3
Framework for Assessing Concern About Synthetic Biology Capabilities
The U.S. Department of Defense asked the National Academies of Sciences, Engineering, and Medicine to “develop a strategic framework to guide an assessment of potential security vulnerabilities related to advances in biology and biotechnology, with a particular emphasis on synthetic biology.” In public meetings, Department of Defense representatives clarified that the primary purpose of the framework was to serve as a tool to aid the consideration of the relative level of concern indicated for current and future synthetic biology–enabled capabilities. It was determined that the framework needed to be flexible enough to be applied in a variety of circumstances and for a variety of purposes, such as: analyzing existing capabilities to evaluate the level of concern indicated at present; understanding how various capabilities compare to, interact with, or complement each other in terms of their level of concern; identifying key bottlenecks and barriers that, if removed, could lead to a change in the relative level of concern; evaluating the change in the level of concern warranted when new experimental results are reported or new technologies arise; and horizon-scanning to predict or prepare for potential future areas of concern. This chapter describes the development of the framework and how it was used to facilitate an expert-based qualitative ranking of capabilities based on a well-defined set of factors to capture relative levels of concern.
APPROACH TO DEVELOPING THE FRAMEWORK
The process used to develop the framework generally followed best practices in expert elicitation and elicitation of attributes and value functions for multiattribute modeling (Morgan and Henrion, 1990; Clemen, 1991; Keeney, 1992; Keeney and Raiffa, 1993). First, the existing frameworks listed in Appendix B were reviewed, along with other published literature, to develop a list of factors that have been identified as being relevant to assessing concerns about the use of synthetic biology. A number of different frameworks have been developed to assess concerns associated with emerging technologies. In biology, these frameworks have typically assessed concerns based on features and capabilities of the biotechnology itself, particularly the capabilities the technology may provide to someone who would wish to create harmful biological entities for a specific malicious use. Some frameworks also consider the severity of potential adverse outcomes and the ability to manage them through detection, mitigation, or attribution. Other work has focused on assessing concerns associated with particular types of experimentation
that may provide generalizable features applicable to a broader set of technological dual-use concerns.1 Another framework approach, typically employed by security groups, is to use scenario-based assessments to identify potential vulnerabilities and the potential ways to mitigate them. Often referred to as “red-teaming,” this approach uses vignettes to describe details of a hypothetical scenario such as specific agents, actors, and affected populations. Although this approach can be informative, some scenario-based frameworks are hampered in the context of biodefense by a lack of evidentiary case studies and by the fact that one can come up with an almost limitless list of malicious activities that could potentially be pursued with biology (Lindler et al., 2005), and so the work is, by definition, never complete or comprehensive.
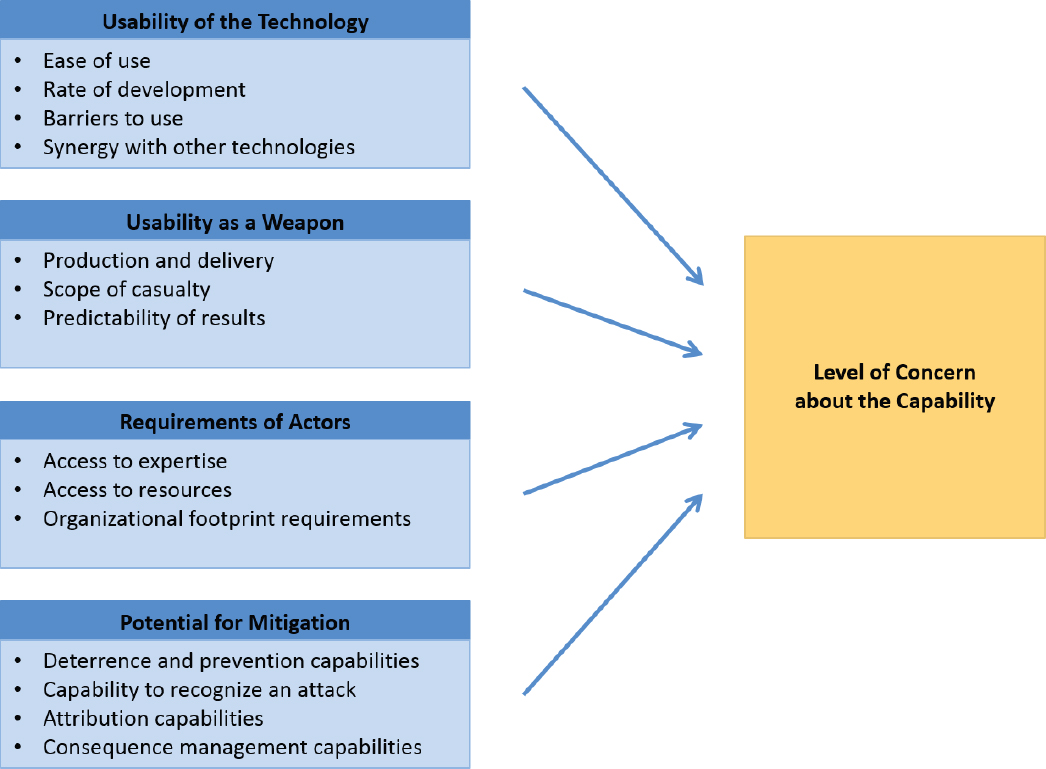
This review of the literature was followed by a process to identify terminology, factors, and approaches that resonated most within the context of the study charge. The outcomes of that process were formalized into a set of factors and elements within each factor, summarized in Figure 3-1 and described in more detail below.
___________________
1 As defined by the National Science Advisory Board on Biosecurity, “Research yielding new technologies or information with the potential for both benevolent and malevolent applications is referred to as ‘dual use research.’” See https://osp.od.nih.gov/biotechnology/nsabb-faq. Accessed November 15, 2017.
These factors delineate the information that would be used to assess the level of concern for particular synthetic biology–enabled capabilities.
Developing quantitative or fixed scales for these factors was not attempted, nor was there an attempt to weight the factors relative to each other in terms of importance or impact on level of concern. Many of the factors and their descriptive elements are interdependent in that they capture ideas that are similar to or overlap with other factors and descriptive elements and are thus correlated with each other, requiring complex considerations for quantification. Instead, a qualitative approach was taken, using the factors and their descriptive elements to guide discussions and inform the assessment of relative level of concern for various synthetic biology capabilities. The assessment of each individual capability then fed into a holistic, relative ranking of the capabilities in terms of level of concern, similar to the methodology used in other studies (Morgan et al., 2001; Willis et al., 2004, 2010).
FACTORS FOR ASSESSING CONCERN
The framework for assessing concern consists of four factors, along with descriptive elements within each factor, as represented in Figure 3-1. The factors are usability of the technology, usability as a weapon, requirements of actors, and potential for mitigation. Conclusions about the relative level of concern about any particular synthetic biology capability are influenced by these four factors; in other words, capabilities that have lower technical barriers to use, more qualities that would enable use as a weapon, low actor requirements in terms of expertise or resources, and a low likelihood of mitigation would be of relatively more concern than capabilities for which there are high technical barriers to use, fewer qualities that would enable use as a weapon, high actor requirements in terms of expertise and resources, and a high likelihood of mitigation. As represented in this framework, those are the two extreme ends of the spectrum of concern. To complement and expand on the factors and descriptive elements, Appendix C lists illustrative questions that arose during the study process that can help facilitate the use of the framework.
Usability of the Technology
Biotechnology is a fast-moving field, and in some ways, synthetic biology is accelerating and broadening the usability of tools to achieve various capabilities. The first factor in the report’s framework, usability of the technology, captures the idea that as tools become more usable, they become more accessible to more people, and therefore the concern about them being deployed for malicious use increases.
Four main elements were included in this study’s assessment of the usability of technologies: ease of use, rate of development, barriers to use, and synergy with other technologies. Rather than attempting to formally score each of these elements for each capability analyzed, these elements were incorporated into one overall assessment of the usability of the technology for each capability considered.
Ease of Use
If a technology is easier to use, it is more likely to be used. Technologies that are in common use are likely to be more accessible and therefore more vulnerable to misuse, though it is also important to consider how outdated or less frequently used technologies may still be exploited for harm.
Advances in technology have made it easier to perform such tasks as creating single-nucleotide modifications and adding genes. Applications that employ combinatorial approaches to generate and test multiple design variants often involve complex work at large scales—as well as a high degree of unpredictability—thus putting them at the more difficult end of the spectrum. The availability of detailed information about a specific gene or pathway of interest also affects how easy or hard it is to use available technologies to manipulate that gene or pathway. These are the types of considerations that analysts can use to determine how much concern is warranted based on the ease of use of the technologies needed for a given application.
Rate of Development
All technologies follow some form of development curve over time. Technological capabilities that are developing rapidly are generally of more concern than those that are still far off in the future. If there is a known commercial use for a technology, private-sector investments may accelerate the rate of development, while technologies that do not have an identified commercial value may follow a slower path, advancing through smaller, disconnected efforts and public funding. Novel technologies may be characterized by rapid improvements in accuracy and throughput as their developers try to establish new markets or compete in existing ones. Technologies that have filled a unique market niche may survive for a long time with only minor improvements in scale or reductions in cost (e.g., the polymerase chain reaction, or PCR, has been in use for decades), while other technologies lose their prominence after being displaced by innovations (e.g., next-generation sequencing, also known as high-throughput sequencing, allows large numbers of genetic sequences to be determined far more rapidly than previous sequencing technologies and is expected to replace older technologies in some molecular identification applications).
Technologies for the synthesis of ever-larger DNA constructs are currently evolving rapidly, as are technologies for editing genes and genomes. For example, it is expected that the synthesis of all chromosomes from one strain of yeast is nearing completion. The engineering of plants to produce raw or finished chemical products is another area that is maturing rapidly. Assessing the degree to which the rate of development affects the level of concern warranted for a given use of technology should include consideration of both the pace of the technology’s evolution and the speed with which it is being adopted.
Barriers to Use
It is also important to consider the presence of significant bottlenecks or barriers, which can lower the likelihood that a technology will be used. For example, key gaps in one aspect of the Design-Build-Test (DBT) cycle, such as Design knowledge, can significantly limit the potential for malicious use of a given technology and consequently lower the level of concern related to how that technology might be used in another phase of the DBT cycle, such as Build. Identifying barriers can also provide insight into potential rapid changes in what may be achievable once those barriers are overcome. This is an especially important consideration in areas of synthetic biology with strong drivers (e.g., beneficial uses attracting significant research) that are pushing the barriers to be broken. Major technological leaps have the potential to change synthetic biology quickly and open up new possibilities; for example, Gibson Assembly® (Gibson et al., 2009) led to a sea change in the ability to compile genetic fragments.
Synergy with Other Technologies
Some technologies may be substantially enhanced by synergies with other technologies, leading to higher level of concern for the capabilities they may enable. For example, CRISPR/Cas9 can be used alone to make a specific modification to a targeted gene. But when CRISPR/Cas9 is coupled with emerging technologies for single-cell sequencing, it is possible to create random libraries of CRISPR/Cas9 guide RNAs, apply them in parallel to single cells, subject the cells to environmental pressures, and use single-cell next-generation sequencing to identify the “winners” (Datlinger et al., 2017)—a far more complex proposition than could be achieved with CRISPR/Cas9 alone.
In the field of computing, the semiconductor technology evolution has brought ever-greater computing power and data storage at ever-lower costs. At the same time, the evolution of networking technology has converged with computing to make computing more ubiquitous, powerful, and inexpensive, thanks in part to a concerted effort to identify and overcome bottlenecks and barriers in both computing and networking. Synthetic biology and sequencing technology may well show a similar convergence in the coming years, in which advances in annotation and predictable sequence-structure-function relationships lead to the ability to reliably design increasingly complex biological systems (Brophy and Voigt, 2014; Chao et al., 2015).
Such developments would have implications for both beneficial and malicious uses of synthetic biology
technology. In determining the level of concern warranted for any given capability, it is useful to consider how synergies among relevant technologies may create opportunities for new types of applications in the future. It is also useful to consider how a breakthrough relevant to one aspect of the DBT cycle might synergize with technologies relevant to other aspects to enable applications that were not previously achievable.
Usability as a Weapon
A central question is whether a capability enabled by synthetic biology can be used in such a way as to cause harm—that is, whether a capability can be used as a weapon. A great deal of previous work has sought to characterize what makes a substance “weaponizable” (Kadlec and Zelicoff, 2000; U.S. Congress, 2006; Carus, 2017). Drawing on that work, usability as a weapon was identified as a primary factor in the framework for assessing concerns related to synthetic biology–enabled capabilities. A capability determined to have more characteristics that make it usable in the development of a weapon warrants a higher level of concern than a capability with fewer characteristics for that purpose. In particular, the elements considered as part of usability as a weapon include implications for production and delivery of a weapon, the expected scope of casualty for a given use of technology, and the predictability of the intended results.
Production and Delivery
There are two types of questions to consider with regard to the production and delivery of weapons created with synthetic biology. They build upon a large body of existing work related to the classical understanding of the use of pathogens to create weapons of mass destruction. Previous frameworks for understanding threats related to bioweapons outline a series of key steps involved in creating a bioweapon and using it in an attack. These steps include bioagent production, stabilization, testing, and delivery (van Courtland Moon, 2006) and might include specific processes such as growing large amounts of an agent, milling it into a powder form, making the agent stable enough to be sprayed in a crop duster or withstand other means of mass dispersal, and testing its effectiveness in animal studies. These steps were considered significant barriers to the production of bioweapons in the Cold War era, in effect limiting bioweapons capabilities to a few well-resourced nation-states. In assessing the biodefense concerns posed by biotechnology, it is important to consider (1) whether synthetic biology could lower the barriers related to bioagent production, stabilization, testing, and delivery or (2) whether advances in biotechnology areas other than synthetic biology may impact the potential to weaponize products created with synthetic biology.
The first item has to do with whether synthetic biology makes unnecessary any of the classically defined steps to weaponization and thus eliminates barriers previously associated with that step. For example, synthetic biology could potentially be used to enhance existing pathogens or create new ones, but it also raises the possibility of types of attacks in which the “weapon” involved is not a pathogen per se, but a genetic construct, toxin, or other entity. Deploying such alternative bioagents might not require the same type of large-scale production or purity of pathogens required for some traditional bioweapons. In addition, synthetic biology could raise concerns about smaller types of attacks that do not require mass dispersal, which could change the equation with regard to the need for stabilization. All of these elements could potentially reduce or eliminate barriers that previously were thought to hinder the use of bioweapons, so their presence would generally increase the level of concern.
The second item relates to how advances in other areas may impact the potential to weaponize products created with synthetic biology. For example, it may be important to consider how advances in technologies such as bioreactors2 may change the nature of the production facilities required to produce harmful agents using synthetic biology.
___________________
2 Bioreactors are vessels in which biologically active substances produce substances or biological components, a type of biotechnology that is not exclusive to synthetic biology.
Scope of Casualty
The scope of casualty it is possible to generate by using a synthetic biology capability to create a weapon gives a sense of the scale of the potential threat it poses. For capabilities that could lead to a large number of people impacted and/or a severe outcome like permanent disability or death, the concern level would be higher.
Predictability of Results
Predictability of results describes the degree to which a malicious actor could be confident that the intended result will be achieved when using a given technology to develop a weapon. A higher degree of predictability would be associated with a higher level of concern. While some technologies, applications, and types of attack may require extensive testing in order to ensure the intended impact, there may be a lower barrier to success if, for example, the bioagent would only need to be produced one time to have the desired outcome, if the attacker has the opportunity to deliver the agent multiple times, or if the attacker can create many versions of the agent to maximize the likelihood of success. To assess the overall predictability of results for the malicious use of synthetic biology, it is useful to consider both a need for testing and phenotype predictability.
Testing A large-scale, long-term, and highly resourced bioweapons operation could likely be expected to perform testing prior to deployment to ensure that the scaled-up bioagent behaves as intended and that the delivery or dissemination method is functional. This process would typically involve testing in animal models to ensure illness or lethality, as well as field testing in specific environments to ensure that the agent survives well enough to persist and infect targets. In the context of a synthetic biology–enabled weapon, it is useful to consider the degree to which testing would be necessary for a given use and how this testing might be carried out. If significant testing is not likely to be necessary, the concern would be higher.
Phenotype Predictability A related question is whether the genotype of a bioagent could be predictably engineered to yield the desired phenotypes. For example, are there known engineering strategies or preexisting research that outlines methods to predictably produce the desired result? Or can the properties of a bioagent be modeled with computational tools? The ability to predictably design, model, or construct an agent could reduce the need for testing. Agents with predictable genotype-phenotype relationships may also require fewer resources to deploy, since it may not be necessary to test multiple genotypes to obtain the desired phenotype. Therefore, as phenotype predictability increases, so does the level of concern.
Requirements of Actors
Any discussion of the concerns related to the potential malicious use of a specific biotechnology needs to include consideration of requirements of the person or people who would be involved in perpetrating an attack, here referred to as actors. Actors may range from a single individual to a dedicated team to a government body. They may be amateurs, biotechnology experts, or engineers or have some other type of relevant expertise. The complexity involved in exploiting a technology (see Usability of the Technology, above) will have varying impacts on the likelihood of use and therefore on the level of concern, depending on the capabilities of the actors. For example, whereas it may be impractical (or would take an extremely long time) for an individual actor to gain the necessary capabilities and knowledge to use a given capability to cause harm, a dedicated team might have the diversity of expertise necessary to enact the same plot much more quickly.
When analyzing how the requirements of actors affect the level of concern about a given capability, it is useful to consider questions related to the expertise an actor would need to possess to effect a given attack, the accessibility of the required resources, and the organizational footprint and infrastructure that would be required.
In addition, while this study did not include consideration of the intents or actual capabilities of actors, which would likely have required access to classified information, such information could, in the future, be incorporated into an assessment of vulnerabilities to inform decision making.
Access to Expertise
Some types of applications of biotechnology require a great deal of expertise in one or more areas, while other uses may require less expertise. The degree to which expertise requirements represent a barrier to malicious use of a technology depends on the expertise possessed (or obtainable) by a malicious actor. It is important to assess the gap between the types of expertise required and the types of expertise that actors might be expected to have access to. In some cases, exploiting synthetic biology for harm may require an actor to interact with the conventional research community to acquire goods, services, or expertise, in which case the concern would be lower because this would be a barrier that may enable malicious use to be detected earlier.
Access to Resources
The particular resources needed to effect a given malicious use of synthetic biology depend on many factors. Resource requirements can include money, time, laboratory equipment and other infrastructure, reagents and other raw ingredients, personnel and expertise, and other types of resources. If more resources are needed, the concern level is decreased because that reduces the number of potential actors. If fewer resources are needed, then there is a higher level of concern.
There are multiple, hypothetical ways for an actor to obtain resources. For example, if an actor requires the use of an expensive DNA synthesizer but lacks sufficient funds to purchase a new instrument via conventional channels (or fears an outright purchase would lead to discovery), the actor may consider purchasing a used synthesizer, obtaining legitimate or covert access to equipment at a company or university, coercing an innocent person with legitimate access to perform the work (via bribing, subversion, blackmail, or threats of harm), or resorting to outright theft. A solo actor could be better funded than a group sponsored by a poor nation-state. Conversely, a poor but resourceful actor might find ways to access even highly sophisticated technologies, for example, by enrolling in a graduate degree program, getting a job in a biotechnology company, or taking advantage of relevant service providers or brokers of services. Assessing needed access to resources is not always a straightforward proposition, but it is nonetheless an important consideration when evaluating potential concerns.
Organizational Footprint Requirements
If achieving a particular malicious use of synthetic biology requires a large organizational footprint, the concern will be lower compared to capabilities for which only a small organizational footprint is needed. Some malicious uses of synthetic biology might be achievable by an individual working with basic supplies and a rudimentary laboratory, whereas other types of attacks might require a larger organization, more personnel, or more extensive infrastructure. Furthermore, considering the organizational footprint that would be required to effect a given type of attack can shed light on the relative importance of other actor attributes, such as access to resources. Organizational footprint also affects considerations related to the potential for mitigation, such as the ability to identify suspicious activity and prevent an attack or the ability to attribute an attack to the actor responsible (discussed further under Capability to Recognize an Attack and under Attribution Capabilities, below). For example, activities requiring less equipment may be able to be pursued by actors with fewer resources and may be conducted in a clandestine laboratory, making detection or attribution more difficult and therefore making concern higher. Malicious uses requiring a large organizational footprint, on the other hand, might require an actor to have access to more funding or access to legitimate infrastructure (such as by being embedded within a university laboratory), increasing the likelihood of detection or attribution and leading to a lower level of concern.
Potential for Mitigation
The impact of an attack depends both on the actor’s ability to deploy a weapon and on the target’s ability to prevent, detect, respond to, or withstand the attack. To comprehensively assess concerns, it is important to consider mitigating factors that may diminish the likelihood that a synthetic biology capability will be effectively used to cause harm or that may reduce the damage caused. Elements within this factor include the ability to deter or prevent an attack, the ability to recognize when an attack has occurred, the ability to trace an attack to the responsible actor (or “attribute” an attack), and the ability to manage the consequences of an attack. Because this factor is a core part of the framework, considerations related to the potential for mitigation were included in the assessments of specific capabilities presented in Chapters 4–6; however, significant data gathering on U.S. mitigation capabilities was outside of the study scope and the assessments presented in those chapters are intended to be illustrative and to demonstrate the assessment process rather than provide a full analysis. Mitigation capabilities are also discussed further in Chapter 8.
Deterrence and Prevention Capabilities
Various factors can affect the likelihood that a malicious actor will decide to pursue an attack and then successfully execute it. One important element that is understood to deter adversaries from pursuing some types of biological attacks is the availability of countermeasures that limit the amount of harm an attack would cause. For example, the fact that the United States has smallpox vaccine stockpiled—and would thus have a ready countermeasure against an attack using smallpox—is expected to deter malicious actors from perpetrating attacks using smallpox.
One approach that has been used as a preventive measure is the establishment of regulatory and statutory safeguards that limit the ability to access particular pathogens or technologies and use them for harm. For example, by limiting access to certain pathogens, the Federal Select Agent Program is intended to reduce the likelihood of those pathogens falling into the hands of malicious actors who might seek to use them as a weapon.
In addition, activities such as intelligence gathering can contribute to deterrence and prevention by increasing the capacity to identify suspicious activities and intervene before an attack takes place, or to catch and punish an actor after an attack has occurred, as discussed under Capability to Recognize an Attack and under Attribution Capabilities, below. Intelligence gathering allows authorities to recognize and respond to activities that may indicate that an actor is preparing for a biological attack, such as by monitoring individuals or groups with a known intention to carry out an attack, monitoring individuals or groups with access to equipment or expertise necessary to develop a bioweapon, or tracing the procurement of supplies that could be used in a biological attack. However, because biotechnology is used for so many beneficial applications and because different combinations of technologies can be used for the same or different purposes, it can be challenging to identify activities, specialized equipment, or other signatures that distinguish suspicious activity from benign activity.
Capability to Recognize an Attack
In general, there is a higher level of concern about attacks that would require some time and work to identify (as a health threat and/or as a purposeful attack) compared with attacks that would be readily recognizable. Once an attack has occurred, recognizing the emergence of an unusual cluster of disease is the first crucial step toward launching an effective response. In addition, being able to differentiate between a natural disease outbreak and purposeful use of a bioagent is vital to preventing subsequent attacks and finding the perpetrators. This knowledge also can inform how medical personnel, public health organizations, and law enforcement or military authorities act to contain the scope of the damage. Public health programs and disease surveillance systems such as those under the purview of the U.S. Centers for Disease Control and Prevention are designed to facilitate the rapid identification and characterization of known infectious disease threats as they emerge. It is important to consider how synthetic biology might affect the ability to identify suspicious activity, recognize when an attack has occurred, and identify the individuals or groups that have been targeted.
Attribution Capabilities
The ability to attribute an attack to the actors responsible is crucial to consider as part of the framework, because attribution may provide a disincentive to attacks in some circumstances. That is, actors may choose different courses of action if their actions could lead to prosecution or retaliation; thus, there is a higher level of concern about attacks that would be more difficult to attribute. Attribution considers scientific evidence, its validation, and nonscientific types of information. In the future, it may be important to consider how attacks that use synthetic biology approaches could conceivably be amenable to the development and validation of different lines of molecular evidence. Such potential opportunities are discussed in Chapter 8, such as next-generation DNA sequencing and analysis of “scars” left by engineering techniques (e.g., a remnant of a DNA vector used to insert synthetically derived biological components).
Consequence Management Capabilities
Protocols and procedures for responding to public health emergencies and to biological and chemical attacks exist in both the civilian and military arenas (CDC, 2001, 2017d). These procedures often involve, for example, epidemiological methods of identifying victims, agents, and modes of transmission, as well as activities such as the development and use of vaccines, drugs, and antitoxins to save lives. Other relevant capabilities include emergency response capacity, availability of supportive healthcare facilities, and effective procedures for isolation and quarantine. When assessing the level of concern about any particular capability, it is important to understand how that capability could change the ability to mitigate the negative impact of an attack.
APPLYING THE FRAMEWORK IN THE ASSESSMENT OF CONCERN
The framework was developed both to facilitate the analysis of synthetic biology–enabled capabilities presented in subsequent chapters of this report, as well as to aid others in their consideration of current and future synthetic biology capabilities. To support and inform the application of the framework by other parties, this section describes the approach taken to identify potential areas of concern, the steps used to apply the framework, and key considerations that guided the analysis.
Approach Taken to Identify Potential Areas of Concern
A number of technologies support various aspects of the synthetic biology Design-Build-Test cycle; selected examples are captured in Appendix A. The interim report (National Academies of Sciences, Engineering, and Medicine, 2017a) released as part of this study identified these technologies as potential items for which the framework could be used to assess concern. However, the technologies themselves pose no inherent harm, and it would generally take a collection of technologies to create a specific capability that warrants concern. As a result, this final report describes how the framework was applied to assess capabilities (rather than technologies) that potentially pose a concern because of the harm they might enable.
A list of potential capabilities to evaluate was identified by gathering a range of possibilities that have been mentioned in various venues as potential concerns associated with synthetic biology and augmenting that list with additional possibilities that had not been previously raised. These potential capabilities were grouped into categories to ensure a consistent approach to their evaluation using the framework. The following potential capabilities were analyzed (see Chapters 4–6):
- Re-creating known pathogenic viruses: Constructing a known, naturally occurring pathogenic virus from the starting point of information about its genetic sequence.
- Re-creating known pathogenic bacteria: Constructing a known, naturally occurring pathogenic bacterium from the starting point of information about its genetic sequence.
- Making existing viruses more dangerous: Creating a modified version of a known virus in which one or more traits have been altered to make the virus more dangerous (such as by enhancing its virulence).
- Making existing bacteria more dangerous: Creating a modified version of a known bacterium in which one or more traits have been altered to make the bacterium more dangerous.
- Creating new pathogens: Constructing a pathogen from the novel combination of multiple parts, which may be derived from various organisms, designed computationally, or created through other strategies.
- Manufacturing chemicals or biochemicals by exploiting natural metabolic pathways: Producing a naturally occurring product, such as a toxin,3 by engineering an organism (e.g., bacterium, yeast, or alga) to contain the known biosynthetic or metabolic pathway for the desired product.
- Manufacturing chemicals or biochemicals by creating novel metabolic pathways: Creating a new biosynthetic pathway that enables an engineered organism to produce a chemical that is not normally produced biologically.
- Making biochemicals via in situ synthesis: Engineering an organism, such as a microorganism that can survive in the human gut, to produce a desired biochemical and delivering this microorganism in such a way that it can produce and release this product in situ.
- Modifying the human microbiome: Manipulating microorganisms that form part of the population living on and within humans—for example, to perturb normal microbiome functions or for other purposes.
- Modifying the human immune system: Manipulating aspects of the human immune system, for example, to upregulate or downregulate how the immune system responds to a particular pathogen or to stimulate autoimmunity.
- Modifying the human genome: Creating changes to the human genome through addition, deletion, or modification of genes or through epigenetic changes that modify gene expression. A subset of this category is the modification of the human genome through human gene drives, the incorporation of certain types of genetic elements into the human genome that are designed to pass from parent to child during reproduction and that would spread a genetic change through the population over time.
Steps Used to Apply the Framework
The framework is designed to facilitate a thorough analysis of any particular capability by providing a set of key factors to consider and specific elements to consider for each factor. To inform decisions, however, it is useful to consider capabilities in relation to each other, that is, to assess areas of concern in relation to other potential concerns. To that end, the framework was applied using the following steps, which can be followed by other, future framework users:
- Gather and organize information about a capability in terms of the four framework factors and the elements relevant to each factor.
- Compare information about the capability to information about other capabilities to determine how the level of concern for a given capability compares to the level of concern for other capabilities.
- Consider all capabilities holistically, using the framework to inform judgments about relative levels of concern, based on all the information generated in steps 1 and 2.
Different types and levels of expertise may be required to successfully analyze the factors and elements related to any particular capability. This committee benefited from a wide range of expertise areas, including synthetic biology, microbiology, computational tool development, bioinformatics, biosafety, public health, and risk assessment.
For the first step, a qualitative approach was used to “score” each capability on each factor using a relative scale from low to high. For example, for the factor usability of the technology, the scale ranged from relatively low usability (which corresponds to relatively lower concern because it is relatively more difficult to use) to relatively high usability (which would be of relatively higher concern because it is relatively less difficult to use).
Figure 3-2 shows the first step in the process using an illustrative example. For the first capability, “Capability 1,” information associated with the elements relevant to the first factor, usability of the technology (which
___________________
3 The phrase “chemical or biochemical” throughout the report includes toxins.

includes ease of use, rate of development, barriers to use, and synergies with other technologies) was discussed and analyzed. Using that information, Capability 1 was placed on a relative scale ranging from low to high usability. Capability 1, the first capability discussed, was placed near the middle of the scale.
Next, another capability, “Capability 2,” was placed on the scale. To do this, each of the elements for the usability of the technology factor were discussed for Capability 2 and compared to those elements for Capability 1. A facilitated discussion was used to place Capability 2 on the scale relative to Capability 1 (see Figure 3-3). Note that the bar for Capability 2 is wider than the bar for Capability 1 in order to represent a broader range of concern regarding usability of the technology for Capability 2.
Each capability was considered in turn, with available information on each of the elements carefully discussed, reviewed, and compared to the corresponding elements for other capabilities, to place the remaining capabilities on the scale, as shown in Figure 3-4.
This process was repeated for each capability and each factor (Usability of the Technology, Usability as a Weapon, Requirements of Actors, and Potential for Mitigation). As the work progressed, the definitions of some of the factors and capabilities were refined, and adjustments were made to the assessments based on those refinements.
To help translate these graphics into usable information, five categories were created along the x axis: high, medium-high, medium, medium-low, and low. These categories are intended to reflect relative levels of concern,


not absolute levels of concern. No numerical scores were assigned to these categories and there was no attempt to normalize categories across factors (that is, to ensure that “medium” on one factor meant the same thing as “medium” on another factor) because such steps were not necessary for their use. Rather, capabilities were placed in the same category when they were seen as similar with regard to that factor. Not requiring the categories to have numerical meaning made it more straightforward to achieve agreement among the experts on the committee, with no loss of value in the information generated since all of the judgments were relative.
As a final step, all of this information was integrated into a holistic assessment of the relative levels of concern across the full landscape of capabilities considered. Chapter 9 presents the results of this holistic assessment (see Figure 9-1).
Key Considerations That Guided the Assessment
As described above, an expert-driven, qualitative, multiattribute methodology was used to develop the framework and apply it to assess concerns associated with synthetic biology capabilities. There are strengths and weaknesses of any methodology. The following considerations guided the assessments presented in this report and could help inform future users of the framework:
- The factors were consistently applied. Care was taken to ensure that the factors were consistently used and appropriately incorporated into an assessment of overall level of concern. Each factor was reviewed separately for each capability and the entire list of capabilities was reviewed as part of the process of determining where each one belonged on the relative scale from “lowest concern for this factor” to “highest concern for this factor.” These graphs did not have absolute values but were maintained in relative terms, so that each capability was assessed relative to the others with regard to each factor. This approach reflects the level of precision that was included in the deliberations about the capabilities.
- The final assessment incorporates a holistic evaluation. A holistic consideration of relative concern is a critical part of ensuring that the final ranking captures the full extent of the input from the ranking process. The relative placement of each capability on the scale of each factor is not deterministic of the final ranking, but rather provides consistent information to be used in making holistic judgments. The final rankings cannot be calculated based solely on the individual factor rankings since additional information may be brought to bear on that holistic judgment; the factors included in the framework are meant to inform holistic judgment, not to replace it or provide a checklist approach. However, the holistic assessment was grounded by consistent use of the factors; to maintain robustness of the factors, when a capability was placed on the scale of overall concern, it was compared to the ratings of the other capabilities already placed on the overall concern graph. For example, if Capability 1 was scored as a medium level of concern with regard
-
to usability of the technology and Capability 2 was scored as a relatively high level of concern with regard to usability of the technology, this information informed the assessment of overall level of concern about Capability 2 relative to Capability 1.
- The factor scaling approach has implications for future comparative assessments. The factors that make up the framework were constructed specifically for this study and were refined through the process of applying them to assess specific capabilities. Using a relative scaling approach allowed these definitions to be refined and aligned as the study progressed. In addition, the use of a relative rather than absolute scale for the factors means that the placement of capabilities already on the scale may need to be adjusted as subsequent capabilities are assessed. For example, if a capability is introduced that holds a much greater concern than the highest-ranked item already assessed, either the already-assessed item might need to be moved down the scale or the scale might need to be extended to allow the new capability to be ranked as “very high” concern. An alternative approach that could be used in future assessments, rather than starting with any capability and making all subsequent judgments relative to it, could be to identify the highest and lowest capabilities on each factor, assign the highest “100” and the lowest “0,” and place all other capabilities on the scale relative to those capabilities.
- Choices may need to be made to capture uncertainty and variability. In placing synthetic biology capabilities on low-to-high scales for each framework factor, placement reflected the range of potential concerns for a given capability, with particular exceptions noted in the analyses presented in Chapters 4–6. Uncertainty and variability beyond notable exceptions were captured by varying the width of the bar (see Figures 3-2 to 3-4 for notional examples), with a wider bar representing greater uncertainty or variability. During the assessment process, one case (re-creating known pathogens) initially had a very wide bar when assessing some of the factors, primarily because of the diversity of organisms that the capability included. In response, that capability was divided into two capabilities that were assessed separately (re-creating known pathogenic viruses and re-creating known pathogenic bacteria) to allow the assessment to be more precise.
- A qualitative assessment approach was used; other approaches to using the framework are possible. Methodologies for technical forecasting in emerging areas such as synthetic biology are evolving to meet the needs of decision makers. The report uses the framework to conduct a qualitative assessment; other users could choose to apply the framework in different but still meaningful ways. In the future, other users may decide to pursue a more quantitative approach to conducting the assessment or to extend the framework to incorporate sources of information outside the study’s scope (such as intelligence on actor intent or additional information on U.S. mitigation capabilities). The choice to use a qualitative or quantitative approach would be impacted by the amount and types of information available and the level of precision and understanding that would be consistent with the available information. Were a quantitative approach pursued, the framework factors and this study’s low-to-high qualitative ranking approach could be fed into that process, although interdependency among the framework factors poses challenges to the use of a simple additive multiattribute model and the use of correlated input distributions would be required. A more complex multiplicative model could be considered to account for the interdependencies, but that approach adds significant complexity. For a quantitative approach, consideration would also need to be given to appropriately representing uncertainty.
In summary, this chapter describes the development of a multiattribute framework that identifies the factors that drive levels of concern for synthetic biology capabilities (the relevant outcome). The guiding objective of this approach was to identify the features of a synthetic biology capability that would affect the level of concern about a given capability being used for harm. The resulting framework is thus intended to describe the reasoning behind what is of relatively higher concern and what is of lower concern, among the capabilities considered, and why. The framework is also intended to serve as a tool that others can use to assess relative concern, albeit not in a formulaic or checklist manner, for newly emerging capabilities and to update the level of concern for existing technologies or capabilities in response to scientific and technical advances. The use of the framework to analyze specific synthetic biology capabilities is described in Chapters 4–6. Chapter 9 discusses the overall landscape of concern and presents results of the holistic assessment across the set of synthetic biology capabilities evaluated (see Figure 9-1).
This page intentionally left blank.














