1
U.S. Army Role in Homeland Security
INTRODUCTION
The nation’s military, particularly the Army, has a long tradition of providing assistance to local, state, and federal agencies in mitigating the effects of manmade and natural disasters; providing for the public safety; and restoring essential services. In the 21st century, the scope of this mission will increase in response to the new threats and challenges. The possibility of terrorists using chemical, biological, radiological, nuclear, or high explosive (CBRNE) weapons has placed dramatic new responsibilities on the civilian emergency responder community and the military. Additionally, the potential for adverse effects of cyberattacks on the nation’s critical infrastructure has increased as the infrastructure enhances its dependence on internetted communications and digital control systems.
In response to the threats, challenges, and missions, the President has signed into law a cabinet-level department, the Department of Homeland Security (DHS). The Department of Defense (DoD) has created the U.S. Northern Command (NORTHCOM), which, among other things, will organize and employ the assets of the military when it becomes necessary to meet these challenges. The Army will play a role in the new organizational structure and in meeting the new organizational demands, but the exact role remains in a general state of flux.
It is clear that the first to respond1 to terrorist events will be the local civilian emergency responders, such as policemen and firemen. However, in
|
1 |
Appendix D provides an excerpt of the Federal Response Plan (FRP) that outlines how the federal government implements the Robert T. Stafford Disaster Relief and Emergency Assistance |
events of national significance that exceed the capabilities of the state and local authorities, the Army will most likely be called upon to assist the lead federal agency, the DHS, and the Army National Guard (ARNG) will most likely be the first Army component to assist in assuring public order, mitigating the effects of the terrorist events, and beginning the recovery for both the public and private sectors.
Finding 1-1. Homeland security is an important extension of the Army’s historical role of providing military support to civilian authorities. The Army will be called on to assist the lead federal agency, the Department of Homeland Security, in meeting a wide range of demands for consequence management and recovery of public order and critical services.
For the purposes of this report the committee is using the definitions in Box 1-1, obtained from the Department of Defense Dictionary of Military and Associated Terms (DoD, 2001).
ORGANIZATION OF THE ARMY
It is important for the reader to understand how the Army is organized and the current limitations of the Posse Comitatus Act before considering how the Army might assist civil authorities.
Organization
While every military unit in the Army is organized, trained, and equipped using a single Army standard, the U.S. Army has three distinct components:
-
The active Army,
-
The Army National Guard (ARNG), and
-
The Army Reserve (USAR).
The active Army is immediately available for use in an emergency. It has a balance of combat, combat support, and combat service support forces. The ARNG (with mostly combat units) and the USAR (with mostly combat support and service support units) are in reserve status and generally require a period of
|
|
Act to assist state and local governments when a major disaster or emergency overwhelms their ability to respond. Both the FRP (Federal Emergency Management Agency. 1999. Federal Response Plan, 9230.1-PL, April, available online at <http://www.fema.gov/rrr/frp/> and accessed on Decem-ber 3, 2002) and the Terrorism Incident Annex (Federal Emergency Management Agency. 1999. Terrorism Incident Annex, April. Available online at <http://www.fema.gov/rrr/frp/frpterr.shtm> and accessed on December 3, 2002) are important for planning purposes. |
|
BOX 1-1 Definitions Terrorism—the calculated use of unlawful violence or threat of unlawful violence to inculcate fear; intended to coerce or to intimidate governments or societies in the pursuit of goals that are generally political, religious, or ideological. Antiterrorism—defensive measures used to reduce the vulnerability of individuals and property to terrorist acts, to include limited response and containment by local military forces. Counterterrorism—offensive measures taken to prevent, deter, and respond to terrorism. |
time to activate before they become available. This period ranges widely, from a few hours to several weeks. The active Army and the USAR are considered federal forces and are at the call of the President; the ARNG has a dual status that allows state governors to use these forces without having to call on the federal government.
Posse Comitatus Act
The Army’s role in the United States is circumscribed by the Posse Comitatus Act of 1878 (PCA) (18 USC 1385), which, as a general matter, prevents the Army (and, by extension, the Air Force) from directly engaging in law enforcement activities such as search, seizure, arrest, and similar actions.2
PCA applies unless the Congress has specifically authorized such direct law enforcement actions by other statute or unless the emergency is of such significance that the President may exercise his direct executive authority under the Constitution.3
The PCA applies to Army active forces, to members of the USAR serving on active duty or active duty for training, and to the ARNG when in federal status. Importantly, the ARNG not in federal status serves at the direction of a state governor and may perform law enforcement functions consonant with the laws of the state. It should be pointed out, however, that active forces may protect federal property necessary to the performance of a federal function and may always act in self-defense and thus may be involved in the protection of critical infrastructure and in force protection roles in the United States.
HOMELAND SECURITY
The concept of homeland security (HLS), while certainly not new, has not received a high priority within the nation until now. As this report is being prepared, there is no certainty about how the newly established NORTHCOM would proceed with the military role, and no specific role has been assigned to the Army. However, there is no doubt that NORTHCOM will have requirements for HLS that the Army and the other military services must meet. To the extent that these requirements cannot be satisfied with current resources, they will help shape the Army’s Science and Technology Master Plan. The committee will consider future Army science and technology (S&T) requirements, as driven by NORTHCOM, in later studies, as the requirements evolve.
The committee proceeded on the assumption that the Army will play a significant role in HLS. A statement by Secretary of Defense Donald Rumsfeld reinforces this assumption:
With regard to supporting the effort to improve security at home, there are three circumstances under which DoD would be involved in activity within the United States.
Under extraordinary circumstances that require DoD to execute its traditional military missions. . .
In emergency circumstances of a catastrophic nature. . .
Missions or assignments that are limited in scope where other agencies have the lead from the outset (Rumsfeld, 2002).
Army Homeland Security Operational Framework
In anticipation of future taskings, the Army has developed a notional operational framework4 for HLS,5 consistent with the National Security Strategy,
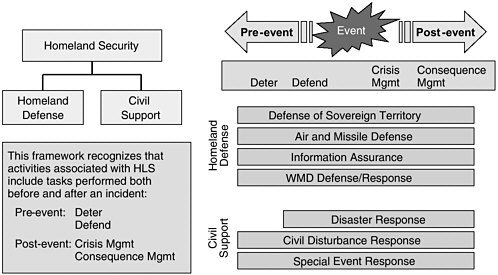
FIGURE 1-1 Army homeland security operational framework. SOURCE: Greg Bozek, Army War Plans Division, Army Deputy Chief of Staff, G3, briefing to the committee on May 15, 2002.
under which it includes “homeland defense” and “civil support.” This is illustrated in Figure 1-1.
These missions extend across a continuum from pre-event to event to post-event and incorporate sequential tasks—that is, deterrence, defense, crisis management, and consequence management.6 The President’s announcement at the 2002 United States Military Academy commencement ceremony regarding preemptory strikes indicates that the model is still a work in progress.
The committee views the missions of “defense of sovereign territory” as a traditional military warfighting mission and beyond its purview, although there are surely many technological developments that would be of interest. The challenge of “air and missile defense” has already been the topic of several excellent studies. Given the limited time frame for this effort, the committee has chosen not to address this element in the report. “Information assurance” and “weapons of mass destruction (WMD) defense/response,” while not new, surely pose new challenges and probably involve new functions or new applications of existing technology.
Homeland Defense
While perhaps least likely, scenarios exist that would demand a Presidential determination and the use of traditional military capabilities in the United States. Conceptually such an event could create the need for special capabilities related to operating in urban terrain but intermingled with and surrounded by U.S. civilians. The major capabilities required to deal with a substantial combatant force or for law and order could involve all three Army components. Additionally, as pointed out in the Army After Next Summer 1997 War Games and subsequent war games such as the Ellipse Series, conducted by Joint Forces Command, the threat to the homeland could limit the national command authority’s flexibility in overseas operations owing to concerns about protecting the homeland (Brennan, 2002).
Civil Support
As previously indicated, the Army has always been available for support of civil authorities. Civil support missions, while long a part of Army responsibilities, take on greater significance in a terrorist environment. The increased sophistication and capability of the terrorist threat require planning for events of catastrophic proportions. Circumstances involving the leveling of significant portions of cities and/or the use of WMD, with perhaps hundreds of thousands of casualties, could require the Army to assist in ways never before anticipated, both in support of civilian emergency responders and as an emergency responder on military installations. The size of the requirement for DoD support to special events (e.g., the Olympic Games and the Super Bowl) has also increased many times over, both in the number of events to be protected and the variety of functions to be performed.
The Army does have substantial relevant capability within its three components.7 However, the ARNG, in its state role, will most likely be the second responder on the scene after civilian emergency responders. The ARNG has organic units such as medical, heavy equipment engineer, military police, and communications units with inherent mobility and self-sustaining capability. It also maintains WMD response units, called civil support teams (CSTs), in many states. Depending on the situation, the active Army and the USAR will be available to reinforce the ARNG with whatever capability is necessary. The active Army has some unique capabilities when it comes to the detection of
biological and chemical weapons and consequence management of the aftermath of their use. These include some important and unique laboratory capabilities, large-scale decontamination units, explosive ordnance disposal teams, and medical research. The medical corps and laboratories also have considerable capabilities in forensic medicine and wound ballistics. The Army Corps of Engineers (USACE) has considerable capabilities that have been used frequently in support roles. Likewise, other major Army activities such as the Army Materiel Command (AMC) can be called upon to provide equipment, supplies, and other assistance to civilian agencies.
Finding 1-2. The Army National Guard, given its historical mission and flexibility, geographic dispersion, dual-mission capabilities, and frequent association with local agencies, is the key Army asset to meet homeland security demands and can be augmented as necessary with special capabilities from the Army Reserve and the active Army.
Organizational Vacuum
While it is not the task of the committee to make recommendations on organizations and functions, the apparent absence of an adequate and integrated national structure for the prevention of terrorist actions and intelligence sharing from the federal to the local (first response) level was striking.
To help it analyze the need for science and technology, the committee made use of a suggested HLS concept of operation and roadmap (see Box 1-2). It should be emphasized that this is just one example of how preparations might be made and information might be shared.
The Army’s Role
The committee has come to believe that the roles of the Army in HLS and in traditional war fighting, while quite distinct, will share certain similarities. One way to look at the Army’s potential role in HLS is to view it in terms of the five major functions the Army must accomplish. HLS operations modify but do not drastically change these fundamental functions:
-
Protecting the force,
-
Projecting the force,
-
Conducting operations,
-
Sustaining the force, and
-
Redeploying the force.
Protecting the force continues to be an umbrella concept that cuts across all five functional areas. It is continuous in nature in that it starts at a home installa-
|
BOX 1-2 Notional Homeland Security Roadmap Presidential Decision Directive 63 (PDD 63) or an updated version of it will serve as a base document for federal, state, and local efforts.
|
tion prior to deployment and closes back on itself with redeployment. In many ways a military installation can be viewed as another element of critical infrastructure and subject to the same considerations (threat analysis, early warning, increased security, etc.) as other critical infrastructures located throughout the United States and overseas. This remains a responsibility 24 hours a day and 7 days a week.
Projecting the force means that generally the force will have to move from a home base to conduct operations. Protection of vital lines of communication (air, land, and sea) must be assured. HLS has added a new dimension to the “fort to port” challenge. The movement of military units to the site of a domestic terrorist attack will be just as challenging—if not more so—than their simple movement to a port of embarkation.
The conduct of operations will generally involve operating with other organizations. These may be allies, coalition partners or, maybe, emergency first responders. Operations bring all the issues associated with compatibility and commonality. For an already manpower-constrained, capabilities-based force, the additional requirements associated with HLS make it even more imperative that S&T be leveraged to the extent possible to free up much-needed manpower. Unlike traditional operations, HLS missions will be accomplished in cooperation with a wide range of civilian local, state, and federal agencies. In considering the challenges of this new role, the committee was struck by the similarities between the Army’s new requirement for cooperative work with U.S. civilian emergency response agencies and the existing requirement for cooperative work with allies and various coalition partnerships. The requirements for interoperability, particularly in communications, are identical.
Without maximizing technology, sustaining the force can put an unacceptable burden on our limited lift and other logistical assets.
Finally, as we have learned so often, the Army must redeploy to its home base, recover, and prepare to do it all over again—and they must do it throughout the period of great vulnerability.
Finding 1-3. There are many similarities between military operations involving allied or coalition forces and operations involving civilian emergency responders.
Link to the Objective Force
The Army has been rethinking its concepts of warfighting since the end of the Cold War. The Objective Force is the Army’s future full-spectrum force that planners envision to be “more strategically responsive, deployable, agile, versatile, lethal, survivable, and sustainable across the entire spectrum of military operations from major theater war through countering terrorism to Homeland Security” (U.S. Army, 2002).
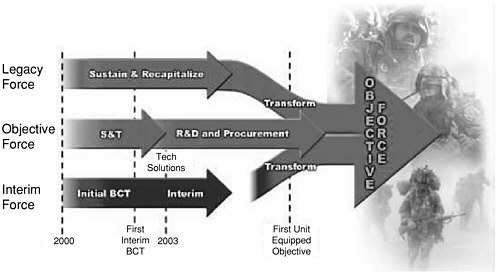
FIGURE 1-2 Army transformation. SOURCE: Andrews (2002)
Even as the Army continues its transformation into the post-Cold-War force, today’s soldiers, frequently called the “legacy force,” must be fully prepared to execute their responsibility to fight and win decisively against any enemy. The final transformation to the Objective Force, which begins in fiscal year 2008, will require many years of effort. The legacy force, in the meantime, will require sustainment and recapitalization to enhance its existing weapons, systems, and platforms to increasingly provide some of the Objective Force-like capabilities. As a transition from the legacy force and a vanguard for the Objective Force, an “interim force” fills the near-term gap. The interim brigade combat team (BCT) is a key element of the interim force. Figure 1-2 depicts the synergy between these forces.
The modernization strategy that is being used to bring the Objective Force to fruition envisions the acceleration of science and technology (U.S. Army, 2002). The committee believes that many of the requirements for HLS can provide a direct link to the capabilities-based Objective Force.
As indicated in the preface, the Army sponsor chose to use DoD’s Defense Counter-Terrorism Technology Task Force taxonomy as a framework. This taxonomy involves the following operational areas (DoD, In press):
-
Indications and warning,
-
Denial and survivability,
-
Recovery and consequence management, and
-
Attribution and retaliation.
Using this taxonomy, the following linkages between the Objective Force and HLS are made:
-
Indications and warnings technologies directly relate to protecting the force. Regardless of whether one is protecting an installation or conducting combat operations, there is a vital need for intelligence. The means of obtaining the intelligence and early warning (IEW) might vary, but the requirement is the same whether protecting an installation or conducting a combat operation. This IEW must then be transformed into actions that protect soldiers, units, and installations.
-
Denial and survivability are combat multipliers for all operations as well as subsets of force protection. Leaders responsible for conducting the wide range of missions associated with today’s Army must optimize the use of manpower and technology to ensure survivability.
-
Recovery and consequence management can be equated to conducting combat operations and redeployment. Assisting civilian emergency responders with the consequence management of a manmade disaster could be viewed as not much different than conducting coalition operations. Recovery is a subtask associated with redeployment.
-
Attribution and retaliation encompass a special form of combat operations. The Army must make available trained and ready forces to determine accountability and hold accountable the perpetrators of terrorism. The Army will most generally find itself supporting the civilian emergency responders or the combat commander, depending upon whether the terrorism is domestic or international.
Conclusion 1-1. Many of the technological requirements for homeland security will be important for the Objective Force.
Recommendation 1-1. To optimize current science and technology efforts, the Army should take advantage of potential transferability between technologies for homeland security and those for the Objective Force.
A great deal of effort and considerable resources are being directed at HLS in the civil sector. Much of the S&T effort of great interest to the Army is being conducted by agencies outside the Army. This commercially developed equipment might have great applicability for the Army, but there does not appear to be a mechanism for integrating the research being done in the civilian community with that being done in the military community. It should also be recognized that technology transfer to the civilian sector will be necessary in order for the civilian sector to exploit Army technology, and this technology transfer should be viewed as an integral element of the Army’s HLS mission. The committee could not identify an integrating process whereby a single agency8 was aware of all of this
activity; therefore, no one is certain of all that is being done. This makes it very difficult for the Army to conduct a gap analysis.
Conclusion 1-2. There needs to be better means to coordinate the homeland security science and technology efforts of the Department of Defense and those of the various civilian agencies.
Recommendation 1-2. The Army should encourage better coordination of the disparate homeland security science and technology efforts.
Conclusion 1-3. Homeland security technologies developed by the Army could be of great benefit to the private sector and to other government agencies.
Recommendation 1-3. The Army should facilitate technology transfer in order to allow the private sector and other government agencies to exploit the homeland security technologies it develops.
Experience over the last decade has taught us that the use of military forces in these situations will require a tailored force package. That is to say, certain types of military units will have to be used together in a coordinated fashion. Most of the Army’s experience in this area has been gained without the pressure of time. The Mission Rehearsal Exercise Model has served the Army well. However, September 11, 2001, shattered that model and has forced us to think about no-notice adaptive force packaging. It is the committee’s belief that this will become the norm rather than the exception to the rule.
Conclusion 1-4. The ability to rapidly deploy a capability-based task force in support of either the homeland security mission or an Objective Force mission will become even more critical.
Recommendation 1-4a. The Army should investigate the technologies necessary to put together on the fly the force packages necessary to meet the requirements of both homeland security and the highly deployable Objective Force.
Recommendation 1-4b. Given the time lag associated with training personnel and leadership to use new technology, now is the time to start dealing with these issues in the context of homeland security, so that they are well honed by the time the Objective Force is fielded.
By having preplanned task forces available, the Army will not only provide better assistance to civilian emergency responders but also will be able to perfect the required techniques by the time the technology associated with the Objective
Force is fielded. The committee draws attention to this implied task to give an example of the synergy between HLS and Objective Force missions.
RESEARCH AND DEVELOPMENT FOR THE ARMY
The Army has traditionally taken care of its own needs for new technology. In the earliest days, hardware was largely built at its own arsenals, but this is largely done now by a broad set of R&D players. Most equipment is manufactured in the private sector, some by contractors and some by commercial suppliers, from whom it is procured off-the-shelf. The R&D for specifying these purchases is done in Army and other military laboratories, in academic laboratories sponsored by the Army, and in industrial laboratories under Army contracts. In recent years alliances of the Army, academe, and industry have been formed to improve the Army’s focus in key areas.
The management of R&D is assigned to different departments, as well as to offices and entities at DoD. The AMC manages most of the R&D through the Army Research Laboratory and the AMC major subcommands that focus on product areas. Each of these has a Research, Development, and Engineering Center that performs 6.2 and 6.3 work—some in-house, but most under contract.9 Separately, the Army’s Medical Commands and the USACE perform their own R&D. Additionally, the USACE Engineer Research and Development Center has the DoD-wide S&T (6.1-6.3) lead for Survivability and Protective Structure for explosive threats. Within the Army the USACE center has a force protection mission, but other participants are responsible for various aspects of the CBRNE threat spectrum. The Deputy Assistant Secretary of the Army for Research and Technology supervises the 6.1-6.3 work for nearly all of AMC and for some of the medical and USACE work. A separate office in DoD oversees chemical and biological warfare work for which the Army is the principal executing agent through the U.S. Army Soldier and Biological Chemical Command (SBCCOM) and the various medical commands, such as the Medical Research and Materiel Command. The Defense Advanced Research Projects Agency (DARPA) carries out work for and with the Army. The most notable DARPA program today is the Future Combat Systems program. Being well aware of the divided R&D responsibilities, the committee decided to review as broad a range as possible of technologies that might be of help to the Army for HLS; it did so for completeness and to make the report more valuable.
The committee believes it is important to recognize an Army challenge to the S&T problem associated with HLS. From everything the committee has heard, it is clear that the ARNG will play a significant role for the Army in HLS. Any
definition of the critical requirements associated with HLS must have ARNG input, and appropriate resources must be applied to the Department of Army Master Priority List. HLS is an area in which the active Army will find itself supporting the ARNG, and this must be recognized when developing the Army Science and Technology Master Plan. The committee feels that the Army must make that commitment to the ARNG.
Conclusion 1-5. The Army National Guard does not appear to play a direct role in defining the critical requirements associated with homeland security.
Recommendation 1-5. The Army National Guard homeland security role must be considered in the development of the Army Science and Technology Master Plan, and resources for these requirements applied as appropriate in developing the Department of the Army Master Priority List.
SCENARIOS
Threats are classified in terms of scenarios, the most common being CBRNE. Scenarios vary widely in their effects. We usually think of nuclear scenarios as very large and regional in effect. Explosive/incendiary scenarios are more likely to be limited in area of impact. The Pentagon disaster, for example, affected only a single building.
Our built environment has been constructed largely on the basis of ordinary occurrences and does not consider warlike disasters. Thus the usual building codes do not provide resistance to bombs, firestorms, nuclear blasts, and the like. There are exceptions. Resistance to earthquakes is now required in many seismically active regions. Wind resistance is specified in certain buildings. And we find that the World Trade Center was designed to resist the impact of an aircraft but not the combination of that plus a conflagration. Nor have we designed our environment with chemical or biological attacks in mind. So we are now faced with having to rethink these hazards and plan our response to them.
One can imagine a wide range of effects for chemical, biological, nuclear, and radiological (dirty bomb) attacks. The committee reviewed scenarios created by the following organizations: Rand Corporation, Hicks & Associates (SAIC), DARPA, and the Office of the Deputy Assistant Secretary of the Army for Research and Technology.
Funding responsibilities are divided within the government, and the Assistant Secretary of the Army for Acquisition, Logistics, and Technology is not responsible for planning investment strategies for chemical, biological, and nuclear threats. Nonetheless, the committee felt that it had to consider all scenarios to ensure the completeness of its work. Furthermore, it needed this
|
BOX 1-3 Some Sample Scenarios
|
|||||||||||||||
better understanding to consider the additional priorities that should be established when a particular technology applies to more than one scenario. The scope and nature of the scenarios tend to dictate both who the principal responders are and the functional capabilities required for dealing with the scenario. Thus, local civilian emergency responders will probably deal with a limited conventional attack, with support from other governmental levels as necessary. A major regional disaster will certainly require state-level response, including the ARNG. In the more severe cases, full military support to civilian authorities will be required, and there may have to be Presidential declarations enabling the full use of federal resources, including federalizing the ARNG and using the active and reserve Army components to maintain law and order.
For the present study these distinctions are important, as each type of scenario is considered, particularly in recovery and consequence management. See Box 1-3 for some scenario examples. Note that in most localized disasters certain elements of the active Army are called upon to assist, but, as indicated above, not for law enforcement. Such elements might include USACE, the various Army
medical commands, and the logistical capability of the AMC. In a chemical or biological attack, the AMC’s SBCCOM will certainly be involved. In developing the capabilities required to address each of the four operational areas—indications and warning, denial and survivability, recovery and consequence management, and attribution and retaliation—the committee had to determine those capabilities that apply to all scenarios and those that are required only for certain scenarios. Thus some scenarios will require massive evacuations; others, vaccinations and quarantines.
FUNCTIONAL CAPABILITIES AND ASSOCIATED TECHNOLOGIES
The committee’s working groups determined that certain functional capabilities were required in each of the operational areas. These, in turn, were broken down into technologies. It is important to note that for this overview, the committee decided to review technical areas one level above a particular project, device, or technique. For example, the committee looked at uncooled infrared night vision as a field capability but not at specific devices presently under development. Once the committee had determined the individual technical areas, the assessments began.
This broad survey of relevant technologies was undertaken to gain some general understanding of the S&T involved. The assessments are meant to assist in devising an R&D investment roadmap for the Army. The committee studied each technical area enough to judge its maturity. The study comments on the state of the technology and on the appropriateness of funding work in this area with Army S&T funds. In some cases it was found that S&T that was important to both the Army Objective Force and to HLS did not warrant the expenditure of Army S&T funding because other agencies or organizations have principal responsibility for that area and S&T funds are appropriated for the other agencies. Regardless of which agency is responsible for the S&T, the Army must be appropriately equipped with the products of this S&T if the products affect the missions assigned to the Army.
Each chapter contains a series of tables that display the committee process. The committee offers its judgments on priority by functionality, technology, characteristics, availability, priority for Army S&T, and uses. Each of the tables is somewhat different, depending on the information it was intended to present; however, all will follow the same general outline.
Functionality is the broadest parameter and is intended to describe, in a general sense, what the technology should be able to do. The technology column is technology at a generic level, not to be construed as suggesting a specific system. The characteristics column provides a general description. Availability is described by clustering the technology readiness levels (TRLs) into three
groups. A full description of TRLs is available in Appendix C. Throughout these tables, the following code is used to describe availability:
-
R, ready (TRL 8-9);
-
N, near (TRL 4-7); and
-
F, far (TRL 1-3).
The committee next gives its opinion on priorities for S&T investment. The following gradients are used:
-
Low, someone else has the mission or the technology is ready and available;
-
Medium, useful but of limited impact and some investment is needed; and
-
High, very important, no one else is working on it, and considerable investment is needed.
In some cases parenthetical entries suggest that participation by universities and/or industry should be especially sought because their technology, understanding, experience, and/or scientific capabilities in these areas are advanced, their databases are useful, and their participation would provide new insight and/ or information to the program and shorten the time frame for development. A summary table appears at the end of Chapter 6 that displays each of the technologies that the committee has rated high—that is, very important for Army S&T. This table will provide insights for high-payoff technologies.
As mentioned above (see the section “Scenarios”), some of the technologies will apply to more than one scenario or be used by more than one type of operator. The committee termed these multiuse technologies, and it tended to give them a higher priority. The following code is used throughout the report tables:
-
H, homeland security (HLS);
-
O, Objective Force (OF); and
-
C, civilian.
As the committee process progressed, it became clear that certain technologies were of such universal significance that they crossed operational boundaries. The committee feels that command and control, communications, computers and intelligence, surveillance and reconnaissance (C4ISR) will be of supreme importance and will apply to a greater or lesser extent in each of the four operational areas. Therefore C4ISR is an implied subarea in each task. Similarly, medical response is a major component of crisis response and must be a part of the discussion on recovery and consequence management.
Conclusion 1-6. Command, control, communications, computers and intelligence, surveillance, and reconnaissance (C4ISR) is of supreme importance and will apply to a greater or lesser extent in each of the four operational areas in both homeland security and the Objective Force.
SUMMARY
In conclusion, the committee believes that the S&T required by the Army for HLS need not be unique. The S&T work already being done for the Objective Force could provide much of the technology needed for HLS. In fact, if approached properly, the HLS effort not only can help to advance the S&T needed for the Objective Force, but can also assist in developing tactics, techniques, and procedures. The ARNG is critical to the success of the Army’s efforts in HLS. In order for the Army to successfully meet the challenge of the HLS mission, all components of the Army must work together.
REFERENCES
Andrews, A.M. 2002. Army Science and Technology…Accelerating the Pace of Transformation. Briefing by A. Michael Andrews, Deputy Assistant Secretary of the Army for Research and Technology, to the Committee on Review of the Effectiveness of Air Force Science and Technology Program Changes. The National Academies, Washington, D.C., August 22.
Brennan, R. 2002. Protecting the Homeland: Insights from Army Wargames. Available online at <http://www.rand.org/publications/MR/MR1490/MR1490.pdf>. Accessed on October 3, 2002.
Department of Defense (DoD). 2001. Department of Defense Dictionary of Military and Associated Terms. Available online at <http://www.dtic.mil/doctrine/jel/doddict>. Accessed on September 6, 2002.
DoD. In press. Defense Counter-Terrorism Technology Task Force. Alexandria, Va.: Defense Threat Reduction Agency.
Rumsfeld, D. 2002. Testimony of the Secretary of Defense before the United States Senate Committee on Appropriations, May 7.
U.S. Army. 2001. Army Science and Technology Master Plan. Washington, D.C.: U.S. Army, Office of the Deputy Assistant Secretary of Defense for Research and Technology (Chief Scientist).
U.S. Army. 2002. Weapon Systems 2002. Washington, D.C.: Government Printing Office.


















