cfm/AID/10316; and CTIA Wireless Quickfacts, available at http://www.ctia.org/advocacy/research/index.cfm/aid/10323. Note that a penetration rate calculated, as here, by dividing subscribers by the U.S. population is likely to be an overestimate, because some individuals may have multiple subscriptions. |
|
3 |
Public Law 109-347. |
motivated in part by a desire to leverage new technologies to increase the reach of alerts and warnings.4 As required under the WARN Act, the Commercial Mobile Service Alert Advisory Committee (CMSAAC) was established in late 2006 by the Federal Communications Commission (FCC) to engage stakeholders in the development of initial policy and procedures for one component of that national system—the use of cellular telephones for alerts. CMSAAC, composed of representatives from service providers, handset vendors, emergency personnel, and industry groups, issued its first report in 2007, defining CMAS’s basic system architecture and establishing technical standards and operating procedures.5
Following the issuance of the CMSAAC report, the CMAS program was established within the Department of Homeland Security. The task of validating the CMSAAC recommendations was assigned to DHS’s Science and Technology Directorate, along with an examination of related issues such as the state of knowledge about the likely public response to alerts and warnings on mobile devices. The workshop summarized in this report was convened as one element of DHS’s examination of public response (see the statement of task for this study in Box P.1 in the Preface of this report).
Overview of CMAS
Three types of alerts were defined by the WARN Act of 2006 for issuance by CMAS:
-
Presidential alerts, to be issued by the president when there is a national emergency or threat (note that a presidential alert, for which the Emergency Alert System [EAS] and its predecessors for communicating with the public in a national emergency were originally implemented, has never been issued);
-
Imminent threat alerts, to be issued when there is an immediate threat to people or property, such as a tornado; and
-
Child abduction emergency alerts (also known as AMBER Alerts), to be issued in the case of a child who has been abducted or who has run away.
Alert system subscriptions can either be opt-in (one must register to receive messages) or opt-out (one must take action to not be registered automatically). CMAS will be an opt-out system; cellular customers would receive imminent threat alerts and AMBER Alerts unless they opted out. It will not be possible to opt out of receiving presidential alerts. Carrier participation is voluntary; to date the major cellular carriers have signed on to the program.
The deployment of CMAS requires new cellular telephone software, which in most cases means the purchase of new handsets, although some phones may be field-upgradable. Once the service is deployed, carriers will be required to notify subscribers if their handsets are CMAS-compatible and to place labels on new handsets indicating whether they support CMAS or not.
CMAS-compatible handsets will use a special alert tone for CMAS messages—to draw attention to the messages and to distinguish them from other messages. This tone will override the normal ringer-volume settings. A unique vibration cadence will also be used to reach hearing-impaired users.
The CMAS architecture (Figure 1.1) provides for alerts to be issued at the federal, state, tribal, and local levels. Alerts are to be transmitted by the originating entities to a Federal Emergency Management Agency (FEMA)-administrated gateway for approval, formatting, and transmission to participating cellular service providers—which will then transmit the alert over their networks.
The message format defined for CMAS was based on prior work to define a standard alert-message format, the Common Alerting Protocol. This format, which specifies the geographical area affected, the recommended action, an expiration time, and the sending agency, is designed to allow messages to increase interoperability with other alert systems. Additionally, the text of the CMAS itself (i.e., not including the header) is limited to 90 characters.
CMAS will use a cell broadcast technology known as short message service-cell broadcast (SMS-CB) to transmit messages. This technology is different from the more familiar short message service (SMS) used to exchange text messages between subscribers. (SMS is also used for alerts and warnings; these opt-in text alert systems have been introduced by a number of organizations and jurisdictions.) Cellular broadcast offers two principal advantages over SMS. First, a single broadcast message can reach each active cell phone within range of a given cellular tower, reducing the network capacity required for message delivery compared to
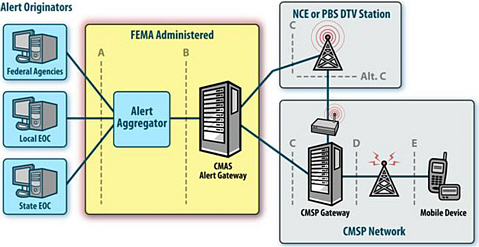
FIGURE 1.1 Commercial Mobile Alert System (CMAS) reference architecture.
NOTE: EOC, Emergency Operations Center; FEMA, Federal Emergency Management Agency; NCE, non-commercial educational; PBS, Public Broadcasting Service; DTV, digital television; CMSP, commercial mobile service provider.
that required for sending messages to each subscriber. Moreover, because cellular broadcast uses a data channel separate from that used for other messages and calls, it is unaffected by network congestion. This is important because cellular networks can become damaged or overloaded in the very crisis situations in which alerts are most needed. The second principal advantage of cellular broadcast over SMS is that, because messages can be localized to cellular towers, alerts can be geographically targeted, and targeted by actual subscriber location rather than by telephone area code or home service area. In the case of CMAS, this capability is to be used to localize messages by county or equivalent jurisdiction.6
The CMSAAC report7 referred to above recommends the use of cellular broadcast technology because of its immunity to network congestion. The same report also cautions about the potential for overloading the network if broadcast messages are allowed to include links (i.e., Web uniform resource locators [URLs]) to more detailed information. Including such links would, of course, be an obvious way to provide more information than can be contained in a CMAS message. However, this
approach was rejected by the CMSAAC out of concern that the practice could quickly lead to network overload.
The implications of this recommendation in light of what is known about the public response to alerts were discussed at the workshop. Several participants observed that it is well known that people often seek to confirm alerts before taking action. It seems likely that people receiving an alert on a cell phone would seek additional information by texting or placing telephone calls to family or friends, using social networks, browsing news Web sites, or searching online—activities that might end up using more capacity than would be needed if people followed a link to official information. It was further observed that the contrast might be even starker if the official information were especially designed to spare network capacity, such as through little or no use of images and other multimedia content. The cumulative effect on network capacity depends on multiple factors, including the relative likelihood of people’s using the network either to download official supplemental information or to seek additional information independently, and the respective network capacity consumed by each activity.
The CMAS program is envisioned by DHS and CMSAAC to be rolled out in flexible iterations, allowing for fuller testing of the system and also for the incorporation of new technologies or other enhancements. The initial phase will use English only, potentially creating challenges for those with limited proficiency in the English language. The sending of messages in non-English languages is being evaluated by DHS’s Science and Technology Directorate and CMSAAC for future iterations of CMAS.
RESEARCH ON EFFECTIVE ALERTS AND WARNINGS AND IMPLICATIONS OF THE RESEARCH FOR CMAS
Conceptually, alerts and warnings are generally viewed as distinct.8 Alerts are designed to indicate that something significant has happened or may happen. Warnings, which typically follow alerts, provide more detailed information, indicating who is at risk, where the risk resides, who is sending the warning message, and what protective actions need to be taken. The distinction is also useful because some technologies are better suited for the delivery of alerts (e.g., sirens or CMAS) whereas others (e.g., broadcast radio and television) are better able to deliver the more detailed messages needed to provide warnings. However, from the standpoint of an individual receiving a message, the distinction may not always be apparent or even relevant.
The Warning Process
People receive alerts and warnings about emergencies in a variety of ways, including print and electronic media and face-to-face communication. Each of these channels of communication has distinct characteristics—such as the rate and precision of dissemination, penetration into normal activities, specificity and distortion, and feedback—that dictate how effective they will be in particular circumstances or in reaching particular segments of the population.
Sirens, for example, provide a very limited amount of information but can be effective at getting people’s attention and have broad reach, notably to people who are outdoors or who otherwise do not have access to broadcast media or telephones. Weather radios provide much more detailed information than sirens can, for example, but the message delivery depends both on people’s owning specialized equipment and on that equipment’s being switched on. Citizens often relay information received on their own alert systems, which frequently leads to a distortion of the initial message. Face-to-face communication does have the advantage, however, of allowing the sender (e.g., a neighbor, coworker, or friend) to verify immediately that the message was received.
Public officials often use multiple outlets to ensure wide dissemination of messages. One reason for doing so relates to the different characteristics of the different communication channels. For example, because weather forecasts allow alerts and warnings to be issued days in advance, many information outlets, including print media, are useful for carrying messages about hurricanes or winter storms. By contrast, tornado warnings are very time-sensitive, and so sirens and other immediate alerting systems are required for these hazards. Not everyone has access to a particular single information source; for example, not everyone happens to be watching television when alerting messages are shown, and not everyone can hear sirens. Finally, people have individual preferences about how they want to receive information.
A model for an alert and warning system includes event detection, message dissemination (alerts and warnings), message receipt, and response. (Box 1.1 focuses on the last two of these elements—message receipt and public response.9) This model takes into account a number of factors associated with the alert or warning, including the source, access to and preferences about communications channels, the message, sender and receiver characteristics, and social and environmental cues, each of which affects how people receive, process, and act on the information.
|
BOX 1.1 The Warning Process: Message Receipt and Response by the Public Below is a list of steps that the affected population takes during a crisis or emergency following the receipt of an alert and/or warning message.
SOURCE: Reprinted with permission from Joseph Trainer. 2010. Myths and Misconceptions Surrounding People, Alerts, and Warnings. Presentation at Workshop on Public Response to Alerts and Warnings on Mobile Devices, Washington, DC, April 13; based on earlier work in D. Mileti and J. Sorensen, Communication of Emergency Public Warnings, Oak Ridge National Laboratory, ORNL-6609, 1990. |
Consider, for example, the process of delivering tsunami warnings: (1) a warning center detects an earthquake with the potential to generate a tsunami; (2) the warning center transmits this information to a variety of receivers, including government agencies and the media; (3) some, but not all, of these entities receive the message; and (4) of those that receive the message, not all transmit it to members of the public. Ultimately, some citizens will receive the message from multiple sources, but some will not receive the message at all—and only some recipients of the message will take prompt action. Flash floods exemplify events with such rapid onset that there may not be time for an official warning message to be formulated and sent. In such cases, it may be individuals in a community who successfully deliver timely messages and prompt appropriate action.
People interact and make decisions during various points in the warning process. They must be exposed to the message, comprehend the message, and then make a decision about what protective action to take. People’s decisions about protective action are often influenced by
situational factors—for example, do they have the appropriate supplies for sheltering in place or evacuating? However, most often people’s first action is to search for additional information to confirm the alert or warning. In such situations, people also consider social cues such as whether their neighbors are evacuating or whether local businesses are closing, and environmental cues such as whether they can see evidence of the reported hazard. They may also turn to other warning sources such as radio, print, or online information for confirmation.
The source of an alert or warning has a marked influence on people’s perception of its validity and thus on their decisions regarding what protective action, if any, they will take. If the information source is not identified in the message, the message is unlikely to be deemed as trustworthy. Several factors affect the public’s view of trustworthiness—for example, does the source have appropriate expertise and does the source have a protective responsibility? Therefore, it is important to recognize that the public will rely on different information sources in different types of emergency situations. For example, in an incident involving water-supply contamination, the public may respond most effectively to warnings from the water utility. Similarly, a weather alert issued by the National Weather Service is generally viewed by the public as having a high degree of credibility. In other situations, such as those for less familiar hazards (e.g., water contamination), the responsible party may not be the most trusted source, and the public will rely chiefly on local and state government information sources.
Effective Warning Messages
For warnings, there is a sizable body of social science research10 on what constitutes effective warning messages, which include the essential elements listed in Box 1.2.11 Other relevant information in addition to the essential elements includes the official actions that have been taken or are in progress, sources of official assistance, and sources for further official information.
In contrast, much less is known about effective content for alerts because traditional alert technologies—such as sirens and weather radio
|
10 |
The extensive “Annotated Bibliography for Public Risk Communication on Warnings for Public Protective Actions Response and Public Education” was compiled by Dennis Mileti, Rachel Bandy, Linda B. Bourque, Aaron Johnson, Megumi Kano, Lori Peck, Jeannette Sutton, and Michele Wood and is available at www.colorado.edu/hazards/publications/informer/infrmr2/pubhazbibann.pdf. |
|
11 |
Much of this section, including the information in Box 1.2, draws on the work of Dennis Mileti and his colleagues, which was provided to committee members as background information leading up to the workshop. |
|
BOX 1.2 Essential Elements of Effective Warnings For warnings, there is a sizable body of social science research on what constitutes effective warning messages. These key elements are listed below. The message should be—
The message should contain the following information:
The message should be confirmed as follows:
SOURCE: Drawn from the work of Dennis Mileti and colleagues provided to committee members as background information prior to the workshop. |
alerts—are only able to convey a very small amount of information. Such alerts require significant public education prior to a hazardous event so that populations at risk can translate tonal alerts to protective actions. Some recent alerting systems, such as the SMS text messages being provided today by many local jurisdictions, are able to provide added content, but because they are new and subscribed to by only a limited subset of the population, there has been relatively little experience with their use in disasters and thus fairly little is actually known about how to formulate effective messages.
As a result, past research and lessons learned are not fully translatable to the question of what would constitute effective content for CMAS alerts,
because CMAS messages will contain more information than conventional alerts provide but much less information than conventional warnings offer. Moreover, CMAS raises novel issues such as the potential advantages as well as drawbacks in providing links (URLs) to associated warnings and other information. Chapter 6 discusses these issues in more detail.
MISCONCEPTIONS ABOUT RESPONSES TO ALERTS AND WARNINGS
Classic examples of misconceptions about people’s behavior following disasters include the idea that there is looting, price gouging, panic, and role abandonment. Such common assumptions about people’s behavior are often at odds with what has been learned from post-disaster research about how people actually behave.
Following is a non-exhaustive sampling of misconceptions relevant to alerts and warnings:
-
Misconception: Alerts cause mass panic. As a result of this misconception, warnings are often delayed until they have become absolutely necessary, in order to avoid panic. In fact, research has shown that what sociologists call normalcy bias—that is, the underestimation of the possibility of the disaster occurring and of its possible effects—is a greater risk. For example, consider the last time that you heard a fire alarm sound—most likely people did not immediately evacuate the building in which the alarm rang.
-
Misconception: People who do not comply with alerts are either irrational or stupid. Research shows that alerting messages received by the public are just one type of input important to decision-making processes. Messages are not directives, and they are normally not immediately complied with. The warning process (Box 1.1) includes physically receiving the warning, understanding the warning, believing its credibility, confirming and personalizing it, and determining what action to take.
-
Misconception: Technical terms are intuitive. Terms that an emergency manager may believe to be intuitive may not be understood by a significant portion of the public. Consider, for example, the difference between a tornado warning (which means that there is imminent danger and one should take shelter immediately) and a tornado watch (which means that conditions for a tornado are favorable and one should prepare to take shelter).
-
Misconception: Response to alerts is binary; either compliance or non-compliance occurs. The reality is that people may take many different actions in response to alerts, actions that are shaped by the steps outlined in Box 1.1.
-
Misconception: Individual messages constitute the complete “system.” Each individual alert or warning should actually be thought of as contributing to a larger, integrated context. It is important to understand not only the meaning of a particular message but also how it relates to earlier alerts and warnings and to information available from other sources.
-
Misconception: Technology delivery systems are neutral or value-free. It is important to recognize that there are distinct characteristics and differences between population groups that own and use particular technologies and population groups that do not own and use those technologies. The characteristics and differences among groups include such factors as income and age.
-
Misconception: One-size-fits-all solutions. No single system will reach the entire population or be suited for all circumstances. Technology, language, type of hazard, and regional subculture are among the many factors that should be taken into consideration.
Note that the identification of the statements above as misconceptions does not mean that they never occur. For example, contrary to the common misconception, looting after disasters rarely happens; however, there are exceptions, such as the pervasive looting that took place after Hurricane Hugo severely damaged St. Croix in 1989. The exceptions are associated with special circumstances—in this case to extreme differences in economic and political status and the release of years of political and social tension following the disaster.
OBSERVATIONS OF WORKSHOP PARTICIPANTS
In the discussion following the panel presentations at the workshop, participants offered a number of observations about the role of CMAS in a national all-hazards warning system, including the following:
-
Alerts and warnings systems are sociotechnical systems that require a thorough understanding not only of the technology but also of the interactions among detection, dissemination, and public response.
-
CMAS will be only one of many sources of alerts and warnings and should be thought of as a new and useful component of what must be an integrated system.
-
Like other capabilities for delivering alerts and warnings, CMAS will have both advantages and limitations. CMAS will allow messages to be geographically targeted with some precision, and it will provide a specific message directly to the public without opportunities for distortion. It also has a potentially wide reach, given that many people keep wireless devices within 3 feet of them all the times—and will be especially
-
important for reaching households that do not have conventional landline telephone service. Among the limitations of CMAS are the brevity of the message content and the fact that there is no provision for receipt verification.
-
Localization of CMAS messages by county or equivalent jurisdiction might be too coarse-grained, especially in the case of large counties and highly localized events. Some tighter localization may be possible, but this would be constrained by the size of the regions potentially served by individual cellular towers and their overlapping coverage.12
-
The cellular networks on which CMAS will depend are susceptible to damage in certain types of disasters, and the message length of CMAS is limited. Thus it will be important to educate people to use older technologies such as broadcast radio and television in addition to mobile devices in order to obtain additional information if needed, or as primary sources of information if cellular networks are not available.
-
Further examination of the CMSAAC recommendation13 not to include URLs in CMAS messages is warranted. CMSAAC rightly cautions about the potential for network overload in emergencies. However, if a CMAS message does not point people to an authoritative source of additional information, it is possible that the network will be overloaded as people place calls, browse news Web sites, or search for information to confirm an alert or warning and obtain additional information. In particular, it is worth considering whether a link to a site carefully designed to minimize network traffic might cause less congestion than the information seeking and resulting demands on network capacity that would take place without such a link.













