E
Opportunities for Creating Value from Network Science
This appendix supports the findings of Chapter 5 and provides details of the scenarios developed in response to Items 3 and 4 in the statement of task. What are the viable investment options for the Army and nation in network science? How does exploiting these opportunities create value? The committee attempted to answer these questions by constructing three scenarios that represent fundamentally different levels of response by the Army.
Scenario 1, Building the Base, examines the alternatives for the Army if it wants to invest a modest amount (on the order of $10 million annually) in 6.1 basic research within the context of its present funding processes. While some changes in the style and content of its present research activities are envisaged, this scenario represents a minimal investment and a minimal change in posture relative to the current Army R&D portfolio of investments and processes. It creates value by increasing the knowledge of topics in the core content of network science and by expanding the base of trained practitioners.
Scenario 2, Next-Generation R&D, examines alternatives created by applying best practices in modern industrial R&D to the Army’s R&D investments in network science. In this scenario, basic research (6.1) investments are coupled with larger applied research (6.2) and, possibly, 6.3 investments, to create technology investment options for the Army to exercise in concert with suppliers. The committee envisages, however, that the management of this process would be substantially different from present Army practices. The committee gives an idea of how these changes could be effected by creating a market-driven R&D environment. Projects that might be funded in this environment are exemplified by three kinds of projects: one in social networks, one in engineered networks, and one in biological networks. Comparison of these projects shows the sorts of issues and benefits that could arise from Scenario 2 investments in the three different areas of important network applications.
Scenario 3 takes as its point of departure the phrase “to enable progress toward achieving Network Centric Warfare capabilities” in Item 4 of the statement of task. In it, the committee asks what the Army (or, more appropriately, the DOD Office of Force Transformation [OFT]1) should do if its primary objective is to create these capabilities in a robust and affordable way over the course of the next decade. A significant investment in network science would be one element in such an effort, but the emphasis would reside elsewhere. Specifically, in this scenario the committee examines past efforts of the federal government to develop major new warfare capabilities all the way from basic research to deployment in the field in order to estimate the magnitude of the effort and investment required to source and deploy such capabilities.
SCENARIO 1, BUILDING THE BASE
Scenario 1 involves a modest level of funding (~$10 million per year) that fits into the Army’s current scheme for 6.1 basic research. Small amounts of Army risk capital funds are invested to create a knowledge and personnel base from which it can attack the practical problems that arise when trying to provide network-centric warfare (NCW) or network-centric operations (NCO) capabilities. It is for this reason the scenario is called “building the base.”
Because the anticipated investment is too small to fund significant interdisciplinary efforts, it should be focused on leveraging existing research in areas related to network science. It would support 20 to 30 single-investigator or small-group grants of $300,000 to $500,000 per year. Such an investment would allow the Army to tap into top research efforts in physical, social, and biological networks. The Army should fund only the most outstanding researchers because the very best are qualitatively different from even the very good. The essential point is that to pay off big in
|
1 |
For further information, see http://www.oft.osd.mil. Accessed August 19, 2005. |
terms of breakthrough ideas and models, the very best researchers must be recruited to do the work. To attract an elite group who will influence the future of network science, the Army must adapt its funding and management policies, possibly offering larger and longer-duration grants with few or no restrictions on citizenship, publication, and the like. The selection criteria would be excellence of research as judged by peer review and track records, relevance to Army objectives, and opportunities for Army involvement through inclusion of suitable Army personnel in the effort.
The committee envisions that the research efforts would be located at major research universities. An important aspect of the program might be a once-a-year conference at an Army laboratory or facility, where the principal investigators (PIs) would report on accomplishments during the year. The program needs enlightened management to support interdisciplinary work through the interaction of a diversity of PIs. A major theme of the program would be the achievement of fundamental advances in network-research-based statistical physics, applied mathematics, development of mathematical models of social phenomena, and other areas by generously funding only exceptionally talented individuals who are organized into a national social network.
Such a program would be the first to address the needs of network science per se. The program would focus on networks as coherent entities characterized by their architecture, structure, and dynamics. By deliberately adopting a broad theoretical and methodological focus, the program would encourage the creation of fundamentally novel ideas. A wide diversity of approaches is a key feature of long-term success. Keeping the goals broad and flexible would allow the Army to cultivate such diversity; a narrowly defined program would eliminate much of the creative potential that could lead to breakthroughs and new ideas. One way to do this would be for the Army to hold one or more workshops with appropriate personnel to determine the topical content for such a program.
The Army’s needs are broad and fundamental in nature: It must learn how to approach the creation of a predictive description of large, interacting, layered networks. A basic science program is the first step toward building up the critical mass of talent needed to address specific Army problems in this area. This modest approach would allow the Army to identify a relevant research community, and organize it so that, with time, it could be called upon to address specific needs.
The proposed approach differs from existing programs in agencies such as the National Science Foundation (NSF) and the National Institutes of Health (NIH) in that it focuses on network science per se. While a significant amount of research is taking place in communities addressing the applications of networks, almost none of this research is funded by dedicated network science programs. Instead, researchers are funded by, for example, the NSF, to improve the Internet or to understand the statistical mechanics of complex systems, or the NIH, to uncover the features of specific organisms or biological processes. Because many of these research programs cannot avoid dealing with the network aspects of these problems, they divert some of their funding in that direction. Nevertheless, most of their work is focused on applying network ideas to specific systems rather than on developing new tools and ideas. Currently, no agency the committee knows of has a specific program devoted to network science. A research program on network science per se is a new concept, with unique and novel goals.
As a consequence of its discussions with Army and DOD representatives, the committee has come to realize that the fundamental problems underlying effective NCO lie in the social domain. Yet how people interact and utilize technology or make decisions based on shared knowledge are areas almost unexplored in the Army’s current basic research portfolio. The committee urges the Army to focus additional resources on the possible applications of network thinking to social, especially organizational, issues (Helper et al., 2000).2 Applications to biology, engineering, and the physical sciences are also essential to Army applications, but the Army is already funding research in these areas. The committee suggests that on the margin the most significant problem is not how to build better satellites, tanks, or medicines but rather is how to organize millions of individuals to collect intelligence, deliver supplies, and prosecute wars over an increasingly global, constantly shifting geographical and political playing field (Garstka and Alberts, 2004). This is a monumental problem that has not, however, traditionally been the province of science. Rather, it has been managed through a mixture of intuition, experience, and tradition. A significant fraction of the proposed program should address this organizational problem the way scientific problems are addressed: through a combination of theoretical modeling, data analysis, and controlled experimentation.
To illustrate the flavor of its thinking, the committee closes this scenario by indicating some promising research topics in four broad areas: network structure, network dynamics, network robustness and vulnerability, and network services. Each area has theoretical, empirical, and experimental components. Investments in basic research in each can provide value for the Army.
Network Structure
Advances in the applications of network research are limited by a lack of fundamental understanding of the structure, evolution, and topology of complex networks (Newman, 2003; Watts, 2004; Newman et al., 2005). Many network models have been formulated and studied by numerical
simulations or approximate analytical methods (Albert and Barabási, 2002; Pastor-Satorras and Vespignani, 2004; Dorogovtsev and Mendes, 2003; Ben-Naim et al., 2004; Bornholdt and Schuster, 2003; Barabási, 2003). While these efforts constitute an advancement in the modeling and representation of networks, the topology of these models is far less rigorously understood. Questions concerning the universality of topological properties, correlations introduced by dynamical processes, and the interplay between clustering, hierarchies, and centrality in networks remain only partially answered (Amaral et al., 2004). A full understanding requires the development of rigorous methods to uncover the mathematical structure of growing networks. Advances in this direction can be achieved only by the empirical study of real networks and by developing the appropriate mathematical tools and metrics not only to characterize novel systems but also to classify networks based on their topology, structure, function, and dynamics. In this respect we are lacking in the fundamental characterization of network topology, in our ability to characterize weighted networks and communities in networks, and in our description of the time evolution of the network topology. In parallel, we need to develop discrete and continuum models that generate networks whose structure and evolution mimic those of real networks.
In spite of considerable effort in social network analysis over the past 50 years and great interest in the past decade, surprisingly little is known about either the detailed structure or the time evolution of social networks. In part, the gap in knowledge has come about because purely social interactions, unlike interactions conducted on an engineered network such as the Web, are much harder to track empirically. It also derives from a tendency to view all networks as static entities with structural features rather than as dynamic processes with parameterized rules. Finally, it has resulted from the tendency to ignore the role of social and organizational contexts in network formation and to focus instead on the role of exceptional individuals or small-group structures. Without a better understanding of social networks, it is extremely difficult to advance our understanding of any social processes, including implementation of the cognitive and social domains of NCO to improve combat effectiveness.
Network Dynamics
Networks are specified not only by their topology but also by the dynamics of information or traffic flow along their links. The amount of traffic characterizes the connections in a communication system or large transport infrastructure and is fundamental for a complete description of these networks (Barrat et al., 2004; Almaas et al., 2004). Heterogeneity in the intensity of connections may also be important in understanding social systems. The ultimate objective is a mathematical characterization that might uncover general principles describing the dynamics of networks. Furthermore, networks provide the substrate on top of which the dynamical behavior of the system must unfold. At the same time, however, the various dynamical processes are expected to affect the network’s evolution. Dynamics, traffic, and the underlying topology are mutually correlated. It is vital to define appropriate quantities and measures capable of capturing how all these ingredients participate in the formation of complex networks. To carry out this task, we need to develop large empirical data sets that simultaneously capture the topology of the network and the time-resolved dynamics taking place on it.
Understanding “how things spread” through different kinds of social, organizational, and technological structures, and with what consequences, is of paramount concern in an increasingly global economy and culture (Watts, 2003). Examples include electronic viruses spreading through computer or phone networks, biological viruses (weaponized or natural) spreading through the contact network in a society, and ideas or strategic concepts spreading on a social network (Arquilla and Ronfeldt, 2001; Pastor-Satorras and Vespignani, 2004; Anderson and May, 1992). Uncovering the similarities and the differences between electronic virus spreading, biological and social contagion, and the interplay between the network and spreading processes is crucial for the research community. Such research has important potential Army applications, from defending the communication infrastructure against viruses to developing scenarios for limiting the impact of a biological contagion.
Individuals making strategic decisions in uncertain or ambiguous environments (which is to say, almost all environments) are influenced either explicitly or implicitly by the decisions of others (Katz and Lazarsfeld, 1955; Watts, 2003). And when all individuals are paying attention to one another and constantly making or updating various decisions accordingly, “social contagion”—the spread of ideas, influence, norms, innovations, attitudes, rumors, unrest, violence, extremism, etc.—becomes not only possible, but pervasive (Rogers, 1995; Gladwell, 2000; Huckfeldt et al., 2004). In some ways, social contagion seems like biological contagion, but in other ways it is fundamentally distinct (Dodds and Watts, 2004, 2005). Sorting out these differences is a key to understanding network contagion.
In order to exploit the information infrastructure capabilities envisaged for NCO, the Army must comprehend how large groups of individuals coordinate their efforts to solve large-scale problems, where “large-scale” implies that the scope of the problem is beyond the capacity of any particular individual to solve or even fully comprehend (Dodds et al., 2003; Watts, 2003).3 Examples of such problems include (1) collating large volumes of ambiguous information, collected in widely dispersed environments, to assess the seriousness
and immediacy of specific threats; (2) coordinating large numbers of troops in novel and rapidly evolving combat environments; (3) coordinating geographically and industrially diverse supply chains to deliver highly specific and time-sensitive logistical support that varies rapidly and unpredictably; (4) business firms attempting radical innovations or recovering from catastrophic supply-chain breakdowns; and (5) educational or community development organizations attempting change to alleviate widespread and deeply rooted social or economic disparities. Large-scale problem solving is complicated because it involves the study of collective behavior that is oriented toward particular (if imprecisely specified) outcomes rather than just the study of processes in action. It is also, and perhaps not surprisingly, the problem area about which least is understood theoretically.
Biology also deals with diverse large-scale networks. The most prominent cellular networks are metabolic networks, the regulatory network, and signaling and protein interaction networks (Barabási and Oltvai, 2004). The key question here is, What do network science results tell you in terms of biology? Are they falsifiable? Do they offer testable predications? In order to be of value, the predictions must ultimately be testable in the laboratory. This kind of work is being partially funded by the NIH roadmap initiatives. Results in this domain might lead to new ways to analyze networks and to make predictions relevant to rapid response to disease and biological warfare.
Another important structural and dynamical issue is the location of function within a biological network—that is, What is the architecture of the network? Networks typically comprise different groups of interconnected elements, or modules, each one being responsible for different functions. In engineered networks, this architecture is designed in a priori. In biological networks, it must be discovered by, for example, identifying highly interlinked communities of elements. Modules can be repeated at different hierarchical levels and interconnected via the hubs of the system. How modularity emerges across many biological networks and how it can be reconciled with the other properties of these networks are basic questions. The constraint and facilitation of biological phenomena by network structure is an issue that is likely to be at the forefront of biology in the coming years.
Network Robustness and Vulnerability
Networks need to be able to function in spite of errors, failures, and attacks. Such phenomena can affect a network’s ability to function in several fashions—for example, by incapacitating nodes and links or limiting traffic, leading to local and potentially cascading failures (Watts, 2002; Dodds et al., 2003; Albert et al., 2000; Cohen et al., 2000, 2001). How do we understand the different modes of network failure? Can we design networks with maximum tolerance of errors and a high survivability under attack? What is the relationship between a network’s robustness and its structure? How do the different dynamical processes taking place on networks affect their survivability? These are questions that, if answered, could fundamentally alter the Army’s ability to design and implement fault-tolerant communications and organizational networks.
Network Services
The operation of computer networks is governed by an architecture, known as a reference model, in which the functioning of the network is divided into independent layers built on top of each other (Tanenbaum, 2003). The lower layers of this architecture deal with the physical connections (including wireless) and electrical signals transmitted across these connections that link the nodes of the network. The important concept underlying this organizational construct is that each layer of the architecture delivers “services” to the layer above according to a standard interface convention. This organization is important to hide the workings of one layer of the architecture from those of all the others. Thus, the technology used to implement one layer can be upgraded without changing the operation of the layers above and below. In the open system interconnection (OSI) reference model describing the architecture of computer networks, the lowest layer is referred to as the physical layer, and the next two layers as the data link and network layers, respectively. On top of these sits the transport layer, whose function is to ensure that the messages from the layers above get transmitted reliably from one computer to another even if the lower three layers are unreliable. These four layers, in concert, establish a reliable communications link between two computers (nodes) on the network, over which messages associated with services created in the upper layers are delivered (Tanenbaum, 2003).
The Internet is the most important and familiar computer network. As important as the Internet itself, however, are the services that are created at the upper levels of the Internet architecture. Among the most visible services that have evolved on the Internet are e-mail, the World Wide Web (www), search engines, and the targeting and formatting of information to individuals. Other services, such as making information available in digital format and positioning data globally, have added value to the network.
Search engines such as Google play a major role in finding Web sites for travel, medical information, research papers, indeed almost anything you can conceive. As commercial activity on the Web increases, all kinds of services that support it have developed. These include services that provide individualized news, weather, driving directions, and maps. Such services allow one to track a storm as it travels across a state in real time or to view the road surface of a highway pass from a camera mounted at the summit. They are changing the way citizens access and use information. Underlying these activities is an evolving research base in
filtering, clustering, ranking, and optimization. This is a broad area of study carried out largely in computer science, electrical engineering, and computer engineering departments worldwide and in many firms. Some of the important topics encompassed by this area are data mining, distributed computing, network protocols, information capture and access, and security, privacy and cryptography. Since these services are vital to NCO, support of basic research in this area should ultimately create value for the Army.
SCENARIO 2, NEXT-GENERATION R&D
Scenario 2 envisages applying best practices in industrial R&D management to the Army’s investments in projects that combine basic and applied network science. Specifically, the committee expects the objective of these projects to be the articulation of technology investment options that could be exercised by the Army and its vendors to provide a desired capability. The amount of this investment is envisaged to be between $25 million and $100 million annually, roughly $25 million per project. There are expected to be investments in the university community for the basic research and in both Army in-house activities and commercial firms for the applied research. The committee envisages, however, that the R&D projects would be managed in a way profoundly different from the way in which current Army in-house and external centers are managed.
The selection of projects to be funded would be market driven and controlled by a top-level Army team. It is expected that connections between the basic and applied portions of the research will be much more intimate. Modern Internet collaborative tools would be used to manage the day-to-day work in rough analogy to the global design of industrial products. The activities are managed in small, intimate groups devoted to specific subprojects that are integrated into the overall project in a looser networked fashion. People flow from one small group to another over time. The entire team makes up a social network consisting of smaller, more tightly coupled social networks. In short, this scenario envisages the application of modern communications networks and tools and the insights of modern social network theory to transform the management of Army R&D projects.
The committee proceeded by first agreeing on the most effective management approach for next-generation R&D projects. It developed the concept of “market-driven” management to apply to all projects that characterize the entire Scenario 2 segment of the opportunity space. While associated issues and benefits will vary depending on the network application, the market-driven approach is the same. To illustrate the scope and scale of next-generation R&D with market-driven management, committee members developed three sample projects in the sociological, engineering, and biological areas of network applications.
These projects were selected in diverse areas to underline the committee’s belief that research will be equally necessary in all areas to advance network science. While each of the sample projects has the potential to advance network science, they should not be construed as a “shopping list,” and the committee does not recommend their implementation without careful comparison of their costs and benefits with those of other research projects.
Market-Driven Management
The U.S. Army faces a significant challenge today—how to create a more responsive R&D process that can leverage the relevant network science initiatives of universities and private companies and use them to design and deliver improved network-centric warfighting capabilities to our forces.
As DOD prosecutes the global war on terrorism, it is terrorist (social) networks that are enabling insurgents to innovate, react, and adapt very quickly—in many cases more quickly than U.S. forces. Given the complexity of NCO, the current R&D model is hard-pressed to react, and it is not delivering new insights and capabilities in a sufficiently timely manner to meet Army operational requirements. One only needs to look at the current challenges facing major programs like the Future Combat System (FCS) to understand that the current R&D process needs drastic change (Weiner, 2005).
To field capabilities for NCO more effectively at the strategic, operational, and tactical levels, the Army must develop a model for next-generation R&D, and the evolution of network science may provide a unique opportunity for the Army to transform the R&D process. To make this new model a reality, the Army must think outside the box, leverage existing technology, and attract outstanding researchers both within the Army and in industry and academia.
By combining new thinking, new incentives, and a close partnership among the military, industry, and academia, the new R&D model could leverage existing networks and collaboration technologies to accelerate the development of network science and simultaneously to enhance the R&D process. The new model must take advantage of the rapid proliferation of technology coming from the commercial sector as well as the increasing amount of network science R&D flowing from university research. At the core of the new model will be the innovative use of robust networks and proven, Internet-based business concepts that drive change and increase the speed with which knowledge, research, and technology are delivered.
Companies like Intel, GE, and Oracle, among others, have established network-centric business practices to deliver new technology, products, and services at a rate that keeps them in the forefront of innovation and competition. They do this by keeping their feelers out in the academic, scientific, and technology communities, monitoring evolving technologies, and placing bets on which ones will mature soon and have the most positive market effect. Simultaneously they develop
and market products, build market infrastructure to support them, please shareholders, and provide new working capital to continue the process. The Army must adapt and incorporate these industry best practices into its new model, perhaps by creating a networked R&D framework that would engage both industry and academic researchers and more closely integrate them with the Army’s in-house R&D resources and stakeholders. The framework could be an eBay-like network model that aggregates ideas and supports a community that rigorously (but rapidly) evaluates them (Surowiecki, 2004).
At the heart of this new model for advancing NCO is the establishment of a national network of virtual centers of excellence at multiple universities, where small groups of researchers act autonomously but are connected to the Army through an R&D coordinating council that also facilitates linkages with private companies. To establish the centers, the Army could implement an initial application process that provides core funding for the researchers. A portion of the funding could be maintained in a focused project fund, which could then be dispensed to research centers that collaborate to address specific Army challenges.
The challenges could be prioritized through an internal application process. Then the Army could post specific problems of interest to which the centers could respond with a brief proposal, estimating time and additional resources needed to address them. The Army would select the most appropriate center to address the challenge and allocate additional funding if necessary. The additional funds might also cover such things as extended data collection, new apparatus needed to perform the task, or programming to generate an interface for a project or even to take an idea to a prototype.
In most cases, members selected to participate in the community would receive base funding to cover their core personnel and other fixed costs. The network of the community would be used to assemble and fund a variety of flexible project teams. In addition to an Army coordinating council, other funding entities (such as other government agencies or private companies) might be invited to participate in this network as sponsors of projects. This mechanism could significantly shorten the normal process between posing a problem or challenge and getting a solution.
Projects could arise in two primary ways. First, the Army coordinating council or another sponsor could post a Request for Proposal (RFP), and various participants from the centers of excellence would submit research proposals. These proposals would be graded by the community of centers, industry participants, and the Army. For large projects, potential participants might also post their own smaller RFPs to assemble teams for subprojects. In either case, project teams could include participants from multiple institutions in the network. When a sponsor wanted help evaluating proposals, it could ask other participants in the network to grade different proposals. Network participants, like those on eBay, would all have a continually updated reputation rating. This buyer-initiated process is similar to that used on sites like Elance, Inc.
A second way for projects to form would be for researchers to post proposals for projects they want to do (or project-related services they are willing to do). In cases of highly desirable projects or services, different sponsors (or sub-project leaders) might compete for the services of a person or team. This seller-initiated process is similar to the process used on sites like eBay.
In either case, the centers and researchers who bring worthwhile knowledge, research, and technology to market are funded, and those who don’t are not. And the lead time of a year or more that is typical for a grant application process could be reduced to weeks or days.
An example that provides valuable insight is the Networked Centers of Excellence (NCE) program in Canada.4 NCE mobilizes research talent across Canada and applies it to critical challenges that benefit all Canadians. The program fosters partnerships of business, education, and government to accelerate the exploitation of knowledge, research, and technology and to speed their transfer to products and services that succeed in the marketplace.
One way the Army could organize and apply this new model would be to staff its coordinating council with qualified R&D people (senior officers at the O-5 to O-7 level, including some with warfighting experience) to operate and manage Army and joint R&D projects, as described above. A one-star general could be placed in charge and told that if successful, he/she will be promoted in 3 years. The council could be limited in number to 15-20, mainly to manage the network community described above. It would consist of experienced R&D officers to guide this process, including some O-6 warfighters who would be able to orchestrate or manage the input from the networked community.
The council members would be like Linus Torvald’s small group of Linux code approvers or eBay’s inner circle of strategic community managers. The Army must give serious thought to how to attract the best minds. Additionally, the Army may want to consider adding to the council one person from industry and one from academia, both of whom are familiar with network research, with what the different centers of excellence can do, and with the cultures of the different communities of researchers.
The council would be given priorities based on the Army’s R&D investment strategy, most likely developed by the Deputy Assistant Secretary of the Army for Research and Technology. It would be given authority to cut through red tape and manage both the process and the networked community of contributors.
|
4 |
For further information, see NCEnet spring 2004 issue, available at http://www.nce.gc.ca/pubs/ncenet-telerce/spr2004/newsletterspr04_e.htm. Accessed August 19, 2005. |
Furthermore, the Army should develop mechanisms for encouraging and recognizing the best and most relevant research. This would involve attracting talented researchers and providing for a constant stream of challenging projects. For continuity, the military officers on the council would be designated “warfighting R&D professionals” and set on an appropriate career path that allows them to develop the next-generation concept of virtual centers of excellence that can meet the Army’s critical needs in network science in a short but realistic time frame.
The next-generation model for network science R&D is depicted in Figure E-1. This figure shows the conceptual relationships between the Army coordinating council, university centers of excellence, and industry consortia as described above.
In summary, the next-generation R&D model outlined in this scenario is a new and different approach based on the proven experience of networked organizations like eBay, Intel, and GE. It is based on principles that have worked for many successful companies that needed to get quality products and capabilities to market quickly: Think Big, Start Small, Scale Fast, and Deliver Value. It is this type of next-generation model that can deliver the knowledge, research, and technology that will enable the nation’s warfighters to win its wars.
For this approach to work requires strong commitment from the Army and DOD senior leadership and their partners in industry and academia. A small team of the best and brightest Army warfighting R&D specialists committed for 3–4 years and working closely with industry and academia would not only contribute to accelerating the development of the field of network science but also contribute to the prompt and cost-effective delivery of effective NCO capability (DOD, 1999). The Army has an opportunity to assume leadership in developing and implementing this new model. In DOD, NCO must be a joint effort, and so should the new R&D model—after it has been proved in the Army. By moving aggressively to implement this model, the Army can establish itself as the lead in DOD and seize the opportunity to make a significant contribution toward improvement of joint network-centric warfighting capabilities.
The statement of task requests the committee to “identify specific research issues and theoretical, experimental, and practical challenges to advance the field of network science.” Briefly stated, one such issue (and major challenge as well) will be to obtain value from the investments that the Army does make to advance network science. In the case of basic research (6.1) alone, relevant challenges are identified in Scenario 1. In the case of the combined basic and applied research (6.1–6.3) projects envisaged in Scenario 2, the challenges depend sensitively on the topics of the research.
To illustrate the scope and scale of next-generation R&D projects with market-driven management, three projects involving the sociological, engineering, and biological areas of network applications were developed by members of the committee as sample projects and are described in following sections.
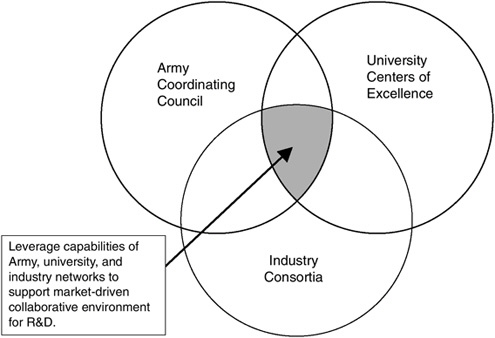
FIGURE E-1 Schematic depiction of next-generation model for Army R&D showing the relationship between the main entities in this model.
Sociological Research: Local Decision Making in a Networked Combat Environment
When network-centric operations are conducted in the field, it is envisioned that squads, platoons, and companies will have access to communications capabilities that provide them with common situational understanding, a common operating picture, information necessary for rapid decision making, and ready communications directly with their commanders and peers. Operations like ground targeting for precision aerial bombardment require that specific items of information be made accessible to specific elements on (or above) the battle. Experiments have been conducted to determine whether access to this information actually increases combat effectiveness, and if it does, how. This proposal is for an exploration of decision making in an information-rich combat environment via the design and conduct of field tests to assess how Army personnel might adapt their processes for searching for information and for decision making to make optimal use of newly acquired information resources.
This problem is of profound interest to the Army because an understanding of the impact of incremental increases in information resources on the search and decision making processes of field units is central to the utilization of these resources to improve the combat effectiveness of these units. This is especially true if the units are expected to fight under nontraditional circumstances like urban guerilla combat.
The proposed approach to this problem is to extend and to adapt current models of networked group decision making to examine how the availability of NCO capabilities might modify the decision-making processes used by combat units in the field and hence the effectiveness of these units (Watts, 2003). The current models apply more to simpler, more generic situations than to the complex situation of decision making in combat. Thus, three lines of investigation would be initiated. First, extensions of the models would be examined to assess the extent to which they can be applied to social situations characterized by information exchange between remotely located small groups collaborating to reach a joint decision. Second, examples of specific unit decisions in field situations would be reviewed to assess if a subset of the decisions could be isolated and subjected to the discipline of constructing validated models. Third, the availability and accessibility of NCO information in field settings would be explored to assess the types and amount of information that realistically could be expected under combat situations. Following these initial lines of investigation, an assessment would be made of the feasibility of combining the results to design and field test a revised set of decisioning processes that showed promise of using the available NCO information assets to improve combat effectiveness. At this stage a decision would be made on whether the prospect of useful results was good enough that the project could usefully be scaled up to support an actionable technology investment option to develop elements of training modules or specifications for the user interface to and functionality of NCO capabilities.
The committee envisages that the models would be constructed and exercised by leading university groups. Their test and validation by means of field experiments and simulations would be performed at Army facilities using primarily Army personnel. These two groups must work together intimately, because the current state of the art in modeling obviously does not extend to the complexities of realistic combat decisioning. Therefore, success of this project depends on an exceptional level of creativity both in the extension of current models and in the identification of specific field-relevant situations in which they could reasonably be tested.
The responsibilities of the university personnel would be to explore the range of behaviors described by current models and their extensions and to work with Army personnel to assess their applicability to unit decision making in an NCO environment. The responsibilities of the Army personnel include management of the program, collaboration with their university partners to assess the applicability of the models to NCO, design and conduct of tests, participation in the analysis and interpretation of test results, and preparation of recommendations to the Army for changes in unit organization and training processes based on the results.
The Army could make this program attractive to researchers at leading universities by making 5-year grants for the work, facilitating the participation of non-U.S. citizens, allowing for timely publication of the results of the 6.1 portions of the program, providing access to state-of-the-art computing and Web collaboration facilities, and making the competition for the grants sufficiently rigorous that only topnotch university personnel could participate.
Special capabilities that would be required include enough computer power to exercise the models adequately and simulation and test facilities for testing models of NCO information availability and usage.
This proposal envisages an intimate collaboration between Army and university personnel in all aspects of planning and executing the program. The project would start with a workshop in which the goals and approach of the project are defined and procedures for collaboration clarified. The principal university personnel involved would be expected to devote at least 3 months each year to the project, with up to a full year temporary assignment possible during the conduct of the experiments. Army personnel would be made available to give participating university groups extended briefings on the realities of decision making under combat conditions. Efforts would be made to keep the assignment of the leaders (both Army and university) of the program stable so that good personal and professional relationships would be established.
This project is expected to differ from traditional Army 6.1 programs in focus, intensity, and style. It would construct, validate, and refine models of combat decision mak-
ing in an NCO environment that would be usable by the Army in determining the kind of information that is needed and in training Soldiers. The research is expected to be performed in the manner of a team social network, and the project would be intense enough to require full-time involvement of participants for extended periods. The university and Army partners will construct a validated model to assess if specific items of information envisaged to be available in an NCO environment can be used to create a decision-making process that demonstrably improves combat effectiveness.
The proposed project also differs from projects sponsored by funding agencies like NSF or the Department of Energy by virtue of being a basic research project in model building and validation that is embedded in a design, test, and evaluation environment that would be suitable for the observation and description of human behavior in particular network-centric operations performed by the Army.
Engineering Research: Large-Area Agent Monitoring Network
The goal of this project would be to develop and demonstrate the ability to create algorithms for communications, sensor fusion, and motion control that can maintain an accurate representation of the location, role, and intent of a distributed set of 10,000+ agents in a distributed geographic area. The sensors would range from high-resolution fixed assets (e.g., satellites), to sensors on platforms whose motion can be dedicated to data collection (e.g., unmanned aerial vehicles [UAVs]), to sensors whose motion is under limited control (e.g., sensors attached to already moving objects or fixed in place). Connectivity between the sensors varies based on local conditions: Some sensors are sporadically available, others are mostly available but moving and changing the network topology, and still others are permanently attached to the network.
A civilian example of this capability would be to maintain a dynamic population density estimate across a city the size of Washington, D.C., that is accurate to within +/– 100 people per square kilometer and to use this information to control the flow of individuals to safety shelters inside or outside the city through a heterogeneous set of transportation systems (cars, trains, buses, walking, etc.). Sensors would include fixed sensors deployed on buildings and in public areas, mobile sensors deployed on vehicles (some of which are dedicated to collecting information, others of which have other primary tasks), and personal sensors carried by emergency personnel.
A military example of this capability would be to maintain an accurate representation of an urban area that included information on the location of (possibly moving) military assets, on the likely location of specific individuals and groups of military interest, on the status of civilian and military infrastructure (roads, communications, power, etc.), and other information relevant to a military operation. Information sources would include dedicated satellite and UAV data, sensors attached to military vehicles operating in the area, and fixed and mobile sensors (including cameras, vibration sensors, communications taps, and power monitoring equipment) placed by military personnel.
Current solutions to this problem involve either trying to centralize all information (as, for example, in an air operations center) or maintaining sparsely interconnected information sources (different military units maintain their own operating pictures, and these are synchronized at a high level and with limited fidelity). The main obstacle to better integration of information is not the communications bandwidth available, but rather our ability to design, build, and operate complex, networked systems at this scale. Traditional approaches to analyzing the dynamics and function of such networks are not likely to provide the insights necessary to design robust, scalable solutions to this problem.
One approach to solving this problem while advancing the field of network science would be to develop a sequence of annual experiments in which new methods and approaches could be tested in a highly instrumented environment, roughly like the military exercises run at the National Training Center (NTC). The Army would define and pay for running the experiments and would provide access to the data collected on various nodes. Universities and companies would demonstrate technologies at the experiments, including forming coalitions to integrate their technologies into a complete solution. A resident military group—patterned after, say, the opposing force (OPFOR) at the NTC—would role play the opposition and try to exploit the technology so that it provided incorrect information about what is going on. All data from the experiments would be made available to the research community at some point after completion of the experiments.
To implement this set of experiments, the Army would have to first identify (or construct) a site and to install instrumentation to allow monitoring of the operation. The type of facility envisaged by the committee would be similar to the Army’s NTC at Fort Irwin, which already has many of the types of instrumentation that would be required to keep track of the movement of and communications between a large number of troops operating in a military exercise.
Finally, the Army would have to develop (or contract someone to develop) a software and hardware framework that defines the interfaces to the portions of the experiment that are fixed (e.g., the vehicles, sensors, and human-interface hardware). The interface specifications and a simulation and/or test suite would be made available to all prospective participants in the exercise. These specifications should be focused on exploring the role of network effects in operations and need to represent current military capabilities, systems, or platforms.
A possible model for this framework is the Open Control Platform (OCP), developed by Boeing as part of the Software-Enabled Control (SEC) program of the Defense
Advanced Research Projects Agency (DARPA). The OCP allowed researchers from academia and industry to run a set of experiments on a test bed consisting of an F-16 and a T-33. Each research site developed its own code, then tested and verified it in simulation. Then the code was run on the experiment, with full data provided to the users at the end of the runs. Operation of the entire SEC final experiment was the responsibility of Boeing. Although this program was much smaller in overall scope than what the committee is proposing here, it provides one example of how to allow many users to access a common test facility.
The experiments must be sufficiently large and complex that a systems-level approach is required to succeed. The committee anticipates that an experiment would involve between 10 and 100 vehicles, hundreds of troops (each connected to the network), and 10,000+ individual sensors and information sources. The venue of the experiment would have a like number of individual agents that needed to be tracked and characterized, as described in the civilian and military applications above.
The participants would be teams of researchers, technologists, and engineers from academia and industry. University researchers would provide new ideas for methods to integrate information, implemented as protocols, algorithms, and theory. They would develop software for communication protocols, sensor fusion, control, etc. Industry would be responsible for overall systems integration as well as implementation of advanced methods for information aggregation in a networked environment. The Army would manage the operation but also insert new technologies from Small Business Innovation Research (SBIR) and other entities receiving 6.2 funding under their control. Several recent examples of such programs, such as the DARPA SEC and Bio-Spice programs, could be used as models for how the teams would work together.
The program would be structured to attract participants. The availability of large-scale experimental infrastructure and data sets for further research would motivate participation by universities, since this capability would be well beyond what is typically available in an academic environment. It would also be important to provide a mechanism for long-term support of fundamental research in network science, perhaps by engaging a dedicated set of researchers to study the overall experiment and provide a running assessment of the adequacy of the science to explain the results of the exercise. In addition to allowing exploration of engineering aspects of network science, this type of environment could also be used to explore the social aspects of networks in military operations—for example, the impact of changes in the network on the tactics used by friendly and enemy units.
Biological Research: Field Biological Threat Assessment
Military personnel are deployed widely in different areas of the globe, are exposed to the different environments and diseases at these locations, and are then, often quickly, redeployed elsewhere in the world. In addition, there is a threat of directed biological attack on the force during combat. These intense conditions can lead to the rapid infection of troops and the spread of agents across the world if not immediately detected and neutralized. Such a threat is also encountered in civilian situations, where economic needs might drive the invasion of remote locations, such as biologically diverse rain forests to collect medicines or wilderness area to drill for oil. Other such situations might entail the exchange of bacterially and virally dense sea waters through ballast uptake and dumping by commercial or tourist ships. Each of these cases involves the introduction of infective biological systems from once-isolated remote locations to places where individuals have not built immunity to them.
The mobility of the military, or even civilian, participants means infections could be brought from the site of interaction to the wider community. Avian influenza provides a prime illustration of the danger posed (see Box E-1) and underscores the importance of having in place a well-informed surveillance and decision structure to detect and respond to emerging biological threats.
The goals of this project would be to develop a focused capability to monitor the biological load of troops prone to rapid redeployment, to demonstrate a capability to detect and identify the source of new biological threats to soldier health, and to provide recommendations for the control of such threats to individuals and populations. A longer term goal would be to turn this information into sufficient knowledge about the biological organism at the molecular level to allow rapid development and deployment of pharmaceutical solutions. For the purposes of this report the committee uses as examples existing viral threats such as human immunodeficiency virus (HIV-1), influenza, and West Nile virus and the emerging threat of avian flu. Similar considerations apply, however, to bacterial threats such as anthrax, tularensis, and leishmania (a particular problem in the Middle Eastern theater).
This overall assessment effort would require a network of monitoring stations reporting on samples from the environment and patients, looking for prevalence of the threat agent and patient response to the agent in terms of morbidity and virulence indices. Agents would be rapidly sequenced and typed. These sequences would be related to their virulences and used to track the spread of a particular strain from location to location. Models of the viral infection and transmission process based on the sequence and prior measurements of similar strains would inform network models of the spread and mutation of these viruses. These models, in turn, would enable rapid risk assessments when an infection appears at a given site.
This biology project links with the social and engineering network sample projects presented above. Data from arrays of sensors in the environment and on individual soldiers would need to be fused into a database of biological and
|
BOX E-1 Avian influenza is an infectious disease of birds caused by the Type A strain of influenza. Nearly all birds are susceptible to it, and different strains have widely differing virulences, with some strains being highly contagious and able to cause severe symptoms, death, or dangerous epidemics. There are at least 15 subtypes of avian influenza that provide an extensive pool of virus. Contact between domestic and migratory birds transmits and mixes these pools, and research has shown that even viruses of low pathogenicity can, after circulating for only a short time, mutate into highly pathogenic viruses. Early detection of these virulent strains and strict quarantine are the most effective means of control. Good sanitation helps in prevention, but virus can exist in the environment for long periods, especially in cold regions. In the absence of prompt control measures backed by excellent surveillance, epidemics can last for years. One of the most worrisome aspects of these viruses is their ability to efficiently recombine their genetic material with that of other viruses to cause an antigenic shift, creating variants less likely to be halted by the immune systems of the birds. These viruses rarely hop species (except to pigs), but there have been a number of recent cases of the avian flu hopping from birds to humans. These cases are so disturbing that a 1997 outbreak of one highly pathogenic strain (H5N1) in Hong Kong poultry that directly spread to 18 humans, 6 of whom died, caused the government to destroy within 3 days the entire poultry population of 1.5 million birds. This action likely averted a large-scale spread to humans and a pandemic. The infected persons were often otherwise healthy, and there seemed to be no age preference. Since then there have been a number of other outbreaks in southern China, Viet Nam, and Korea. The H5N1 strain is of particular concern because it has a propensity to acquire genes from viruses that infect other animal species, increasing the probability that these new strains might become virulent to humans. Testing and diagnosis for the virus is rapid and reliable, and treatment is the same as for human flu. Vaccines can be effective, although only temporarily. Antivirals often work, but they are expensive and in short supply. The upshot is that rapid detection, estimation of the threat, and good command and control, such as was demonstrated in the Hong Kong poultry massacre, are important means for containing this possible source of pandemic. SOURCE: Adapted from a document found at http://www.who.int/csr/don/2004_01_15/en/. |
geographical information. This database would be provided with analytical and decision management tools that assess the risk associated with detection of a new strain of virus or infection event. The information would need to be coordinated from forward field laboratories to commanders responsible for combat operations, especially troop deployment.
A pilot study in this area would be designed to cooperate with Marine and U.S. Navy SeaBee medical aid stations (MASs) already engaged in disease and noncombat illness surveillance, as well as with the global disease tracking efforts of the Centers for Disease Control (CDC) and the World Health Organization (WHO). The MASs could be charged with monitoring soldiers for a panel of viral species and would be outfitted to rapidly sequence isolates. Perhaps a field team would be dispensed to sequence similar viruses in local fauna and environments. Sequences would be filed in databases along with soldier data (health and some form of identifier for tracking where individuals are stationed and how they are moved from place to place). These databases would be integrated with, for example, the influenza database at Los Alamos National Laboratory.5 A university team would work on relating sequence, virulence, and geographic information into a model of the sequence determinants of different virulence and epidemiological parameters, such as transmissibility and the rate of mutation. Working with a DOD team, the university team would develop structured epidemiological models of the spread and of new viral infections in the troop population based on models of troop movement and the viral dynamics. An Army team would then focus on modeling decision processes under different scenarios in order to optimize containment of any viral threat.
This project involves four major challenges: (1) choosing the scale, breadth, and accuracy of the data needed for construction and parameterization of the network models, (2) developing a modeling framework relating data at the viral sequence level to the level of whole populations of infected individuals, (3) creating modeling tools that take into account the unique ability of live biological threat agents to adapt to and mutate around human interventions, and (4) developing a decision support model that prescribes an effective course of medical and social intervention to quell a possible viral outbreak. This work faces the challenges generally faced by multimodal, multiscale network analysis—how to place the sensors (in this case medical and environmental surveillance); how to fuse their information into network models at both the epidemiological and molecular
|
5 |
For further information, see http://www.flu.lanl.gov. Accessed August 19, 2005. |
levels; and how to use these network models to direct distribution of resources and to design interventions—and requires network science at all scales. Since coordination and communication among the teams is paramount to the success of a project at this scale, the online infrastructure and computational resources would be an early focus.
An initial coordination team would identify the key existing infrastructure for achieving the project goals and would establish contact with the requisite field sites and field military personnel. The team would develop a knowledge of the key data trackers in the WHO and CDC. It would identify candidates to participate in the program. Key government players and invited participants would attend a workshop to discuss what technology, resources, and organization would be necessary for success of the program. A subset of this group would form a project team and create the final 5-year project design. Dedicated team leaders would be chosen from the Army, other government agencies, and nonmilitary research groups.
The scale of the work, the diversity of participating agencies, and the use of military field data make this a project outside the scope of most funding agencies. The committee expects that the basic science to be accomplished as well as the important societal and military applications would make this project attractive to the scientific community at large.
SCENARIO 3, CREATING A ROBUST NCW/NCO CAPABILITY
The statement of task instructs the committee to “recommend those relevant research areas that the Army should invest in to enable progress toward achieving network-centric warfare capabilities.” When the committee examined the literature on this topic from the DOD OFT, it discovered that the concept of “network-centric warfare” had been superseded by the concept of “network-centric operations,” as described in a conceptual framework document published on the OFT Web site6 (Cebrowski and Garstka, 1998; Garstka and Alberts, 2004). In interviews and discussions with representatives of the Army and DOD, committee members learned that opinions on NCW and NCO varied widely and were substantial, not just a matter of nomenclature. Moreover, the literature on the topic is dynamic, with new reports and publications frequent. Since this report is intended as an archival document, the committee elected to use the published conceptual framework description version 2.0 (Garstka and Alberts, 2004) as its point of reference.
In Scenario 3, the committee adopts a national point of view. Its purpose is to ask what the nation must do if the strategic vision of NCO is to become a reality. Investment in research by the Army is a part of Scenario 3, albeit a modest one.
Transforming the U.S. military from its current state to that envisaged for NCO, as described by Garstka and Alberts (2004), is probably the most complex undertaking in the history of the U.S. government. Its achievement would arguably be comparable to the successful pursuit of World War II or the cold war with the Soviet Union. It is a long-term, difficult, costly, and risky undertaking. It is not clear to the committee that the difficulty, cost, and risk associated with this notion have been communicated effectively to the senior management of the Army and DOD. In Scenario 3, the committee emphasizes the magnitude of the undertaking and sets forth the view that significant new activities will be required to accomplish it.
Think first of designing the most complex weapons system yet: say, a large aircraft carrier. Add to this the complications in the physical domain associated with, for example, secure, reliable wireless communications via satellite to soldiers on a mobile battlefield. In the information domain, add the hardware and software challenges associated with storage, search, and retrieval of orders of magnitude more data than have ever before been processed in real time, as well as the challenges associated with ensuring the security and reliability of these data. In the cognitive domain, add issues associated with processing information from all three services by a junior officer at a local (mobile) workstation. In the social domain, add the complications of orchestrating the decision-making process in this information-rich, real-time environment and the issues associated with tactics and training to use all this information-processing capability. In all seriousness, the challenge seems more like science fiction than like science and technology that can be delivered up by the R&D operations of the military services as currently constituted or even by commercial R&D.
The committee regards it as highly unlikely that existing methods of designing and procuring weapons systems will be adequate to accomplish this monumental undertaking. Current experience in the services themselves supports this point of view (Brewin, 2005). The committee regards the task of converting the current state of the U.S. military to the vision articulated for NCO as vastly more challenging than seems to be appreciated.
Not only is the task dauntingly complex, the knowledge necessary to accomplish it does not even exist. In similar cases—the Manhattan Project and the initial days of NASA come to mind—a focused, long-term national initiative was required, and it seems likely that something similar will be required in this case also. Thus, in Scenario 3 the United States undertakes a focused national initiative, comparable in scope to the Manhattan Project, to design and deploy NCO capabilities as described in the conceptual framework document version 2.0 for all the military services during the coming decade.
|
6 |
For further information, see http://www.oft.osd.mil/. Accessed August 19, 2005. |
Insights from Network Thinking
What insight does network thinking offer on this subject? First, a network organization (as opposed to a hierarchical one) is required because the organization must learn how to do the job on the job.7 A critical function is specifying the architecture of the interacting networks in the various domains, setting the interfaces between them, and monitoring successive waves of implementation to ensure consistency and learning. This could be accomplished by a senior executive office that also managed the program itself. Underneath this top layer of the network is a project management layer responsible for converting the architecture into a series of projects that implement and test various elements of the architecture. Think of this layer as the middleware of the organization. Beneath this is a network layer of vendors and military logistic organizations that provide and source the material for operational commands. A model for the vendor organization might be Sematech. A model for the logistics organization might be the nuclear Navy. The important points are that a new network organizational structure and work process is required to create a capability of this complexity and that the scale of the activity is larger than the Army alone; it must be national, or at least DOD-wide.
Another insight is that the design and implementation of NCO capabilities are on the same scale and of the same complexity as their use. The same principles of better, faster decisions by means of information sharing apply. Thus, the environment in which the capabilities are designed can be regarded as a test bed for many of the expected capabilities themselves in the information, cognitive, and social domains. Taking advantage of this insight could make the overall job less onerous and should be an explicit consideration in initiatives to create NCO capabilities.
Synopsis
The committee was not tasked to resolve the issues raised in Scenario 3 but considers their resolution to be of paramount national urgency. The committee stresses that the knowledge of networks that we possess today is not adequate to design predictable, secure, robust global networks. Members heard presentations and read reports on how the “transformation” to a future force capable of NCO is not likely to be achieved by traditional approaches to creating technology. They came to recognize that the policies and practices currently used to procure these capabilities do not take into consideration the uncertainties inherent in the current state of understanding the design and implementation of complex networks. The purpose of Scenario 3, then, is to emphasize that the task of designing, testing, and operating the envisaged NCO capabilities is of an exceedingly high order of complexity and should be approached as seriously as the Manhattan Project or NASA’s race to the moon.
The committee would be remiss in its responsibilities if it failed to note the essential urgency and profound difficulty of this task. The chances of delivering NCO capabilities in a timely and affordable way would be greatly increased by a focused national initiative combining the initiatives of all services under central leadership, to respond successfully to the diverse challenges of future warfare.
REFERENCES
Albert, R., and A.L. Barabási. 2002. Statistical mechanics of complex networks. Review of Modern Physics 74(1): 47–97.
Albert, R., H. Jeong, and A.L. Barabási. 2000. Error and attack tolerance of complex networks. Nature 406(6794): 378–382.
Almaas, E., B. Kovacs, T. Vicsek, Z.N. Oltvai, and A.L. Barabási. 2004. Global organization of metabolic fluxes in the bacterium Escherichia coli. Nature 427(6977): 839–843.
Amaral, L.A.N., A. Barrat, A.L. Barabási, G. Caldarelli, P. De Los Rios, A. Erzan, B. Kahng, R. Mantegna, J.F.F. Mendes, R. Pastor-Satorras, and A. Vespignani. 2004. Virtual roundtable on ten leading questions for network research. European Physical Journal B 38(2): 143–145.
Anderson, R.M., and R.M. May. 1992. Infectious Disease of Humans: Dynamics and Control. Oxford, England: Oxford University Press/Oxford Science Publications.
Arquilla, J., and D. Ronfeldt. 2001. Networks and Netwars: The Future of Terror, Crime, and Militancy . Santa Monica, Calif.: RAND.
Barabási, A.L. 2003. Linked. New York, N.Y.: Plume, a member of the Penguin Group, Inc.
Barabási, A.L., and Z.N. Oltvai. 2004. Network biology: Understanding the cell’s functional organization. Nature Reviews: Genetics 5(2): 101–114.
Barrat, A., M. Barthélemy, R. Pastor-Satorras, and A. Vespignani. 2004. The architecture of complex weighted networks. Proceedings of the National Academy of Sciences of the United States of America 101(11): 3747–3752.
Ben-Naim, E., H. Frauenfelder, and Z. Toroczkai. 2004. Complex Networks. New York, N.Y.: Springer-Verlag.
Bornholdt, S., and H.G. Schuster, eds. 2003. Handbook of Graphs and Networks: From the Genome to the Internet. Weinheim, Berlin: Wiley-VCH.
Brewin, R. 2005. DOD Mulls Network Coordination. Available at http://www.fcw.com/article88939-05-23-05-Print/. Accessed May 31, 2005.
Cebrowski, A., and J. Garstka. 1998. Network centric warfare. Proceedings of the United States Naval Institute 24: 28–35.
Cohen, R., K. Reez, D. Ben-Avrahan, and S. Havlin. 2000. Resilience of the Internet to random breakdowns. Physical Review Letters 85(21): 4626–4628.
Cohen, R., K. Reez, D. Ben-Avrahan, and S. Havlin. 2001. Breakdown of the Internet under intentional attack. Physical Review Letters 86(16): 3682–3685.
Department of Defense (DOD). 1999. DOD Financial Management Regulation Volume H.
Dodds, P.S., and D.J. Watts. 2004. Universal behavior in a generalized model of contagion. Physical Review Letters 92(21): 218701.
Dodds, P.S., and D.J. Watts. 2005. A generalized model of social and biological contagion. Journal of Theoretical Biology 232(4): 587–604.
Dodds, P.S., D.J. Watts, and C.F. Sabel. 2003. Information exchange and the robustness of organizational networks. Proceedings of the National Academy of Sciences of the United States of America 100(21): 12516–12521.
Dorogovtsev, S.N., and J.F.F. Mendes. 2003. Evolution of Networks: From Biological Nets to the Internet and WWW. Oxford, England: Oxford University Press.
Garstka, J., and D. Alberts. 2004. Network Centric Operations Conceptual Framework Version 2.0. Vienna, Va.: Evidence Based Research, Inc.
Gladwell, M. 2000. The Tipping Point: How Little Things Can Make a Big Difference. New York, N.Y.: Little, Brown and Company.
Helper, S., J.P. MacDuffie, and C. Sabel. 2000. Pragmatic collaborations: Advancing knowledge while controlling opportunism. Industrial and Corporate Change 9(3): 443–483.
Huckfeldt, R., P.E. Johnson, and A. Sprague. 2004. Political Disagreement: The Survival of Diverse Opinions within Communication Networks. Cambridge, England: Cambridge University Press.
Katz, E., and P.F. Lazarsfeld. 1955. Personal Influence: The Part Played by People in the Flow of Mass Communications. Glencoe, Ill.: Free Press.
Newman, M.E.J. 2003. The structure and function of complex networks. SIAM Review 45(2): 167–256.
Newman, M.E.J., A.L. Barabási, and D. Watts, eds. 2005. The Structure and Dynamics of Networks. Princeton, N.J.: Princeton University Press.
Pastor-Satorras, R., and A. Vespignani. 2004. Evolution and Structure of the Internet: A Statistical Physics Approach. Cambridge, England: Cambridge University Press.
Rogers, E.M. 1995. Diffusion of innovations. New York, N.Y.: Free Press.
Surowiecki, J. 2004. The Wisdom of Crowds: Why the Many Are Smarter Than the Few and How Collective Wisdom Shapes Business, Economies, Societies and Nations. New York, N.Y.: Doubleday.
Tanenbaum, A.S. 2003. Computer Networks, 4th edition. Upper Saddle River, N.J.: Prentice Hall PTR.
Watts, D.J. 2002. A simple model of information cascades on random networks. Proceedings of the National Academy of Sciences of the United States of America 99(9): 5766–5771.
Watts, D.J. 2003. Six Degrees: The Science of a Connected Age. New York, N.Y.: Norton.
Watts, D.J. 2004. The “new” science of networks. Annual Review of Sociology 30(1): 243–270.
Weiner, T. 2005. “Drive to build high-tech Army hits cost snags.” New York Times, March 28, 2005.














