Science and Technology to Counter Terrorism in Critical Areas
CYBERSECURITY IN ITS COMPLEXITY
Understanding Cybersecurity and Related Challenges
Srinivas Mukkamala opened his presentation by stating that cybersecurity issues appear to be simple, but are actually very complex. The vulnerabilities associated with many of our cybersystems arise whenever newer sub-systems are integrated with existing, outdated systems. This has become a serious problem particularly in protecting critical infrastructures in the United States. One example Mukkamala raised was that of the many computerized systems in hospitals. If these systems were compromised, patients’ health could be seriously threatened. Mukkamala and his colleagues concluded that Level I trauma centers are vulnerable, due to systems that have minimal or in some cases no security features.
Mukkamala then described the international online marketplace for exploits and personal information. There are individuals and illicit businesses whose business model is to sell the capability to exploit software vulnerabilities in other people’s computer systems and enable the purchaser to misuse the information or the system. There are websites where these exploits are marketed and sold among trusted users.
Similarly, personal and credit card information are bought and sold, enabling identity theft around the world. An identity is easy to steal, and such theft is very serious for those who are victimized. The information is often acquired illegally by malware that enables hackers to gain access to individuals’ computers or to databases of thousands or millions of people.
Unfortunately, antivirus software does not detect malware. It can look for anomalies and known exploits, but new malware can go undetected. Malware trees can be constructed showing the relationship among different types of malware and the methods they use. These can be useful in forensics on a cybersecurity event, but they fall short of attribution. In Mukkamala’s view, the largest problem in addressing cybersecurity is the lack of reliable attribution methods. As a result, those who seek to commit a crime or an act of terrorism via cyberspace can be reasonably sure that they will not be detected and quite confident that they will not be identified.
Similarly, insider threats are a serious problem because it is difficult to detect a breach of cybersecurity, and when it is detected, it is not easy to identify the culprit(s). In particular, privileged users, such as system administrators, can move through systems without tracking.
The Department of Homeland Security (DHS) in the United States has therefore recommended that every 72 hours all critical infrastructure systems should be scanned for unusual or nefarious activity. A key to success is cyber-threat intelligence, so timely sharing of information is essential.
Cybersecurity Challenges in India
B. J. Srinath spoke about cybersecurity concerns in India and the efforts taken by the government to regulate and address the problem. He stated that cybersecurity threats are global and require cooperation across nations. The government of India cooperates internationally, including conducting joint exercises with the United States Computer Emergency Readiness Team (US-CERT). Cyberthreats have increased in sophistication, both by criminals and by governments. Many countries are developing capabilities for cybersurveillance and cyberattack. Malware from these different sources is now targeting mobile devices in addition to networked computers. The government of India has been working through public-private partnerships to tackle some of the problems related to cybersecurity. Due to concerns regarding loss of reputation and the need to protect proprietary information, many commercial organizations do not report cybersecurity incidents.
Srinath concluded by stating that a large number of cyberattacks take the form of the hacking of websites to proliferate political views, often views that are violent or may incite violence.
R. Narasimha began the discussion by stating that according to press reports a significant number of financial cyberattacks are conducted in India, or that those who conduct the attacks are being trained in India. N. Balakrishnan replied that cyberthreats at Indian banks are treated as pollution. India is a source of a significant amount of spam and it also has a large number of botnets, which may be used in an attack, but India is not the source of attacks. A participant asked if there are efforts parallel to those in the life sciences to establish norms of behavior. Mukkamala noted that in some countries cyberattacks are not illegal and in others, such as Germany, selling exploits is legal. Another participant pointed out that purchasing such exploits is how companies like Microsoft discover and fix security problems in their own software. With regard to credit card fraud, India does not have any legal requirements to disclose or even report the number of credit cards compromised, for example. The only requirement is that the incident be reported to CERT. Cyberspace today suffers from underreg-
ulation rather than over regulation, added Srinath. Further, laws and regulations vary greatly across different countries, which makes tracking crime difficult.
Another participant noted that automated cybersecurity threats also exist. Balakrishnan stated that 20 percent of tweets are machine originated, which enables the amplification of a message or the spread of a potentially dangerous message. In India, the use of websites, social media, and other cyber means to recruit terrorists, incite terrorist acts, and even coordinate activities is a real concern.
Other issues were raised by workshop participants. One participant asked if it was possible for hackers to hack into air traffic control systems to bring down a plane. Srinath stated that he believed it was just a matter of time before these types of security breaches would occur. Although some such systems are air gapped (have no direct connectivity to other information systems), “an air gap is no air gap.” At some point the gaps are breached through error (unwitting file transfers) or deliberately.
Finally, Van Romero proposed a prioritization approach. A simple penetration does not constitute a significant compromise of valuable information or loss of control. Banks, like vegetable sellers, assume some loss. They protect the important parts and do not worry much about the rest. One has to factor in some threats and security breaches, but critical assets should be protected.
GLOBAL HEALTH SECURITY AND STRENGTHENING PUBLIC HEALTH INFRASTRUCTURES
The Anthrax Letters: Lessons for Leaders
David Franz began by noting that he would discuss the anthrax letters that were sent to politicians and prominent members of the media in October 2001, and his underlying approach is preserving the good of powerful science in a dangerous world.
Franz first provided a very brief overview of biology in the 21st century and a short history of safety and security. He then discussed the anthrax letters, but brought in two other cases that he considers insider issues, although they are not as well known as the anthrax letters. Franz then turned to the U.S. government response and the implications of the government’s response for the life sciences enterprise. Finally, he briefly discussed what leaders can learn from all of this and how we can find a balance in the way we respond to these types of incidents. Franz explicitly did not discuss the technical, forensic, or other issues related to the anthrax letters. Franz quoted from the U.S. National Academy of Sciences’ (NAS) report that examined technical issues regarding the anthrax letters and the investigation and forensics that followed.1 One relates directly to the idea of the insider threat. It says, “An unavoidable observation from the
________________________
1National Academy of Sciences. Review of the Scientific Approaches Used During the FBI’s Investigation of the 2001 Anthrax Letters. Washington, D.C.: The National Academies Press, 2011.
2001 Bacillus anthracis mailings is that the best subject matter experts in a given area might also be viewed as suspects.”2 The report’s highest-level summary conclusion was, “It is not possible to reach a definitive conclusion about the origins of the B. anthracis in the mailings based on the available scientific evidence alone.”3 Franz recommended the report to anyone interested in the technical, law enforcement, and forensic response.
Where does bioterrorism or the insider threat fit into the whole spectrum of terrorism problems addressed at this workshop? The anthrax letters killed five people.4 Atomic bombs dropped on Japan during World War II killed an estimated 250,000 people.5 Experts believe that about 10,000,000 to several million people died worldwide in the 1918 flu pandemic.6 Another data point on a potential scale is the 1965 New York City subway trial in which researchers released a simulant of anthrax.7 They estimated that in one day approximately a million people could be infected with anthrax spores.8 Fortunately, there have not been any intentional, high-impact events. In thinking through how to scope the bioterrorism prospect, Franz referred to John Vitko, who led the biosecurity program at DHS in the science and technology (S&T) directorate. Vitko coined what he called a “Vitko unit”: If an event kills 10,000 people or costs $1 million, that is one Vitko unit, and any event above that unit, he believed, should be addressed by DHS S&T (see Figure 4-1). This is just one example of how one person tried to deal with a very complex problem with a lot of unknowns.
Franz turned very briefly to 21st century biology, which has undergone a revolution in the last 20 years. Genes from different organisms can be spliced together to make new organisms and new organisms can be designed from scratch. The rate at which base pairs can be sequenced is rising faster than the increase in microprocessor speed resulting from the increase in the number of
________________________
2Ibid, p. xvii.
3Ibid, pp. 4, 118.
4Ibid, p. 44.
5Bernstein, B. J. “The Atomic Bombings Reconsidered.” Foreign Affairs, Jan./Feb. 1995. Available at: http://www.foreignaffairs.com/articles/50569/barton-j-bernstein/the-atomic-bombings-reconsideredhttp://www.foreignaffairs.com/articles/50569/barton-j-bernstein/the-atomic-bombings-reconsidered; accessed September 22, 2014.
6Taubenberger, Jeffrey K. and David M. Morens. “1918 Influenza: the Mother of all Pandemics.” Emerging Infectious Diseases. Vol. 12, No. 1. January 2006. Available at: http://wwwnc.cdc.gov/eid/article/12/1/pdfs/05-0979.pdf; accessed October 20, 2014.
7These simulations were conducted when the United States had an offensive biological warfare program until 1969, when it was stopped by President Richard Nixon.
8Gerstein, D. Bioterror in the 21st Century: Emerging Threats in a New Global Environment. Annapolis, MD: Naval Institute Press, 2009, p. 68. Available at: http://books.google.com/books?id=JbJOuG4Q3_IC&pg=PA1&source=gbs_toc_r&cad=3#v=onepage&q=1966%20New%20York%20subway&f=false; accessed Sept. 22, 2014.
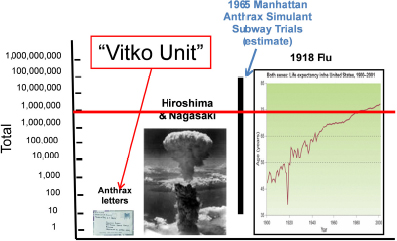
FIGURE 4-1 John Vitko coined what he called a “Vitko unit.” If an event kills 10,000 people or costs $1 million, that is one Vitko unit, and any event above that unit should be addressed by the Department of Homeland Security, Science and Technology Directorate. NOTE: The 1918 flu graph contained within this figure is set to the height of the “y” axis of the larger figure. SOURCE: Franz, 2014.
transistors that can be fit on a semiconductor chip (the Carlson Curve rises faster than Moore’s Law). This is a revolution, and it is not only occurring in India or in the United States. It is global. Franz stated that proliferation of technologies, proliferation of knowledge in biology, is essentially over. Proliferation of tacit knowledge, how one cooks the recipes, may not be over. The proliferation of this knowledge is a global issue.
Franz said that when he was on active duty as late as 1998, the focus was on safety, and there was little talk of biological security. In his command brief in 1997, Franz said his three top priorities, in addition to providing medical countermeasures for the war fighter, were safety, safety, and safety because people were working in biosafety level (BSL) four labs with hemorrhagic fever viruses. One needle stick or one bone fragment through a glove could be almost certain death. He wanted to get as close to a zero-defects operation as possible. Much of those safety practices came from the former offensive program in the United States. Arnold G. Wedum, a physician at Fort Detrick in the 1950s and 1960s, developed what eventually became the first section of the Centers for Disease Control and Prevention (CDC) guidelines. After the turn of the 21st century, a series of events (September 11, 2001 [9/11] and the anthrax letters, which Franz calls 10/4), caused the science community, in this case represented by NAS, to start thinking about becoming involved in these issues.
Right before these incidents, there was a surprise in biology in Australia with an ectromelia virus, a mousepox virus. Then there was de novo synthesis of
polio; this was the second time it was done by E. Wimmer.9 This was followed by a surprise in something learned about orthopox viruses called a spice gene that was a virulence factor. All of these discoveries, along with the biotech revolution, were accompanied by an incredible budget increase in the United States for biosecurity, which went from $137 million in 1997, most of it allocated to the Department of Defense (DOD), to $6 billion in 2002.
NAS assessed this situation and formed a committee chaired by Gerry Fink from Massachusetts Institute of Technology. Franz served on that committee, which wrote a report titled Biotechnology in the Age of Terrorism: Confronting the Dual Use Dilemma.10 The committee concluded that life science research underpins so many elements that are critical for health, food, energy, security, and for all of us. However, good science can be put to bad uses. It may be unlikely; maybe it will not occur very often, but these are very powerful tools that could potentially be put to bad uses. The report recommends education and awareness as the key ways to address this potential threat. The report also recommended that the U.S. government form a high-level committee in the Department of Health and Human Services—not in a security agency—that would bring together security professionals and health professionals for the first time. This was called the National Science Advisory Board for Biosecurity (NSABB).
When Franz awoke on the morning of August 2, 2008, a picture of his previous laboratory and Bruce Ivins, one of the scientists in that laboratory, was being shown in the media. Ivins was a Federal Bureau of Investigation (FBI) suspect in the anthrax letters case, and he had just committed suicide. Franz recounted that he was giving a talk shortly thereafter, and he had first made a slide that said “the insider threat is more serious than I thought,” but he quickly changed that slide to read, “the insider threat is more difficult than I thought.” The insider threat is a really tough challenge. As Joshua Lederberg said about biological warfare in general, there is no technical solution to this problem. It will require an ethical or a moral solution.11 Then he paused and asked, would an ethical or moral solution appeal to a sociopath? Franz believes that encapsulates some of these issues that we are dealing with not only in regard to biology, but also in other fields as well.
Within 4 days of Ivins’ death, Congress responded. Two congressmen wrote a letter to President George W. Bush stating that if the allegations are true, the FBI has identified a serious weakness in security at one of the nation’s prem-
________________________
9Molla, A., et al. “Cell-Free, de novo Synthesis of Poliovirus.” Available at: http://www.ncbi.nlm.nih.gov/pubmed/1661029; accessed October 20, 2014.
10National Research Council. Committee on Research Standards and Practices to Prevent the Destructive Application of Biotechnology. Biotechnology Research in an Age of Terrorism. Washington, D.C.: The National Academies Press, 2004.
11Preston R. “Annals of Warfare: The Bioweaponeers.” The New Yorker, March 9, 1998, pp. 52–65. Available at: http://www.newyorker.com/magazine/1998/03/09/the-bioweaponeers; accessed September 26, 2014.
ier laboratories for the study of some of the most deadly pathogens in the world. Their allegations also raised equally troubling security concerns about thousands of other scientists and technicians who work with select agents in hundreds of labs across our country. The same year the Graham-Talent Commission wrote a report called World at Risk.12 Suddenly biology was elevated to a significant risk, but the commission also said the United States should be less concerned that terrorists will become biologists and far more concerned that biologists will become terrorists. This report is referring to experts like those gathered at the workshop. Shortly thereafter, DOD implemented a new regulation called AR50-1 that has been used in draft form since 2004, called Biological Surety.13 Those who have worked in nuclear programs know nuclear surety very well. Franz had worked in a chemical program at the U.S. Army Edgewood Chemical Biological Center where there was a chemical surety program. Biology, however, had never had a surety program of this kind. The surety program includes not only safety, which biologists in a lab like Franz’s know and love and appreciate and support, but also security. Biologists do not mind fences around the labs, or cameras in their labs. That really does not bother them. An agent accountability program was also introduced and it quickly fell apart because it is very hard to know how to account for replicating agents that are hard to measure. Therefore, that program was ended. It is easier to account for chemicals and radiological and nuclear materials than for some biological agents.
There is also a personnel reliability program that is meant to address questions such as: Are scientists mentally alert, emotionally stable, trustworthy, and so on? Franz highlighted a couple of lines from the AR50-1 that hint at what the certifying official should look for in an employee: inappropriate attitude, negligence, delinquency, arrogance, flippancy, and so on. Someone sent Franz a blog written about the time this list came out and the person said, “this reminds me of many scientists I know.” Really smart people are often just a tiny bit weird and quirky, and often irritating. Again, this describes experts like us. Interestingly, DOD did implement the program, which was signed on July 28, 2008. Bruce Ivins died at his own hands on July 29, 2008, although the program had been in place in the lab at which he worked for some time.
In addition to the issues associated with Ivins and the anthrax letters, another recent set of events has shaped thinking and practice regarding biosecurity in the United States.
________________________
12Graham, B., and Talent J. World at Risk: The Report of the Commission on the Prevention of WMD Proliferation and Terrorism. New York: Random House, 2008.
13Department of the Army. Army Regulation 50-1. “Nuclear and Chemical Weapons and Materiel, Biological Surety.” Washington, D.C., July 8, 2008. Available at: http://fas.org/programs/bio/resource/documents/biological_surety_08.pdf; accessed September 22, 2014.
The United States National Institutes of Health National Institute for Allergy and Infectious Diseases (NIH NIAID) funded two scientists to take the H5N1 virus and try to make it transmissible in mammals. There has been a pandemic of H1N1, which transmits very easily between humans, but it is not too virulent and it does not kill many people. H5N1 does not transmit easily between humans. It transmits from a chicken to a human, or a duck to a human, or a wild bird to a human, and perhaps 60 percent of the cases are lethal. NIH therefore asked two scientists, one in Rotterdam and one at the University of Wisconsin (Fouchier and Kawaoka, respectively), to take the H5N1, mutate it, and produce a virus that was transmissible by air in ferrets, which is the best flu animal model. The researchers succeeded. They did exactly what they were asked to do, but one of them, Ron Fouchier, started making statements.14
First, in Malta, he said that this is very bad news, and then he said this flu is as efficiently transmitted as seasonal flu, and then in an interview he said that it is probably one of the most dangerous viruses one can make. Then both Fouchier and Kawaoka submitted their papers to Science and Nature. Those journals brought the articles to NSABB, which read them and determined that there were elements of the papers that should not be published, such as the gene sequences and the approximately five to seven mutations. NSABB also recommended that the international community be involved. The U.S. government and Tony Fauci, director of NIAID, led this effort. A meeting was organized with the World Health Organization (WHO) that brought representatives of 13 or 14 other countries to discuss this issue. At that meeting, Fouchier presented slightly different data, and the WHO meeting concluded with a statement that the data should be published. Then NSABB examined the issue again in March 2012, and voted unanimously that Yoshi Kawaoka’s paper should be published, and voted 12 to 7 that Fouchier’s should be published, and they were subsequently published.15
Franz does not consider this episode a technical surprise. If anything, he considers it an ethical lapse on the part of a scientist, a legitimate scientist, who was not trying to do harm, but some of his statements caused issues that were uncomfortable for a number of people. Shortly thereafter, another new guideline was released by NIH, which must be followed by those who wish to receive funding from NIH: the framework for guiding the U.S. Department of Health and Human Services funding decisions regarding highly pathogenic H5N1
________________________
14Fouchier, R., et al. “Airborne Transmission of Influenza A/H5N1 Virus Between Ferrets.” Science, June 22, 2012, vol. 336, no. 6088, pp. 1534-1541. doi: 10.1126/science. 1213362. Available at: http://www.sciencemag.org/content/336/6088/1534.full; accessed September 21, 2014. See also Harmon, K. “What Will the Next Influenza Pandemic Look Like?” Scientific American, September 19, 2011. Available at: http://www.scientificamerican.com/article/next-influenza-pandemic/; accessed September 21, 2014.
15National Science Advisory Board for Biosecurity. Findings and Recommendations, March 29-30, 2012. Available at: http://osp.od.nih.gov/sites/default/files/resources/03302012_NSABB_Recommendations.pdf; accessed September 22, 2014.
“gain-of-function research.”16 This refers to research that changes a virus’s virulence, for example. In this set of guidelines, two issues were addressed. First, one should not do anything that nature is not going to do in the future. But discerning what nature will do is difficult. Second, one has to assure that biosecurity risks can be sufficiently mitigated and managed. Franz stated that he did not know how to do that either. He knows how to mitigate and manage biosafety risks, but it is not clear how to mitigate and manage biosecurity risks. The guidelines were published in February 2013.17
There are three individuals whose cases have led to biosecurity measures in the United States. The first one was Larry Wayne Harris, who tried to acquire plague bacillus in 1996 from the American Type Culture Collection.18 This is a center in Virginia near Washington, D.C., where isolates of many bacteria and viruses are kept for scientists to use. He tried to acquire it illicitly by forging stationery and stating that he had a clinical laboratory. This incident led to the select agent rule that states that if two laboratories want to exchange a select agent, both laboratories must be certified by the CDC. Next, after the anthrax letters, army regulations as well as the USA Patriot Act were adopted.19 The USA Patriot Act changed the select agent rule by registering scientists who work with select agents, not labs. Finally, after the H5N1 issues, there is a new policy or regulation on oversight of life sciences dual-use research. Three individuals who did something either illegal or possibly unethical had a significant impact on the regulatory scheme that scientists are now living with in the life sciences enterprise.
Franz provided additional examples of how hard this problem is to address. For the years 2009 and 2010, Gigi Kwik Gronvall and her colleagues at the University of Pittsburgh Medical Center identified naturally occurring outbreaks of select agents.20 They are everywhere, obliterating her map. Another very specific example is of Supaporn Wacharapluesadee, a researcher from
________________________
16National Institutes of Health. “A Framework for Guiding U.S. Department of Health and Human Services Funding Decisions about Research Proposals with the Potential for Generating Highly Pathogenic Avian Influenza H5N1 Viruses that are Transmissible among Mammals by Respiratory Droplets.” February 21, 2013, p. 2. Available at: http://osp.od.nih.gov/sites/default/files/funding-hpai-h5n1.pdf; accessed September 18, 2014.
17National Institutes of Health. “A Framework for Guiding U.S. Department of Health and Human Services Funding Decisions,” February 21, 2013.
18See, for example, Revkin, A. “Arrests Reveal Threat of Biological Weapons.” New York Times, February 21, 1998. Available at http://www.nytimes.com/1998/02/21/us/arrests-reveal-threat-of-biological-weapons.html; accessed September 18, 2014.
19U.S. Congress. H.R. 3162. Patriot Act. Available at: http://www.gpo.gov/fdsys/pkg/BILLS-107hr3162enr/pdf/BILLS-107hr3162enr.pdf; accessed October 24, 2014.
20Center for Biosecurity. Everywhere You Look: Select Agent Pathogens.Countries in which naturally occurring disease outbreaks caused by select agent pathogens were observed, January 1, 2009 through October 31, 2010. Available at http://www.upmchealthsecurity.org/diseasemap/index.html; accessed September 21, 2014.
Chulalongkorn University in Bangkok.21 She studies an emerging disease, the Nipah virus, which killed many pigs and some people in Malaysia. All she does is lay plastic tablecloths under fruit bat roosts, collects the bat droppings, and isolates the virus from the bats fairly easily. The ease with which she and others can conduct this research demonstrates that it is not possible to lock up the bugs.
Franz’s concern is the over-regulation of the life sciences. A balance between research and security has to be found. Regulations are needed, but there has to be a balance with the conduct of science. Franz is concerned that overregulation will affect our ability to provide health care, food, agriculture, and energy. It will affect the economy, the ability to compete globally, and even national security. It may take 5 to 10 years to know the full effect of overregulation on the life sciences and then maybe to rebuild and turn the trend around.
What can we do? Franz asked. We cannot lock up the bugs. We cannot control equipment and technology. We have tried on an international scale to do this with mechanisms like the Australia list. We cannot control knowledge. We cannot isolate scientists. We cannot know all the biohackers that might be out there. What we can do is to build awareness and understanding. We have tried that, and Franz thinks it has been pretty successful, even globally. We can seek to communicate and build trust in laboratories and globally, and Franz does not think we have tried hard enough in that area. We can use good to counter harm, technologies to produce medical countermeasures and other discoveries; we have been semisuccessful there. We can apply leadership principles in labs. In the United States, we have not tried hard enough to do this. We can impact the culture of laboratories, especially our biological security laboratories. With regard to the way ahead, the life sciences community needs to take an active role, to take responsibility and not just sit back. There needs to be transparency in science. Scientists need to communicate with, educate, and recruit young scientists. They need to demonstrate a culture of responsibility and build public trust, build communities of trust, and work with regulators. We need some regulation, but we need to consider the real risks, consider the real safety or security that we gain from a given regulation and think this through very carefully, and consider the entire cost because there are always tangible and intangible costs when implementing regulations. One of Franz’s philosophies when he was commanding the U.S. Army Medical Research Institute for Infectious Diseases was to seek solutions that limit the frustration of scientists, because 99.9 percent of the scientists just want to work hard and do a good job. If one overlays or hampers the ability of scientists to do their work just because there might be an outlier within that group, the approach may be out of balance.
________________________
21Wacharapluesadee, Supaporn, et al. “Bat Nipah Virus, Thailand.” Emerging Infectious Diseases. Vol. 12, No. 1, January 2006. Available at: http://wwwnc.cdc.gov/eid/article/11/12/pdfs/05-0613.pdf; accessed October 20, 2014.
With regard to communities of trust, Kendall Hoyt at Dartmouth College, who wrote a book called Long Shot: Vaccines for National Defense,22 examined why the U.S. government was able to produce defense vaccines in the 1940s, 1950s, and 1960s, and why we just cannot seem to deliver them to soldiers or citizens today, although technologies are better and regulatory schemes are a little bit higher. She reached two conclusions. One, in those days, there was a champion who would take that antigen all the way from its technological base through animal testing, and stick with it and fight for that antigen as he or she developed a vaccine. The other conclusion was the existence of communities of trust. There were individuals that came out of World War II who worked at Walter Reed Army Institute of Research. Maurice Hilleman, for example, who was on many NAS committees, went to work at Merck. Someone else went to Pfizer, and Maurice would call his friend at Pfizer and ask: What was that cell line we used at RARE when we were making that vaccine? The person at Pfizer would actually tell him. Now there are rows of lawyers standing between the scientists. Those communities of trust, Hoyt found, were critically important in making progress. A high-trust organization increased value, accelerated growth, enhanced innovation, improved collaboration, strengthened partnership, improved execution, and heightened loyalty. Low-trust organizations have redundancy, bureaucracy, politics, disengagement, turnover, and fraud. As leaders in our organizations, Franz said, we can move our organizations to become high-trust organizations. Enlightened leaders who lead with science, talk about quality, and emphasize safety, vision, education, and so on, can make a difference in the cultures of organizations. This is hard to do, and it does not scale easily. It is much easier to put a fence around something than to find a leader who does a great job.
Of the many risks and threats, Franz is actually more concerned about chronic diseases, communicable diseases, and emerging diseases, but we may also have lab accidents. We may have intentional misuse of information. We may have bioterrorism. We may even have biowarfare by nation-states. However, Franz said, our approach needs to be balanced. We cannot just regulate these potential threats away. We need enlightened leadership, a culture of personal and corporate responsibility, and leaders who are willing to take responsibility to develop thoughtful regulation and safe and sustainable practices, and maintain freedom for scientists to explore so that we can make progress for all people in the life sciences.
Franz concluded that there is only one way to entirely eliminate risk: that is to turn out the lights, unplug the freezers, board up the doors, send everyone home, and let weeds grow in the parking lot of laboratories. There would be no more insider risks; however, there would also be no more science. As a result, we cannot afford to have zero risk. It is just not an option. It is a dangerous
________________________
22Hoyt, K. Long Shot. Vaccines for National Defense. Cambridge, MA: Harvard University Press, 2012.
world and we must work through these issues together. It is very important to work together globally because what happens in one country impacts another.23
Global Health Security in India: India’s Experience with H1N1
J. K. Bansal began by stating that in the last decade, several pathogens have emerged, causing infectious diseases such as Chikungunya, dengue fever, severe acute respiratory syndrome, Japanese encephalitis, Congo-Crimean hemorrhagic fever, H1N1, and H5N1. In addition, there are reports that terrorist organizations are attempting to acquire biological agents such as anthrax, plague, and smallpox; possible sources of these agents could be a microbiology lab, a veterinary lab, or a facility associated with the biotech industry. However, as of today, the emphasis is on biological terrorism because biological weapons are relatively cheap and easy to produce, and a very small amount that can cause havoc. Terrorists could also use a genetically modified organism, which is difficult to detect. There are no vaccines, drugs, or antibiotics available to treat some of these diseases. Some of these agents, specifically anthrax, can be manufactured in a very crude, improvised laboratory and can be disseminated relatively easily.
Therefore, it is important to have biosafety measures and, specifically, biosecurity measures. The National Disaster Management Authority (NDMA) of the government of India, where Bansal is a member of the leadership, is deeply concerned about bioterrorism and has formulated national guidelines for biological disaster management, including bioterrorism. These guidelines cover biosafety, biosecurity, management of epidemics and pandemics, countermeasures for bioterrorism, management of animal disease, and agroterrorism. On April 21 and 22, 2008, NDMA organized a conference entitled, “A National Workshop on Pandemic Preparedness: Beyond Health.” The information exchanged at the conference and captured in the proceedings proved to be helpful in preparing business contingency plans in nonhealth sectors with topics including:
- Supply of food and essential commodities
- Water resources
- Law and order
- Transportation – surface transport and shipping
- Transportation – civil aviation
- Transportation – railways
- Information and communication
- Power
____________________________
23Franz, D. “The Dual Use Dilemma: Crying Out for Leadership.” Saint Louis University Journal of Health and Law Policy, Vol. 7, Issue 1, 2013. Available at: http://www.slu.edu/Documents/law/SLUJHP/Archives/Vol7-1/Franz_Article.pdf; accessed September 22, 2014.
- Commerce and industry
- Rural sector needs
- Finance
- Defense
Further, a steering group on global health security held a meeting in June 2013 at Chatham House.24 As a member of that group, Bansal presented on India’s multisectoral approach, and his paper was subsequently added to the document of the meeting. Participants agreed on the need for a whole-of-government approach, similar to what NDMA planning in India stresses: an approach that includes not only the public health sector and law enforcement, but also water, transportation, telecommunications, and energy sectors. The participants agreed on a common framework for global health security, which included prevention, detection, and rapid response to infectious diseases of international concern. Specifically, the steering group recommended global health security first by focusing on prevention by promoting biosafety and biosecurity. Measures suggested include the control of infectious disease outbreaks and the prevention of emergence of drug-resistant microorganisms. The second set of recommendations focused on early detection through biosurveillance and by developing laboratories capable of accurately detecting a biological agent and reporting biological incidents or biothreats of international concern. The third set of recommendations focused on rapid response by developing mechanisms for multisector response.
As an overview of global health security in India, Bansal listed the primary organizations and agencies involved: NDMA, National Crisis Management Group, Ministry of Health and Family Welfare, State and District Health Department, Primary Health Care System, government and private medical institutions, research institutes such as the Indian Council of Medical research, Defense Research Development Organization, and agencies related to the health care sectors such as those involved with water supply, hygiene, and international organizations.
For early detection of an infectious disease, India has initiated a project called the Integrated Disease Surveillance Program (IDSP). IDSP organizes structures at the national level, state and district levels.
If a dangerous pathogen emerges, it is immediately reported for a prompt response. Weekly information is provided by program offices of district surveillance units and on to regional surveillance units and then to state surveillance
________________________
24The Chatham House Steering Group held a meeting in June 2013 on Global Health Security, and recommended the prevention of avoidable epidemics by promoting national biosafety and biosecurity systems, detecting threats early through biosurveillance, rapid response, and establishing a multi-sectoral response capacity to effectively counter biological threats of international concern. Global health security risks are considered multinational pandemics, which require international cooperation such as on global disease surveillance, airport quarantines, and other measures.
units. This information is obtained from the peripheral health systems, for example, a primary health care center, a district hospital, or a private practitioner. With regard to biosurveillance, the Indian government has worked with the BSL-4 laboratory in Pune and there have been proposals for a BSL-3 laboratory as well. Some of the biological agents, such as anthrax, are especially dangerous because in the powder form it can be sustained for a longer period and disseminated through a central air conditioning system reaching any part of a building. Therefore, sensitive buildings, such as airports, hospitals, and railway stations, need to be protected by lighting, grill work, intrusion alarms, and increased surveillance.
During the Commonwealth Games held in India in 2010, a foolproof security system for chemical, biological, radiological, and nuclear (CBRN) threats was put in place, Bansal said. For biological agents, they have initiated a biological standard for detector systems that can sense a biological agent at a distance of up to 5 kilometers. The integrated biological disease detection system is very useful for field purposes and can detect and respond to incidents. Planning needs to be done before an event, during an event, and after an event. Key elements of planning include intelligence before an event; detection, protection, and decontamination at the time of an incident; and further investigation after an incident. For response to a suspected bioterrorist attack, individuals or victims would be hospitalized first and then a message would be sent to the director of emergency response, who in turn would inform the Ministry of Health and Family Welfare, and sends a rapid response team for investigation, containment, and other tasks. The Ministry of Health and Family Welfare then would request the involvement of the Ministry of Defense. In the event of an incident, the Ministry of Defense’s medical services would reinforce the response teams, and military hospitals would be ordered to admit patients.
International cooperation is also very important. In the 21st century, disease outbreaks in one country can be disseminated to other countries through rapid transportation. Due to incubation periods, which for anthrax may be 4 to 6 weeks, an infected person may not feel or appear sick for some time; however, during that period, an individual may infect others. Therefore, it is very important to screen passengers coming from a country where a particular disease is prevalent. Similarly, if a particular country has a high prevalence of an infectious disease, screening prior to passengers departing can prevent further infections. For example, more than 120,000 migrant workers from India went to Saudi Arabia. India deploys trained medical teams at the airport to screen returning passengers for those with symptoms of Middle East respiratory syndrome coronavirus.
International cooperation is essential for these and a variety of initiatives. Bansal offered several suggestions, beginning with broader adoption of the 2005 International Health Regulations. He then proposed a web-based forum where the scientists and experts could interact with each other to formulate strategies on how to combat or counter biothreats. He suggested a stockpile of various antibiotics and vaccines at regional levels. In terms of research, Bansal under-
scored the need for joint cooperation on the most dangerous diseases. Joint exercises, he said, should be conducted to develop communication systems and on-the-ground coordination between countries prior to an incident because such cooperation in the midst of a response is not possible. Pooling medical expertise and resources and exchanging ideas and best practices can also improve the management of pandemics and other types of incidents.
India has taken the initiative in advancing international collaboration. There are cooperative programs with CDC in Atlanta, including one on the detection and prevention of emerging pathogens. In May 2013, a joint conference on the emergence and reemergence of pathogens and biorisk management was organized by NDMA in collaboration with CDC.25 Decision makers at the highest levels also participated, because the conclusions and recommendations of any meeting or conference must be implemented to be effective. In 2007, India participated in an Interpol conference on biosafety and biosecurity.26 In February 2012, India hosted a meeting of the South Asian Forum for Health Research, where delegates participated from a variety of countries, including Bangladesh, Bhutan, Malta, Nepal, Pakistan, and Thailand.27 Meeting participants deliberated transmission of a variety of infections and implementation of countermeasures. NDMA also organized a meeting with the World Society for the Protection of Animals, during which animal diseases and zoonotic diseases were discussed in detail.
Bansal then turned to India’s experience with managing H1N1. NDMA took proactive measures, applying lessons learned from the avian flu outbreak in 1918, which killed one-third of the population.28 As early as April 2009, the
________________________
25A two-day conference was held exclusively on “Emerging and Re-emerging Pathogens & Bio–risk Management” on May 7 and 8, 2013, in Delhi to develop best practices to deal with effective prevention and mitigation of biothreats. Renowned experts in biodefense from India and the United States participated to draw a roadmap for prevention, mitigation and preparedness.
26An Interpol workshop on preventing bioterrorism was held in Muscat, Sultanate of Oman, March 19-21, 2007. It was attended by 62 delegates from 15 countries, including senior police officers, government representatives, and representatives of the health, scientific, and academic communities. The objectives of workshop were to provide information and training, to encourage the development of a response capability, to promote relations between and with regional, national and international organizations, and law enforcement agencies, to develop a draft plan of action on a regional, national and international basis, and to present the Bioterrorism Incident Pre-planning and Response Guide.
27India is the chair of Asian Regional Health Forum. In February 2012, India hosted the 4th meeting of the Forum. Delegates from Bangladesh, Bhutan, Maldives, Nepal, Pakistan, Srilanka, Thailand and India participated. Cross border transmission of infections in neighboring countries and counter measures were discussed.
28Lessons learned from the 1918 avian flu pandemic were discussed, including both health and non-health emergency areas. Necessary business continuity planning of essen-
H1N1 pandemic alert was sounded by WHO. India initiated a prompt and effective response.29 Kits and personal protective equipment were distributed at airports and passengers were screened. The personal protective equipment, kits, and nasopharyngeal swab kits were also made available at hospitals designated to treat H1N1 in major cities such as Bangalore, Delhi, Hyderabad, and Pune. These hospitals had diagnostic kits, medicines, isolation wards, and quarantine facilities. NDMA, along with the Ministry of Health and Family Welfare, began screening passengers arriving from affected countries. Pharmaceutical companies were instructed to enhance their manufacturing capacity for Tamiflu should greater supply be required. Community awareness involved the regular dissemination of what should and should not be done to avoid concern or panic.
A control room was established at airports and in state crisis management groups. These control rooms were in constant contact with NDMA, the National Crisis Management Committee, and district authorities. Business community plans and in non-health-sector plans were also prepared.
For pandemic response, three points were adopted: (1) medical intervention with antiviral drugs, vaccines, and medical care; (2) nonmedical intervention through personal hygiene, and quarantines; and (3) food, power, transportation, and telecommunications. There was a contingency plan for maintaining the essential services of food, water, and health care. A multisectoral approach was adopted involving the health, defense, finance, transport, and telecommunications sectors. Through this methodology and a proactive approach, India experienced only minimal impact from H1N1. The Ministry of Health and Family Welfare coordinated events, issued guidelines, and ensured that state health departments were in compliance with or in consonance with the guidelines issued by the ministry. Private practitioners, private hospitals, and nongovernmental organization, energized activities along with the District Disaster Management Authorities or District Health Departments. Community leaders were also involved by dispelling rumors. At the same time, community leaders educated people to wash their hands before eating and cover their faces while sneezing or
________________________
tial service providers was initiated as a priority. To develop the Business Continuity Plan for Non-Health Sectors, NDMA issued guidelines on influenza H1N1.
29Due to the effective response in India, there was minimal impact of the 2009 H1N1 pandemic. In India, the Ministry of Health and Family Welfare (MoH&FW) coordinated the entire response across the country and helped state governments in critical areas. State governments managed the pandemic following guidelines issued by the MoH&FW. The private health sector through Public Private Partnerships, non-governmental organizations, The Red Cross, and The Indian Medical Association worked with district authorities. Community leaders were involved for awareness to curb rumors and to coordinate with government agencies. Essential services in non-health sectors were maintained by the Department of Food, Water Supply, Transportation and Telecommunications, etc. Individuals and families were provided with personal hygiene information, such as the importance of washing hands, covering one’s mouth and nose when sneezing and coughing, and home quarantine.
coughing to prevent infections. They also ensured that non-health services were also maintained. NDMA coordinated and monitored all events throughout the country and ensured that contingency plans were made available in all the states. At the same time, NDMA was also monitoring the status of H1N1 throughout the world. In addition to the role of the government, pandemic response planning takes into account the need to coordinate with industry, civil society, and local communities. This holistic approach is needed to provide medical interventions, such as distribution of drugs and vaccines; nonmedical interventions, such as quarantine; social interventions, such as communications; and essential basic services, such as security, food, water, and power.
Bansal stated that under current circumstances there is a threat of biological terrorism against innocent people around the world. To fight terrorist threats, comprehensive, preventive measures need to be planned and countries need to be fully prepared to handle an epidemic arising from such an eventuality. Bioterrorism will most likely be multinational, leading to a pandemic; therefore international cooperation will be of immense value for biodefense. Global disease surveillance, health intelligence, incorporation of WHO guidelines, quarantine at airports, utilization of global outbreak databases, and alert and response networks are the major components of pandemic preparedness plans and must be undertaken well in advance of an incident. In conclusion, cooperation on the exchange of information and experience, and the sharing of global best practices, modern technology, equipment, and skills among nations are the need of the hour in responding to a bioattack of international concern.
The discussion began with a question regarding how to deal with a combination of open information and rogue labs. Franz stated that because this is difficult, scientists must work together. Further, it is more likely that there would be a rogue individual than there would be a rogue lab because labs are hard to isolate internationally.
Norman Augustine then asked a question of Bansal about whether medical workers who are likely to come in contact with diseases during an epidemic should be required to be vaccinated in advance against known threats, for example, smallpox. Or is the risk of vaccination on such a large scale greater than the benefit to be gained? Bansal replied that in India officials try to vaccinate some groups of first responders, for example, the National Disaster Response Force (NDRF) and the Delhi police, but one has to weigh the benefits against the risks. There are considerably high risks associated with the anthrax vaccine, but fewer risks are associated with the polio vaccine, which is also less likely to be a bio-terror agent. Clearly, one has to weigh the costs and benefits, even for the vaccinations against H1N1.
A workshop participant asked Franz about the screening of scientists and ethical issues: For scientists working in critical labs, what concrete steps should
be taken to avoid an incident such as the anthrax attacks, where a scientist may do something mischievous?
Franz began first by stating that he cannot promise that any actions will work. He could not guarantee that there would not be an insider threat in his laboratory. However, one can reduce the likelihood through the leadership and cultural approaches he discussed. If the director of a laboratory and everyone in that lab, no matter their rank, knows they can walk in and talk to the director if they want to, that culture of openness will likely help. The director may reinforce that there may be situations in which he or she needs to use the chain of command, but there might be times when someone is so troubled that the person does not want to talk to someone in that chain. These sound like fairly soft and squishy solutions, and they are very hard to scale. If we have 10 army labs in the United States and we wanted to do this in every lab, it would probably be impossible. But openness, transparency, focus on quality, support, and the people at the bench are more important. Seemingly small actions by the director, like asking his assistant to block out time every week for him to just go walk around the labs and talk to people, are critical. Scientists love to share their results. By listening and responding, Franz believes a healthier culture is built, and there is a greater chance of finding an outlier and dealing with that outlier. Franz added that when he was at the lab, background checks were not performed, but after the anthrax letters, FBI background checks have been conducted on everyone. The participant followed up by asking if there are objective methods that can be developed for background checks. Franz replied that Bruce Ivins had a number of background checks, including by the FBI. We do not know for certain if he was the anthrax mailer, and there is no definitive evidence that he was. However, the circumstantial evidence is overwhelming that he committed those actions.
Bansal continued the discussion by noting that labs are not the only places of concern. In any place that needs to be protected, one has to develop methodology that applies universally. First, a person responsible for a particular task has to be held accountable. Within any organization, there are different levels of security and different types of people. One approach is the two-person rule, as is used in the BSL-4 lab at the National Institute of Virology in Pune. In addition to subjective approaches, objective measures are also needed, such as background checks. Those who work in sensitive positions in India have background checks and are monitored.
Based on his experiences as director of the Defense Research and Development Establishment (DRDE) in Gwalia, which has expertise in handling chemical and biological terrorism K. Sekhar relayed what happened in India after the anthrax attacks in the United States. There was a barrage of letters that contained white powder addressed to various members of parliament. At one point, they received nearly five hundred to a thousand envelopes containing white powder. It took quite a while to go through and analyze all the powder. Sekhar assured members of parliament that the substance was nothing but chalk powder; however, the fear created was enormous. After those events, India began a major program to train forensic experts. Over the 4 to 5 years of his ten-
ure, every forensic laboratory in the country received training on emergencies related to CBRN.
The same participant asked Bansal about the reliability of biosensors and whether there is a regular system of standardizing the precision and accuracy of biosensors to avoid false positives and false negatives. Bansal replied that the accuracy of biosensors is dependent on knowing the baseline of the biological agent naturally occurring in the background.
Another question pertained to the availability of emergency equipment and medical supplies such as masks and antibiotics, for India’s population of 1.2 billion people. Bansal replied that India has a high degree of preparedness, as the success story with H1N1 indicates. India does stockpile drugs for a certain number of people, and there are the commonly used antibiotics and detection equipment that could be sent from one part of the country to another. India is fully prepared, he said. There is also a stockpile of masks, but people must be educated on the need to use them. In terms of disseminating information, NDMA has a community-based disaster management plan that educates communities. For example, during the events in Fukushima, Japan, people in India received messages on their telephones stating that there would be acid rain in India, so they should not come out of the house. Bansal appeared on television and told people that Japan is about 6,000 kilometers from India and the direction of the wind is northeast; therefore, it was not blowing in the direction of India. There was no question that anything was coming to India by way of rain, wind, or sea. One has to develop a strategy to curb rumors and panic.
A participant asked about botulinum toxin because, he said, it is the only toxin that might be used in a terrorist attack. Russia is reported to have a large amount of botulinum toxin, and now it is on the open market for medical prophylaxis as well as for cosmetic uses.
Franz replied that botulinum is an interesting toxin. It is the most toxic substance known. It is a large, 50 kilodalton protein and it is not very stable, especially when it is purified. In former biological weapons programs, both the United States and the Russian Federation conducted work on it, but stopped. The Iraqis also tried to work with it. It is best not to stabilize it. It is denatured when it is very pure. The material that is used medically is very pure, because an immune response to some of the chaperone proteins occurs if it is not purified. Therefore, in order to have toxicity, it has to be injected or taken orally. It is not a very good aerosol weapon because it is not very stable and because it appears that macrophages in the airways destroy it. Also, there is a significant latent period. Franz did studies in nonhuman primates on inhalation methods, and then trying to treat them with antibodies as soon as they started showing clinical symptoms, and that was usually too late. The very first visible clinical signs are some changes in vision, and even if treatment starts early, it is probably too late. Then a ventilator is needed to keep the subject alive, and depending on the serotype, this could be for up to 30 days sometimes. A concern about botulinum would be contamination of something like milk.
A participant asked about the low mortality rates in the United States due to H1N1, because, unfortunately, the mortality rate was higher in India. What, he asked, was the strategy in the United States for the distribution and use of Tamiflu? With regard to Tamiflu and H1N1 in the United States, there was a great deal of monitoring to determine whether there was resistance developing. However, the United States focused on vaccines as the first line of resistance and Tamiflu was used only in specific cases. A participant noted that studies were conducted in Japan over the last 10 years on the medical prophylaxis of Tamiflu and very insignificant levels of resistance were found. Since resistance does not seem to be a problem, Tamiflu could be more widely distributed to help control the spread of the infection.
A final question was asked about mass monitoring of the public, for example, of people getting off airplanes and infrared scans being taken of their foreheads to see if they have a fever or not. Civil liberties seem to get in the way of this type of monitoring. Is that a good thing to do? And if it is, how do we deal with civil liberties issues? Bansal replied that monitoring is not for fever symptoms because there are so many causes of fever, and only a medical exam can determine the cause. As a doctor, he understands that careful observation is critical, and one cannot jump to a particular treatment until the particular cause is known so that the treatment will not change the course of the disease and affect the ability to determine the actual cause.
TECHNICAL ASPECTS OF NUCLEAR SECURITY
V. S. Ramamurthy introduced the presentation of the joint NAS-National Institute for Advanced Studies (NIAS) report entitled, India-United States Cooperation on Global Security: Summary of a Workshop on Technical Aspects of Civilian Nuclear Materials Security.30 He noted that one of the primary goals of the workshop was to jointly develop proposals for cooperation on nuclear materials security among experts from India and the United States. This challenge is complex and requires a multidisciplinary approach. He expressed his delight at the publication of the joint report that captures the 2013 workshop and highlights what we can do together to identify solutions.
Ravi Grover thanked Ramamurthy for the opportunity to speak at the formal Indian launch of the joint report. He reaffirmed that security of materials, facilities, export controls, and technologies associated with nuclear materials is taken very seriously in India, as is the development of proliferation-resistant technology. Using science and technology, one can reduce the magnitude of the problem of nuclear materials security. He noted that the nuclear security summits have raised the level of concern about nuclear materials security, and dis-
________________________
30National Research Council. India-United States Cooperation on Global Security. Summary of a Workshop on Technical Aspects of Civilian Nuclear Materials Security. Washington, D.C.: The National Academies Press, 2013.
cussions have taken place on all aspects of nuclear security, including the global security architecture, the role of the International Atomic Energy Agency, the security of nuclear materials and radioactive sources, the nexus between nuclear security and nuclear safety, the security of transportation, combatting nuclear trafficking, nuclear forensics, and, most importantly, nuclear security culture, especially in industry. India has participated in each of these summits. As a part of the summit process, communiques and work plans have been issued, indicating the commitment of participants to nuclear security. Many countries have come together to offer gift baskets to do more than what is included in the communiques.
Another effort is the Nuclear Threat Initiative Nuclear Materials Security Index,31 and one gets the sense that people are looking at the issue of nuclear security differently by focusing on disarmament and the elimination of weapon-grade materials. The way that this is viewed by some, however, may be a confirmation bias. Nuclear security needs to be examined without a confirmation bias in that there needs to be independent assessments of security that do not simply endorse the status quo without actually testing the system rigorously. One has to look at synergy between nuclear security and science and technology to reduce the overall problem. Nuclear materials are used in the generation of energy, which is especially important in India.
L. V. Krishnan stated that the 2012 workshop provided a wealth of information, just as this workshop is doing, but was more specifically focused on nuclear facilities and issues of nuclear materials security. It was an excellent opportunity for professionals to interact and share their perspectives, experiences, and programs. Speakers came from the United States with diverse experience in a range of aspects of nuclear materials security, including handling, which is large scale in the United States, and which requires advanced techniques of nuclear materials accounting, for example. Though production of materials in the United States has stopped, there is still a need for safety and security. India has developed in-house expertise, and they have made use of limited materials. Based on Indian power needs, experts have continued to work on developing proliferation resistant reactors, and reprocessing techniques are also being developed.
Krishnan also noted that there are links among safety, security, and safeguards, and there is a need for balance between the conflicting desires for greater transparency for the sake of safety, and the requirement for confidentiality for security purposes. Materials, control, and accounting require the right type of nuclear instrumentation for detection, and the quantification of nuclear materials. Nondestructive assay is a technique of mass spectrometry that provides near real-time information on nuclear materials and utilizes nuclear detectors and instrumentation. However, some materials are always left over in the plant, and this discrep-
________________________
31Nuclear Threat Initiative. Nuclear Materials Security Index. Available at: http://ntiindex.org/; accessed September 21, 2014.
ancy in material inventory is called materials unaccounted for. New real-time accounting techniques can help in material balance areas. Physical security is developed specifically for every facility, even for reactors of the same design. This is called the design-basis threat (DBT). The DBT, which is designed by scientists, law enforcement personnel, and security professionals, and includes training and requires training, was discussed as essential to security. In India, the Global Center for Nuclear Energy Partnership (GCNEP) has a school of nuclear security studies, which has been set up to train people.32 The threats being considered are external forces, sabotage, and terrorism from the sea.
Krishnan also highlighted nuclear forensics, which involves analysis after capture, age, and isotopic composition. It is an imprecise science. Databases are critical and a national database is the first step in being able to have a library of forensic samples. In the United States, there are 300 samples in the national databases.
With regard to cybersecurity, software needs to be tested often, because the use of commercial systems has its risks and unknown vulnerabilities. The Security Network Access systems used at Indian facilities have different zones with firewalls. However, unless the digital systems are appropriately secured, increasing the level of connectivity of many critical facilities may actually introduce more vulnerabilities and increase the risks of cyberattacks.
In conclusion, there were numerous suggestions about cooperation on safeguards, safety and security. There is common ground on the importance of detection and of tracking materials to maximize safety and security. Spent fuel may be used as a means of exploring these issues together. Not all lessons, however, can be directly transferred from one place to another, so we need to take context into account.
Raymond Jeanloz stated that we have a great deal of agreement on the Indian and U.S. sides. The focus of the workshop was on civil nuclear materials and technical aspects because we come from the technical communities in our countries. The background for the workshop was the nuclear security summit of 2010 and one of the outcomes of that summit was a commitment by the Indian government to establish the GCNEP.33
________________________
32The school’s mission is “To impart training to security agencies on application of physical protection system and response procedure, to enhance physical security of nuclear facilities by developing and deploying most modern technological tools including information security and to provide facilities for test and evaluation of sensors and systems used for physical security.” Government of India, Department of Atomic Energy, Global Centre for Nuclear Energy Partnership, School of Nuclear Security Studies. Available at: http://www.gcnep.gov.in/schools/snss.html; accessed September 21, 2014.
33Cann, M. 2010 Nuclear Security Summit National Commitment Implementation: Steps in the Fight Against Nuclear Terrorism. Paul H. Nitze School of Advanced International Studies (SAIS), Johns Hopkins University. U.S.-Korea Institute at SAIS, 2012. Available at: http://uskoreainstitute.org/wp-content/uploads/2012/03/USKI_NSS2012_Cann.pdf: accessed September 21, 2014.
Civilian nuclear materials are found in many countries, and the tracking of materials is less perfect than one would like, as we need to balance nuclear energy and nuclear capacity with nuclear security. Jeanloz emphasized the systems approach to nuclear security, and noted that the report raised the importance of comparing notes among Indian and U.S. experts to this end.
Communication with the public is also crucial, and the point was made in the report that the technical community needs to think about this communication in advance because the public and policy makers need to be convinced that the solutions are reliable and can be trusted.
Focus on future collaboration leads to discussion of technologies and larger-scale systems integration. Built-in validation will help to mitigate problems of human reliability so that people stay alert and are notified that they are performing well. This means integrating hardware and software with the psychology of individuals and culture; this is another imperfect area where we can work together.
Jeanloz noted that there are strong capabilities in both the United States and India, but the interpretation of results is still somewhat an art form. It is not enough to have a complex understanding of a sample since decision makers need to have attribution for actionable intelligence. There may be pressure for a rapid turnaround of information. There are many areas for cooperation in this regard. For example, we could begin by analyzing facilities in the field and start building databases, because we need to have something to compare against. There is also a need for more specific understanding of processing materials, age dating, and chronological analysis. An effective program will require international cooperation. There are technical ends and political ends: databases need to be compiled and different countries or groups have databases that need to be made more available via technology while still protecting the confidentiality of the samples. It is not necessary to share the details when querying a database.
Insider threats are also a challenge because we do not have enough ideas about how to identify an insider and to act on this knowledge. There are technological solutions that need to be developed beyond Personnel Reliability Programs (PRP). Examples of possible technical solutions include delay mechanisms to control access to critical areas, observation cameras, and material balance techniques to monitor movement and use of sensitive materials.
Jeanloz concluded by saying that a key to this report was highlighting the potential for cooperation among experts from Indian and U.S. national labs, academic labs, and industry. It was very clear that the technical communities continue to want to work together, and we can benefit from working together.
A participant asked if security classification is based on legal and predetermined criteria. Michael O’Brien replied that if we analyze security, there are systems that are classified, and there are classification guides that are descrip-
tions of a detailed protection system that someone may exploit. Every country has its own security systems and no matter what they want to share, they cannot.
Micah Lowenthal also noted that one can discuss safety systems without giving away too much because one can talk about reliability, and this can help provide confidence to people. With regard to the threat, there is very little that is shared publicly and DBT is not shared. There have been proposals for international databases on forensics, but the United States has been promoting the idea that each country should have its own database so that if there is a question, we can be confident that another country could answer that question for its own purposes.
A participant asked about cyberthreats and the inadequacy of psychological threat analysis. If one takes a large number of cases, there will be people who are doing bad things, including killing people. Close observation of people alone does not always reveal these problems. Are there other means of psychological testing that can provide confidence in the psychological fitness of the employees in sensitive facilities? Would an approach such as “know your employee” help increase this confidence?
Jeanloz replied that PRP is the type of detailed program that is used as a means of evaluating threats, and some are common-sense practices, such as routine testing for drugs and alcohol use, just like for pilots. Yes, there are a number of these tests that are used. He did not want to diminish these practices, but perhaps there are some other technological solutions, such as the two-person rule or engineering solutions to make it difficult to subvert the system. We could benefit from another round of joint discussions on this because there may be technologies that can help build a difficulty for misusing the system.
O’Brien noted that at the 2012 workshop, an overview of a 2-week training session was given. The training deals with insider threats, identifying anomalies, engineering out potential vulnerabilities, recognizing insider threats, and addressing operational aspects of facilities. This is an area ripe for cooperation.
Mukkamala noted that after an incident, such as a school shooting, people can work backward to identify threats; companies do this as well. One can be persuaded to provide this information, and industries sometimes do this.
Grover made a final comment. There is a lot of tension at the present time because, on one hand, civil society demands transparency, and on the other side, there are technologists and bureaucrats who feel the need to protect sensitive technologies. How do we balance these two perspectives?
Jeanloz agreed that this is a challenge and added that the problem is even greater because there is a tension between privacy and the tracking of technology to depersonalize the discussion; we allow ourselves to be tracked by companies. Transparency vs. sensitive information and tracking of information is what social media is doing. For our democracies, there is a debate on the nature of privacy. Is privacy gone? We should not jump to this conclusion. Augustine added that in his view, privacy is gone. The CEO of one of the better known web-based social sites said that one can build tiny cameras and people leave
cameras around the home and post videos on the web that they cannot get back. The CEO said simply, “Get used to it.”
FROM SUGGESTIONS TO COOPERATION
Stephen Cohen noted that his overall concern was for the output of the workshop to not disappear into space. Converting technology insights into useable policy recommendations is the most difficult task of all. So how can we convert ideas and suggestions into policy that will be implemented? This involves interface with the policy community, the media, and politicians.
Politicians are busy people. They need material that they can understand and that allows them to prioritize the way in which they spend money and the way in which they allocate time. That is the major task. What we have done at this workshop thus far is a superb, world-class discussion of how technology can influence the prevention of terrorism, and amelioration of terrorism, but how does that translate into words that a politician can understand? How do you do things that get people to do the right thing without forcing or coercing them? One of the key points Cohen learned is that the responders to a disaster or a terror event must keep ahead of the media or keep current with the media because the media have a life of their own, especially social media.
Cohen offered a practical way forward: make a comprehensive list of potential areas for cooperation. That forces people to think about priorities. What is the most important issue? What is the least important issue? How does one balance out chemical threats, biological threats, nuclear threats, cyber threats? Politicians must demonstrate why things that do not appear to be a threat now might be a threat in the future, and why they are worth attention and perhaps money and time, which, of course, is the scarcest resource of all in governments.
In particular, what about the whistle-blower effect both in governmental organizations and in private organizations. How does one get companies or perhaps government units to behave responsibly in terms of developing protected devices when it is not profitable to do so?
Cohen has learned that an efficient system, one that is geared to protect against terrorism, is actually more profitable in some ways as well. There is less waste; this is the case with the use of baggage tags, and tagging of containers. The system actually works better when one prepares for security in many ways. The additional cost of security may actually be regained in terms of efficiency of plant operation and so forth.
A point that A. K. Sinha made is that preparation for disasters may have spin-off effects for other threats, including terrorism and vice-versa. Perhaps in a future meeting, we can explore the relationship between disaster preparedness and terrorism preparedness. If money is spent on disaster management, for example on a national disaster management center, competence in terms of terrorism management is improved.
Cohen wrote a book in 1978 about the Andhra Cyclone and clearly, India has improved preparedness and response to cyclones to a level better than Amer-
icans, as seen during Hurricane Katrina. Sinha thinks the government had looked at the Orissa case here, also. When government reviews their own performance and it improves, they inspire confidence in their people and their populations. This applies to terror attacks as well as natural disaster events.
Cohen also proposed a new meeting on the question of implementation. When he first came to India 50 years ago, almost to the month, he attended several Indian National Congress Party meetings. The one Hindi phrase that was burned into him quickly: “We must implement. We must implement.” He has heard this phrase often ever since. It was astonishing.
V. J. Sundaram stated that the systems approach has been stressed with the need for quality reviews, testing, maintenance, training, retraining, and finally accrediting the whole system. He agreed that implementation is key. Whether it is for tackling national industrial disasters or emergencies or for terrorism response, which will reduce vulnerability, he thinks that using systems engineering designed for Six Sigma certification makes systems more reliable and robust. It takes time, however. As an engineer, he was glad that the question of whether India needs a better quarantine system for agricultural and food was emphasized. The same thing with health; proactive measures helped India to contain H1N1.


























